In their words:
On your website, in the article https://xakep.ru/2022/10/14/ddosia/ it is stated: “Basically, DDOSIA participants attack targets set by the pro-Russian hack group KillNet. In particular, they took part in a recent large-scale DDoS attack on major airports in the United States”, referring to some “researchers”. We operate independently and have nothing to do with the KillNet hack group. We choose our own targets for DDOS attacks. Please edit the publication (https://t.me/xakep_ru/13062), otherwise it turns out ugly. And learn to separate flies from cutlets, in the end, you could ask the source. You are an old, respected magazine, not magazines for 3 rubles a pack Team NoName057(16)
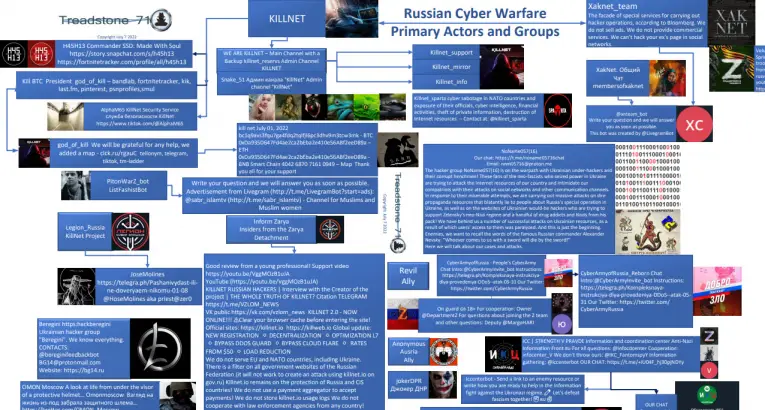
Download the Treadstone 71 Report – July 13
Crowdsourced DDoS: DDOSIA pays volunteers to participate in attacks … discovered the DDOSIA crowdsourcing DDoS project, in which a Russian-speaking hack group pays volunteers to participate in attacks on Western organizations. https://xakep.ru/2022/10/14/ddosia/
https://cybershafarat.com/2022/08/15/manifest-noname05716-to-be-released-aug-17/




You must be logged in to post a comment.