The below information provided via Lab Dookhtegan and Treadstone 71 research supports earlier Treadstone 71 reports on Iranian influence operations, cyber operations, persona generation, Basij Cyber Battalions, and targeted adversary analysis (see the links below). Iranian intelligence operations demonstrates fear of dissident and opposition activities abroad and an effort to control and eliminate any potential counter narrative to the official revolutionary line, including assassinations. Iran controls internal communications with Dezhfa. The Shahid Kaveh organization is not new as we have reported on them many times in the past (see the links below).
While this holds to be true, there are still internal Iranian regions and opposition groups targeted for cyber penetration, oppression, and suppression of messaging. Iran targets and uses internal spies to penetrate groups that have nothing less than a differing opinion on how the country should be run. They infiltrate, identify, arrest, torture, and murder. Their inability yet constant attempts to control dissident behavior takes shape below in our postings and analysis. Iran cyber tradecraft blends with the kinetic as they seek to learn about all dissident movements, online postings and traffic, the installation of surveillance applications and malware on targeted devices, and the penetration of opposition internal operations shows they cannot be trusted. We suggest these types of activities be included in the efforts at JCPOA renewal (along with fomenting unrest in Lebanon, Gaza, Jordan, Turkey, Yemen, Bahrain, and Saudi Arabia non-inclusively).
Associated files are available within this posting.
- Treadstone 71 “The Sayad Project”
- Treadstone 71 CYBERBAN Shahid Kaveh Unit
- Treadstone 71 We are exposing here our correspondence with one of the members of “Shahid Kaveh” Mohammad Shamlou-Fard (Shambouli)
- Basij Cyber Battalions:
- #Basij Cyber Battalions – Latest From Treadstone 71 – The Cyber Shafarat – Treadstone 71
- Cyber Battalion Empowerment Courses in Abali – Iranian Basij Cyber Battalions – The Cyber Shafarat – Treadstone 71
- Establishment of a cyberspace headquarters in Masoumiyah Theological Higher Education Institute – Data Laundering – The Cyber Shafarat – Treadstone 71
- The Basij Cyber Battalions are working to counter enemy attacks in cyberspace (Names and cadre for some of the Basij Resistance areas around Tehran) – The Cyber Shafarat – Treadstone 71
- Forming #cyber battalions and service teams is one of the core plans of the #Basij – The Cyber Shafarat – Treadstone 71
- Student Basij Initial Enrollment Form – The Cyber Shafarat – Treadstone 71
- Iranian Influence Operations
- Targeted Adversary Research and Analysis
- An explosive new report from Treadstone 71 Link Analysis of Various Iran Cyber Operators and Academics – The Cyber Shafarat – Treadstone 71
- Day 2 and 3 #VAJA #MOIS data release from Parastoo as of 16:00 May 5 ETD – The Cyber Shafarat – Treadstone 71
- The latest from #Parastoo on the RANA Institute hack of Sharif University – The Cyber Shafarat – Treadstone 71
- Day 4 Parastoo on hacked accounts at Sharif University – The Cyber Shafarat – Treadstone 71
- Rana Institute continues to spy on Iranian Citizens for the MOIS #Parastoo – The Cyber Shafarat – Treadstone 71
- Tapandegan Releases Trove on Iranian Stock Market Manipulation – The Cyber Shafarat – Treadstone 71
- Dissident Tracking and Assassination
- Iranian MOIS – Vaja hacks Turkish Government Site Tracking dissidents – The Cyber Shafarat – Treadstone 71
- Masoud Molavi CV – Assassinated Istanbul -Ordered through Iranian consulate – Video – The Cyber Shafarat – Treadstone 71
- Inside The World of Cybersecurity Experts Who Hunt Criminals (VIDEO) (newsy.com)
As translated directly from Iranian Intelligence documents
Iranian tar
- Targeting the 2020 Free Iran Annual Meeting – targeting orgchart
- British, American, French, UK, Italian Targets – Free Iran 2020 Annual Meeting – Invited People – Americans – Social Media – Live Broadcast targeting
In the name of God
Ilianet Gostar Iranian
Sayyad Project
Significance
One of the major purposes of Sayyad project is to cause disruption in the activities of enemy groups.
The annual meeting of these groups is a main and important venue for promoting this organization. Holding such events is a means for this group to announce they are still alive and hence to provide a part of their budget. Therefore, causing damage and disruption to these meetings may damage their reputation and ruin their existence, and as a result lead to their faster destruction.
Purposes
- Preventing the annual meeting if possible or causing disruption in the process of holding the meetings.
- Showing that the meetings are useless and they can only be used locally.
- Preventing the development of these groups and recruitment of new members.
- Ruining the international reputation of the enemies.
- Eliminating the support of the enemy groups by European countries
- Making Albania unsafe as the enemies’ host.
- Blacklisting these groups as terrorist groups
Potential measures
- Identifying the enemies’ websites
- Obtaining the access to the enemies’ major websites used for dumping data and analyzing the existing data to identify the important figures, their local agents, the recruiting methods and their collaboration with these groups.
- Identifying the websites that provide live coverage of these meetings in order to disrupt the live broadcast of the meeting and to end their connection to the meetings if possible.
- Providing campaigns for cyber resistance against the enemies
Achievements
- Causing disagreement among Albanian people regarding the existence of the enemies in their countries.
- Destroying the communication channels between the enemies and their local forces inside Iran
- Destroying the sham magnificence of the enemies
- Unveiling the real truth of the enemies
- Preventing the spread of news regarding the enemies’ meetings
- Blacklisting these groups as terrorist groups
FAX: 021-7671336, 021-7672823
Ilianet Gostar Iranian
Sayyad Project
Subject: locating, identifying and prioritizing all measures that lead to damaging s.x.v (س.خ.و) and disrupting their performance, and providing ideas and means for fulfilling the desired goals.
- Introduction
After a careful study of the enemy groups, it seems that the strength of enemy groups is in how they establish connections with different individuals to carry out operations that counter the benefits of the Islamic Republic of Iran either locally or internationally. They even use these connections to perform physical operations. Given this issue, in order to cause damage to these groups, the priority should be given to intelligence measures to obtain information from individuals, means of communicating with groups, identification measures and identifying their agents.
- Taken measures
- Suggested measures
- Obtaining the access
- Existing accesses
- Obtaining the access
- Tavana website
Note: After reviewing the information of Tavana website and considering that the website advises the users to create fake emails for themselves at the very beginning of membership, accurate information cannot be obtained from users and members collaborating with the website.
Suggestions: this website provides a series of VPN services to its users. It is suggested that malwares be developed and embedded in this website in order to infect the website users’ systems. These malwares shall obtain identity information such as the number of accounts, names and phone numbers of real individuals so that the website connection to local forces can be interrupted, through using contact information and important forces.
- tv, live stream website
Note: Over the past years, this group used live stream function of synople.tv to have live broadcast of their meetings. Given the current state of the world and the spread of covid-19, it seems that the annual meeting of this group will be held on the Internet.
Suggestion: the access to the website should be analyzed and necessary measures should be taken at the time of the meeting to disrupt the live broadcast of the annual meeting.
- Emails of certain individuals who are a member of enemy
Note: Over the past years, a limited number of emails from the enemies have been obtained.
Suggestion: To better analyze and identify the relevant individuals, we need access to the emails.
Notes: given the background of the enemy, it seems that sending threatening emails to the members of this group does not suffice. Thus, after using the email platforms, to better know them, disuniting emails can be sent to them. Such emails can be sent by emails of their own or email that we have access to.
3.1.2 New accesses
- org
Note: this is the main website of Mujahedin. In the radio section of this website, besides to live news broadcast, a program called “those who want to interact” is aired, whose function is to establish health appointment for radio audience and those who want to collaborate with the group.
Suggestion:
- Obtaining the access to radio.mojahedin.org which is the subdomain of the main website and pertinent to the radio section
- Obtaining the access from the email introduced in radio for establishing relation with audience.
- Analyzing the information existing in the email in order to identify the important person, their local forces and the means and process of establishing relations and recruiting new members to collaborate with them.
- The use of obtained platforms. Subdomain of the main site and the site email, after completing the identification work, to upload the desired content on the website. This content should be in line with disrupting the site’s communication with its audience and introducing its own intermediaries.
- com website
Note: This is the TV website of enemies. This website has 2 software programs. One software program is for live broadcast and the other one is for video archive and website programs.
Suggestion: obtaining the access to both website and software programs with the following objectives:
- Causing disruptions in live broadcasts during sensitive moments e.g. during important live speeches.
- Placing the desired content in the website and archive software.
- Infecting the users’ system to locate them
Note: given the background of enemies and the probability of their operations inside Iran, this capability can be used to locate the users and find their geographical coordinates during the operations.
- Identifying websites that support enemies for mass hacking and preventing the news coverage of the group annual meetings
- Identifying the admins of telegram channels with the goal of
- Sending malware together with videos and photos with interesting content for them
- Hacking the accounts.
- Finding the geographical coordinates of the enemy camp with the goal of:
- Finding the users of Twitter and Instagram, who provide content in Persian or submit relevant posts in social platforms. Waging psychological warfare, making discontent or establishing relationship with the camp
- Finding ISPs that provide them with the Internet and causing disruption in their internet connections or damaging their systems.
3.5 Providing a list of hashtags and issues they have focused on and finding the person who has used these hashtags first with the goal of identifying important individuals and major forces.
3.6 establishing relation with fake individuals and enemies.
FAX: 021-7671336, 021-7672823
In the name of God
Ilianet Gostar Iranian
Report on discovery and membership in a secret dissident group
First, an attempt was made to identify the key members of the resistance channel, whose telegram channel was available at moghavevat.org, and it led to an acquaintance with its admin, Mr. Siamak Rezapour.
By communicating with him and trying to enter their secret circles, he finally introduced us to a group manager named Mehran Salehi (manager of one of the groups).
In the name of God
Ilianet Gostar Iranian
In order to prevent the actions of the Iranian opposition living abroad, in the first step, it is necessary to monitor all the activities of these oppositions, including their movements and relations with different countries. For this reason, the identification of Albanian airports and related airlines is a priority.
Albania currently has three international airports and two airlines.
- Tirana International Airport
The airport is located 11 km northwest of Tirana in a region called Korce and is known as Mother Teresa Airport. It is also known as Rina Airport. This is the main airport of Albania
Year of construction: 1957
Area: km2
Number of flights in 2018: 25426
Number of runways: 1
Number of passenger terminals: 1
- Kukes Airport Zayed bin Sultan Al Nahyan
This airport is located 3.5 km south of Kukes city. Despite being an international airport, it operates like a local one. No website has been found for it and the facilities of this airport are the facilities of a normal small airport.
This airport is currently under reconstruction.
- Vlore airport
Vlore international airport is an airport project expected to be built in 2020 and in the Vlora city of Albania.
FAX: 021-7671336, 021-7672823
info@eeleyanet.ir
Albawings airline
Domain: albawings.com
Introduction
Albawings is one of the best Albanian airlines. This company was founded in 2015 and now connects Albania to European destinations.
Albawings is also committed to provide the most reasonable prices for flights destined for Albania.
Airlines
- The website capabilities
- Online reservation system of the airline – under domain booking.albawings
- No access
- Distribution management system under domain dms.albawings where documented written reports are uploaded by pilots and flight crew.
Accesses
- Access to dms.albawings panel (distribution management system)
- Shell access to the main website
- Offline webmail access – update function (the need for deepening for online access)
Offensive measures
- Obtaining the information of passengers
- Causing disruption in the report system of flight crew and pilots in DMS
Achievement
- Intelligence dominance over the arrival and departure from Albania
Contact Treadstone 71 on our services
In the name of God
Ilianet Gostar Iranian
Subject: the reports of measures taken in Khalgh Project 99
Report date: 02/13/2021
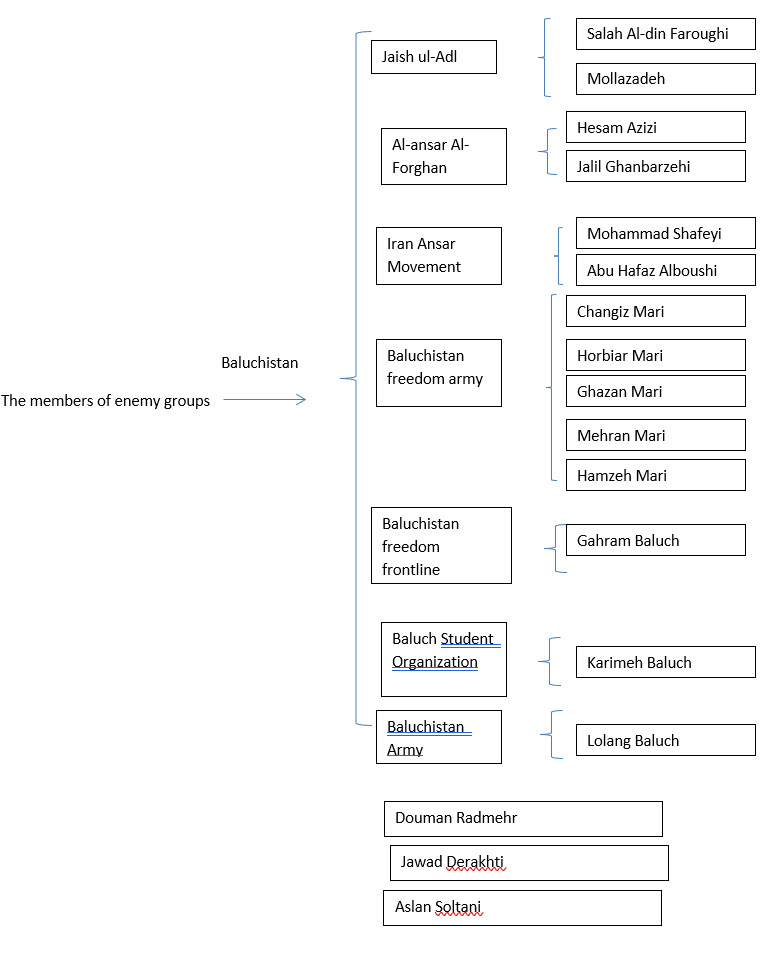
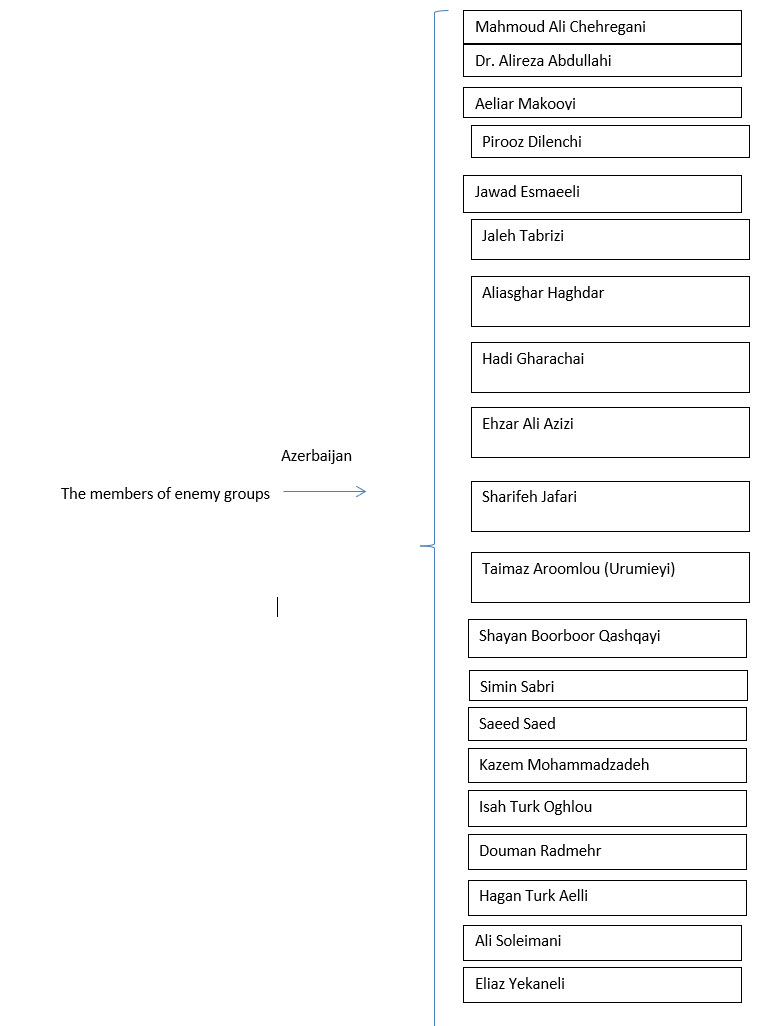
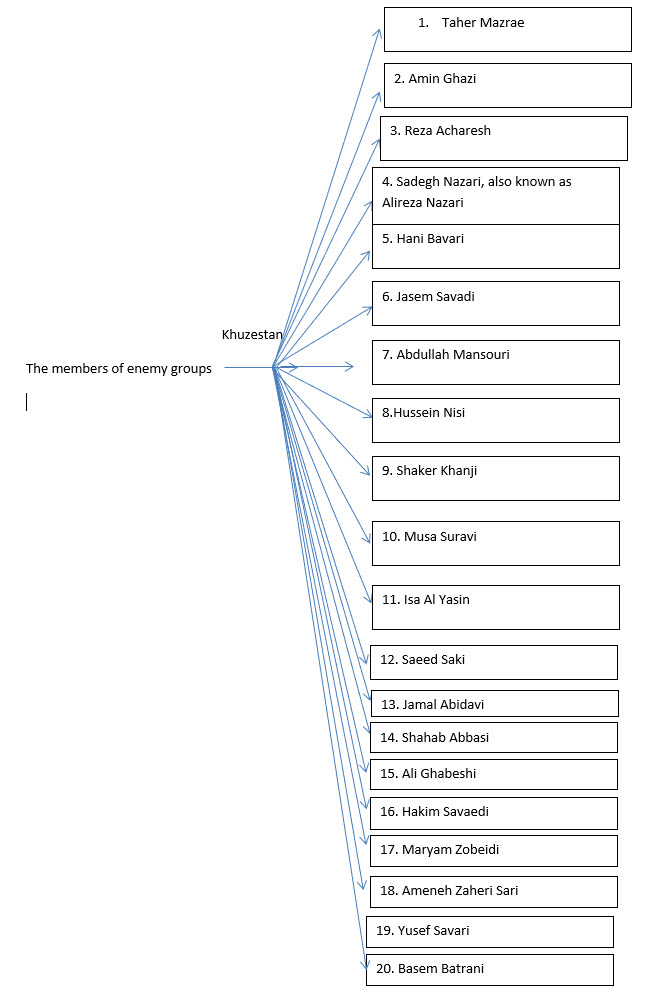
- Creating a list of enemy groups in Iran in the form of excel files and based on URL, the group name, place of establishments, social networks, IP, etc.
- Categorization of groups to Kurdistan, Baluchistan and Ahwaz enemy groups.
- Creating a double single sheet and two flashcards for Pakistan accesses
- Creating a single sheet of Zelli app (an app used by the enemy groups)
- Creating an initial map for enemy groups
- Providing an introduction report to Ali Javanmardi accounts and placing them in the system
- Completing the map of groups, and introducing their members, leaders and Facebook IDs
- Holding meetings and reporting the taken measures to Mr. Engineer
- Placing the individuals’ Facebook IDs in the system
- Providing a list of Kurd Personalities in Kurdistan and the relevant photos
- Completing the list of Facebook IDs with 68 IDs so far, the majority of which belongs to Democratic Party of Iranian Kurdistan, Komala Party and Kurdistan Free Life Party.
FAX: 021-7671336, 021-7672823
info@eeleyanet.ir
In the name of God
Ilianet Gostar Iranian
http://alahwaz.com alahwaz.info
http://www.pscp.tv/w/1zqKVewVyrlxB
http://www.pscp.download/?url=https%3A%2F%2Fwww.pscp.tv%2Fw%2F1zqKVewVyrlxB
http://www.kurdpa.net/index.php?besh=dreje&id=2704 ( GET )
FAX: 021-7671336, 021-7672823
In the name of God
Ilianet Gostar Iranian
Sayyad 2 Project
Introduction
Over the holy 40-year history of the Islamic Revolution, many forces have done their best to weaken, destroy or mislead this popular movement which arose from the pains of the oppressed and deprived people, a movement that was guided by the light of our late Imam and then the supreme leader, both enjoying the support of Imam Zaman (may our lives be sacrificed for Him). Among these forces were the enemies of the Holy Islamic Republic of Iran, which collaborated with the global arrogant powers to bring the movement of Imam Ruhollah Khomeini (peace be upon him) to its knees.
Now, many years have passed but they do not still feel regret about their deeds and are after fighting the revolutionary and martyr-growing nation of Iran. However, the young and revolutionary Iranian believers are ready to combat these hated enemies of revolution in every single frontline. Therefore, they have decided to conquer the fake dugouts of the enemies on the Internet, which are weaker than spider’s net. This project is among such measures taken by these revolutionary youths.
Treadstone 71 – Contact | Treadstone 71
Report on discovery and membership in a secret dissident group
First, an attempt was made to identify the key members of the resistance channel, whose telegram channel was available at moghavevat.org, and it led to an acquaintance with its admin, Mr. Siamak Rezapour.
By communicating with him and trying to enter their secret circles, he finally introduced us to a group manager named Mehran Salehi (manager of one of the groups).
After contacting him and requesting to join the secret groups, he sent videos about the security of the telegram and how to keep it safe. He mentioned that we can become a member under the condition of conforming to these security guidelines (by reviewing the video, we found out that almost all security points were observed).
Finally, we entered a group called Bahar Iran.
After the membership in the group and doing a search, we found that members discuss the objectives and plans in the group. According to a schedule, every night at 22 pm, one key member analyzes the daily news and elections, under the cover of a teacher.
| Weekly plan of live sessions in the first week of Ordibehesht
|
||
| Saturday | A talk with Master Javid: the economic structure of the regime | 22 pm |
| Sunday | A talk with Master Khorasani: daily political topic | 22 pm |
| Monday | A talk with Mehran Salahi: Army’s notice and achievements | 22 pm |
| Tuesday | A talk with Master Khorasani: daily political topic | 22 pm |
| Wednesday | A talk with Master Shahin Qobadi: revolutionary diplomacy | 22 pm |
| Thursday | No dialogue | 22 pm |
| Friday | No dialogue | 22 pm |
At present, this organization is carrying out activities such as slogan writing, recruitment, etc. in Tehran and other cities, especially Karaj. Documents collected from members and the second assigned force are also attached.
In addition, the profiles of members and important people of this group have been photographed and documented due to the lack of public access to the group.
In this group, we entered as Ms. Melika Rahnama who is a student of Law at Azad University of Karaj. We were active in that group by building trust among the members
Files:
- Statements and news
- Videos
- Photos and members ID
Targeting Information:


| row | Host | Subdomain | Ip |
| 1 | mojahedin.org | mojahedin.org | 15.188.230.179 |
| 2 | mojahedin.org | autodiscover.mojahedin.org | 52.6.140.65 |
| 3 | mojahedin.org | autodiscover.mojahedin.org | 54.175.152.112 |
| 4 | mojahedin.org | autodiscover.mojahedin.org | 52.23.143.228 |
| 5 | mojahedin.org | event.mojahedin.org | 13.224.198.31 |
| 6 | mojahedin.org | event.mojahedin.org | 13.224.198.26 |
| 7 | mojahedin.org | event.mojahedin.org | 13.224.198.116 |
| 8 | mojahedin.org | event.mojahedin.org | 13.224.198.36 |
| 9 | mojahedin.org | library.mojahedin.org | 13.224.198.116 |
| 10 | mojahedin.org | library.mojahedin.org | 13.224.198.36 |
| 11 | mojahedin.org | library.mojahedin.org | 13.224.198.31 |
| 12 | mojahedin.org | library.mojahedin.org | 13.224.198.26 |
| 13 | mojahedin.org | report.mojahedin.org | 13.224.198.26 |
| 14 | mojahedin.org | report.mojahedin.org | 13.224.198.116 |
| 15 | mojahedin.org | report.mojahedin.org | 13.224.198.36 |
| 16 | mojahedin.org | report.mojahedin.org | 13.224.198.31 |
Opposition website URLs and IPs for targeting
| row | Domain Name | Creation Date | Registrar | |
| 1 | mojahedin.com | 10/15/2003 | networksolutions.com | |
| 2 | rahnamatolid.com | 5/24/2011 | realtimeregister.com | |
| 3 | mojahedin.org | 11/3/1997 | networksolutions.com | |
| 4 | estakhrsaz.com | 5/21/2018 | publicdomainregistry.com | |
| 5 | lgtamirat.com | 8/19/2017 | onlinenic.com | |
| 6 | aroadecor.com | 8/13/2017 | publicdomainregistry.com | |
| 7 | arioservice.com | 8/8/2017 | publicdomainregistry.com | |
| 8 | reykanrepair.com | 5/7/2017 | onlinenic.com | |
| 9 | bitumen-portal.com | 12/26/2016 | publicdomainregistry.com | |
| 10 | bitumenportal.com | 12/26/2016 | publicdomainregistry.com | |
| 11 | mehrparsfund.com | 10/26/2016 | realtimeregister.com | |
| 12 | aroa-petroleum.com | 10/25/2016 | publicdomainregistry.com | |
| 13 | aroa-tech.net | 7/21/2016 | publicdomainregistry.com | |
| 14 | aroatech.net | 7/13/2016 | epag.deenwhois | |
| 15 | aroatech.com | 7/13/2016 | epag.deenwhois | |
| 16 | ts-iranian.com | 6/18/2016 | onlinenic.com | |
| 17 | mivekhoshk.com | 11/1/2018 | apiname.com | |
| 18 | canadasettel.com | 2/16/2015 | tucowsdomains.com | |
| 19 | khaterehstudio.com | 6/18/2016 | realtimeregister.com | |
| 20 | taranomsobh.com | 5/24/2014 | realtimeregister.com | |
| 21 | julius-watch.com | 7/1/2017 | realtimeregister.com | |
| 22 | azimi-el.com | 5/12/2013 | realtimeregister.com | |
| 23 | mehrbroker.com | 2/7/2008 | realtimeregister.com | |
| 24 | mancaveentertaintment.info | 4/15/2013 | godaddy.com, llc (r171-lrms) | |
| 25 | mancaveentertaintment.us | 4/15/2013 | (registration services) whois.godaddy.com | |
| 26 | spadanashop.com | 2/26/2018 | zenregistry.com | |
| 27 | peykeshadi.net | 12/3/2014 | networksolutions.com | |
| 28 | azimi.net | 10/19/1999 | networksolutions.com | |
| 29 | spadanapipe.com | 2/28/2019 | apiname.com | |
| 30 | parsa-trade.com | 9/25/2013 | zenregistry.com | |
| 31 | aroa-tech.com | 7/13/2016 | internetbs.net | |
| 32 | instabotgram.com | 1/11/2018 | joker.com
ینستابات گرام | افزایش فالور واقعی اینستاگرام | سه روز هدیه رایگان Instagram Gram | Increase real Instagram followers Three days free gift |
|
| 33 | farazplast.com | 6/25/2014 | joker.com | |
| 34 | spadana-pipe.com | 10/20/2003 | zenregistry.com | |
| 35 | pumpkeen.com | 11/16/2011 | zenregistry.com | |
| 36 | vivaskin.net | 10/31/2010 | zenregistry.com | |
| 37 | parsianexir.com | 3/1/2011 | realtimeregister.com |
|
- Internal Iranian Targets – Domains Sub-Domains Site Leadership
- TV Stations-Twitter-Telegram-Facebook-SocialMedia Targets and Political Parties

Contact Treadstone 71 for information on cyber intelligence training, services, and consulting including intelligence program builds, cyber counterintelligence, adversary targeting, program assessments and customized services.
Treadstone 71 – Contact | Treadstone 71














You must be logged in to post a comment.