
Over the past few years, new terms have emerged to describe the constant state of conflicts around the world, in the form of concepts such as hybrid warfare, cyber warfare, gray zone conflict, misinformation, deceptive information, deep forgery, infiltration operations, and cognitive warfare. But they are only a few of the new terms that have…
Read More “Cognitive War All Encompassing” »

This material was prepared by Russian students of the course “HUMINT: Methodology” Seven Radicals “for communications” Klaus Martin Schwab (German: [klaʊs ˈmaʁtiːn ʃvaːp]; born 30 March 1938) is a German engineer, economist and founder of the World Economic Forum (WEF). He has acted as the WEF’s chairman since founding the organisation in 1971. Psychological picture Negotiation Behavior Prediction 1….
Read More “Klaus Martin Schwab
Psychology of the Seven Radicals” »
Treadstone 71 Cognitive Warfare Training – Recognized by Russian philosophers, political technologists, media managers, producers, journalists and TV presenters, military correspondents, bloggers, volunteers and organizers of assistance to the front, designers and artists, writers, poets and musicians, sociologists and psychologists. On March 11, 2023, the Skolkovo Technopark will host a forum dedicated to information and…

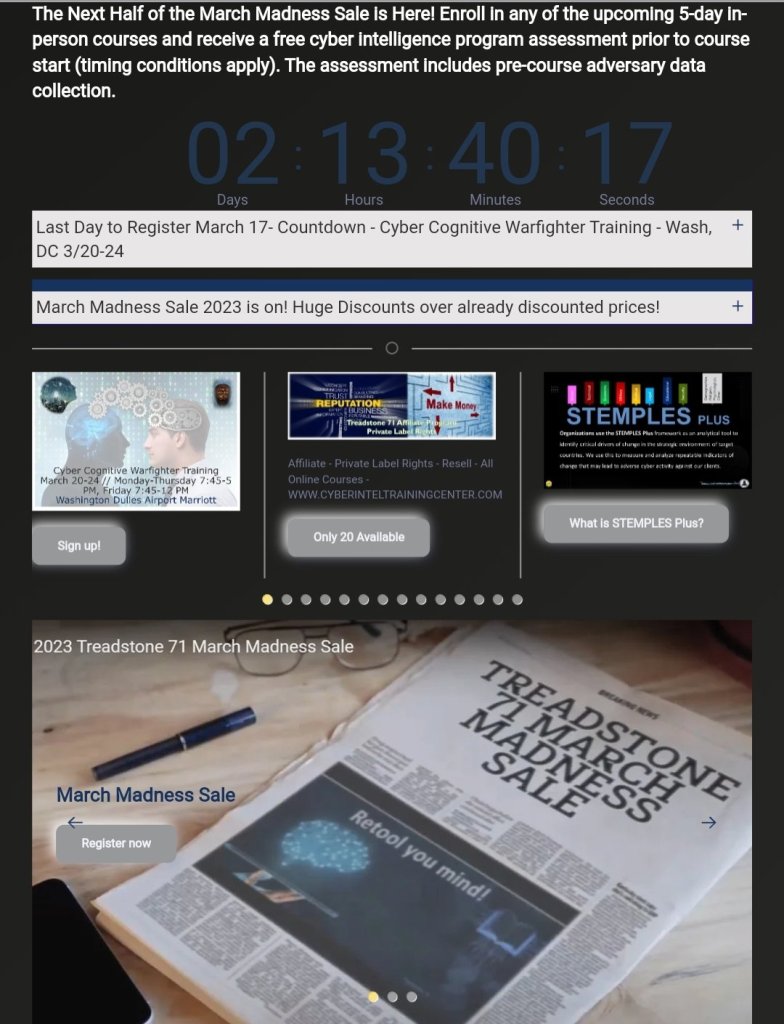
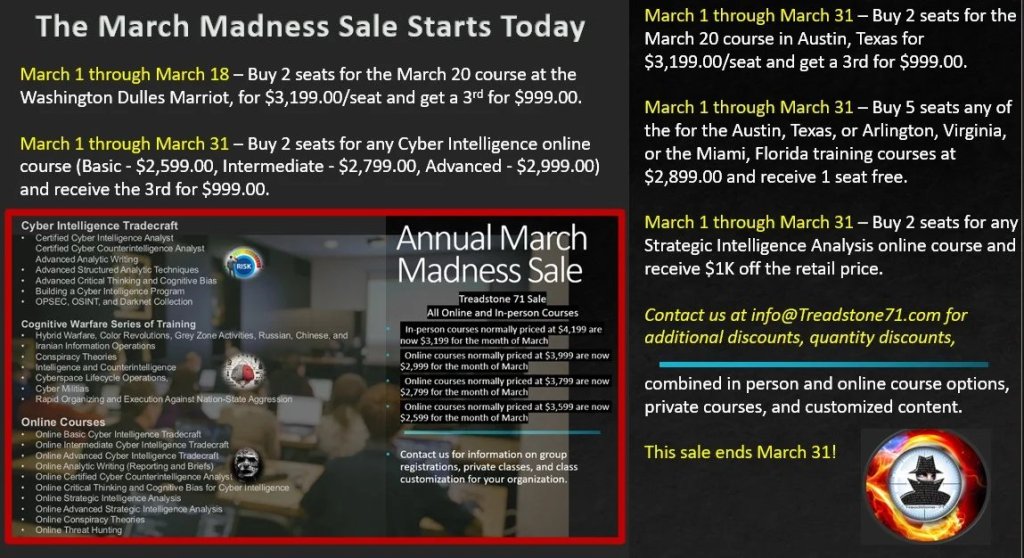
Our In-Person courses cover intelligence, counterintelligence, influence operations, how to build a cyber intelligence program, geopolitical and strategic intelligence, open-source intelligence, clandestine cyber human intelligence, persona development and use, and operational security in online environments. Our courses include: Cyber Intelligence Tradecraft Cognitive Warfare Series of Training Online Courses NOTICE: We use PayPal via our shopping cart….
Read More “MARCH MADNESS SALE Prices in effect through March 31 ” »


HALF MOON BAY, Calif., March 7, 2023 (SEND2PRESS NEWSWIRE) — Treadstone 71, LLC, the source for cyber intelligence, counterintelligence, hybrid, and cognitive warfare, announces new courses and services. “Targeted adversary data collection creates significant risk when seeking relevant information not available from threat intelligence feeds. Our operational security (OPSEC) training courses reduce risk to negligible…
Read More “OPSEC a Critical Requirement for Open-Source and Dark Net Collection” »

https://tinyurl.com/T71MM #Training #Courses #CybersecurityIntelligence #CyberIntelligence #OSINT #OPSEC #Darknet #HybridWarfare #CognitiveWarfare #ReferenceGuides #ConspiracyTheories #CyberMilitias #CounterIntellignece #InformationOperations #SATS #Analysis #AnalyticWriting #Customized #Private #Online #inperson

OPSEC methods, online anonymity, persona creation, secure browser configuration with no verified leaks. OSINT and Darknet searching, Social media searches and collection, Personality identification using Myers-Briggs, the Big 5, the Dark Triad/Pitch Black Tetrad, the Psychological Techniques of the Seven Radicals, and the Nine Enneagram Type. Methods and TTPs of cyber HUMINT tactics, campaign development,…
Read More “Cognitive Warfighter” »

Effective information framing is critical to the success of an infiltration attempt. If you can make a topic “socially, personally and emotionally” relevant to your audience, it will be harder for them to ignore you. According to Mark C. Suchman’s research, “legitimization” in society is divided into three general categories: A.n effective digital narrative in…
Read More “Frame the narrative – Control it” »
In the history of China, the elements of combined wars have often included important components of “conflict and war” with neighbors. Ancient Chinese rulers basically used four methods to neutralize their problems and challenges. The first approach was to use the barbarians to fight the barbarians; In this case, by using wild mercenaries and creating…
Read More “Deception and gray area in classical Chinese military literature” »

You must be logged in to post a comment.