The number of cyberattacks on Russia in 2022 increased by 80%, 25 thousand fell on state resources – Chernyshenko
“And of course, information security is at the forefront, because the number of cyber attacks on Russia has increased by 80% this year. Moreover, if last year the financial sector was the main target of cyberattacks, this year it is the public sector. 25,000 or even more cyber attacks on state resources and 1,200 incidents on critical infrastructure have been successfully eliminated,” he said during a meeting with Russian President Vladimir Putin on Monday.

According to Chernyshenko, “this struggle will always continue,” as the cyber troops of all unfriendly countries are fighting against Russia
The number of cyberattacks in Russia increased by 15 times in the first half of 2022
The number of pre-investigated crimes for the six months of 2022 amounted to 8.2 thousand, the remaining unsolved – 21.1 thousand. , according to the results of 2021 – 24.3%, ”says Yuri Rusanov, head of the department of the Prosecutor General’s Office of the Russian Federation for the Siberian Federal District.
At the same time, the total number of cyber attacks in Russia in the first half of 2022 increased by 15 times compared to the same period last year, StormWall reported. The most attacked industries were the financial sector (32% of the total number of attacks), retail (14%), the logistics sector (10%), the insurance industry (8%) and the public sector (18%). The education sector (7%), the entertainment sector (5%), the tourism industry (4%) and other industries (2%) were also subjected to DDoS attacks.

The number of DDoS attacks on the public sector during this period increased 17 times, on logistics – 16 times, in the insurance industry the number of attacks increased 15 times, in the financial sector – 12.8 times, in retail – 11 times. The duration of attacks has increased: at the beginning of 2022, their period averaged 7 hours, in 2021 – about 3 hours, now some of them last for weeks. On July 21, 2022, Kaspersky Lab announced the longest DDoS attack in Russia. It started in May 2022 and lasted almost 29 days.
The calculations of specialized analytical companies contradict the official data of law enforcement officers due to the reluctance of some companies to contact them with hacking problems, experts say. “So, for example, the victims do not know the procedures for dealing with the fact of cyber attacks or believe that the attackers are outside the jurisdiction of Russian law. In addition, companies may not apply to the authorities out of a desire to hide the identified attacks and data leaks, as well as due to the lack of built-in mechanisms for detecting and registering cyber attacks. Another important factor is the lack of trained personnel capable of conducting an internal investigation to identify the causes of the incident,” said Daniyar Iskhakov, Deputy Director of the Consulting Department of the Innostage group of companies.

Experts explain the sharp surge in hacking attempts by the unstable political situation in the world. “A feature of recent times is that more and more so-called hacktivists are participating in attacks, whose main goal is not financial gain, as it was before, but causing maximum damage to organizations and their processes. This is especially dangerous for industrial enterprises and critical information infrastructure (CII), the disruption of which can lead to serious consequences, including for the population. However, organizations that are not associated with critical infrastructure are also at risk of attacks, ”says Maria Namestnikova, head of the Russian research center at Kaspersky Lab.
At the same time, government agencies and the financial sector turned out to be the most protected, says Alexey Pavlov, director of business development at the Solar JSOC cyberattack counteraction center at RTK-Solar. “Health care and education have become the most vulnerable sectors,” the expert believes.
hacker on the phone
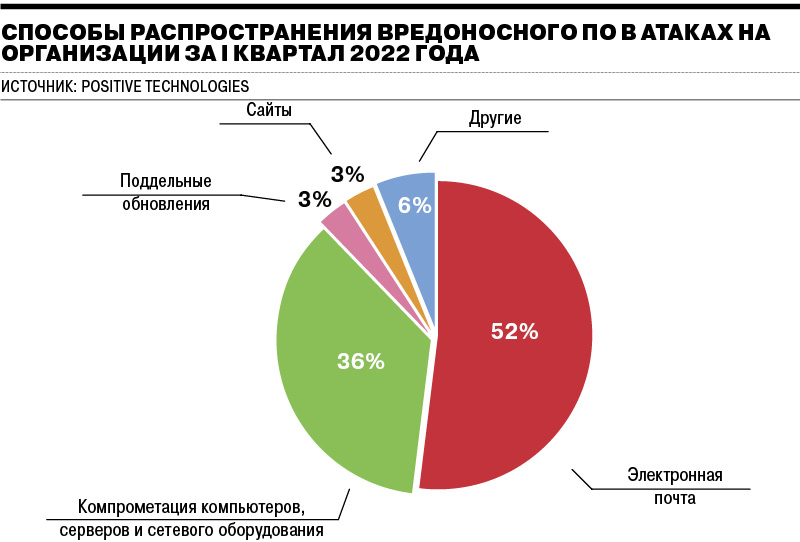
No new mechanisms for hacking software products were invented in 2022, only the number of hacking attempts has changed, emphasizes Philip Shirov, co-founder and director of the Altapp cloud business automation service. “Basically, these were DDoS attacks on government and private services in Russia and defacing (changing one web page to another) of the websites of government agencies and Russian companies,” he comments.
For ordinary users, traditional threats are still relevant: phishing, scam, telephone fraud, which also show growth. From January to June, residents of the Novosibirsk region sent 120 complaints about cyber fraud to the Bank of Russia. This is 1.5 times more than in the same period last year.
“Social engineering remains one of the most dangerous hacking methods used by cybercriminals, largely because it relies on human error rather than technical vulnerabilities. This makes these attacks even more dangerous – it is much easier to deceive a person than to hack into a security system,” says Svetlana Koryagina, information security expert at OCS Distribution.
In 2022, security breaches by third parties have become an even bigger threat as companies increasingly turn to independent contractors to complete work that was previously done by full-time employees, analysts say.
“The second most important threat is ransomware. They have been a notable threat over the past few years and don’t seem to be going anywhere anytime soon. In 2021, the average cost of a ransomware attack was $4.62 million. In many cases where security breaches occurred in small and medium enterprises, companies were forced to close permanently because they could not recover from such a serious attack,” says Svetlana Koryagin.
Ransomware attacks are unique in that they are quite slow. This means that once hackers gain access to a system, they work for weeks, sometimes months, to encrypt sensitive information before demanding a ransom, the expert explains.Expand to full screen
1/2 _
_
The market is preparing its own
Problems with information protection among Russian users in 2022 arose, among other things, due to the departure of the largest international companies – developers of information protection systems. Cisco, IBM, Imperva, Fortinet, Microsoft, Norton, Avast and others announced the termination of their activities in Russia. They accounted for 39% of the total market volume as of 2021, by the end of 2022 their market share will decrease to 12%. “System integrators, customers and customers are now urgently looking for replacements for these manufacturers,” comments Ms. Koryagina.
The current situation is beneficial for Russian vendors, as the demand for cybersecurity solutions is steadily growing. It is due to the changed geopolitical situation and measures taken by the government (regulators) and business to strengthen cybersecurity, according to analysts from the Center for Strategic Research (CSR).Expand to full screen
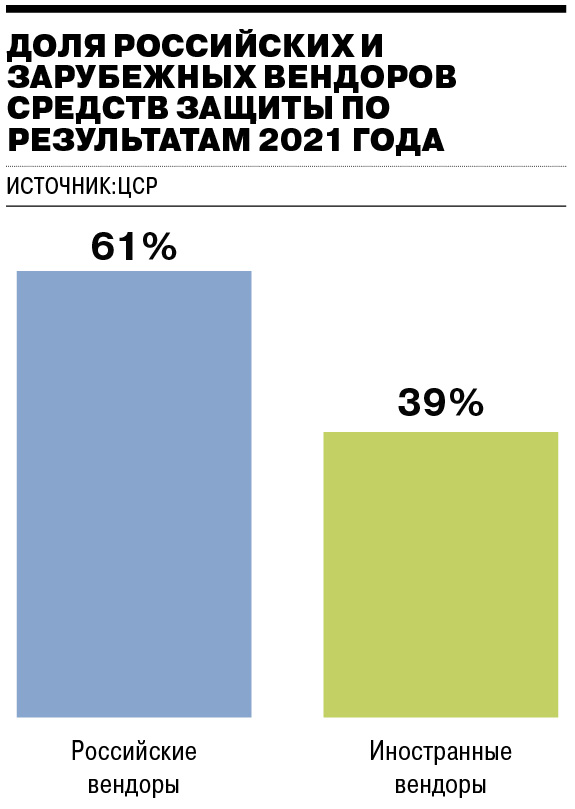
The Russian information security market has been engaged in import substitution for several years. With the departure of foreign vendors, the fullness of some segments will decrease, which will allow other players to occupy the free space, and the general background allows us to predict that the growth rates of the information security market may even exceed analysts’ expectations, Svetlana Koryagina believes.
“This will make Russian cybersecurity one of the most attractive industries in terms of investment. In the near future, we can expect the emergence of new players, mergers and acquisitions, business expansion and the entry of information security developers into the capital market,” she adds.
According to analysts from the Center for Strategic Research (CSR), in the next five years, the Russian cybersecurity market will grow 2.5 times – from 185.9 to 469 billion rubles. At the same time, starting from 2023, almost the entire budget of customers for information security tools in the B2G and B2B sectors will be spent on products of Russian vendors, which will enable the growth of this part of the market from 113 billion rubles. in 2021 to 446 billion rubles. in 2026.
Also, the active position of regulators and authorities regarding the need for import substitution (ensuring technological independence) of technical solutions related to ensuring the safe operation of critical information infrastructure objects will have a significant impact on the cybersecurity market, analysts say.
From March 31, 2022, by presidential decree in Russia, the purchase of foreign software for use at significant CII facilities is prohibited, and from January 1, 2025, the use of foreign software at such facilities is prohibited.
The market share of foreign vendors will continue to decline, experts say. “It is expected that the share of foreign vendors in the domestic market will stabilize at the level of 5%, but may grow to 8% in 2026. Further, the dominant position of domestic vendors may change in connection with the likely gray imports, ”the CSR study says.
Business spending on information protection at the same time began to grow, industry representatives say. “Given that the number of cyberattacks and their intensity have increased tenfold, the costs of cybersecurity for businesses should be significant – presumably “several times”. I believe that we will get more accurate figures when companies that specialize in the field of information security report their profits. Most commercial organizations that cannot protect themselves from cyber attacks on their own have turned to such organizations,” says Philip Shirov.
18% of 500 CEOs surveyed by KPMG in 2021 said cybersecurity risk will be the biggest threat to their organizations’ growth over the next three years. That’s nearly double the 10% of executives who said the same thing in mid-2020—a significant change in attitude in just six months.
“Companies have begun to take a closer look at their own cybersecurity. Increasingly, they are inventorying IT perimeters and looking to increase security through the introduction of new technologies and processes. Secure remote access solutions are in increasing demand. The cyber intelligence service is also becoming more popular. It involves both monitoring the mention of a company in the dark web and profile hacker Telegram channels (for example, if someone wants to order an attack on an organization), and obtaining information about known perimeter vulnerabilities (for example, if vulnerable company servers are published in the public domain)”, – says Alexey Pavlov.
At the end of the year, cloud security spending will grow by 41.2%, while data security spending will grow by 17.5%, infrastructure protection by 16.8%, and identity access management by 15.6%. %, for integrated risk management – by 12.6% and for security services – by 11.4%, Svetlana Koryagina believes.
The problem of cybersecurity in the coming years will be the most relevant for both ordinary users and companies. At the same time, the qualifications of cybercriminals will continue to grow. The consequences of attacks will directly depend on the level of training of specialists and the development of AI systems in Russia









You must be logged in to post a comment.