Disrupting Threats through Advanced Foresight– No tracking
Executives demand rapid, quantified intelligence. Traditional compliance models fail against hybrid warfare. Hostile actors blend economic coercion and cognitive manipulation [Treadstone 71, 2026]. Leaders almost certainly face exploitation without preemptive capabilities.
Organizations require the adaptive cyber intelligence lifecycle built for disruption driven by foresight.
Analysts separate verified facts from adversary claims. Intelligence operators form a cognitive army to detect analyze expose counter and contain emerging threats. Specialists execute cyber psychological operations influencing through strategy. Integrated behavioral threat analysis highly likely stops malicious insiders before operational sabotage happens. Advanced intel analysis ai methods infused with AI replace subjective guesswork.
Access is free with no tracking
Teams access structured operations at
https://www.treadstone71.com/decision-support-strategic-intelligence-tools
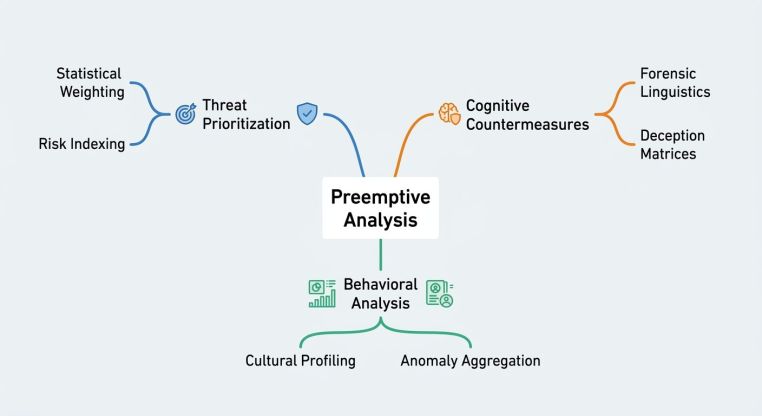
- ATCRI: Statistical weighting produces an almost certain threat prioritization.
- ACS: Game-theoretic decision trees yield a probable disruption of adversary planning.
- CWC: Forensic linguistics and semiotics offer an even chance of containment.
- CWIA: Anomaly and aggregation analysis leads to the probable identification of synthetic media.
- HTIM: The Cultural Nexus Framework guarantees almost certain behavioral mapping.
Analysts apply pattern, trend, and tendency analysis to map threat trajectories across domains. Operators evaluate adversarial actions with link and technical analysis. Teams separate verified facts from adversary claims directly within the matrices. Analysts establish a baseline for organizational understanding. We rank evidence to expose hidden vulnerabilities.
Assessors rely on integrated behavioral threat analysis to stop malicious insiders. Specialists infused with AI replace subjective guesswork with structured frameworks. Ignorance guarantees operational defeat. Organizations require the adaptive cyber intelligence lifecycle built for disruption driven by foresight.
Adversaries adapt operations daily. Treadstone 71 advanced analytic dominance sats process evolving hostile tactics. Operators apply the treadstone 71 cultural nexus framework to chart terrain vulnerability. Analysts evaluate raw data using forensic linguistics, semiotic analysis, and stylometrics. Teams model cognitive biases. Game-theoretic simulations reconstruct how opponents process deception. Current collection confirms an almost certain advantage when forecasting hostile shifts. Strategic intelligence drives positioning. Ignorance guarantees operational defeat.
Executives access targeted micro-briefings at
https://www.treadstone71.com/decision-advantage-executive-intelligence-micro-briefings
Intelligence stemples plus evaluates operational exposure against society, technology, economics, military, politics, law, education, and security vectors. Assessors map external shocks before penetration occurs.
Operators deploy anomaly and aggregation analysis to isolate automated bot activity from organic discourse. Specialists use pattern, trend, and tendency analysis to expose hostile acquisitions and regulatory lawfare. Security personnel execute link and technical analysis to track supply chain exposure. Assessors evaluate the likelihood of multi-domain threats. We project effects and future implications with a probable outcome of reducing decision delays.
Attribution remains highly likely when using structured tradecraft. Motives become clear through the Pitch Black Tetrad framework.





You must be logged in to post a comment.