The global cyber threat landscape of 2026 represents a critical and highly volatile inflection point in adversarial operations. This era is characterized by the unprecedented convergence of generative artificial intelligence, industrialized extortion networks, and rapidly accelerating exploitation timelines that render traditional, human-reliant defensive postures structurally obsolete. Within this hostile environment, a newly designated threat actor, tracked under the moniker M3RX, has emerged within the underground Ransomware-as-a-Service (RaaS) ecosystem. Initial telemetric observations and dark web tracking indicators suggest that M3RX represents a highly automated, opportunistic ransomware and extortion syndicate operating with significant geographic and sectoral breadth. The emergence of M3RX occurs against a macro-environmental backdrop where traditional defensive paradigms are failing; adversaries are moving with devastating velocity, and the democratization of sophisticated tradecraft via generative artificial intelligence has fundamentally altered the economics of global cybercrime.
This intelligence dossier provides an exhaustive, multi-dimensional analysis of the M3RX threat actor, situating its observable activities within the broader contextual realities of the 2026 digital battlefield. By synthesizing dark web telemetric data, global threat landscape reports, advanced behavioral analysis, and signal-to-noise disambiguation techniques, this report delineates the operational contours of M3RX. The analysis explores the profound implications of the actor’s automated publication infrastructure—evidenced by highly anomalous, machine-speed data leak synchronizations—its victimology profile, and the hypothesized tactics, techniques, and procedures (TTPs) it employs. Furthermore, this dossier addresses the systemic vulnerabilities that permit such actors to flourish, including the severe escalation of malware-free intrusions, the critical vulnerability of edge devices, and the shrinking window for defensive intervention known as breakout time.
The objective of this comprehensive report is to equip security leadership, incident responders, and strategic planners with the nuanced, actionable intelligence required to preempt, detect, and neutralize the threat posed by M3RX. Furthermore, it serves as a critical examination of the epistemological challenges inherent in modern threat actor categorization, providing a framework for identifying legitimate indicators of compromise amidst the vast ocean of telemetric noise generated by automated intelligence ingestion engines.
The Ontological Challenge of Threat Actor Categorization
The formal tracking, naming, and categorization of cyber threat actors remain complex, often highly fragmented endeavors across the global cybersecurity industry. Traditional intelligence reporting frequently struggles to capture information in formats that are simultaneously comprehensible to human analysts and seamlessly integrated into machine-actionable defensive architectures. The foundational problem lies in the epistemic divide between strategic intelligence—which relies on narrative, intent, and geopolitical context—and tactical intelligence, which relies on purely technical indicators intended to be consumed directly by cyber defense products, such as firewalls and endpoint detection systems.
When a “New Event” is detected and categorized under the broad umbrella of Cyber Threat Intelligence with the specific tag “New Threat Actor,” analysts must immediately confront the structural deficiencies of industry nomenclature. The cybersecurity vendor ecosystem is perpetually plagued by confusion regarding naming conventions. This confusion is driven largely by commercialization pressures, proprietary intelligence silos, and marketing initiatives. Different intelligence providers—such as CrowdStrike, Palo Alto Networks, and Mandiant—frequently assign disparate, proprietary monikers to the exact same adversarial group. For instance, a single state-sponsored entity might be tracked simultaneously as APT28, Fancy Bear, STRONTIUM, or Iron Twilight depending on the vendor dashboard being utilized.
This lack of standardization creates significant friction for threat intelligence analysts attempting to synthesize global telemetry. When the entity M3RX is flagged as a new actor, the immediate analytical imperative is to determine whether this represents a genuinely novel syndicate operating with bespoke cryptographic primitives and unique infrastructure, or whether it is merely a rebranded affiliate of an existing RaaS cartel attempting to shed the scrutiny of international law enforcement. The fragmentation of the ransomware ecosystem frequently sees operators from dismantled groups—such as Conti, Hive, or ALPHV—resurface weeks later under new banners, utilizing slightly modified encryptors but identical upstream access methodologies.
To mitigate this pervasive confusion, the industry must increasingly rely on standardized behavioral frameworks, primarily the MITRE ATT&CK matrix. As highlighted by principal security engineers within the field, the MITRE framework provides a reliable, centralized resource to demystify aliases and strengthen defenses based on shared adversary behavior. The framework categorizes the specific Tactics, Techniques, and Procedures (TTPs) utilized during an attack rather than relying on arbitrary marketing aliases. Effective threat actor intelligence does not stop at assigning a name; it requires mapping every exploited vulnerability and observed action back to specific MITRE ATT&CK tactics, thereby connecting the technical weakness directly to the business risk and the operational profile of the attacker. For M3RX, future analytical efforts must focus entirely on extracting its behavioral DNA from forensic artifacts to map its operations against known MITRE groups, transitioning the intelligence from theoretical categorization to actionable defensive posture.
Telemetric Genesis of M3RX and Ecosystem Positioning
M3RX was formalized as a tracked entity following a sudden and highly concentrated burst of activity on specialized open-source intelligence platforms designed to monitor ransomware groups, dark web markets, and threat actors. The primary mechanism for identifying these new actors involves continuous, automated scraping of Tor hidden services, decentralized networks, and dedicated leak sites (DLS) operated by extortion syndicates.
As of late April 2026, the global ransomware intelligence ecosystem tracks over 566 distinct operational groups and has recorded more than 30,475 individual ransomware posts tracked in the open. The environment is highly dynamic, characterized by continuous fluctuations in operational volume. For example, recent weekly activity metrics indicate the tracking of 167 active posts across 32 active groups. While established entities like Qilin currently dominate the volume of observed attacks—accounting for over 28% of recent activity with a staggering 235.7% week-over-week increase in posting frequency—the entrance of M3RX alongside other novel groups signals the continuous fragmentation and regeneration inherent within the RaaS economy. Other notable movers in the same temporal window include The Gentlemen, seeing a 142.9% increase, and Lockbit5, attempting to re-establish dominance following previous disruptions.
The intelligence collection methodology underlying these platforms is highly sophisticated, utilizing torrent intelligence, passive swarm scanning, IP/Autonomous System Number (ASN) pivoting, BEP-48 tracker scraping, and webseed mirroring to map the infrastructure of these illicit organizations. Currently, the ecosystem tracks over 1,315 swarms, 352 of which remain alive, and monitors cross-group IP pivot signals to identify infrastructural overlap between seemingly disparate threat actors.
The classification of M3RX as a new entity is driven by its sudden operational cadence and its distinct dedicated presence within these complex intelligence directories. The group has been confirmed to utilize standardized extortion documentation, and is listed systematically among groups with known notes, including established syndicates like Akira, BlackBasta, and Lockbit. Although the specific textual contents of the M3RX ransom notes for individual victims like dmschweiz.ch have not yet been fully parsed into centralized, human-readable repository displays, the group’s infrastructural footprint is undeniably active. The emergence of M3RX underscores a persistent operational reality of the 2026 landscape: the barriers to entry for conducting global extortion campaigns have been drastically lowered, allowing nascent groups to rapidly deploy cloud-hosted infrastructure and execute successful compromises on an international scale without requiring the multi-year development cycles of legacy advanced persistent threats.
Disambiguation of Telemetric Noise: Filtering the M3RX Signal
A critical component of advanced Cyber Threat Intelligence is the systematic disambiguation of telemetric noise. Automated threat intelligence platforms, Security Information and Event Management (SIEM) systems, and broad open-source intelligence (OSINT) scrapers frequently utilize exact string matching to identify potential Indicators of Compromise (IOCs). When a new string, such as “M3RX”, is added to a global watchlist, ingestion engines will recursively search historical and contemporary databases for any occurrence of this character sequence. This invariably results in the generation of massive volumes of false positives, which human analysts must meticulously filter to preserve the integrity of the intelligence pipeline.
An exhaustive historical query of the “M3RX” string across disparate public databases yields a high volume of critically deceptive artifacts that must be explicitly decoupled from the ransomware threat actor. The failure to disambiguate these sources can lead to catastrophic defensive misconfigurations, such as the accidental blacklisting of critical supply chain components or the generation of spurious regulatory compliance alerts.
Financial and Corporate Filings (EDGAR Database Artifacts)
A primary source of telemetric noise originates from the automated scraping of the U.S. Securities and Exchange Commission (SEC) EDGAR database. Automated ingestion of these highly formatted, legacy text documents frequently encounters Optical Character Recognition (OCR) errors or highly specific, proprietary alphanumeric formatting codes that inadvertently match threat actor designations.
- Cooper and Ocular Sciences Acquisition (2004): A historical SEC filing detailing the acquisition intentions between Cooper and Ocular Sciences contains a corrupted text block explicitly containing the string “M3RX” (`… M3RX”?%/49D4-5+%] This is definitively an artifact of legacy document encoding or OCR hallucination and bears zero relation to the cyber threat landscape.
- Symantec Earnings Transcripts (2005): Similarly, a transcript of a Symantec Corporation earnings call involving Enrique Salem, SVP of Security Solutions, features a corrupted transmission block containing the sequence (… M3RX#ET+R,GBIRI:”,_(Q,W8#,WRC.4#FL9X…). The proximity of the word “Symantec” to the string “M3RX” in an automated SIEM ingestion could falsely trigger an association between the security vendor and the threat actor, requiring immediate human override.
- Neuralstem Corporate Governance (2018): A filing regarding the independence criteria of directors at Neuralstem, adhering to NASDAQ regulations, features a similar cryptographic or encoding artifact (… M3RX>E2@HT@AJIJZHCI?8P_&3^:+U]\G>V*[IC…).
- Regions Financial Corporation (2018): An 8-K filing from Regions Financial Corporation contains a sequence matching the string (`… M3RX]^9I?’>9/MR/O?:Q?GNM_EJ?Y2:-PGEQ
In all aforementioned instances, the presence of the string is purely coincidental, representing base64 encoding errors, corrupted PDF-to-text conversions, or legacy SEC transmission artifacts.
Operational Technology and Supply Chain Intersections
A more dangerous category of telemetric noise arises when a threat actor designation mirrors a legitimate product catalog number, particularly within Operational Technology (OT) and critical infrastructure supply chains.
The string “M3RX” is heavily embedded within the product catalogs of Grace Engineered Products, specifically pertaining to their Permanent Electrical Safety Devices (PESDs) and GracePort configurations. These devices are utilized to safely verify the presence or absence of voltage from outside an electrical enclosure, mitigating arc flash risks and ensuring compliance with NFPA 70E / CSA Z462 safety standards. The catalog explicitly lists multiple part numbers containing the exact string:
- P-S11S21-M3RX: A Voltage indicator with flashing red LEDs, horizontal mount.
- H-S10-M3RX-EZ-V: A Voltage indicator multi-environment vertical mount kit.
- H-S11-M3RX-EZ: A Voltage indicator multi-environment horizontal mount kit.
If an automated threat intelligence feed were to indiscriminately ingest “M3RX” as a malicious indicator, a naive EDR or firewall configuration might begin blocking traffic related to the procurement, updating, or digital documentation of these critical safety devices. This exemplifies the critical necessity for context-aware intelligence; a string is not inherently malicious, and its domain context must be validated prior to the implementation of defensive countermeasures.
Public Health Data Artifacts
Finally, the string appears in completely unrelated public data sets, such as the New York State Department of Health restaurant inspection databases. A specific UUID identifying a data row for an inspection at the “Best Friends Family Diner” in Plattsburgh, NY, features the identifier row-w2td-m3rx.35sj. This further underscores the stochastic nature of alphanumeric string generation in modern database architectures and the necessity for rigorous, human-in-the-loop intelligence validation.
| Domain Context | Artifact Description | False Positive Classification Rationale |
| SEC EDGAR Filings (2004-2018) | Corrupted text blocks in Cooper, Symantec, Neuralstem, and Regions Financial filings. | Legacy encoding errors, base64 corruption, or OCR hallucinations. No cyber context. |
| Operational Technology | Grace Engineered Products PESD part numbers (e.g., P-S11S21-M3RX). | Legitimate hardware catalog identifiers for electrical safety voltage indicators. |
| Public Health Databases | NYS DOH row UUID identifier (row-w2td-m3rx.35sj). | Randomly generated database primary key. |
Table 1: Disambiguation of Telemetric Noise and False Positive Identification for String “M3RX”.
Having successfully filtered this systemic noise, analysts can focus exclusively on the verified, dark web telemetric data related to the M3RX ransomware syndicate.
Victimology Profile and Opportunistic Exploitation Strategy
An analysis of the verified, compromised targets published by the M3RX operational infrastructure reveals a distinct lack of geographic, geopolitical, or sectoral concentration. Instead, the targeting profile indicates a fundamentally opportunistic exploitation strategy. This methodology is highly indicative of an automated entity relying heavily on the mass scanning of internet-facing vulnerabilities or the bulk, indiscriminate acquisition of compromised corporate credentials from Initial Access Brokers (IABs) operating within illicit marketplaces.
The known victims, explicitly claimed by M3RX on their dark web extortion portal, span multiple continents and sovereign jurisdictions, encompassing North America, Europe, and Oceania.
| Victim Domain | Probable Sector / Vertical | Geographic Location | Publication Timestamp (UTC) |
| rotak.it | General Commercial / Unknown | Italy (Europe) | 2026-04-23 20:52:54 |
| rainforestclean.com | Commercial Services (Cleaning) | Global / Non-Specific | 2026-04-26 12:44:06 |
| airdriephysio.com | Healthcare (Physiotherapy) | Canada (North America) | 2026-04-26 12:44:07 |
| primeproperties.com.au | Real Estate / Property Mgmt. | Australia (Oceania) | 2026-04-26 12:44:08 |
| anvilarts.org.uk | Arts and Cultural Organization | United Kingdom (Europe) | 2026-04-26 12:44:09 |
| dmschweiz.ch | General Commercial / Logistics | Switzerland (Europe) | 2026-04-26 12:44:10 |
Table 2: Verified M3RX Victimology and Publication Timeline.
This widespread geographic footprint stands in stark contrast to advanced nation-state nexus actors, who typically restrict their operations to specific regions aligned with strategic, geopolitical, or military objectives. M3RX’s global reach perfectly mirrors the behavior of financially motivated eCrime syndicates that prioritize revenue generation over strategic disruption.
The inclusion of the United Kingdom, Switzerland, Canada, and Australia in their targeting matrix aligns with broader macro-intelligence observations. Global data sets dictate that high-GDP Western nations bear the overwhelming brunt of cybercriminal focus. The United States, for instance, represents nearly 25% of all observed threat activity globally, followed closely by the UK and Germany. This volume directly reflects economic realities; organizations within these regions are perceived to possess the financial liquidity, cyber insurance policies, and operational imperatives necessary to meet exorbitant ransom demands.
However, the specific sectoral targeting of M3RX is highly instructive. The group is not engaging in “Big Game Hunting” (BGH)—a strategy focused exclusively on Fortune 500 conglomerates, critical national infrastructure, or major financial institutions. Instead, M3RX aggressively exploits the “soft underbelly” of the global digital economy: the small-to-medium business (SMB) and mid-market enterprise sectors.
Entities such as regional arts organizations (anvilarts.org.uk), localized healthcare clinics (airdriephysio.com), and property management firms (primeproperties.com.au) frequently operate under severe structural disadvantages. They possess constrained IT budgets, heavily rely on legacy or unpatched infrastructure, and generally lack continuous, 24/7 internal security telemetry or dedicated Security Operations Centers (SOCs). These organizations are prime candidates for rapid encryption and data exfiltration operations.
This opportunistic strategy is highly economically viable within the industrialized framework of modern RaaS operations. By fully automating the attack and extortion lifecycle, threat actors can generate substantial aggregate revenue by extorting smaller, highly reliable sums from a massive volume of mid-market victims. This approach allows the group to fly under the radar of major international law enforcement task forces—such as Interpol or the FBI—which are typically mobilized only when critical infrastructure or highly public multi-billion-dollar entities are compromised.
The Automation Imperative: Analyzing the Five-Second Publication Window
Perhaps the most revealing indicator of M3RX’s technical sophistication, backend infrastructure, and operational methodology lies in the precise chronometry of its victim data publications. An analysis of the group’s public extortion ledger, captured via continuous tracker scraping, reveals a highly anomalous and critically important temporal pattern.
On April 26, 2026, the M3RX infrastructure published the details of five distinct corporate victims within a meticulously synchronized, sequential five-second window.
- 12:44:06 UTC: rainforestclean.com
- 12:44:07 UTC: airdriephysio.com
- 12:44:08 UTC: primeproperties.com.au
- 12:44:09 UTC: anvilarts.org.uk
- 12:44:10 UTC: dmschweiz.ch
This exact, one-second interval between consecutive, distinct publications provides profound insight into the group’s operational mechanics. The processing of a victim onto a dark web Dedicated Leak Site (DLS) is a complex, multi-step procedure. It typically involves authenticating with the Tor hidden service, generating a unique victim identifier URL, uploading preliminary sample data or proof of compromise, formatting the extortion demands, inserting standardized HTML/CSS templates, and committing the entry to the backend database.
Human operators, even those working with highly optimized administrative interfaces, do not execute multi-variable publication tasks with perfect, uniform, one-second cadence. This telemetric signature definitively proves the utilization of advanced, API-driven automation and command-line scripting at the infrastructural level. The threat actor has decoupled the human from the publication process, relying on an automated cron job or a sequential processing queue to parse a list of newly compromised targets and generate their public extortion profiles instantaneously.
The presence of such rigorous automation at the terminal phase of the attack lifecycle allows analysts to confidently hypothesize regarding the upstream operations of the M3RX cartel. If the group has industrialized its public-facing infrastructure, it is a statistical certainty that its initial access, lateral movement, payload deployment, and data exfiltration pipelines are similarly automated. M3RX does not function as a boutique, manual hacking collective carefully navigating individual networks; rather, it operates as a programmatic, mass-processing entity designed entirely for volume, velocity, and scale.
The Macro-Environmental Threat Matrix: Contextualizing the 2026 Landscape
To fully conceptualize the specific operational mechanics and the overall threat posed by M3RX, it is imperative to situate the actor within the prevailing conditions of the 2026 cyber threat landscape. Threat actors do not operate in a vacuum; their strategies are entirely dictated by the defensive environments they encounter and the technological tools at their disposal.
Global intelligence reports, synthesized from incident response engagements and endpoint telemetry worldwide, characterize the current era as the “Year of the Evasive Adversary”. This period is defined by a fundamental paradigm shift wherein traditional defensive visibility is systematically degraded, and offensive operations are executed with unprecedented, often machine-driven, celerity. The operational reality facing enterprise defenders is stark: according to the latest aggregated intelligence indices, an alarming 56% of all corporate systems currently possess critical exposures. This creates a massive, easily accessible attack surface, providing automated actors like M3RX with an endless supply of vulnerable targets.
This widespread exposure is continuously exacerbated by the rapid evolution of advanced tactics, techniques, and procedures (TTPs), the unceasing proliferation of highly evasive ransomware variants, and the increasing frequency of catastrophic supply chain attacks that bypass traditional perimeter defenses. Security leaders and Chief Information Security Officers (CISOs) are consequently forced into a continuously reactive posture. They are overwhelmed by thousands of theoretical vulnerabilities competing for their attention, struggling daily to separate actionable risk from the deafening noise of the global telemetry stream.
The success and rapid scaling of emerging groups like M3RX is a direct, unavoidable symptom of this degraded macro-environment. When the baseline of global security posture is characterized by widespread, unpatched exposure and a reliance on reactive monitoring, threat actors do not need to invest millions of dollars into developing zero-day exploits. They merely need to outpace the patching, detection, and human response cycles of their targets using known, highly industrialized exploit kits.
The Acceleration of the Adversarial Lifecycle: The Breakout Time Crisis
Within this hostile environment, the single most critical metric defining the battleground between offensive efficacy and defensive response is “breakout time.” Breakout time is the precise duration between an adversary’s initial, successful compromise of a host system (the beachhead) and their ability to laterally move to other internal nodes within the victim network. Once an adversary achieves lateral movement, containment becomes exponentially more difficult, and the probability of catastrophic data exfiltration and domain-wide encryption nears certainty.
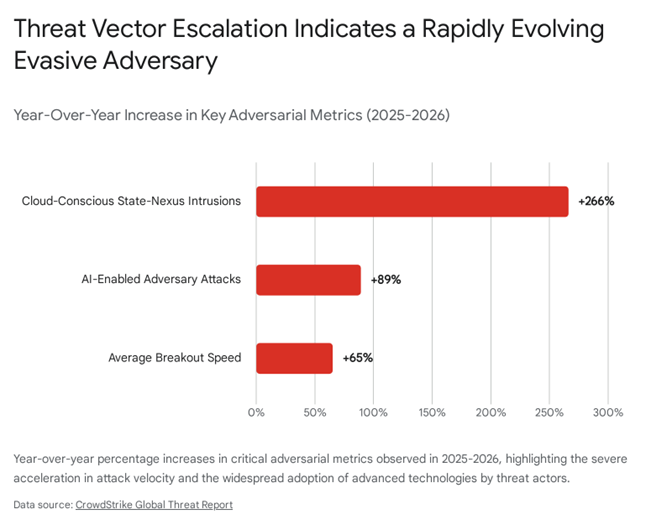
Historically, breakout times were measured in days or hours, providing Security Operations Centers (SOCs) with a viable window to detect anomalous behavior, investigate alerts, and quarantine compromised machines manually. By 2026, this window has essentially collapsed. Recent forensic analyses and global threat reports have recorded the fastest eCrime breakout time on record at an astonishing 27 seconds, an operation attributed to the highly sophisticated Punk Spider activity cluster. Furthermore, the industry has observed a massive, systemic 65% year-over-year increase in average breakout speeds globally across all tracked adversary groups.
This hyper-acceleration signifies a fundamental, physical shift in the dynamics of cyber warfare. As adversaries like M3RX move faster than ever, driven by automation and scripted execution, the window for human detection, triage, and manual response continues to shrink towards zero. For a group like M3RX, which relies heavily on high-velocity automated data publications, minimizing upstream breakout time is absolutely essential to their business model. If a corporate defender requires several minutes to log into a SIEM console to investigate a low-fidelity alert, they have already lost the engagement. M3RX and its contemporaries operate on the mathematically sound assumption that legacy organizational response capabilities cannot possibly match machine-speed execution. Consequently, strategic defense must completely pivot from human-in-the-loop validation strategies to fully autonomous, real-time response frameworks to have any realistic hope of intercepting these hyper-accelerated attacks.
Artificial Intelligence as an Adversarial Force Multiplier
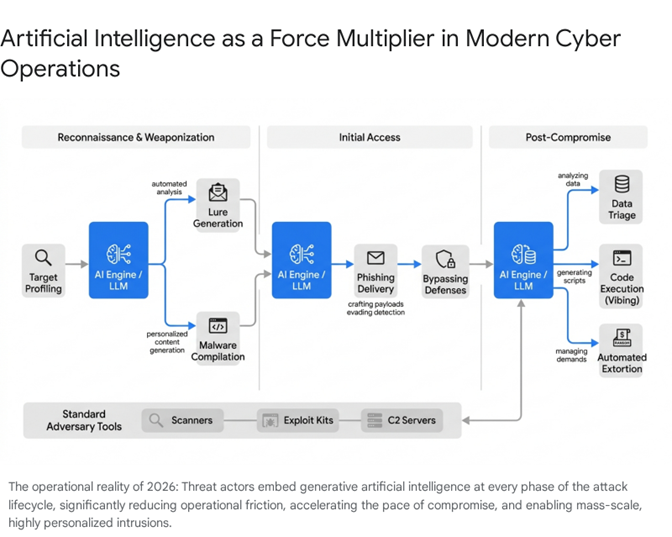
The defining technological characteristic of the 2026 threat landscape—and arguably the primary structural enabler of M3RX’s operational velocity and success—is the ubiquitous operationalization of Artificial Intelligence by malicious actors. AI is no longer an emerging, theoretical concept restricted to academic papers or highly funded nation-state laboratories; it is deeply and permanently embedded into how everyday eCrime syndicates plan, iterate, and sustain complex cyberattacks. The conversation within the intelligence community has rapidly shifted from merely recognizing the speed AI provides to deeply understanding its role in systematically reducing operational friction across the entire cyber kill chain.
Intelligence reveals a staggering 89% increase in attacks executed by explicitly AI-enabled adversaries. This transformation is absolute and pervasive. Threat actors across the entire spectrum of sophistication, ranging from highly resourced nation-state groups like North Korea’s Jasper Sleet and Coral Sleet (formerly tracked as Storm-1877) to financially motivated RaaS affiliates like M3RX, are aggressively leveraging AI to scale their malicious activity and accelerate their tradecraft.
Crucially, AI represents a severe, dual-pronged threat to corporate environments. First, it functions as a profound force multiplier for the adversary, allowing them to execute attacks with greater speed, precision, and volume. Second, it simultaneously introduces entirely new, highly vulnerable attack surfaces within corporate infrastructures. Organizations are rushing to adopt internal Large Language Models (LLMs) and AI productivity tools without adequate security controls. Indeed, over 90 major organizations have recently reported severe incidents where their own legitimate, internal AI tools were actively exploited by adversaries to generate malicious commands, bypass internal guardrails, and seamlessly exfiltrate sensitive proprietary data.
The scale of this adversarial integration is massive. Mentions of generative AI platforms, most notably ChatGPT, within dark web criminal forums have surged by 550% compared to any other tool or model, indicating a massive, community-wide effort to weaponize these consumer technologies. While fully autonomous, “agentic” AI—where an AI model independently plans, funds, and executes an entire campaign from end to end—remains relatively rare, the tactical execution of modern attacks has been largely surrendered to machine intelligence, with a human-in-the-loop providing only top-level strategic direction.
Generative AI in Reconnaissance and Payload Delivery
For an opportunistic, high-volume group like M3RX, the earliest phases of the kill chain—specifically reconnaissance, target profiling, and initial access—are where AI provides the highest and most immediate return on investment. Despite decades of security awareness training, email remains the absolute fastest, cheapest, and most pervasive path to initial network access. However, the efficacy of traditional, spray-and-pray phishing campaigns has historically been strictly limited by poor grammar, lack of contextual relevance, and easily identifiable malicious formatting that is quickly flagged by rudimentary email gateways.
Generative AI has effectively and permanently eliminated these defensive barriers. By embedding AI seamlessly into their mass-phishing operations, threat actors can now research target organizations at machine speed. These models synthesize vast amounts of public data—scraping LinkedIn profiles, corporate press releases, SEC filings, and social media footprints—to craft highly personalized, contextually flawless lures that bypass both human skepticism and traditional linguistic analysis engines.
Furthermore, AI enables the rapid generation of polyglot campaigns, fundamentally altering the geographic limitations of threat actors. Previously, a Russian-speaking or Chinese-speaking syndicate would struggle to convincingly phish a mid-sized Italian logistics firm or a Swiss commercial entity. Generative AI eliminates this language barrier entirely, allowing a group to seamlessly and convincingly target victims in English, German, French, and Italian simultaneously. This capability is directly evidenced by M3RX’s diverse victimology, simultaneously targeting dmschweiz.ch (Switzerland) and rotak.it (Italy) alongside anglophone entities in the UK, Canada, and Australia, without requiring native speakers on their operational payroll. The objectives of the threat actor have not changed—they still seek credential theft, financial gain, or payload execution—but the precision, persistence, and massive scale enabled by these AI tools have vastly upgraded the threat. Once access is achieved, AI continues to assist by rapidly “vibing code” for custom malware variants and autonomously triaging massive volumes of stolen data to locate the most sensitive financial records or PII, maximizing leverage for the extortion demand.
Malware-Free Intrusions and the Identity Crisis
Once initial access is successfully achieved, the subsequent methodologies employed by modern adversaries further complicate detection and response efforts. A defining characteristic of the current threat environment, heavily utilized by groups operating at the speed of M3RX, is the sharp and sustained decline in reliance on traditional, disk-based compiled malware. In recent assessments, an overwhelming 82% of all recorded network detections were categorized as entirely malware-free. This statistical reality has profound, structural implications for how security architects must understand and counter the operations of contemporary syndicates.
Malware-free intrusions, rather than relying on custom-compiled executables that can be easily hashed and blocked by antivirus software, rely heavily on compromised identities, stolen session tokens, and the exploitation of legitimate administrative tools already natively present within the victim’s environment. This highly effective technique is known as “Living off the Land” (LotL). By hijacking valid user accounts or exploiting misconfigured Active Directory settings, adversaries can traverse the network masked entirely as legitimate corporate personnel. They utilize tools like PowerShell, Windows Management Instrumentation (WMI), and remote desktop protocols (RDP) to execute their objectives, effectively bypassing traditional Endpoint Detection and Response (EDR) solutions that rely primarily on identifying malicious file signatures or anomalous rogue executables.
This aggressive pivot toward identity-centric attacks necessitates a total paradigm shift in defensive strategy. Security teams can no longer focus solely on securing physical or virtual endpoints. They must relentlessly monitor identity fabrics, authentication protocols, and behavioral anomalies within cloud identity providers (IdPs) like Azure AD or Okta. The ease with which AI assists in rapidly triaging stolen credential dumps and scripting complex LotL commands further accelerates this dangerous trend, allowing groups like M3RX to seamlessly blend into background network noise until the moment of encryption.
Exploiting the Periphery: Edge Devices and Cross-Domain Escalation
In their continuous pursuit of highly evasive operations, adversaries are increasingly shifting their initial focus away from heavily monitored, traditional employee endpoints (laptops and workstations) and toward the unprotected periphery of the corporate network. Intelligence indicates a massive, systemic escalation in edge device and cross-domain attacks. By specifically targeting internet-facing appliances—such as VPN gateways, perimeter firewalls, load balancers, and hypervisors—threat actors exploit critical visibility gaps inherent in most enterprise architectures.
These edge devices are highly attractive targets for several reasons. They often run proprietary or embedded operating systems that lack robust native security monitoring or the ability to host third-party EDR agents. Furthermore, they are notoriously difficult to patch comprehensively, often requiring significant network downtime that IT departments are hesitant to authorize. The exploitation of these peripheral architectures allows adversaries to establish a persistent, highly privileged foothold entirely outside the purview of standard SOC monitoring.
From this unmonitored vantage point, adversaries move fluidly across the network, escalating privileges across identity structures, cloud environments, and internal virtual networks while completely avoiding heavily monitored endpoints to evade detection. The severity of this specific vector is underscored by the observed activities of Advanced Persistent Threats (APTs); for example, the highly sophisticated China-nexus adversary OPERATOR PANDA directed a massive 40% of its vulnerability exploitation efforts specifically at edge devices, recognizing them as the path of least resistance into secure networks.
Furthermore, telemetry indicates a dramatic 266% increase in cloud-conscious intrusions executed by state-nexus threat actors. This cross-pollination of tactics is critical to understanding the RaaS ecosystem. The advanced TTPs pioneered by state-sponsored actors—such as sophisticated cloud infrastructure manipulation, token theft, and edge device zero-day exploitation—inevitably and rapidly trickle down to the eCrime ecosystem. It is highly probable that automated RaaS affiliates like M3RX are leveraging pre-packaged exploit kits specifically targeting edge device vulnerabilities (such as recent critical flaws in Fortinet, Ivanti, or Citrix gateways) to reliably secure their initial footholds across their diverse, global victim base.
Mapping to the MITRE ATT&CK Framework and Risk-Based Prioritization
The ultimate objective of M3RX is unmitigated financial extortion, executed via the rapid deployment of ransomware and the mass exfiltration of highly sensitive corporate data. The modern ransomware ecosystem operates on a model of double or triple extortion, where the threat of publishing exfiltrated data on dark web leak sites—the exact mechanism utilized by M3RX—serves as the primary coercive lever.
To defend against this industrialized machine, organizations must fundamentally alter how they process vulnerability data. Currently, CIOs and CISOs are paralyzed, overwhelmed by thousands of Common Vulnerabilities and Exposures (CVEs) competing for limited patching resources. Simple awareness of a CVE is no longer sufficient; security leaders must determine if that specific vulnerability is exploitable within their unique environment, and crucially, which adversaries are actively using it.
This requires the adoption of Threat Actor Intelligence platforms that move beyond arbitrary vendor naming conventions and map directly to the MITRE ATT&CK framework. By utilizing platforms like Horizon3.ai’s NodeZero, defenders can automatically connect exploitable vulnerabilities to the specific, real-world adversaries who weaponize them—from ransomware crews like AKIRA and M3RX to nation-states like Salt Typhoon. Every exploited vulnerability must be tied to specific ATT&CK tactics and techniques, providing defenders with a clear, mathematical view of how attacks unfold. Attack chains must visualize how a single weakness on an unpatched edge device can lead to rapid domain compromise, data theft, and eventual ransomware deployment, with clear, quantifiable links to business risk. Only through this rigorous, framework-driven approach can organizations achieve true, risk-based prioritization and close the gaps exploited by automated entities.
Strategic Imperatives and Autonomous Defensive Posturing
The emergence of the M3RX threat actor, contextualized within the hyper-accelerated, AI-driven, and highly evasive threat landscape of 2026, necessitates a severe and immediate reevaluation of enterprise defensive strategies. Traditional, reactive security postures that rely on human alert triage and signature-based antivirus are structurally inadequate to counter adversaries that measure breakout times in seconds and utilize generative AI to bypass standard heuristic detections.
To effectively defend against M3RX and the broader cohort of next-generation threats, security leadership must implement the following strategic imperatives:
- AI-Driven Autonomous Response: Given the new benchmark of a 27-second breakout time, human-reliant detection and manual triage processes are entirely obsolete. Organizations must aggressively deploy AI-native security platforms capable of autonomous, machine-speed response. These systems must be authorized to automatically isolate compromised network nodes, terminate anomalous identity sessions, and block malicious processes the millisecond they deviate from established behavioral baselines, without waiting for SOC analyst intervention.
- Zero Trust and Comprehensive Identity Protection: With 82% of all network intrusions occurring without the use of traditional malware, defense-in-depth must center entirely on the identity fabric. Continuous, algorithmic monitoring of Active Directory environments, strict enforcement of phish-resistant multifactor authentication (MFA) across all internal and external perimeters, and deep behavioral analytics on user access patterns are absolute, non-negotiable requirements to detect LotL techniques.
- Edge Device Hardening and XDR Consolidation: The corporate attack surface has expanded far beyond the traditional employee endpoint. Security teams must aggressively prioritize the patching and hardening of edge devices, VPN appliances, and hypervisors. Furthermore, telemetry from these notoriously opaque assets must be deeply integrated into a centralized Extended Detection and Response (XDR) architecture to eliminate the critical visibility gaps currently favored by evasive adversaries.
- Continuous Threat Exposure Management (CTEM): Security teams must abandon arbitrary patching cycles and adopt platforms that connect theoretical vulnerabilities directly to real-world exploitation paths utilized by groups like M3RX, enabling true, intelligence-driven prioritization.
Wrap Up
The telemetric identification and subsequent operational analysis of the M3RX threat actor provide a stark, highly instructive encapsulation of the realities defining the 2026 cyber warfare domain. M3RX is not an isolated, artisanal anomaly; rather, it is the natural manifestation of an industrialized, highly automated Ransomware-as-a-Service economy that aggressively leverages generative artificial intelligence to reduce operational friction, maximize disruptive impact, and scale globally. The group’s demonstrated ability to opportunistically compromise organizations across multiple continents and industry sectors, subsequently executing flawlessly synchronized extortion publications within mere seconds, underscores a severe and permanent escalation in adversarial capabilities.
Defending against this unprecedented caliber of threat requires the cybersecurity industry to entirely transcend outdated, reactive methodologies. The continued reliance on legacy, signature-based detections and manual incident response protocols is a guaranteed formula for systemic, organizational failure in an era defined by malware-free identity attacks, machine-generated phishing campaigns, and sub-minute breakout speeds. By deeply understanding the behavioral mechanics of M3RX, ruthlessly disambiguating telemetric noise, and acknowledging the macro-environmental forces driving the success of modern threat actors, organizations can pivot toward resilient, AI-empowered defensive architectures. The future of global cyber defense relies entirely on out-innovating the adversary, meeting machine-speed attacks with autonomous, machine-speed mitigation, and fundamentally disrupting the economic viability of the industrialized extortion model.





You must be logged in to post a comment.