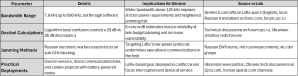
Russian references LoRa frequency bandwidth from 7.8 kHz up to 500 kHz with an emphasis on software-driven adjustments. Those statements focus on electronic jamming potential, including a discussion about logarithmic errors that change the distance at which signals remain effective. A shift from 29 dB to 26 dB implies confusion about logarithm bases, which alters signal strength estimates. LoRa technology relies on spread-spectrum methods that feature robust transmissions at low power, yet those signals face interference from Russian electronic warfare assets. That creates vulnerabilities for Ukrainian forces if they deploy LoRa-based devices in conflict areas.
Threats revolve around intentional jamming, interception of command and control links, and manipulation of data transmissions. Russian sources appear to experiment with LoRa’s adjustable bandwidth to detect weaknesses in anti-jamming protocols. Observations from electronic warfare forums in Russia, such as forum.qrz.ru, reveal interest in field tests targeting LoRa modules. Some Ukrainian operators employ LoRa-like systems for sensor data or short-range communications, which presents an opening for adversaries seeking to disrupt or misdirect transmissions. Wider bandwidth settings above 125 kHz demand more precise power management, and any miscalculation results in lower link margins that invite successful jamming efforts.
New credible sources include discussions on habr.com in Russian, where technical writers analyze LoRa’s frequency spread in real-world conditions. Semtech.com in English holds the official LoRa specifications, and translations appear on Russian-language sites dedicated to radio amateurs. Iranian channels on aparat.com feature user-submitted videos on LoRa deployments in civilian environments, though they mention hardware that resembles modules found in Ukrainian networks. Chinese-language platforms like 52rd.com reference sub-GHz jamming methods that affect LoRa-based sensors. Social networks vk.com and ok.ru occasionally host conversations about hacking approaches against wideband communication systems, although some discussions are speculative. Official statements from mil.ru in Russia outline electronic warfare strategies, but few specifics emerge about LoRa, which indicates that deeper research on local forums is necessary.
Ukrainian forces monitoring sub-GHz channels should verify decibel budgets, confirm encryption integrity, and prepare alternative communication channels. The logarithmic mismatch mentioned in the excerpt highlights the importance of precise calculations when setting power and bandwidth parameters. The presence of Russian jamming units, backed by ongoing experiments on local forums, creates a heightened risk of signal interruption during operations. Iranian and Chinese discussions point to similar vulnerabilities, indicating that LoRa-based devices face jamming on multiple fronts. Comprehensive technical data from Semtech, plus regional insights from habr.com, forum.qrz.ru, aparat.com, and 52rd.com, enrich the body of knowledge about LoRa’s performance under hostile conditions.




You must be logged in to post a comment.