Russian SVR appeal for information. Use of Tor, Tails, and PGP advised. “InformBuro-Southern Federal District”
IMPORTANT
If you become aware of the facts of crimes committed or being prepared not only on the territory of the Russian Federation, namely:
– about terrorism and related acts (assistance, calls for terror, etc.);
– on the taking of hostages or preparations for the capture;
– about an illegal armed formation;
– about the hijacking of an aircraft, watercraft or railway transport or preparation for hijacking;
– on illegal actions with nuclear and radioactive materials;
– about preparation for encroachment or encroachment on the life of a statesman or public figure;
– about the violent seizure of power or preparation for it;
– about preparing for a military mutiny;
– on preparations for an attack on diplomatic missions;
– any other activity related to international terrorism
If necessary, we will assist in proper and timely informing the responsible employees of the competent services and departments
If you have any information about impending terrorist attacks on the territory of the Russian Federation, you can contact the FSB of Russia by phone:
+7 (495) 224-22-22
8 (800) 224-22-22
If you have any other valuable (important, useful) information about the events and circumstances listed above and/or others, and are ready to share this information while in a hostile environment, please use the secure channel of communication with the Russian Foreign Intelligence Service.
Anonymity and confidentiality are guaranteed in all cases of appeals.
FOREIGN INTELLIGENCE SERVICE OF THE RUSSIAN FEDERATION IN COMMUNICATION
On the website of the Foreign Intelligence Service of the Russian Federation there is an inconspicuous link – Report Information (“report information”), this is the only phrase in English on the main page of the site.
NOTE: THE LINK BELOW IS TO THE SVR
The link leads to instructions for sending an appeal to the “virtual reception” of the SVR, located on the darknet (“shadow Internet”).
Dear visitor!
Dear visitor!
If you are outside Russia and have important information regarding urgent threats to the security of the Russian Federation, you can safely and anonymously share it with us via the virtual reception system (VRS) of the SVR over the TOR network. Our onion address is:
If you are located outside of Russia and have important information about threats to the security of the Russian Federation, you can send it to us in a secure and anonymous way through the Service’s virtual reception in the TOR network at:
svrgovru24yd42e6mmrnohzs37hb35yqeulvmvkc76e3drb75gs4qrid.onion




Sites in the .onion domain zone are not accessible through regular browsers and are not indexed by popular search engines.
This is the first darknet reception among all European intelligence agencies.
The reception is intended for those who “are outside of Russia and have important information about threats to the security of the Russian Federation.”
Sending information is offered in a “secure and anonymous way” according to “simple instructions”:
first download the Tor browser (if the resource is blocked, use a VPN) or the Tails operating system (you can even use a flash drive).
These solutions encrypt Internet traffic and pass it through three random nodes, which can be located anywhere in the world.
Next, the visitor is invited to go to the reception site in the .onion zone, enter a verification code (to exclude calls from bots – programs that imitate human actions) and copy five random words in English: they will be a verification phrase for further interaction with the special service. They are best memorized, not written down.
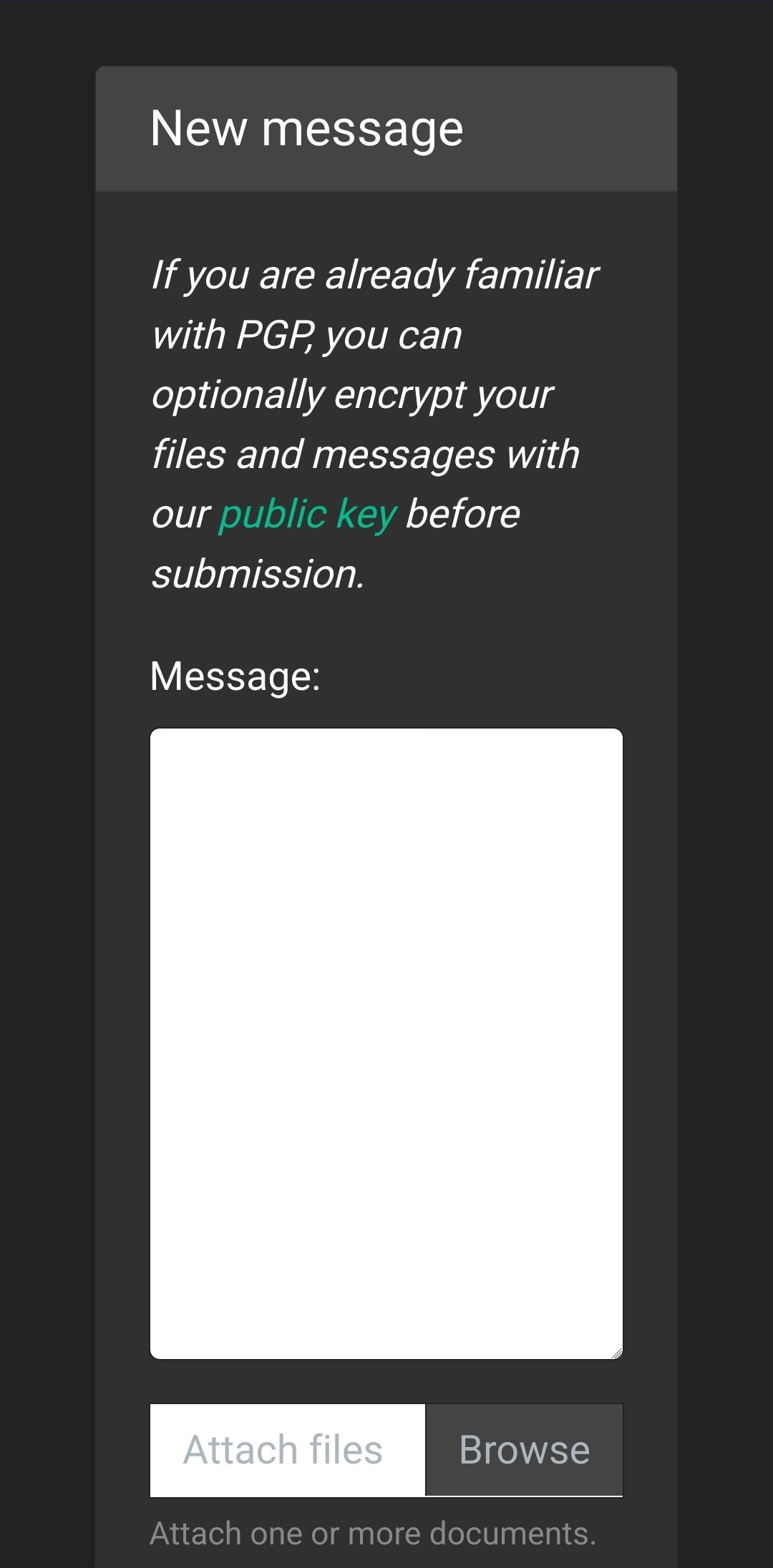
Following this, a form opens for sending files with a total volume of no more than 15 megabytes and text of almost any length.
The virtual reception, in case of success, will inform the sender with phrases in English, the translation of which is: “Success! Thank you for sending us this information. Please check the answers later” (this is what the verification phrase is for).
If you know how to work with PGP, then as an additional security measure, we recommend that you encrypt your message to the Russian Foreign Intelligence Service using the following public PGP key (see paragraph 5 of the Instructions)
—-BEGIN PGP PUBLIC KEY BLOCK—–
mQINBF7bruoBEACb78LwhlBJDhT707sK7MlFGB0S8qCaSQdUVzMAdQ5kW9hB/FJV
f1FmO4szUPvWCwHVvynM8JCBfRM6E2jaET24yxJOJbEOKNYEtMCCe2+uhUVKe4pc
w6GzmD0g1ODfW3mdnlF3DNokBKAd85sB3/owJhxBbwBUPEUmk+DVSCAiM8paO8pT
b89BoqN63hdal8fCO8BtNngl3oI+xS3kKRCWkn5IuEZdDxCUqB8CzX9QMGX84DhH
wlHvvFuqOpDJt07ULh3a/T4QxoLCYQYS+a7KWmZQhObe/4ecWOrxKHrugB/cXzGu
4V+02OKB9Gq03AVSLhfO50yIhoggHEDyIvDzFaBRcfZxtIDXY2F49A+VWaLLixYt
ZixrrK0HMEJMvSoXceQZU2g5Fi7qTCwuOxirhq0zOlI/orAQTHVthcmBYqt2jX1X
7075/lmjJd0mS3hqofOYfbkTQutYI8hjXqFfcIOqkhNwyiGge9/qejULy29MoEir
jvB5sUg9joI77LjoE2e7v1NBq2XHSyMFfAkr9D2Dd/qYiMBgyhjBUGwIs7BmDcES
8fRwJynRgUElX1YiREIMRtCvxz+GwhF7Smnu1KXqeo7OotKI4783Qp0R+RIcaczb
VmWnaK6v5TVaxGO+0Yw8eFjts/UTrrECcc9D7LYC9DzFmb6fpdKwQl/cUQARAQAB
tB5mZWVkYmFjayA8ZmVlZGJhY2tAc3ZyLmdvdi5ydT6JAjkEEwECACMFAl7bruoC
GwMHCwkIBwMCAQYVCAIJCgsEFgIDAQIeAQIXgAAKCRDyY8kgehzDs0MAD/4yx68x
ijVJSoRx/ArI4g4MBK9h1f76aQtIsisQZdysS0gI9TXiOiTH+ncezzjLl6dpogq8
06MxSKX5xqWTdYzuHmJYmk51mDOzLV5B5wu/hz7FJ/JWow8qX3S0T1kGZiAhx1l7
lgtZ2fSCgad7XEWUIQBL93s0wqYfr3Tk1ZRLrFx+ds29IlP3xHz4MZhvEcbgoWUo
9NMefp5nzLwTNcyKOs14VA8cPR6i0DboPRGO85WW1mVFl+Uii76HRqNVLy30dgXt
6VPYVgAh1Tki2OX9W2SFwp2q97y9LSpYZlwZBZgS2k6FiCj59FCUdJWe3PBZ+sQR
kXS5/Nh/UUqHH++Cpedgu9RwG/jpjMHOg4zOrdx4UT5a52/MhX/7nqmG2s99c3tx
03I4m9dSe9S/pvfE6q3+eQrb3AFgixhpzlRCJulEcMd4HerfpAJkRJDKQojkG8tR
aV9FEDz669mFlUtgRBTEp7TMT2/JbkreqONQ/ycL7KRXRLTM7Ql0oL3Xzuddio2Y
ic2R0/03sTVENblMysQvUDw9IOEV+PtWRSwosa7YxwcEYkOwtMjOsGjJ6CtbAq3d
ByNhS+9lX6QM9VKtge5JwC519emSDEKnt4SvEwRcWLnWU90+rEBPsIou3HFEwQ8a
YV9tCx2MYia8e/yz6VsSpecVVkB6wWroP33oWLkCDQRe267qARAAwhrcr4W0tBOW
Xo++XlsS55Efy8bhM+H/ETP1Z8VhdgbC8LwmTAeCWp/FztoblhNGUlBfvy8ZqHS9
3D5U/SQo+WOBuvaQ28RtY/0JCML6Ms+u0W1UE2TbM499TQMO3xZWozacy7qrkg0O
SCL1JQ0YLLPdUa9T9I2ZUrplww7b/wN+NFRUkPd5tDsPbKKul0aw4y0IJVSIhXU4
XrQUX0iff5jIymzqEr1u15iEX6AwvwT3iHNCEhr0lWe7KVnjr3pxG1tlBS5cECrp
1D3twOCTJrQKhsJBaPNG8yhj4hHG0iPmgb4SLonRwyzoRFg9/F7ALig4P26lmN67
3UYpTr4jGxBiAPyMohzj4mWfDjp95blIs7c1Yf1DcqhO/ODAX0qtlWivp/uNB73p
ry/ixPP18YrDnCEzW4U8uJ/yiony4U9O0G26GjtEgB7ZGryk6fToRepCd8hL0hsM
p3iLxm5LYvtDw4EExTNksNLgxIp7KNN+/tb0o7b4Y8UoG6fVMpywVID6iKeyIiVW
5KhKRRYCw84VMWs5yl6igEc1FEplAw804zANIqM2J/QBfgplstrhJ3Y6wkHFEblT
8TvTqGr5MJzkSr1ZxnX6uVctKR8VTIHy7gHQ3G3Z75saNvcU+4qqNg/0PfLbnW/O
79x5UiIZa2vNaIl1kSRn98YsMKEYlk0AEQEAAYkCHwQYAQIACQUCXtuu6gIbDAAK
CRDyY8kgehzDs/VcD/9y7TtPthPTgkWGlnCXl+wL9BWFnumbQrYq7SQ5AauI86BH
5LCjweoPcgUkG3GF0o81NEZpWh+ZDl0h5VzEdc7bvQt9ZP16czuwhyZiK+b2me/n
Lutx9b2fUePRfKBnhm1vomShcvOXH3fmp80w9JsB92Wj56Ajo5WR3hIcHHheOSRa
63K/rzdQZ7UIDPDVIROEHMJciuo8V2H+FNvHkjSJPkgnAj17+XqvAEUdMF9hTHUN
uM2AajUrpWB3OXpbTMCDWbXoBWMDfVki7EFiFftXkLnaExqk2A9zgjEy+nht9S1y
l6NXwM6McpHxClzSoZDTDugywUPF3Izx1F5tca0DJeoyNTs3Gp6CcEnV9Qs9F5MW
0iw2mi5eF1uHV0JOQGLkFQWuGeyoe9Nio3L9Ho3uEzInQ/V9uvo84RbfarmmVXFY
lVjF2icAMzU3eTOGqAUIS10XFADYxRfogqG25jjjwFS4b/9YJqsImE8e+x75f+z6
0Nx0SAfvURUNjqPcTyQhpnlHPg8ayZzECLF2NCeLRQo8s/zNd3IxRJpdbgjgLK4A
L7/Zek4rAP8W0fc2wcFZjuwRCvPWvIID3mP1EsUru5TLSfkxo2B03HzPB6WMyH5v
iSzLXvjpn272L9B1TE8FFBC6Dl0U74+np+lHVM+qIEfWE8KMK3nVEqIXBfzGcQ==
=5vim
—–END PGP PUBLIC KEY BLOCK—–
Third parties will not be able to read the correspondence, even if for some reason they get access to it.
The legitimate addressee – in this case, the Foreign Intelligence Service of the Russian Federation – on the contrary, will be able to decrypt the letter using their cryptographic key.
In the materials of the US National Security Agency, published by its former employee Edward Snowden in 2014, it was claimed that letters encrypted with PGP were invulnerable.
If you are in a hostile environment and are afraid for your safety, then do not use smartphones, computers and other electronic devices associated with you or your friends to access the network and maintain communication with the Russian Foreign Intelligence Service.
Correlate the importance of the information you transmit with the measures taken to ensure your safety!
If you are in a hostile environment and/or have reasons to worry about your security, do not use a device (smartphone, computer) registered to you or associated in any way with you or people from your personal settings for network access.
Relate the importance of information you want to send us with the security measures you are taking to protect yourself!
Please do not send information regarding media inquiries, press releases, archival research or other such matters through this channel.
Please do not send information concerning media inquiries, press releases, archival research and other similar issues through this channel.







You must be logged in to post a comment.