
What is Cognitive Warfare? https://www.treadstone71.com/

Intelligence Tradecraft Operator – Cyber Cognitive Warfighter Training – New York City Jun 12-16 OPSEC methods, online anonymity, persona creation, secure browser configuration with no verified leaks. OSINT and Darknet searching, Social media searches and collection, Personality identification using Myers-Briggs, the Big 5, the Dark Triad/Pitch Black Tetrad, the Psychological Techniques of the Seven Radicals,…
Read More “Cyber Cognitive Warfighter Training with Open AI / ChatGPT functions” »
Treadstone 71 Cognitive Warfare Training – Recognized by Russian philosophers, political technologists, media managers, producers, journalists and TV presenters, military correspondents, bloggers, volunteers and organizers of assistance to the front, designers and artists, writers, poets and musicians, sociologists and psychologists. On March 11, 2023, the Skolkovo Technopark will host a forum dedicated to information and…

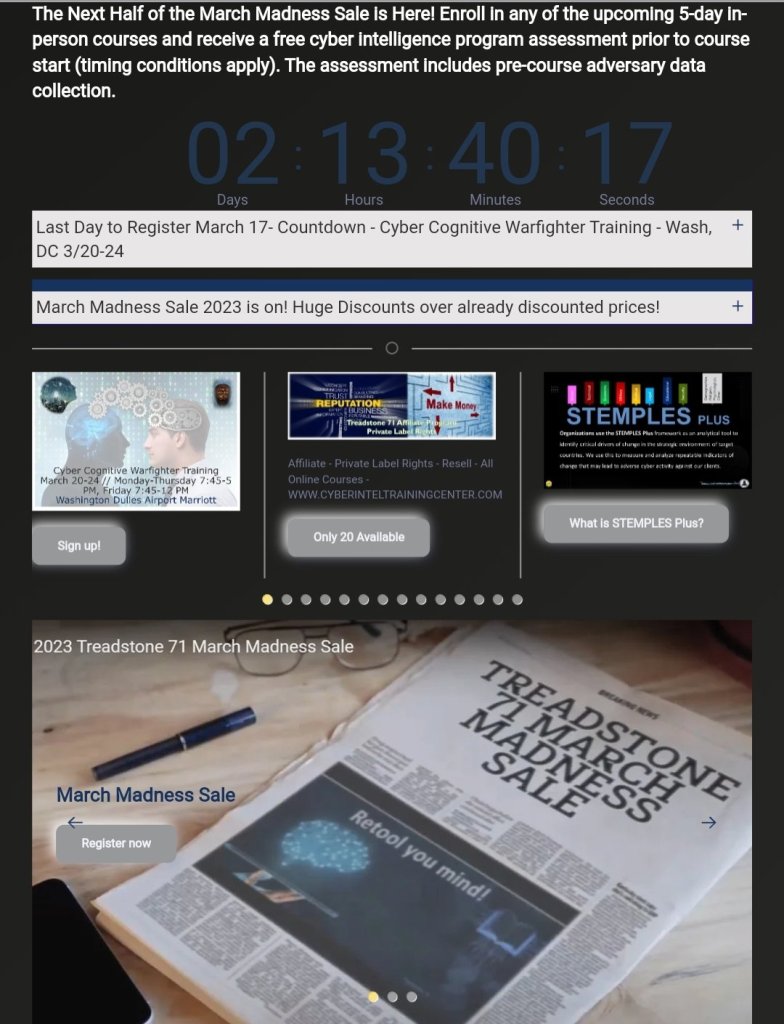
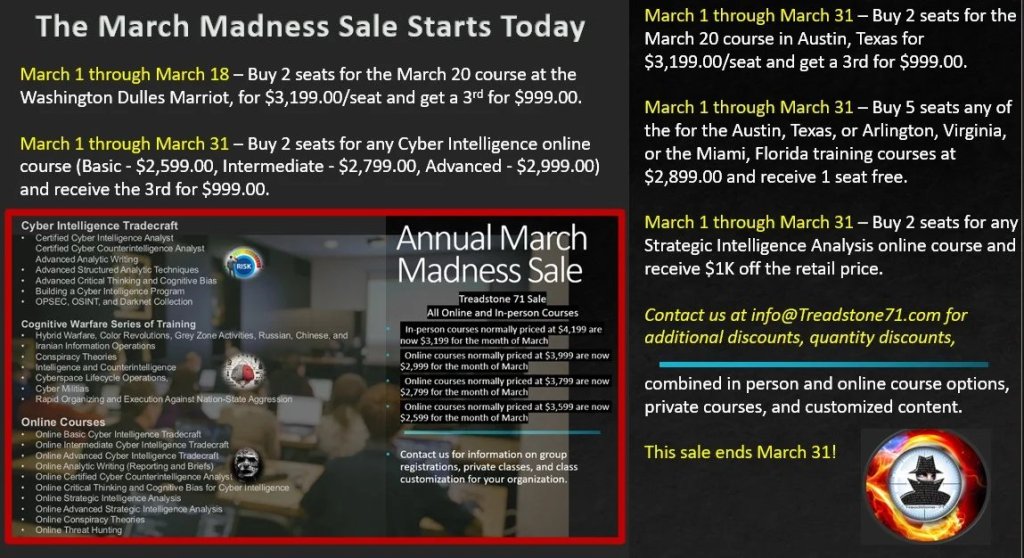
Our In-Person courses cover intelligence, counterintelligence, influence operations, how to build a cyber intelligence program, geopolitical and strategic intelligence, open-source intelligence, clandestine cyber human intelligence, persona development and use, and operational security in online environments. Our courses include: Cyber Intelligence Tradecraft Cognitive Warfare Series of Training Online Courses NOTICE: We use PayPal via our shopping cart….
Read More “MARCH MADNESS SALE Prices in effect through March 31 ” »


HALF MOON BAY, Calif., March 7, 2023 (SEND2PRESS NEWSWIRE) — Treadstone 71, LLC, the source for cyber intelligence, counterintelligence, hybrid, and cognitive warfare, announces new courses and services. “Targeted adversary data collection creates significant risk when seeking relevant information not available from threat intelligence feeds. Our operational security (OPSEC) training courses reduce risk to negligible…
Read More “OPSEC a Critical Requirement for Open-Source and Dark Net Collection” »

Reflexive control theory seeks to guide the target unconsciously in a predefined manner and often against their own interests. This can be done by influencing the enemy’s information channels and sending messages that change the flow of information in the adversary’s favor. An adversary makes a decision by acting in a manipulated information space, provoking…
Read More “The theory of reflexive control” »

WASHINGTON DULLES – 3/20-24 CYBER COGNITIVE WARFIGHTER COURSE OPSEC methods, online anonymity, persona creation and management with Myers-Briggs, the Big 5, the Dark Triad/Pitch Black Tetrad, the Psychological Techniques of the Seven Radicals, the Nine Enneagram Type, cyber HUMINT tactics, campaign development, management, and execution. // Adversary targeting with cyber D3A/F3EAD, PIRs, OSINT, Darknet. //…
Read More “Intelligence Tradecraft Operator – Cyber Cognitive Warfighter training” »

You must be logged in to post a comment.