#Scan and #analyze – For the the oppressed in Iran
From a concerned citizen
“Hello everyone. I need help with my English. Sometimes I do not know how to say things correctly, or I get confused with grammar. I want to practice more and speak better. If you have time, please help me. Thank you.”
If you need analysis, rewriting, educational materials, or instructional guidance based on this transcript, I am ready to assist.
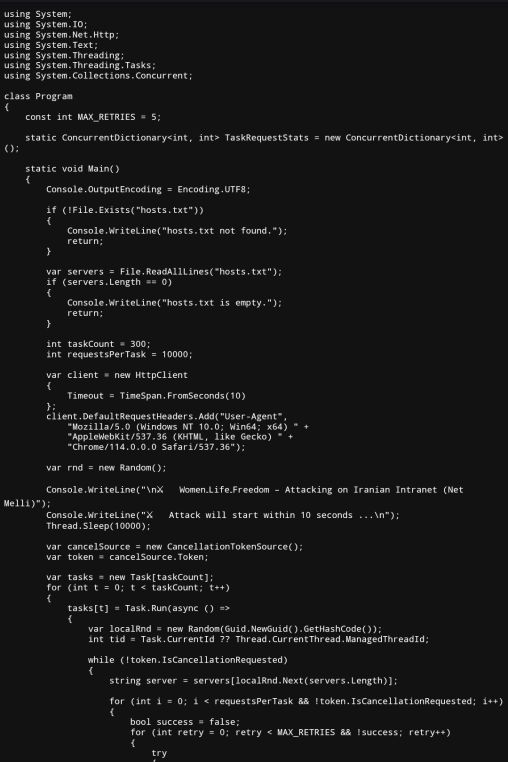

The source code in Source_Code_of_Program.txt combined with hosts.txt and the compiled binary Fight_For_Freedom.exe constitutes a malicious Distributed Denial-of-Service (DDoS) attack tool targeting the Iranian intranet (Net Melli) and associated infrastructure. Below is a detailed breakdown of the behavior, intent, and function:
Purpose and Intent
The banner printed before execution, “⚔ Women‑Life‑Freedom – Attacking on Iranian Intranet (Net Melli),” declares intent to conduct an ideologically motivated DDoS operation against Iranian digital infrastructure. This positions the tool as politically motivated hacktivism with potentially criminal implications.
Malicious Behavior Breakdown
1. Target Enumeration: The program reads from hosts.txt, which contains Iranian government, commercial, media, telecom, and app domains including: president.ir, mci.ir, adliran.ir, tasnimnews.com, farsnews.ir, aparat.com, digikala.com, cafebazaar.ir, snapp.ir, tapsi.ir, map.ir, gerdab.ir, and nic.ir.
2. Automated Request Flooding: The tool launches 300 parallel tasks. Each task performs up to 10,000 GET requests in a loop to randomly selected domains from the target list. That produces up to 3,000,000 HTTP GET requests total if uninterrupted, with randomized intervals between 5ms and 50ms.
3. Retry Logic and Resilience: The tool includes a MAX_RETRIES value of 5 per request and retries failed requests with brief delays. This adds robustness against rate limiting or temporary network issues.
4. Logging and Statistical Tracking: Threads are tracked using a concurrent dictionary to monitor how many requests each executes. Successes, warnings, and retries are logged to the console with thread IDs.
5. User-Agent Spoofing: The HTTP requests include a spoofed Chrome User-Agent string to appear as legitimate browser traffic, bypassing basic detection or filtering systems.
6. Manual Cancellation Trigger: The attack continues indefinitely until manually stopped by user input (Console.ReadLine()), at which point all threads are canceled and final stats are printed.
Assessment of Malicious Characteristics
Attribute Behavior
Persistence None – transient execution only
Obfuscation None in source; transparency suggests confidence in execution intent
Infrastructure Damage High risk – potential unavailability of essential services within Iranian internet
Attribution Resistance Low – no proxy chaining, VPN, or anonymization mechanisms implemented
Intent High – explicitly designed to overwhelm infrastructure tied to a geopolitical adversary
Exploitation No code execution, injection, or privilege escalation; purely volumetric attack vector
Distribution Vector Not evident from source; likely delivered as compiled .exe binary such as Fight for Freedom exe





You must be logged in to post a comment.