With respect to the many Iranian cyber professionals doing what is natural, standing up for your country – we find we must post data relative to adversaries.
LEARN CYBER INTELLIGENCE TRADECRAFT – http://www.planetreg.com/E76722275820
A few years ago, Iran held a capture the flag (CTF) exercise focusing on exploitation of their nuclear facilities as related to the Atomic Energy Organization of Iran (AEOI) – http://www.aeoi.org.ir/Portal/Home/ .
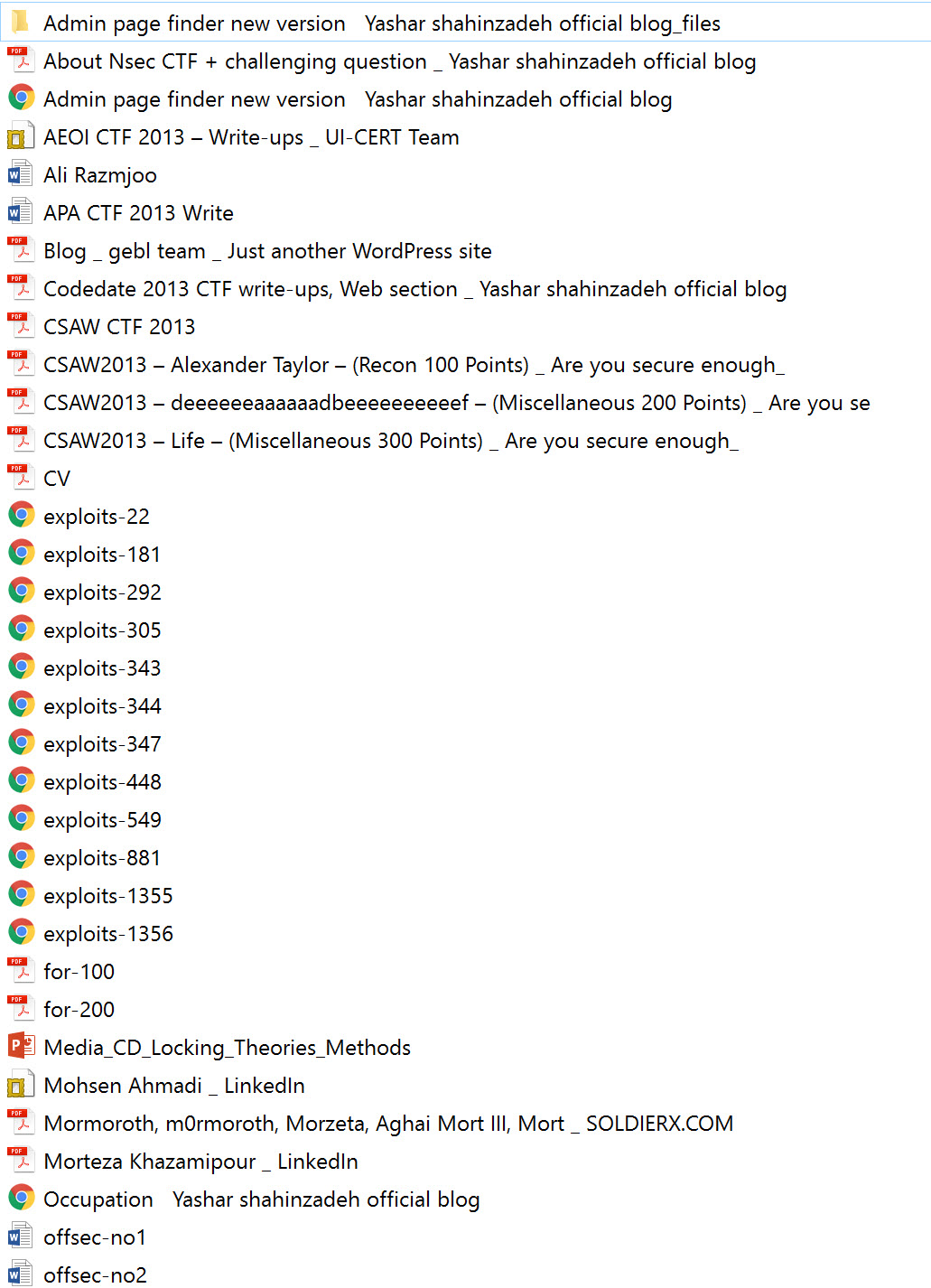
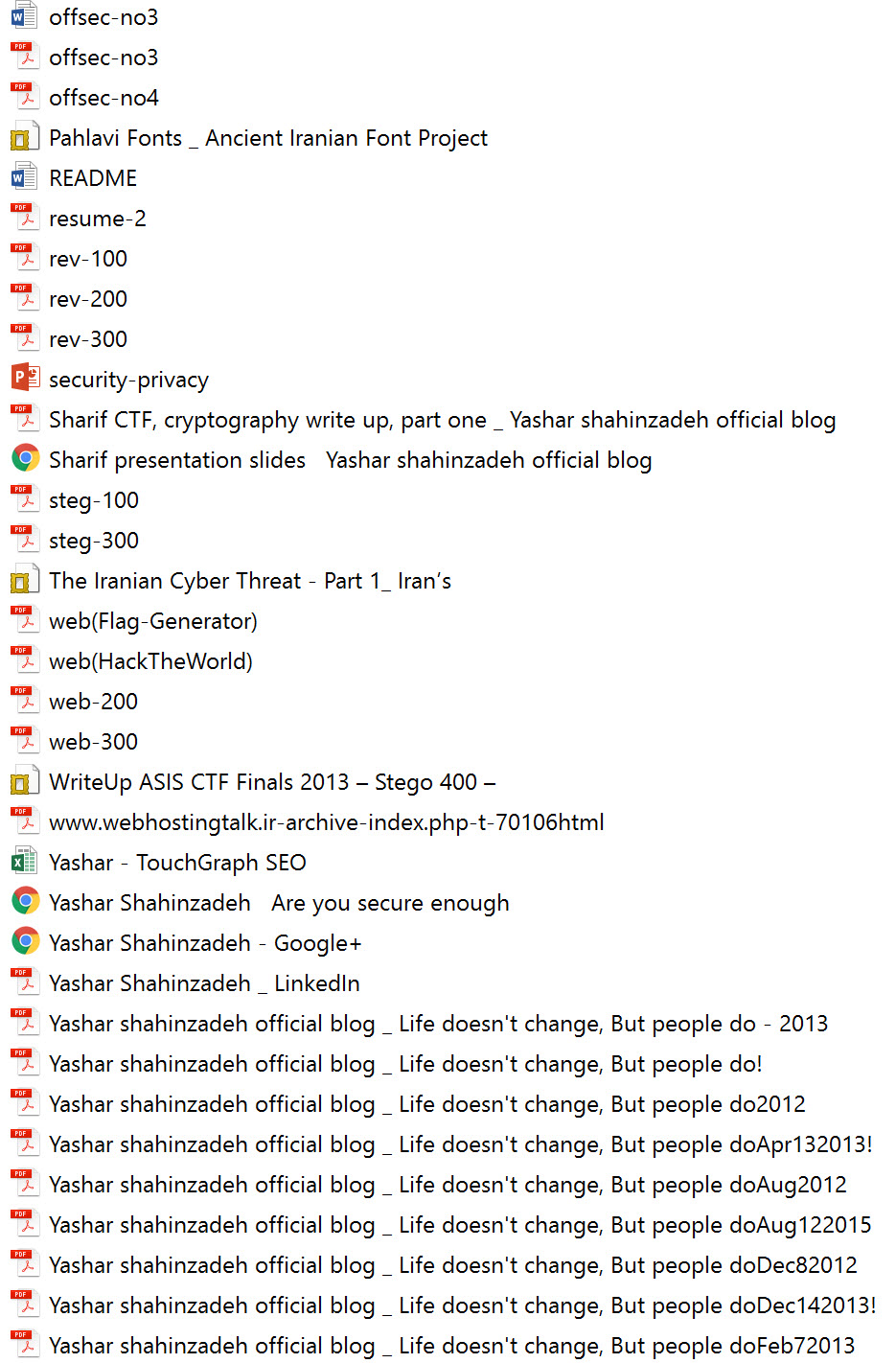
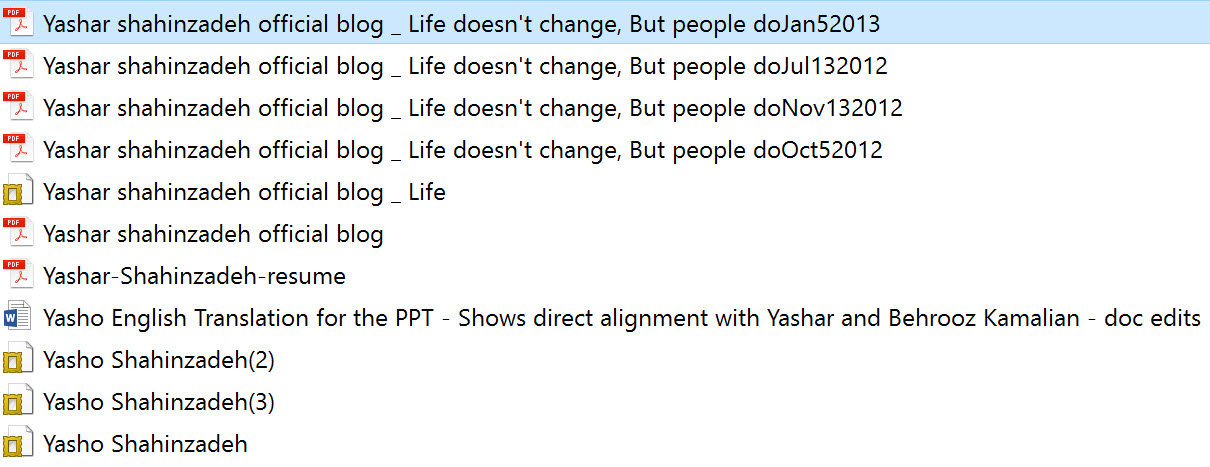
Yashar Shahinzadeh (Sc0rpion), a central figure in this event, pulled any and all data about the event from his blog. The blog itself was removed. Several organizations including HP attempted to acquire this information. Treadstone 71 provides this information below and via the links provided relative to the CTF exercise as well as other related data. More on Yashar and his new venture may be found at offsec.ir. We do not claim the files to be all inclusive but sufficient for review.
Cyber Counterintelligence Tradecraft Certification – http://www.planetreg.com/E81673415169740
Iran cyber practitioners continue to hone their skills driven from CERT activities at Sharif University, CTF participation, as well as holding their own CTF events. This in conjunction with study, research, and extensive government efforts to expand Iran’s capabilities surrounding anything offensive and defensive cyber, demonstrate their resolve at becoming a global cyber power. In the estimation of Treadstone 71, they have done so.
(Iranian hacking tools … https://cybershafarat.com/2016/08/30/iranian-hacking-tools/ )
Update – http://irancybernews.org/en/ICNA/6/338
There are 107 files totaling about 103MBs of data related to the CTF activities non-inclusively.
https://web.archive.org/web/20140208040711/http://blog.y-shahinzadeh.ir/
This site was taken down this year – previously very active for two years in CTF activities for Iran
http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/ Life doesn’t change, But people do! Tue, 18 Feb 2014 06:53:49 +0000 hourly 1 http://wordpress.org/?v=3.7.1 http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2086 Sat, 31 Aug 2013 18:44:12 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2086 […] at least). We (Me and Morteza) participated, and our team ranked 33. We proudly ranked first in the qualification round, though. It was due to lack of free time and weekend; previous CTF was held in the middle of the […]
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2085 Sat, 31 Aug 2013 18:06:43 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2085 […] at least). We (Me and Morteza) participated, and our team ranked 33. We proudly ranked first in the qualification round, though. It was due to lack of free time and weekend; previous CTF was held in the middle of the […]
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2011 Thu, 16 May 2013 16:13:16 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2011 It wasn’t absolutely an event officially termed CTF.
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2010 Thu, 16 May 2013 10:47:06 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2010 The first CTF competition held by Isfahan University in 6th ISC conference in 2004 see sbisc.ir
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2009 Wed, 15 May 2013 14:56:51 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2009 I think Sharif was the first
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2008 Wed, 15 May 2013 11:32:39 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2008 FYI, that was the first organized CTF sponsored by AEOI
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2002 Wed, 01 May 2013 18:17:50 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2002 Thank you, saying hi from Iran
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2001 Wed, 01 May 2013 06:29:20 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2001 Great Blog, saying hi from the United States
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-2000 Tue, 30 Apr 2013 06:36:49 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-2000 Hi,
Scoreboard changed finally.
We got the 4th place & scoreboard will be changed in these days.
our Blog
Best regards,
]]> http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/#comment-1999 Mon, 29 Apr 2013 11:30:27 +0000 http://blog.y-shahinzadeh.ir/?p=840#comment-1999 Hi, good job bro
adding host header in Burp is not needed for crawling
just add webhack-02.ctf and challenge IP to the hosts file
Yashar Shahinzadeh AKA Sc0rpion: Security consultant, Web security enthusiast, an expert in PHP exploitation and development. Experienced in working with some companies as security manager and auditor.
Morteza Khazamipour AKA Mormoroth: IT Expert. CEO @ ISCN Hacking team Pen-test and security research. Proficient on penetrating web applications in black-box mode.
Yashar Shahinzadeh official blog
Life doesn’t change, But people do!
Remote backups, WordPress plugins
Third parties have always been a danger for content management systems which are relatively secured (As a tangible example, Joomla or WordPress). I’ve recently been working on some WordPress’s plugins thanks to a penetration test project. Today I’m updating here covering two plugins’ analysis; another update will be allocated for some other plugins. Better WP Security and WP security scan are two plugins concerning about WordPress security. However, I feel being insecure with them. Some days ago, I reported scandalous security issues on mentioned plugins. In the rest of the post, I’m trying to expand them on by extra details. …continue reading
Logical vulnerabilities, inspiration
: All, News, web application: Written by Yashar Shahinzadeh: 01-02-2014
Logical vulnerabilities are much more dangerous, and they are often semi-harder to find compared with technical holes, and nobody can deny it. These days, everyone boasts on his penetration testing skills, having security projects have become commonplace. Furthermore, scanning a web application by a vulnerability scanner such as Acunetix is widespread. If we pay more attention, and being more realistic, we end up a professional penetration test doesn’t only comprise automatic scanning. However, a scanner would be a big help in crawling and even digging application for technical vulnerabilities in back-end components, notably within a black-box test of giant applications. …continue reading
About 4th Sharif university’s CTF
: All, CTF, Sharif CTF: Written by Yashar Shahinzadeh: 12-01-2013
Fourth Sharif university’s CTF was successfully held on 20 of November 2013 in in department of computer engineering. I took part in the contest with Respina team name, and we proudly ranked first! Further information can be found here. The rivalry was very intensive, and there were many Iranian hacking teams appeared in the local area. The scoreboard had a dozen of fluctuations which resulted in being an unpredictable ranking of teams, notably in the last hour of the contest that the scoreboard had been frozen, whereas we were staying at the first place in most times (except a short duration).
Limonade directory traversal filter bypass
: All, Bypassing, Local file disclosure, PHP: Written by Yashar Shahinzadeh: 11-18-2013
I’ve recently been occupied by a security research about detection and exploitation of well-known vulnerabilities. Consequently, I’ve had to develop some applications suffering various holes deliberately that I’ve carried out some parts by Limonade framework. While I was coding a page, I suddenly found a suspicious directory traversal filtering seemed to be bypassed easily at a glance. I spent some time that it was followed by setting up a page receiving a file’s name as input, opening and showing correspondent contents as a response.
About Nsec CTF + challenging question
: All, Bypassing, CTF, Linux, PHP, Server hacking: Written by Yashar Shahinzadeh: 10-16-2013
A few days ago, Nsec CTF organized by UITcert was successfully held in Isfahan locally. If I want to be more exact, it was begun from 9th of October (2013) for two consecutive days covering Jeopardy and Attack-Defense formats respectively. I participated in the CTF with Respina team; we were three people. However, we were allowed to be four as other teams mostly were. Two teams had to be eliminated on the first day, obviously the last two in the scoreboard. We proudly accomplished scoring first in both days. There were many changes in scoreboard throughout the period of contests (The …continue reading
CSAW CTF 2013 write-ups
: All, CTF: Written by Yashar Shahinzadeh: 09-22-2013
Well, the CSAW CTF has just finished few minutes ago, it was very fascinating and challenging. Did we rank 68 among? Participants and 1386 teams who accomplished solving a challenge at least! Some tasks required the good skill of programming, some needed intelligence within knowledge. From where I stand, the Recon tasks were amazing; the webs were hard and about my favorite category, I indicate Miscellaneous! Despite our action which we put every challenge we solve, this time, we decided to publish interesting ones, and hold the others. We will update this post and ha.cker.ir if we receive any request …continue reading
Brute force challenge?
: All, brute-force, Linux: Written by Yashar Shahinzadeh: 09-19-2013
Although brute-force attacks are useless these days, there are still some cases which conducting a brute-force attack might bring outstanding results. When we talk about brute-force, THC-Hydra is probably the first choice comes across your mind, after that there would be some alternatives. The story began about roughly ten days ago when I heard about http://www.pentesteracademy.com in Twitter and its challenges. Some after, I saw people solved the challenges mostly by coding within Python. Consequently, I decided to spend few hours to solve the challenges, in different ways albeit. I the following, I start putting the walk-through of four challenges …continue reading
Third sharif CTF online write-up (Final round)
: All, CTF, PHP: Written by Yashar Shahinzadeh: 09-12-2013
Last night I was searching for a file I’d lost, suddenly I found an interesting folder named ANS. There were final Sharif’s CTF write-ups which have never been published on their official site(?). The final round was held on February the 12th,2013 locally in the department of computer engineering for the third time. The web section challenges were categorized by Windows and Linux separately. Consequently, there are two write-ups in PDF format. I’ve written them in the Persian language, and there is no alternative for dear readers knowing English. Sharif CTF final round’s write-ups (Linux) Sharif CTF final round’s write-ups (Windows) …continue reading
ASIS CTF write-ups
: All, CTF, PHP: Written by Yashar Shahinzadeh: 08-31-2013
In general, I never take part in CTFs except some. Today, ASIS CTF was held with more than 150 teams (128 teams accomplished solving a challenge at least). We (Me and Morteza) participated, and our team ranked 33. We proudly ranked first in the qualification round, though. It was due to lack of free time and weekend; previous CTF was held in the middle of the week, and we were at our workplace, truly we were a team, not two people only. However, it’s finished, and this post is completely allocated to its write-ups. I put the Web section write-ups. …continue reading
Exploiting FCK editor
: All, Hacking, Hacking tool, PHP: Written by Yashar Shahinzadeh: 08-02-2013
In this update, I’m going through an exploitation of an unprotected FCKEditor located in a server. It must be noted that this post isn’t a new bypass or method, it’s a simple exploit I’ve been implementing in my penetrate tests. I’ve seen many administrators who have heard about file upload vulnerability removing HTML interface, and they regard this procedure as a preventive factor. However, it isn’t definitely, lack of HTML interface doesn’t mean that an attacker cannot exploit the up-loader. An efficient way would be restricting access or even updating FCKEditor (I currently don’t know whether it’s patched against old arbitrary …continue reading
| February 2014 | ||||||
| M | T | W | T | F | S | S |
| « Jan | ||||||
| 1 | 2 | |||||
| 3 | 4 | 5 | 6 | 7 | 8 | 9 |
| 10 | 11 | 12 | 13 | 14 | 15 | 16 |
| 17 | 18 | 19 | 20 | 21 | 22 | 23 |
| 24 | 25 | 26 | 27 | 28 | ||
Recent Posts
- Remote backups, WordPress plugins
- Logical vulnerabilities, inspiration
- About 4th Sharif university’s CTF
- Limonade directory traversal filter bypass
- About Nsec CTF + challenging question
Blogroll
- 0x0ptim0us’s blog
- Abbas Naderi’s blog
- Faryad’s blog
- http://pentesterlab.ir/blog/
- Me on Twitter
- Mormoroth’s blog
- Shabgard’s forum
- WebAmooz
Archives
- February 2014(1)
- January 2014(1)
- December 2013(1)
- November 2013(1)
- October 2013(1)
- September 2013(3)
- August 2013(2)
- July 2013(2)
- June 2013(1)
- May 2013(1)
- April 2013(1)
- March 2013(3)
- February 2013(1)
- January 2013(2)
- December 2012(2)
- November 2012(2)
- October 2012(2)
- September 2012(1)
- August 2012(4)
- July 2012(8)
- June 2012(2)
Categories
- All
- brute-force
- Bypassing
- Cross site request forgery
- Cross site scripting
- Cryptography
- CTF
- Farsi
- Hacking
- Hacking tool
- Java
- Linux
- Local file disclosure
- Man in the middle
- Mssql injection
- MySQL injection
- News
- PHP
- Physics
- Server hacking
- Sharif CTF
- web application
Meta
- Log in
- EntriesRSS
- CommentsRSS
- org
© 2014 – Yashar shahinzadeh official blog
https://cert.sharif.edu/?a=contentNews.id&id=124
https://cert.sharif.edu/ctf//p/6/contests/
https://cert.sharif.edu/ctf/p/7/contests-ctf/
https://cert.sharif.edu/ctf/p/9/contests-poster/
https://cert.sharif.edu/ctf/p/10/contests-workshop/
http://news.softpedia.com/newsTag/Izz+ad-Din+al-Qassam+Cyber+Fighters
https://cert.sharif.edu/ctf/p/11/contests-forensic/
CTF AEOI IR – write-ups – http://blog.y-shahinzadeh.ir/2013/04/aeoi-ctf-write-ups/ (2013)
http://ufologists.ufoctf.ru/98/write-ups/asis-ctf-finals-2013-stego-mysterious-points-writeup
http://asis-ctf.ir/fa/ (/en/ for English)
DID NOT FIND CTF AEOI for 2012. Only 2013. Links above.
Mr. Richman, a famous and rich person, has gone missing. The police have investigated the case, and found his laptop. They believe That a forensic analyst can give them a significant Insight on what has happened. As a forensic expert, you are provided with a VMWare virtual machine, which plays the role of Mr. Richman’s laptop. Further to aid you, you are also given Several logs of network packets sent and received by his laptop. Your task is to find the timeline of important events which affect Mr. Richman’s case. Moreover, you should find as much evidence as possible. The more you Reveal, the higher your score will be. Here’s the VM file links, split into 2 parts, and password protected: Download VM file part1 md5sum: 98C65E6669581423377F0C055B70A12F Download VM file part2 md5sum: 7Eeb500D0F198D8Ed56530Ad21E1E25D compressed files pass is’; a, Vlkhdvhk ‘ The Captured packets network is available here (password protected, too) Captured packets network Download compressed file pass is ‘Nhka’hiavdt’
Profile information of mormoroth@ymail.com
Name
Jamileh Azizinayaz (2011-10-25 12:20:05) (not verified yet) (Assumed bogus)
Nickname
cati (2011-10-25 12:20:05) (not verified yet)
Age
35 (2011-10-25 12:20:05) (not verified yet)
Gender
Female (2011-10-25 12:20:05) (not verified yet)
Location
Tehran (2011-10-25 12:20:05) (not verified yet)
Alireza Atfali – Magic Boy
Mormoroth & Magicboy
Mormoroth – Morteza Khazamipour
Potential Address:
Address: no. 10, 3rd arghavan, boostan sq, saadat abad, Tehran, Tehran, IR
Phone: +989939700
nic-hdl: mk2433-irnic
person: morteza khazamipour
e-mail:
پور الخزامي مرتضی
مرتضی الخزاميپور
address: no. 10 , 3rd arghavan,boostan sq,saadat abad, Tehran, Tehran, IR
phone: +989939700
source: IRNIC # Filtered
nic-hdl: da50-irnic
org: Ertebatate Shabakeye Day
e-mail:
source: IRNIC # Filtered
امن پردازش خوارزمی – Amn Pardazesh Kharazmi – ITSEC Team
Website: http://www.amnpardaz.com/
Also part of the team: https://www.linkedin.com/pub/mohsen-ahmadi/68/a28/b12
Obtain licenses from the Ministry of Culture – i.e., validation to hack
Twitter (Twitonomy – mentions of Stuxnet style attacks). It is a Stuxnet style tool – key point here is when you leave cyber weaponry on the battlefield, expect it to be reused against you. Great point for the report/analysis.
http://betabeat.com/2012/10/experts-think-muslim-cyber-fighter-attacks-on-u-s-banks-well-funded/
Look at TTPs here.
Images with text – always centered text – tendency
“Mrt. Izz ad-Din al-Qassam Cyber Fighters” MRT could be short for Morteza
MRT – no relation to military rank http://en.wikipedia.org/wiki/Rank_insignia_of_the_Iranian_military
Acronyms (English) http://acronyms.thefreedictionary.com/MRT
http://forums.deltafoxy.com/forum.php






You must be logged in to post a comment.