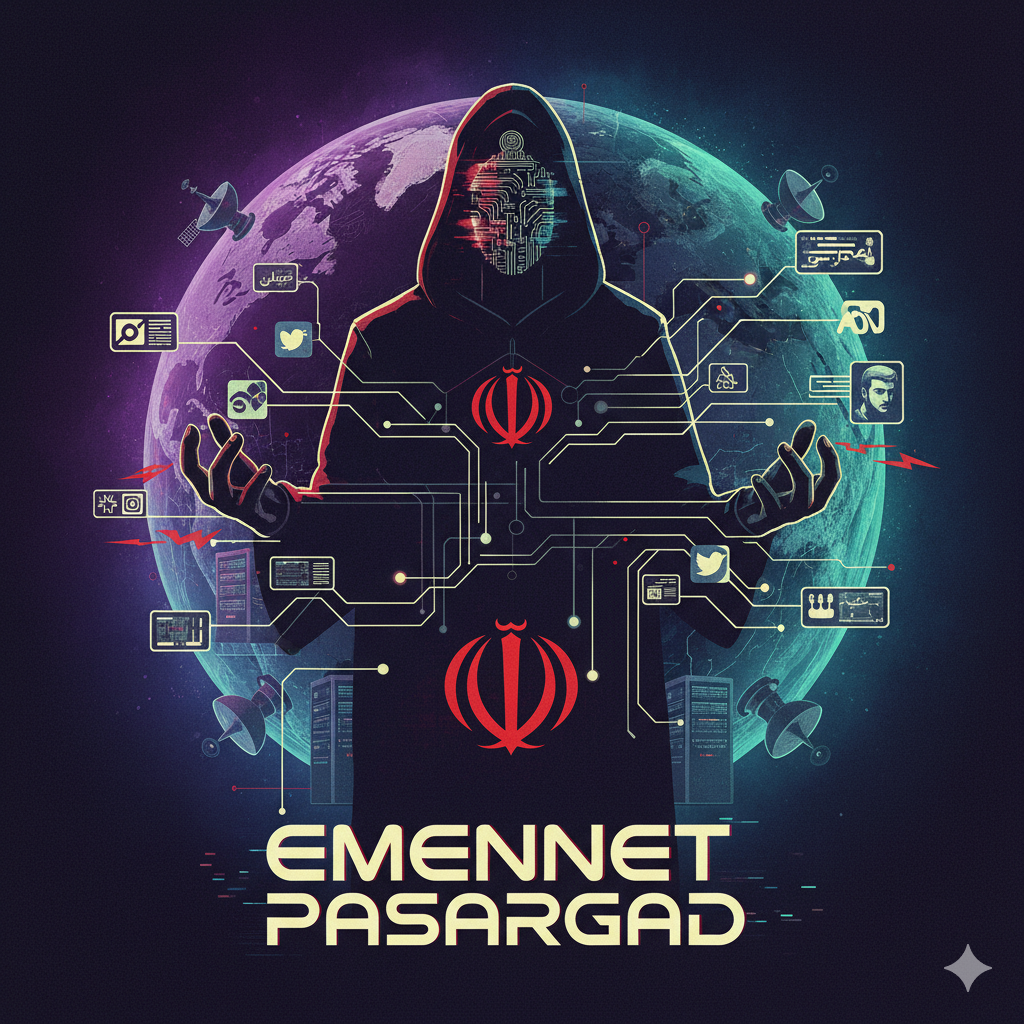
Announce a no-nonsense briefing that names operators, maps their Tehran hubs, and ties tradecraft to real artifacts. Readers move from first contact to 2025 with a straight line of evidence—sanctions packages, indictments, leaked Farsi memos, and vendor reversals. Investigators track how blunt phishing hardened into modular implants, signed payloads, Azure-fronted control, and persona farms that run election interference and regional pressure. Security teams receive clear actions that break HR lure portals, disrupt code-signing supply, isolate cloud tenancy, and expose false flags. Analysts get structured methods that test assumptions, weigh rival hypotheses, and project next moves from timing, tooling, and target selection. Accountability follows named leaders, offices, and procedures that appear across foreign ministry breaches, ICS probes, telecom espionage, and synchronized influence tied to Gaza and nearby flashpoints. Open the report and step through names, places, and procedures that anchor every claim. Emennet Pasargad – Aria Sepehr Ayandehsazan