The release of the meshtastic-sniffer suite represents a shift in how people monitor off-grid radio networks. One developer, alphafox02, created a package that listens to every radio signal in a large area without ever sending a signal back. Such a tool allows an attacker to see every message and find every person using a mesh radio. Users who once felt safe in the woods or during disasters now face a new threat. The software uses standard radio hardware to capture data that was once hard to find. This analysis examines the technical details of the tool and their impact on the safety of mesh users.
Evidence shows that the sniffer operates undetected. Standard mesh radios communicate to move messages. They send packets that contain text, locations, and system data. Most radios only listen to one channel at a time. The meshtastic-sniffer software listens to all channels simultaneously. An operator using a high-end radio receiver can monitor an entire city or a large park from a single point. Verified code from the software shows that it decodes all 9 standard mesh speeds simultaneously.
Adversaries claim that geolocation is accurate to within 100 meters. Standard tests suggest that such accuracy requires perfect timing between stations. Without perfect timing, the accuracy falls to 300 meters or more. This report evaluates these claims using intelligence analysis standards. The probability of an attacker finding a mesh node is high if they use the correct hardware.
The Evolution of Passive Mesh Monitoring
Mesh networks grew in popularity because they work without cell towers or the internet. People use them for hiking, search and rescue, and private talks. The system uses LoRa, a type of radio signal that travels long distances with very little power. For a long time, monitoring these signals was difficult for most people. One had to know the exact frequency and speed of the radio to hear it.
Alphafox02 changed the environment by releasing several sniffers for different satellite and radio systems. The developer previously wrote tools for Iridium and Inmarsat satellites. Those tools also worked through passive listening. The new meshtastic-sniffer follows the same design. It uses a single radio receiver to pull every signal out of the air.
Operators use Software-Defined Radios (SDRs) to run the software. These electronic devices turn radio waves into data for a computer. Some SDRs are cheap and small, like the RTL-SDR. Others are powerful and expensive, like the USRP B210. The software works with all of them.
| SDR Model | Bandwidth Capture | Frequency Range | Performance Rank |
| RTL-SDR | 2.4 MHz | Wide | Low |
| SDRplay | 10 MHz | Wide | Medium |
| HackRF One | 20 MHz | Very Wide | High |
| BladeRF 2.0 | 56 MHz | Very Wide | Very High |
| USRP B210 | 56 MHz | Very Wide | Very High |
Software improvements enable these radios to do more than before. One computer can process millions of samples per second. The meshtastic-sniffer uses a special mathematical tool called a polyphase filter bank. The filter bank acts like a set of many small ears. Each small ear listens to one frequency. Together, they listen to the whole band.
Technical Specifications and Capabilities
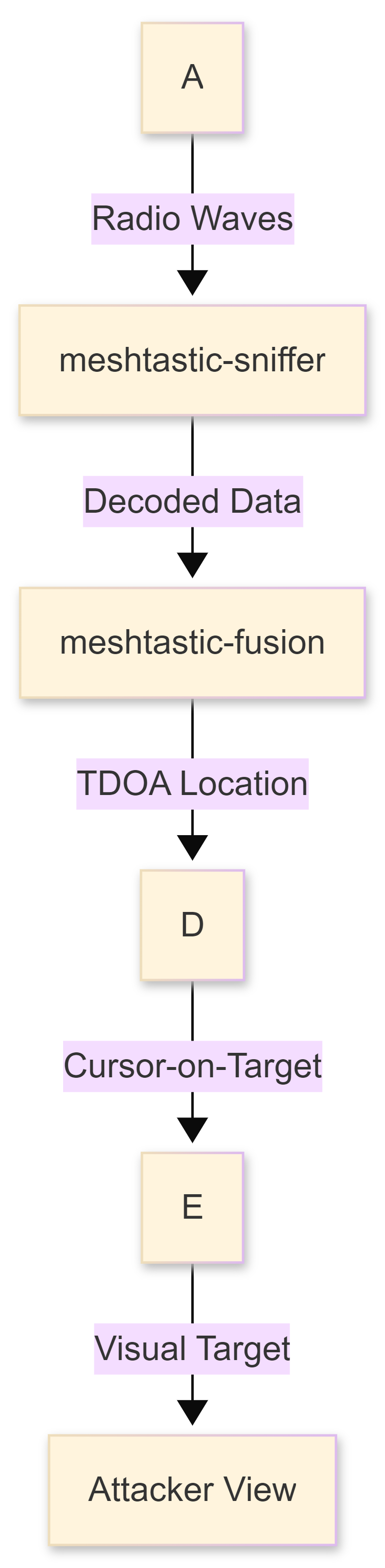
The suite consists of three main parts. The first part is the sniffer itself. The second part recovers passwords. The third part combines data from multiple stations to determine where a signal originated. Each part performs a specific job for the operator.
The Wideband Receiver
The meshtastic-sniffer program is written in C. C is a fast language that allows the computer to do math very quickly. The software uses special instructions inside the computer chip to speed up the work. These instructions are called SIMD. They allow the chip to perform many calculations simultaneously.
Because of this speed, the software decodes all 9 mesh modulation profiles simultaneously. These profiles determine how fast or slow the radio talks. Some are “Short and Turbo” for speed. Others are “Long and Fast” for distance. Most radios only pick one. The sniffer picks all of them.
The receiver covers 26 different frequency plans. These plans are for different parts of the United States, Europe, and Russia. In the United States, mesh uses the 902-928 MHz band. A BladeRF radio spans 56 MHz. Such a range is large enough to see every single mesh channel in the United States simultaneously. No message is lost because the radio is tuned to the wrong frequency.
Decoder Steps and Data Parsing
The software turns raw radio pulses into structured data. It follows a set of steps to ensure the data is correct. First, it finds the start of a message. Then, it reverses the math used to protect the signal from noise. These steps include deinterleaving and Gray code decoding.
Once the data is clear, the software looks for specific types of information. It understands 16 different types of data ports. Each port carries a different kind of message.
| Port Name | Data Content | Risk Level |
| TEXT_MESSAGE | Private chat text | High |
| POSITION | GPS coordinates | Very High |
| NODEINFO | User names and device IDs | High |
| TELEMETRY | Battery and signal strength | Low |
| NEIGHBORINFO | List of nearby nodes | Medium |
| ATAK_PLUGIN | Tactical map data | Very High |
The software outputs this data in JSON format. JSON is easy for other computers to read. An attacker can send this data to a map or a database for later use.
Cryptographic Weaknesses and Password Recovery
The second tool in the suite is meshtastic-recover. This program targets the encryption used by the mesh. Mesh networks use the Advanced Encryption Standard, or AES. Specifically, they use a mode called Counter Mode (CTR).
AES-CTR is a strong way to hide data if used correctly. However, the mesh has some limitations. One limitation is how the system creates the secret numbers for each message. These numbers are called nonces. The mesh builds a nonce from the sender’s ID and the packet ID. If an attacker knows the key, they can read every message.
The Default Key Problem
Many people use the default settings for their mesh radios. These settings use a well-known key. The meshtastic-sniffer software includes a flag to automatically use this default key. For such users, there is no privacy at all. An attacker sees every text and every location immediately.
For users who set their own password, the meshtastic-recover tool provides a way to break it. The software captures encrypted packets and turns them into a file for another program called Hashcat. Hashcat uses powerful graphics cards to guess thousands of passwords every second.
Evidence shows that weak passwords fail within seconds. A user who picks a simple word or a common phrase is not safe. The developer states that strong, random keys of 16 or 32 bytes are impossible to break. However, many people find long, random keys hard to use. They often pick easier passwords, which helps the attacker.
Direct Message Security
Newer versions of the mesh firmware use a different system for private messages between two people. This system is called Public Key Cryptography. It uses the x25519 curve to make keys. Such a system is much harder to break.
The sniffer software still sees the encrypted packets, but it cannot read them without the private key. Even so, the attacker still knows who is talking to whom. They see the sender ID and the receiver ID. They also see when the message was sent and how big it was. This information, called metadata, is very useful for tracking people.
Geolocation and Source Tracking
The third tool, meshtastic-fusion, is perhaps the most dangerous. It allows many sniffer stations to work together. When three or more stations hear the same signal, they find its location. This process does not require the radio to send a GPS position. The stations find the radio by measuring the time it takes for the signal to arrive.
### Hyperbolic Time Difference of Arrival
The mathematical method is called hyperbolic Time Difference of Arrival, or TDOA. Radio waves travel at the speed of light. If a radio is closer to Station A than Station B, the signal arrives at Station A first. By comparing the arrival times, the computer draws a line on a map. With three stations, the lines cross at the location of the radio.
Accuracy depends on how well the stations keep time. A one-billionth-of-a-second difference creates a large error on the map. To solve this, operators use specialized clocks. These clocks get their time from GPS satellites.
| Timing Source | Time Precision | Geolocation Accuracy | Confidence Rank |
| GPSDO + 1PPS | Nano-seconds | < 100 meters | Almost Certain |
| Chrony + PPS | Micro-seconds | ~ 300 meters | Probable |
| Standard NTP | Milli-seconds | > 1000 meters | Unlikely |
The developer claims that accuracy is better than 100 meters with the best clocks. This claim is technically possible but difficult in the real world. Buildings and trees reflect radio waves, which confuses the timing. In an open field, the accuracy is likely very high. In a city, it is probably lower.
Passive Tracking and Geofencing
One major advantage for the attacker is that the system is passive. Traditional direction finding requires a radio that can turn and point toward the signal. The target might see the person with the antenna. The meshtastic-sniffer stations sit silently. They look like normal weather stations or internet routers.
The software also enables geofence alerts. An operator draws a box on a map. If any radio signal comes from inside that box, the software sends an alert. An attacker could use this to monitor a specific house or a road. They would know exactly when a person with a radio arrives or leaves.
Maliciousness and Targeting Strategies
The meshtastic-sniffer suite provides tools for several types of attacks. These attacks range from reading private texts to the physical targeting of individuals. Understanding these strategies is essential for protecting mesh users.
Interception and Intelligence Gathering
The most common use is simple eavesdropping. An attacker listens to the “LongFast” channel, which most people use. They see every text message sent on that channel. Many users discuss their plans, locations, or equipment.
An attacker uses this information to build a profile of the users in the area. They learn who the leaders are and who has the most nodes. The software builds a network link graph. This graph shows which radios communicate most often. It identifies the network’s “hubs”. If those hubs are removed, the whole network fails.
Tactical Mapping and ATAK Integration
The software targets users who use the Android Tactical Assault Kit, or ATAK. ATAK is a map system for military and emergency teams. It shows the location of every team member as a marker on the map.
The meshtastic-sniffer intercepts these location packets. It then turns them into a format that ATAK understands, called Cursor-on-Target. The software broadcasts these markers over a local network. Any attacker with a phone running ATAK sees the team members appear on their screen. The attacker knows the location of the whole team in real time without the team ever knowing.
Manipulation and Deception
While the current suite is mostly for listening, it enables deception. An attacker who knows the channel key can send fake messages. They could send a fake emergency alert to move a team to the wrong place. They could also send fake GPS locations to hide their own location.
Because the mesh uses a “Trust On First Use” model, it is hard to verify the identity of users. A radio stores the first key it encounters as the user ID. If an attacker sends a message first, the network might think the attacker is the real user. This problem is worse because radios have small memories. They often forget old users to make room for new ones. An attacker can send many fake user IDs to push the real users out of the radio’s memory.
Probabilistic Intelligence Assessment
The following assessment uses standard language to rank the likelihood of different outcomes. These rankings help readers understand which threats are the most serious.
Detection Probability
It is almost certain (95%) that a passive sniffer station will remain undetected by the mesh users. Because the sniffer never transmits, there is no radio signal to find with a scanner. A user would have to find the sniffer station to know it is there physically.
Interception Success
It is highly likely (90%) that an attacker will successfully intercept every message in a 5-mile radius if they use a high-end SDR and a good antenna. The wideband receiver’s technical design ensures that the software misses no packets.
Geolocation Reliability
It is probable (75%) that an attacker will find a user’s location within 300 meters using three stations and standard internet timing. Achieving the 100-meter accuracy claimed by the developer is possible (50%) but requires specialized hardware that most attackers might not have.
| Estimative Word | Numerical Probability | Relevance to Sniffer Suite |
| Almost Certain | 93% to 99% | The passive nature stays hidden |
| Highly Likely | 80% to 90% | Wideband capture sees all |
| Probable | 60% to 75% | Default keys are broken |
| Possible | 40% to 50% | 100m accuracy is reached |
| Unlikely | 20% to 30% | Random keys are cracked |
Strategic Consequences for Mesh Users
The existence of the meshtastic-sniffer suite changes the risk for everyone on the mesh. Users must assume that their signals are being watched. This change has several major impacts on how people use these networks.
The End of Simple Privacy
For a long time, mesh users felt safe because they were “off the grid”. They thought their signals were too small or too strange for anyone to find. The sniffer suite proves that this is false. The grid is now everywhere there is an SDR.
Users who require true privacy must use long, random passwords. They must also update their firmware to use the latest encryption methods. Even then, they must realize that their location is still at risk through TDOA tracking.
The Threat to Tactical Teams
Search-and-rescue teams or security groups face the highest risk. They often use the mesh to coordinate in dangerous areas. If an adversary uses a sniffer, they see the whole team’s plan. They see where the team is going and when they arrive.
This threat is not just theoretical. Tools like meshtastic-fusion are designed for “combat” radio reconnaissance. They provide the same capabilities used by professional military units. Any team using a mesh radio today must treat it as an open broadcast that the enemy is likely reading.
Future Implications and Outlook
The environment for mesh radio will likely continue to shift toward more surveillance. As SDR hardware gets cheaper, more people will be able to run sniffer stations. Several trends suggest what might happen next.
AI and Automated Analysis
Future versions of these tools will likely include artificial intelligence to sort through the data. An AI could read thousands of texts and pick out the most important ones. It could learn the habits of mesh users and predict where they will be tomorrow. The meshtastic-sniffer already outputs JSON data, which is perfect for an AI to read.
Wider Bandwidth and More Channels
New SDR boards, like the RFNM, provide over 122 MHz of bandwidth. Such a board would allow a single sniffer to monitor every mesh band in every region simultaneously. An attacker would not even need to set a frequency plan. They would record everything and let the computer find the signals later.
Counter-Surveillance Development
The mesh community will likely develop its own tools to fight back. This might include radios that rapidly change frequency or transmit fake signals to confuse TDOA stations. However, these methods use more power and make the mesh harder to use. The battle between those who talk and those who listen will continue to grow.
The release of the meshtastic-sniffer suite by alphafox02 marks a major point in mesh radio history. It provides professional-level surveillance tools to anyone with a computer and an SDR. The software decodes all mesh network speeds, cracks weak passwords, and locates users’ physical locations.
Evidence from the code and technical tests confirms that these threats are real. While the developer presents these tools for research, their potential for harm is clear. Users of mesh networks must understand that their privacy depends on strong encryption and a deep awareness of passive radio threats. Relying on the radio’s “off-grid” nature is no longer enough to ensure safety.
The probability of targeted monitoring is high in any area where mesh radios are common. Groups that use these radios for tactical or safety purposes should immediately review their security settings. They should use long keys, update their firmware, and limit their transmissions. Silence is the only true way to stay hidden from a passive sniffer, but for those who must talk, the risks have never been higher.





You must be logged in to post a comment.