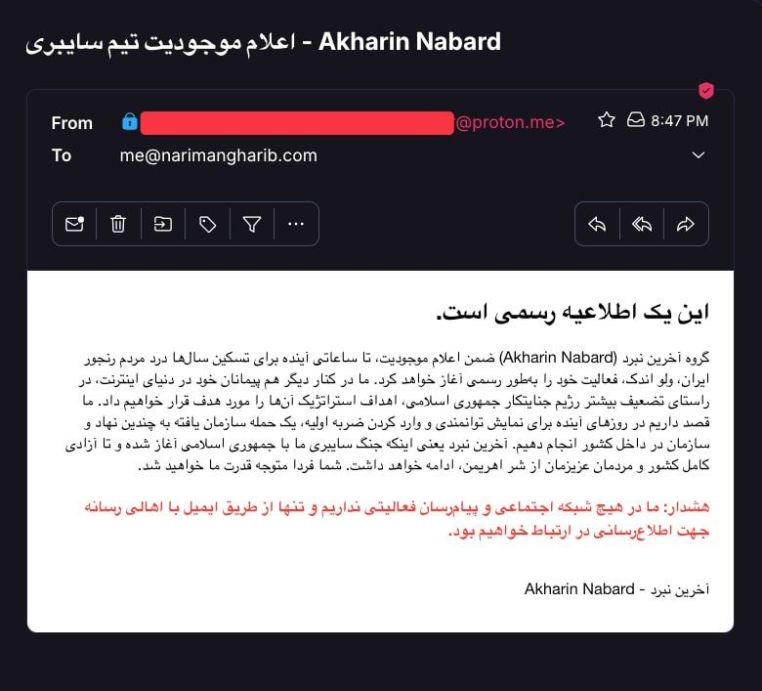
A newly emergent Iranian dissident hacking team that publicly announced its existence in mid-June 2025 amid an escalating Iran–Israel conflict. In an email manifesto sent to Iranian exile journalists, the group declared a cyber war against the Islamic Republic regime, vowing to “strike [the] strategic targets” of the “vile Islamic Republic” in order to “alleviate years of pain of [the] suffering people of Iran” and ultimately to free the country from the regime’s grasp. The announcement indicated imminent action–>
Akhareen Nabard claimed it would launch a “sudden cyber attack” on multiple organizations inside Iran within hours as an initial blow, officially beginning what it calls the “last battle” against the regime. Notably, the group stated it has no social media presence, opting instead to communicate only via email with media contacts – a likely security precaution and a measure to prevent disinformation. The founders’ identities remain unknown, but the ideological orientation is explicitly anti–Islamic Republic and pro-people, echoing the rhetoric of Iranian opposition and hacktivist networks that emerged during recent protest waves. The timing and language suggest Akhareen Nabard positions itself as part of the broader Iranian dissident cyber resistance, aligning with anti-regime hacktivist coalitions that have promised to intensify operations during the ongoing geopolitical crisis.
Caption
Smoke rises over Tehran after a reported Israeli airstrike in June 2025, amid escalating military hostilities.
This kinetic conflict has paralleled a surge in cyber warfare between Iran and anti-Iran actors. In this environment, Akhareen Nabard (“The Last Battle”) announced its formation and vowed imminent cyber operations against Iran’s regime.
Group Profile–Formation & Context
Akhareen Nabard publicly “announced its existence” on June 17, 2025 via a statement emailed to Iranian journalists. The backdrop is a sharp escalation in Iran–Israel hostilities, including Israeli strikes on Iranian military/nuclear sites and reciprocal missile attacks. Cyber conflict has intensified alongside the shooting war–>Israeli-linked hacker teams have launched destructive attacks on Iranian infrastructure, while Iran’s cyber units strike back at Israeli targets. In this charged climate, Akhareen Nabard portrays itself as a patriotic Iranian hacktivist unit rising to wage a decisive digital battle against Tehran’s regime.
The group’s name – “The Last Battle” – implies a final confrontation, a do-or-die effort to bring down the Islamic Republic. This framing resonates with the rhetoric of Iranian opposition movements who see the current crisis as an opportunity to topple the regime. Akhareen Nabard explicitly casts its mission in grand terms: it announced that its cyber war with the Islamic Republic has begun and will continue until Iran and its people are completely free. The group claims to stand “alongside [its] allies in the internet world” – suggesting affiliations with other hacker collectives or supportive foreign actors – to deliver heavy blows to the regime’s apparatus. While newly formed, the group’s messaging and methods place it in the lineage of Iranian dissident cyber groups that have emerged since 2018 to challenge the regime during protests and crises. Like those predecessors, Akhareen Nabard is likely composed of exiled or underground tech-savvy activists (possibly with help from foreign intelligence) intent on sabotaging regime assets as a form of resistance.
Ideology and Motivation
The group’s ideology is unequivocally anti-regime and framed as pro-people. In its manifesto, Akhareen Nabard invoked the “years of pain” endured by ordinary Iranians and presented its cyber-attacks as retribution and relief on behalf of the Iranian people. This aligns with the narrative of prior Iranian hacktivist outfits that justified their hacks as acts of protest against corruption, repression, and the regime’s diversion of national wealth to malign activities. For instance, the Iranian hacker group Tapandegan (“Palpitaters”) similarly defaced airport screens in 2018 with messages protesting the regime’s costly regional adventures and economic mismanagement. Akhareen Nabard’s rhetoric – referring to the Islamic Republic as “palid” (wicked/unclean) and promising to continue until “complete freedom” – echoes the maximalist goal of regime change. This suggests ideological synergy with secular pro-democracy activists and possibly with opposition networks like the MEK (Mujahedin-e Khalq) or royalist “restart” hackers, though the group does not explicitly cite any faction. The group likely aims to appeal broadly to all regime opponents by using inclusive, nationalist language (e.g. “our dear people”) and avoiding partisan symbols. Its promise to coordinate with “other allies in cyberspace” hints at a collaborative orientation – possibly leveraging the global hacktivist community (e.g. Anonymous cells that supported Iran’s 2022 protests) or even covert partnerships with states hostile to Tehran. In sum, Akhareen Nabard’s profile is that of a hacktivist insurgent unit emerging from Iran’s opposition milieu, catalyzed by the war context to take bold action it sees as the “final battle” against an illegitimate regime.
Intent & Strategic Objectives-Stated Intent
According to its founding statement, Akhareen Nabard’s immediate intent is to conduct a wave of cyber-attacks on high-value regime targets inside Iran, commencing within “the next few hours” of its announcement. The group described the first operation as a sudden, simultaneous cyber strike on several institutions and organizations – effectively an opening salvo to demonstrate its capabilities and inflict shock on the regime. By “strategic targets,” the hackers likely mean critical nodes of the government’s power structure or economy. The email explicitly framed this as the initial blow in a broader campaign, indicating a sustained operation rather than a one-off stunt. The ultimate strategic goal, as declared, is regime destabilization and eventual overthrow through cumulative cyber sabotage. “The Last Battle means our cyber war… will continue until the complete freedom of our country and people from the regime’s clutches,” the group proclaimed, underscoring that its endgame is nothing short of the Islamic Republic’s collapse. In effect, Akhareen Nabard intends to use cyber means to advance what Iranian opposition on the ground have failed to yet achieve – the weakening or collapse of regime control. This aligns with known anti-regime digital sabotage campaigns in recent years, where hacker groups seek to erode the government’s authority by exposing its secrets, draining its resources, and disrupting its functions.
Implied Targets & Scope
Though the group has not publicly named specific targets, its wording and the context allow some inference. “Strategic” regime targets likely include: government ministries and state agencies, especially those tied to security or propaganda; critical infrastructure sectors (energy, transportation, finance) that are pillars of the state’s stability; and military-industrial assets (e.g. IRGC-owned companies, defense networks). Recent precedence supports this: in parallel with Akhareen Nabard’s emergence, an established anti-regime hacker crew “Predatory Sparrow” targeted Iran’s Bank Sepah (a major state bank financing the IRGC) and claimed to have destroyed its data, and even Iran’s largest crypto exchange was hacked to seize funds and punish sanction-evasion. Those attacks were justified by accusing targets of funding the regime’s military and “terrorism”. It is very likely Akhareen Nabard will pursue similar high-impact targets: banks, exchanges, or economic infrastructure linked to the Revolutionary Guards; key government communication platforms (state media, ministries’ sites); and possibly Iran’s critical services (power grids, transit systems, or nuclear facilities) if they have the capability. During Iran’s 2022 protest crackdown, dissident hackers showed interest in such targets – for example, the group Black Reward breached the Atomic Energy Organization’s email server to leak sensitive nuclear project data in solidarity with protesters. Akhareen Nabard’s promise to act “in the coming days” suggests a campaign that could escalate from initial chaos (e.g. defacing websites or DDoSing services) to deeper penetrations like data theft, hack-and-leak operations, and destructive attacks on infrastructure. Indeed, past anti-regime hacks evolved in this way: Tapandegan moved from display defacements to leaking internal government correspondence exposing corruption, and another group, Lab Dookhtegan, systematically dumped cyber-espionage tools and passwords from Iran’s own APT units to sabotage them. Akhareen Nabard likely aims for a similarly comprehensive campaign: embarrassing the regime by publishing its secrets while also hampering its ability to govern (through outages or data destruction).
Alliances and Affiliations
A notable phrase in the manifesto is that the group operates “alongside [its] other allies in the world of the internet.” This implies coordination with one or more existing hacker collectives. Possibilities include the amorphous Anonymous hacktivist network – which in 2022 carried out website defacements and service disruptions in support of Iranian protesters – or other Iran-focused dissident teams (some of which are believed to be affiliated with exile opposition parties). Another plausible reading is coordination with foreign cyber units. For example, Predatory Sparrow (Gonjeshke Darande), widely believed to be an Israel-aligned operation, has been conducting concurrent attacks as part of Israel’s broader retaliation against Iran. It is conceivable that Akhareen Nabard is serving as a public hacktivist front or proxy for a state-led cyber offensive, providing deniability to foreign sponsors. The group’s communication method – discrete emails to media, no public channel – is reminiscent of how Lab Dookhtegan operated (Lab Dookhtegan quietly leaked Iranian cyber-spy files via Telegram to journalists in 2019, suspected as a Western/Israeli intel front). If Akhareen Nabard has backing from or links to such sponsors, its attacks could align with those nations’ strategic objectives (e.g. hitting Iran’s military, nuclear, or financial sectors in tandem with kinetic strikes or economic pressure). On the other hand, if it’s a grassroots collective of Iranian hacktivists, its “allies” might refer to sympathetic tech activists worldwide offering knowledge or infrastructure (VPNs, botnets, etc.). Either way, the group’s framing of a united cyber front hints that its operations won’t occur in isolation – they form part of a broader trend of anti-regime cyber sabotage that has accelerated during the Iran–Israel confrontation.
Strategic Goals
In strategic terms, Akhareen Nabard seeks both psychological and material impact. Psychologically, successful cyber-attacks on high-profile regime targets can undermine the regime’s aura of control and invincibility, bolstering the morale of protesters or dissenters. For example, when hackers posted anti-Khamenei messages on state TV or airport monitors in past incidents, it had an outsized propaganda effect, signaling regime vulnerability. We can expect Akhareen Nabard to similarly publicize its attacks to embarrass the leadership – possibly releasing videos of disruptions or troves of internal documents that reveal regime abuses. Materially, the group likely aims to inflict tangible damage on regime capabilities. Disrupting banking systems or stealing funds, for instance, hits the state’s pocket and may sow public distrust in financial stability. Shutting down services (fuel distribution, transportation networks, etc.) can create internal chaos, stretch the regime’s crisis management, and even spark public anger at government incompetence – as seen when gas station payment systems were hacked in 2021, causing days of queues. The ultimate strategic intent – if sustained with enough force – would be to weaken the regime’s grip such that either popular uprisings intensify or elements within the system lose confidence and defect. In essence, Akhareen Nabard sees cyber warfare as a new front to achieve the goals of the Iranian opposition movement: destabilize the Islamic Republic and hasten its collapse.
Known or Prior Activities
Because Akhareen Nabard is brand new, it has no confirmed prior operations under that name. Its credibility will be judged by what happens following its declaration. However, analysts are scouring for any “digital footprints” that might link this persona to earlier known attacks or identities:
Precursor Identities
It’s possible that Akhareen Nabard is a rebranding of an existing hacktivist entity. In the past, Iranian dissident cyber actors have changed monikers or worked in concert. For instance, the group Edalat-e Ali (“Ali’s Justice”) surfaced in 2021 by leaking Evin prison abuse videos, and those videos were later amplified by Tapandegan’s channels, showing interplay between groups. One might ask if members of Edalat-e Ali or Tapandegan are involved in this “Last Battle” initiative. The tone of Akhareen Nabard’s message (patriotic and justice-oriented) certainly resembles Edalat-e Ali’s and Tapandegan’s communiqués, which condemned regime injustices and vowed to expose them. Another possibility is linkage to Ghiam ta Sarnegouni (“Rise Until Overthrow”), a coalition that hacked Iranian state media and leaked regime documents during the 2022 protests, often suspected of ties to the MEK. Akhareen Nabard’s maximal name and aim (final battle until total freedom) sound in spirit like “ghiam ta sarnegouni”. If so, the new group could be essentially a cyber cell of Iranian dissidents (possibly MEK-affiliated “rebel units”) stepping up amid the war – not unlike how in March 2022, MEK-linked hackers defaced dozens of government sites and wiped servers in the Ministry of Culture. In that attack, slogans and images of MEK leaders were used, whereas Akhareen Nabard has, so far, kept a lower ideological profile, perhaps to attract wider support.
OSINT Clues
Open-source intelligence hasn’t yet tied “Akhareen Nabard” to known hacker infrastructure or tooling. The group used a ProtonMail address to send its announcement – a common choice for threat actors needing anonymity and security. No Telegram or website has surfaced (the group warns it has none, to prevent impostors). Researchers will likely look at the techniques used in any imminent attack by Akhareen Nabard to see if they match known malware or methods from past campaigns. For example, if a custom wiper malware is deployed, it could be compared against Indra’s wipers or Predatory Sparrow’s toolset for code similarities. If the group publishes stolen data, analysts might examine the breach vectors (phishing emails, supply-chain compromise, etc.) for patterns seen before. At present, aside from the manifesto, the only footprint is the claim of pending action – which means the world is essentially on watch for the group’s debut attack to define its reputation.
Relation to State Actors
Given the war context, one must consider if Akhareen Nabard is essentially an alias or cut-out for a state-led cyber offensive. Iran’s adversaries (Israel, the U.S., others) have previously masqueraded as hacktivists to conduct cyber ops without direct attribution. The 2019 Lab Dookhtegan leaks of Iran’s APT34 were likely Western or Israeli intelligence in origin, yet they were presented as the work of an “unknown group” angry at the regime. Similarly, Indra, the group behind the 2021 Iran railway hack, outwardly identified as “regime opposition”; however, some experts questioned if a nation-state was pulling the strings because of the sophistication involved. If Akhareen Nabard’s forthcoming attacks display advanced capabilities (e.g. multi-stage intrusions, use of zero-day exploits, or coordinated network outages across domains), this will raise suspicions of state backing. An indicator will be scale: truly independent hacktivists might deface a few websites or leak documents, but wiping out entire databases or causing physical damage (e.g. to industrial systems) typically requires APT-level resources. For now, the group has positioned itself in the public eye similarly to prior anti-regime hacktivists (not explicitly naming a state sponsor, using Iranian nationalist language). Whether that is genuine or a convenient cover remains to be seen.
Prior to its first confirmed operation, Akhareen Nabard’s “resume” is mostly its alignment with a pattern of Iranian opposition cyber actions. It has explicitly tied its mission to those historical efforts by referencing “other allies” and the common goal of regime downfall. The group’s credibility will hinge on delivering results comparable to those earlier hacks – e.g. causing a notable disruption or leak. If it fails to manifest attacks, it could be dismissed as a psy-op or bluff. But if it succeeds, it will join the ranks of significant Iranian dissident threat actors.
Tactics, Techniques, and Procedures (TTPs)
Anticipated Attack Methods
While we await the full reveal of Akhareen Nabard’s tactics, their announcement and the modus operandi of analogous groups provide strong hints. Likely TTPs include:
Coordinated Multi-Target Attack
The group specifically mentioned a “sudden cyber attack” on several entities as an initial demonstration. This implies a coordinated strike, possibly launching malware or exploits against multiple networks in quick succession. This could be done via a supply-chain compromise (if the targets share a common software or service provider) or through pre-positioned access in each target that the attackers activate simultaneously. For instance, the Indra group in July 2021 managed to paralyze Iran’s train system and deface railway station displays all at once, suggesting careful pre-infiltration and timing. Similarly, Black Reward in 2022 breached an entire email system of Iran’s Atomic Energy Organization and then dumped the data in one go. Akhareen Nabard may follow these models, hitting multiple ministries or companies at the same time for shock value.
Defacement & Propaganda Injection
As a dissident hacktivist operation, we expect the group to leave political messages in any system it compromises. This could include website defacements (replacing homepage content with manifestos or protest imagery) and hijacking of digital signage or broadcasts. Past groups like Tapandegan excelled at this: they took over airport monitors to display anti-IRGC slogans and protest photos, and even infiltrated state TV briefly to air anti-Khamenei visuals. Akhareen Nabard could attempt to deface government web portals or intranets with its “Last Battle” branding and calls to uprising. Another vector is SMS/email broadcast if they compromise an official communication system, they might send mass messages to citizens or officials with their statements (as Tapandegan did by emailing members of parliament from a hacked municipal account).
Data Breach & Leak (Hack-and-Leak)
It is highly probable the group will employ data exfiltration for exposure of regime secrets. Nearly all notable anti-regime cyber groups have used stolen information as a weapon. For example, Lab Dookhtegan leaked internal passwords, hacking tools, and victim logs of Iran’s cyber espionage unit (APT34) to cripple its operations. Tapandegan similarly published leaked letters and confidential documents revealing IRGC economic corruption (e.g. secret orders and business deals). Even Predatory Sparrow, known for destructive hacks, has dumped data from time to time to support its claims. Akhareen Nabard, by targeting “strategic” institutions, likely aims to obtain sensitive internal emails, databases, or files from those targets – and then release them to media or on forums. The content could range from evidence of human rights violations, to financial records showing graft, to technical information that embarrasses or hinders the regime (such as blueprints of nuclear sites or lists of intelligence operatives). A dramatic leak would both validate the hackers’ penetration and serve their propaganda goal of shaming the government.
Destructive Attacks (Wipers/Ransomware)
The phrasing “strike… strategic targets” and the allusion to delivering more “blows” suggest Akhareen Nabard may not be satisfied with just stealing data – they likely intend to damage or disrupt the functioning of their targets. This could involve deploying wiper malware to erase data and cripple systems. Indra famously used custom wipers to destroy data on Syrian companies’ networks and on Iran’s train control systems, effectively “locking users out of machines, changing passwords and wiping entire systems” to maximize disruption. In some cases, these wipers were disguised as ransomware (demanding ransom that was not actually collectible, purely to confuse incident responders). Predatory Sparrow likewise caused a physical sabotage: its cyberattack on an Iranian steel mill in 2022 induced an equipment failure and fire. If Akhareen Nabard has similar capabilities or backing, they might attempt to trigger outages in critical infrastructure. Possible scenarios include: wiping banking system servers (to erase account records or disable transactions), sabotaging industrial control systems at power plants or refineries (leading to shutdowns or accidents), or corrupting government databases (e.g. deleting or altering land registries, passport records, etc.). In the war context, even infrastructure that supports the military (like rail lines used for logistics or telecom networks) could be targeted with destructive malware to impede Iran’s war effort. However, such complex attacks require advanced skill; it remains to be seen if Akhareen Nabard possesses it. At minimum, they could use readily available ransomware/wiper tools to damage less secure targets and “make a loud statement.”
DDoS (Denial-of-Service)
Volume-based attacks to overwhelm websites or online services might also be part of the toolkit, though these are more transient. During past protest waves, Anonymous-affiliated hackers routinely launched DDoS attacks on Iranian government sites, causing temporary outages. Given that Akhareen Nabard emphasizes a sudden attack, they might coordinate DDoS strikes to coincide with their hack-and-leak or defacement operations, thereby amplifying the disruption. For instance, if they hack a ministry and start wiping its servers, they could simultaneously DDoS its public website and email servers to slow the response and communication. DDoS by itself is less impactful on “strategic” targets (since it doesn’t penetrate data), but as a supporting tactic it can increase pressure and visibility.
Phishing & Social Engineering
To gain initial access, the group will likely rely on spear-phishing and credential theft – a tried-and-true technique in both state-sponsored and activist hacks. Many Iranian institutions have been compromised in recent years via phishing emails (often imitating trusted senders) that delivered malware or stole passwords. The success of operations like Black Reward’s nuclear agency breach or Edalat-e Ali’s prison CCTV hack presumably started with tricking insiders or exploiting weak passwords. Akhareen Nabard, if composed of veteran hacktivists, may already have a trove of breached credentials (possibly shared among the anti-regime hacker community). They could use those to log into systems or VPNs. Alternatively, they might deploy malware-laced documents (e.g. a fake official letter luring officials to open it) to get a foothold. Given the group’s likely small size and lack of an apparent zero-day arsenal, social engineering is the most plausible initial vector for them to infiltrate multiple targets relatively quickly.
Operational Security and Communication
It’s worth noting the group’s OPSEC choices as part of their “tactics.” By forgoing social media or public channels, they reduce the risk of their communications being hijacked or traced. ProtonMail provides end-to-end encryption and anonymity for correspondence. This suggests a degree of sophistication – they are wary of counter-intelligence. It also implies they will rely on third-party reporting (journalists and outlets) to broadcast their accomplishments and communiqués. In practice, after each attack, we can expect Akhareen Nabard to email proof (screenshots, data samples) to known anti-regime journalists or outlets like Iran International or BBC Persian, who can then publish the story. This mirrors how Lab Dookhtegan shared leaked data with the media, or how Predatory Sparrow posts claims on Telegram which are then picked up by news sites. The group’s warning about impostors suggests they anticipate regime cyber units might create fake “Akhareen Nabard” profiles to muddy the waters – a common tactic by Iranian state actors to confuse narratives. By controlling info release tightly, the group tries to ensure their TTPs (tactics, techniques, procedures) can’t be easily dissected or countered in real-time by the regime.
Capabilities Assessment
Technical Capability
At this early stage, Akhareen Nabard’s true technical prowess is unproven. However, their ambition to hit multiple strategic targets hints at a moderate to high capability, at least in planning and coordination. The fact that they confidently gave a short timeline (“within hours”) for launching an attack suggests they may already have access to some targets or exploits ready to fire. If the group were inexperienced or bluffing, they would likely not risk such a definitive time-bound claim. Thus, we assess that Akhareen Nabard has at least a few skilled operators with access to relevant tools or credentials. They might benefit from prior breaches: for example, massive leaks of Iranian networks (like the 2021 leak of 5,000 surveillance camera feeds or credentials leaked by Lab Dookhtegan) could furnish the group with entry points. It’s also possible they share resources with more established actors. If any ties exist with Israeli agencies or Western cyber commands, the group could have covert access to advanced malware or intelligence on vulnerabilities in Iranian systems (e.g. known unpatched flaws or insider contacts).
However, we should also consider that many hacktivist groups inflate their abilities. The “credibility of threats” remains to be validated. Iran’s government will certainly be on high alert now – its National Cyber Headquarters has already warned of “widespread enemy cyber efforts to disrupt services”. So the element of surprise may be reduced. If Akhareen Nabard’s attempted attacks are detected and blocked, their actual capability might prove more limited (script kiddie-level DDoS or basic web defacements which the regime can quickly contain). On the flip side, if the group manages to pull off something like taking down parts of the electric grid or erasing bank records, that would signal a top-tier capability often associated with state actors. Given historical precedent, it’s plausible Akhareen Nabard can at least achieve medium-impact breaches (e.g. leaking tens of gigabytes of internal emails, or defacing prominent sites). Many prior dissident hacks in Iran have achieved such outcomes without full nation-state resources – often through persistence and exploiting known weak points like default passwords or insider cooperation. For instance, Edalat-e Ali reportedly accessed 150 security cameras in Evin prison because guards used a very weak password (“123456”). Similarly, GhyamSarnegouni (Uprising till Overthrow) hacked the Fars News agency in 2022, likely via phishing an employee, and exfiltrated databases including security memos. These suggest that with determination and some insider knowledge, activist hackers can penetrate “secure” systems of Iran. Akhareen Nabard, coming after these events, likely has learned from those successes.
Threat to Critical Infrastructure
One focus of analysis is whether Akhareen Nabard poses a genuine threat to civilian infrastructure or lives. Their manifesto couches actions as being for the people, implying they will avoid wanton damage that directly harms civilians. We can expect them to target regime institutions, but many such institutions (banks, transit, power) also serve the public. For example, if they knock out banking systems, ordinary Iranians could lose access to money – a tactic that might backfire by causing public anger. If they shut down parts of the electric grid or railways, civilians could be endangered. Groups like Indra and Predatory Sparrow seem cognizant of this balance: Indra’s railway hack, while disruptive, was done by posting fake delay messages and locking IT systems rather than derailing trains. Predatory Sparrow claimed its steel plant hack was timed to avoid casualties (hitting an empty facility on a holiday) – an assertion to maintain moral high ground. It’s likely Akhareen Nabard will follow a similar ethic: high-impact but low-casualty operations. They might focus on data-centric attacks (financial data, confidential files) and symbolic targets (e.g. disabling a regime TV network or a government portal) that embarrass the regime more than hurt the populace. That said, in the fog of cyber war, miscalculations can occur. If the group attempts something like disrupting air traffic control or hospital systems (hopefully unlikely given their stated cause), that would cross into dangerous territory. As of now, there’s no indication they intend to harm civilians; their wrath is directed at the regime’s “strategic infrastructure” – presumably meaning the regime’s power centers (military, security, propaganda, finance).
Resource & Skill Indicators
The group’s use of ProtonMail and lack of social media show they understand basic operational security, which points to experience. The speed of planned operations (“in the coming hours/days”) suggests they have operational readiness – either through prior reconnaissance or through leveraging ongoing attacks by others. For instance, if Israeli hackers have already infiltrated certain Iranian networks during this conflict, Akhareen Nabard could possibly piggyback on that. It’s notable that just one day before their email, Predatory Sparrow knocked Iran’s Bank Sepah offline and presumably created chaos in banking. It’s conceivable Akhareen Nabard might take advantage of the disarray or vulnerabilities opened by that attack to hit related systems. In cyber warfare, attackers sometimes coordinate or follow one another’s strikes to compound effects. If such coordination is happening, it would elevate Akhareen Nabard’s capacity far beyond a lone group – essentially acting as part of a multi-pronged cyber campaign.
While we cannot yet quantify Akhareen Nabard’s technical skill with certainty, early signs and contextual clues indicate they are more sophisticated than the average hacktivist group that Iran has seen in the past. They appear to at least match the caliber of groups like Tapandegan and Edalat-e Ali, who penetrated high-level systems, and they may even align with the capabilities of Indra or Predatory Sparrow if foreign support is involved. We will know more once their first attacks either succeed or are thwarted.
Propaganda and Messaging
Narrative and Themes
Akhareen Nabard’s propaganda content (as gleaned from its initial communiqué) centers on liberation, justice, and retaliating against tyranny. Key themes include: portraying the Islamic Republic as an evil that must be vanquished (“regime palid (vile)”), positioning the hackers as saviors fighting on behalf of the oppressed (“years of pain of our people”), and framing cyber warfare as a legitimate and necessary front in the struggle for Iran’s future (“our cyber war… will continue until freedom”). This narrative dovetails with the messaging of Iran’s broader opposition and protest movements – where hacktivists cast themselves as extensions of street protesters in cyberspace. For example, during the 2019–2022 protests, videos of hacktivist actions often carried slogans like “We are with you” to the Iranian people, and content aimed to delegitimize the regime. We see Akhareen Nabard adopting a similar tone of righteous rebellion.
Expect the group’s propaganda to emphasize regime vulnerabilities and victories of the resistance. If they succeed in attacks, their statements will likely highlight what was compromised and tie it to regime wrongdoing. For instance, should they leak officials’ communications, they may annotate those leaks with explanations of corruption or crimes revealed. This was a tactic used by others: the Edalat-e Ali group, when leaking prison footage, explicitly stated it was to expose torture and human rights abuses; Tapandegan, when exposing IRGC economic meddling, framed it as proof of the regime betraying Khamenei’s orders and public trust. Akhareen Nabard, given its grandiose name, might also invoke historic or patriotic motifs – such as likening their cyber “battle” to past Iranian struggles against tyranny (perhaps drawing on imagery from the 1979 revolution or even earlier Persian history).
Their choice of name “The Last Battle” itself is propagandistic: it signals to supporters that the final phase of conflict is here. It’s almost apocalyptic language, possibly meant to inspire a sense of urgency and unity against the regime. This can galvanize other activists and foment hope that the regime is on its last legs. Conversely, it’s also psychological warfare against the regime’s rank-and-file: implying “we will fight to the bitter end, your time is up.” If the regime’s personnel believe multiple powerful hacker groups (domestic and foreign) are converging to attack, it could sow paranoia and demoralization. Already, Iranian officials have expressed alarm about hackers targeting “vital networks, banks, and even military” and have urged their IT staff to be extra vigilant. Akhareen Nabard’s messaging will aim to amplify that alarm.
Channels and Language
As noted, the group is not using public channels like Telegram or Twitter under its own name – at least for now. Instead, it relies on trusted journalists and opposition media to relay its propaganda. For example, Nariman Gharib (to whom the email was sent) and outlets like Iran International are likely to publish the group’s claims. This gives the group a level of credibility and reach; Iran International, BBC Persian, etc., have large audiences and are followed by regime insiders as well. It’s a savvy strategy: by feeding scoops to these media, the group ensures its message is reported widely (often translated to English too), without it having to maintain its own servers or channels that could be taken down or tracked. We saw a similar pattern with Predatory Sparrow: after each major hack, they posted statements on a Telegram channel, which were then immediately picked up by international press. Akhareen Nabard is essentially cutting out the middle step and giving the news directly to press. This also wraps its propaganda in a veneer of journalism, potentially making it harder for the regime to dismiss as just “enemy propaganda” – because it’s delivered as a news story of a breach.
In terms of content style, their first message was in Persian (with the group name also provided in Latin script). Future communications might continue primarily in Persian to directly address Iranian authorities and people. However, they may also issue English summaries or allow media to quote them in English, to reach a global audience and influence international perception of Iran (painting the regime as under siege and vulnerable, perhaps to encourage foreign solidarity or caution foreign businesses about dealing with Iran).
Propaganda Targets
The propaganda is aimed at multiple audiences
Domestic Iranian audience: to encourage citizens that the regime is faltering and that resistance is active even in cyberspace. They want ordinary Iranians to cheer the blows against hated institutions (e.g., seeing Bank Sepah down or IRIB hacked likely elicits satisfaction among dissenters) by causing high-profile disruptions and leaks. They might even inspire more insiders to leak info or sabotage from within, if those insiders feel the momentum of “the last battle.”
Regime elite and security forces: to instill fear and confusion. If officials know hackers may be reading their emails or could hit their infrastructure at any time, it breeds distrust internally. After past hacks, Iranian ministries often conducted internal purges or communications lockdowns, disrupting their workflows out of fear of spies. Akhareen Nabard’s propaganda will aim to exacerbate that, making the regime waste time on defensive measures and witch-hunts. Their messaging “we have allies everywhere online” is essentially a warning that “you’re surrounded digitally.”
International audience (especially allied to opposition) to gain support and recognition. They can rally the Iranian diaspora, human rights organizations, and possibly friendly governments to their cause by publicizing their actions If, say, they expose evidence of Iranian officials’ crimes, that could bolster calls for sanctions or legal action abroad. They might tailor some messages to highlight how their hacks protect the world (e.g., preventing Iran from funding terror – a narrative Predatory Sparrow used). This appeals to Western sensibilities and could indirectly attract resources or safe haven for the hackers.
Rival hacktivist or APT groups
Interestingly, propaganda can also be a signal to other hacker groups. Akhareen Nabard claiming the mantle of “The Last Battle” may be a bid to coordinate or even compete with groups like Indra, Sparrow, Anonymous, etc. If they achieve notable successes, they could become a central rallying brand for anti-regime cyber efforts, potentially unifying disparate actors under the “last battle” narrative.
In essence, Akhareen Nabard’s propaganda content is poised to be a mix of political proclamation, psychological warfare, and celebratory communiqués of cyber victories. We should expect them to capitalize on every successful hack with a statement that not only claims credit but frames it in the context of their ultimate goal (e.g., “this attack brings us one step closer to the regime’s end”). On the flip side, they will likely remain silent or vague about failures, to maintain an image of strength.
Potential Impact and Escalation Paths–Threat Impact on Regime and Civil Sector
If Akhareen Nabard’s campaign unfolds as threatened, the impacts could span government operations, critical services, economic stability, and public morale. Some projections:
A successful attack on multiple ministries or state databases could cripple administrative functions. Imagine if the hackers wipe or encrypt internal servers of, say, the Ministry of Interior, or the national ID database – government services could halt, causing chaos for citizens needing paperwork, and hampering coordination of war or security efforts. This directly impacts governance and could erode citizens’ already-waning trust in the state’s competence to provide services.
Strikes on financial institutions (banks, exchanges, central bank systems) are particularly dangerous to the regime. We’ve already seen Bank Sepah taken offline by other hackers. Should Akhareen Nabard extend such attacks – e.g. targeting Bank Mellat or the central banking infrastructure – it could trigger bank runs or financial panic. Rob Joyce (NSA official) noted that disrupting a major bank’s data can have “major impacts” on trust. If people suddenly can’t access accounts or suspect their savings might vanish due to hacks, the economic fallout and public anger toward the regime would surge.
Critical infrastructure outages
If the group can cause blackouts, telecom outages, or transportation disruptions, this would have immediate societal consequences. Given Iran’s adversarial posture, severe outages might even be interpreted by the public as signs of wartime defeat (imagine parts of Tehran losing power or internet – people might think the country is collapsing under attack). That could either spark panic or, conversely, inflame anti-regime protests as citizens blame the leadership for bringing them into a disastrous war. In 2021 when gas pumps were hacked, there were instances of drivers chanting against the Supreme Leader while stuck in fuel lines, cursing his “incompetence”. Similar scenes on a broader scale would be a political nightmare for Tehran.
Military and security implications
If Akhareen Nabard or its allies target military command networks, intelligence databases, or defense industries, it could degrade Iran’s ability to conduct war or internal repression. For example, leaking lists of intelligence officers or IRGC members (as some hacks have done) exposes them to danger or sanctions and hurts morale. Disabling parts of air defense or disrupting communications at critical moments could have direct impact on the physical battlefield (though such high-level capabilities are more likely in the realm of state cyber units like Israel’s Unit 8200 rather than independent hackers). Still, even smaller acts – like jamming police radio networks or defacing surveillance systems – could aid on-the-ground opposition activity.
Civilian collateral
There is a risk of collateral impact on civilians. If the group’s attacks overshoot (for instance, knocking out the power grid could endanger hospitals or vulnerable populations), this could turn some public sentiment against the hackers or be used by regime propaganda to paint them (and by extension, the opposition) as reckless traitors. The regime would surely exploit any such mishap. Thus far, successful dissident cyber ops have been careful to minimize direct civilian harm, and hopefully Akhareen Nabard will follow suit.
Escalation with Regime Countermeasures
The Iranian government is not a passive victim in cyber space; we anticipate significant countermeasures and retaliation. Likely responses include:
Strengthened Cyber Defense and Isolation: Iran might temporarily disconnect or isolate critical networks (a “cyber curfew”) if attacks intensify. Already, reports indicated some international internet links were disrupted in Iran after the latest attacks, as a defensive measure. The regime may ramp up its “National Information Network” (intranet) usage to keep vital services running offline from the global internet. This could mitigate some external hack threats but also slow everyday operations (and itself generate public frustration at service outages).
Internal Security Crackdown
The Ministry of Intelligence (MOIS) and IRGC Cyber units will hunt for any insider collaborators or negligent personnel that enabled breaches. Expect increased vetting of IT staff, possibly detentions or harsh punishment for suspected leakers. This could create a climate of fear among government tech workers, ironically leading to more mistakes or disloyalty. But in the short term, the regime’s cyber teams will be in high alert mode, likely foiling some amateurish attacks. If Akhareen Nabard uses known exploits, Iran’s cyber defense (CERT teams) might contain damage quickly.
Counter-Hacking & Misinformation
The regime might deploy its own hacker groups or bots to counter Akhareen Nabard’s info war. As mentioned, they could create fake “Last Battle” channels claiming things to discredit the group. Or they could unleash doxing attacks – for instance, hacking opposition figures and falsely attributing it to Akhareen Nabard’s failure, or leaking fake “communications” to tarnish the group’s image (e.g., claiming the group is funded by CIA or Mossad to reduce local support). Iran’s state media will almost certainly call the group “terrorists” or foreign agents, and if possible, show “evidence” of such links to undermine the group’s patriotic narrative.
Cyber Retaliation Abroad
If Akhareen Nabard is seen as working in concert with Israel or Western entities, Iran may retaliate in cyberspace against those nations’ interests. The Independent Persian report suggests American companies could become targets as Iran and Israel trade cyber blows. Indeed, Iranian APTs (like Charming Kitten, Phosphorus, etc.) might be unleashed to hit Israeli infrastructure or even attempt to breach media and tech platforms used by dissidents. In previous episodes, Iran responded to Israeli cyber actions by attacking soft targets like civilian infrastructure (e.g., the attempted hack on an Israeli water facility in 2020). We might see analogous strikes if they blame Akhareen Nabard’s successes on Israeli backing.
Physical Response
While less likely directly, the line between cyber and kinetic might blur. If the group significantly damages critical systems, Iran might lash out kinetically at perceived culprits (for example, targeting opposition groups physically or even striking at Israel if they think Israel was behind a catastrophic cyberattack). Similarly, Israel might escalate airstrikes if Iranian hackers (state or proxy) manage to hit sensitive targets in Israel. The cyber operations are happening “behind the scenes” of the aerial exchanges, but a big cyber event (like a major blackout or a successful hack of military systems) could influence the trajectory of the broader conflict.
Projected Evolution Paths
There are a few scenarios for how Akhareen Nabard’s campaign could evolve in the coming weeks:
1. High-Impact Successful Campaign: In this optimistic (for the group) scenario, they execute one or several major attacks as promised – e.g., disabling a significant regime service or leaking explosive documents. This would instantly cement their credibility. If successful, Akhareen Nabard would likely expand operations, either by recruiting more members or receiving more support from allies. We could see a series of escalating attacks, each hitting a different sector: one day the banking system, next day state media, then perhaps an airport or power facility. The regime might struggle to plug all holes, especially under war pressure. This scenario could contribute to a cascading failure in Iran’s infrastructure or trigger mass unrest (if, say, communications are down or salaries can’t be paid due to IT chaos). The “last battle” could then truly become a multi-front internal crisis for Tehran. Internationally, this level of success might prompt emergency diplomatic efforts or even interventions to prevent humanitarian fallout (for instance, the U.S. might quietly assist in cyber defense for critical civilian systems to avoid catastrophe, even while opposing the regime).
2. Limited but Symbolic Strikes: It’s possible the group achieves partial success – e.g., they deface a few government websites and leak some internal memos, but do not fundamentally disrupt core systems. This would still be significant as a symbolic victory and morale boost for the opposition. The impact on infrastructure would be minimal, but propaganda impact moderate. In this scenario, the group might then recalibrate to a longer-term insurgency: picking off one target after another, gradually eroding the regime’s sense of security. This could stretch out over months, aligning with the war’s timeline. The regime would endure the nuisance but perhaps avoid collapse. However, the psychological effect could still be cumulative, contributing to “death by a thousand cuts.” If war tensions ease, Akhareen Nabard might continue as an active threat group focusing on internal regime targets (like how some protest-born groups persisted even after demonstrations waned, continuing to leak files or disrupt events sporadically).
3. Preempted or Fizzling Out: Another path is that the group’s attacks are largely thwarted or underwhelming. The regime might have anticipated some of their moves (especially after publicizing the threat) and hardened key systems or trapped the hackers in a honeypot. If their first strike fails or only yields trivial results, the group’s credibility would suffer. They might then retreat into quieter mode, possibly attempting more stealthy hacks to recover – or they might dissolve if they fear identification. In this case, the direct impact on infrastructure would be negligible, though the regime may still use the attempt to justify tightening digital control (e.g., more internet censorship “for security”). The opposition would lose a potential asset, unless another more capable group picks up the slack. Given the strong wording of the manifesto, a fizzle would be embarrassing; thus the actors behind Akhareen Nabard likely have a plan to avoid a total flop. It could be that even if big hacks aren’t feasible, they’ll produce some visible action (for instance, a joint operation with another group where they claim partial credit) to save face.
4. Integration into Proxy Warfare: If the war continues, one could see Akhareen Nabard essentially integrating into a coalition of anti-Iran cyber forces. They might coordinate explicitly with Predatory Sparrow, Indra, etc., dividing targets among themselves (for example, Sparrow focuses on financial and military, Akhareen Nabard takes on government ministries and media, another handles transportation, etc.). This coalition approach could maximize damage and overwhelm Iran’s cyber defenses. In effect, Iran could face a cyber onslaught on multiple fronts. The outcome of that could be severe short-term disruptions. Iran has resilient and capable cyber engineers too, so it would be a tit-for-tat battle – possibly pushing Iran to consider extreme measures like negotiating a cyber truce or lashing out in other domains (kinetic terror, etc.). The involvement of multiple groups would blur attribution, allowing each to deny being state-sponsored while collectively functioning as a proxy cyber army serving strategic goals (e.g., Israel’s goal to cripple Iran’s nuke program and economy, the Iranian opposition’s goal to incite regime change, etc.). This scenario is essentially an intensification of proxy cyber warfare with Akhareen Nabard as a new entrant rallying others under the “last battle” banner.
Given current indicators, a medium scenario (#2) seems plausible in the near term: we will likely see at least a few noticeable disruptions or leaks claimed by Akhareen Nabard in the days ahead. Even if those don’t decisively cripple infrastructure, they will add to the cumulative pressure on Tehran. Over time, depending on the conflict’s trajectory, the group could either ramp up (if war and unrest expand) or fade (if tensions cool and security tightens). Nonetheless, the emergence of Akhareen Nabard clearly “aligns with known trends” of anti-regime digital sabotage: it is part of the continuum of increasingly audacious Iranian dissident cyber operations that parallel Iran’s external conflicts and internal crises.
Akhareen Nabard vs Similar Iran-Linked Cyber Groups
To contextualize Akhareen Nabard, we compare it with four notable groups active against Iranian interests, highlighting orientation, known operations, tactics, and affiliations:
Group Name Active Since / Peak Orientation & Stated Motives Notable Operations & Targets Tactics/Techniques Affiliation / Sponsorship
Akhareen Nabard (“The Last Battle”) 2025 (June) – present
(Emerging during Iran–Israel war) Anti–Iranian regime dissident hacktivist. Declares a “cyber war” to topple the Islamic Republic, citing years of public suffering. Aims to free Iran from regime control; ideology of revolutionary change. Presents itself as part of Iran’s opposition, fighting alongside other cyber “allies.” Planned initial multi-target cyber-attacks inside Iran (announced via manifesto). No confirmed prior ops under this name. Expected targets: regime “strategic” assets (government ministries, IRGC-related companies, critical infrastructure). Context suggests focus on wartime targets (military, finance) and regime control systems (media, internal networks). Likely hack-and-leak, defacements, and disruptive attacks (wipers or DDoS). Will employ spear-phishing and possibly leverage known exploits/credentials from past breaches. Plans simultaneous strikes on multiple networks for shock effect. High emphasis on propaganda in Persian. Uses secure comms (ProtonMail) and no open social media to maintain OPSEC. Iranian dissident network, possibly with foreign (e.g. Israeli or Western) support. Language and goals align with Iranian opposition groups (could involve MEK-affiliated hackers or protest “cyber units”). The timing amid war raises likelihood of coordination with Israel-led cyber operations (acting as a proxy front). Not state-acknowledged; claims grassroots patriotism.
Indra
~2019 – 2021
(active covertly since 2019; publicized in 2021) Anti–Islamic Republic “regime opposition” hacker group. Appeared to target Iran and its allies (name references a war deity). Claimed to fight regimes sponsoring terrorism. Essentially a sabotage-focused entity opposing Iran’s government.
Jul 2021
Cyberattack on Iran’s national railway system – disrupted trains and defaced station displays with messages telling passengers to call Khamenei’s office. Crashed rail scheduling systems, causing chaos.
2020
Attacks on multiple Syrian companies (e.g., state oil companies, private firms linked to Iran) in 2019–20. Possibly behind other Iran incidents (some overlap with later “Predatory Sparrow” claims). Destructive malware (wipers) that masqueraded as ransomware. Indra’s tools “destroyed data without means of recovery,” locking systems and replacing passwords/wallpapers. Specialized in crippling critical infrastructure: wiped corporate networks, knocked transit offline. Used coordinated intrusions (left artifacts tying Syrian and Iranian attacks together). Likely gained access via supply-chain or stolen creds. Also employed defacement for psychological impact (e.g., trolling Khamenei with the 64411 phone number display). Unclear – purportedly independent opposition, but suspected state backing. Check Point attributed Indra’s sophisticated campaign to an actor with capabilities beyond average hacktivists. Some reports explicitly noted Indra was not an official Israeli operation, suggesting it might be a non-state group, or possibly a front for another state or a contractor group. No known affiliation with Iranian exile orgs; name “Indra” and targeting of Assad-linked entities raised speculation of foreign (perhaps Israeli or Indian) sponsorship.
Lab Dookhtegan (“Sewn Lips”) 2019 (March–April)
Anti-IRGC/anti-regime hack-leak persona. Claimed to expose Iran’s “cyber lies.” Motivation: punish and impede Iran’s state hackers (perhaps in retaliation for regime espionage). The name implies silencing the regime (sewing its lips).
Mar–Apr 2019
Leaked a treasure trove of data from Iran’s APT34 (OilRig) group via Telegram. This included source code of hacking tools, lists of breached accounts/passwords, victim data from 66 organizations worldwide, and identities of APT34 operators. Essentially doxxed Iran’s elite cyber espionage team and published their tools (Web masks, backdoors, etc.). No other publicly claimed ops after 2019 dump (it went quiet after). Hack-and-leak (mass data dumping). Likely achieved deep infiltration of IRGC’s cyber infrastructure – possibly access to command-and-control servers or build servers of APT34. Method might have been insider help or a counter-hack against an Iranian spy group. Data was leaked gradually on Telegram channels in both English and Farsi, with explanatory notes. The leaks forced Iran’s hackers to abandon tools and reset operations. No destructive attacks on infrastructure – Lab Dookhtegan was purely an information exposure campaign (a form of sabotage by disclosure). Widely believed to be state-sponsored (Western or Israeli). The quality and sensitivity of the leaks strongly suggest an intelligence operation under guise of hacktivism. Observers pointed to Israel’s Mossad or US CIA as likely behind it, as a way to burn Iran’s cyber capabilities without direct attribution. The group’s anonymity and one-time burst of activity fit a false-flag hacktivist pattern. It presented itself as Iranian (posting in Persian, grievance against the regime), but there’s no evidence of ties to domestic opposition groups. More likely a proxy arm of a foreign cyber offensive aiming to neutralize Iran’s hackers.
Tapandegan (“Palpitating”, i.e., Heartbeats) 2018 – 2019 (peaked in mid-2018; some later activity) Iranian grassroots hacktivist group. Explicitly supportive of Iranian protestors’ economic and political demands. Framed its hacks as a new form of civil protest, demanding regime invest in Iran’s people rather than foreign adventures. Non-violent, civil disobedience ethos via cyber.
May 2018
Hacked flight information displays at Mashhad International Airport – showed images and messages from the Dec 2017–Jan 2018 protests, and slogans condemning regime spending in Gaza, Lebanon, Syria. Forced airport to shut boards off for hours.
Jun 2018
Repeated similar hack at Tabriz International Airport screens.
Summer 2018
Hacked Tehran Municipality’s email and social accounts; from there, sent an email to dozens of Iranian MPs urging action against corruption and economic mismanagement. Leaked whistleblower letters (e.g., revealing IRGC defied Khamenei’s orders to curb its economic empire). Exposed a secret IRGC luxury hotel purchase during economic crisis.
Aug 2021
(Attributed) Released CCTV footage of abuses in Evin prison in coordination with Edalat-e Ali, acting as a conduit to draw attention to the videos. System intrusion & defacement of displays – exploited weak security in public info systems (airport IT) to broadcast protest content. Likely used insider help or simple credentials to access these networks (airports acknowledged a cyber breach occurred). Credential compromise & account takeover – e.g., guessed or phished the Tehran Municipality email password (possibly trivial security) to then access Twitter/Instagram and email all MPs. Leak and publicize documents provided by sympathizers (“insiders and whistleblowers”) – essentially acted as a hacktivist publisher for leaked secret files on IRGC and government corruption. Maintained an online presence (Telegram/YouTube) to publish videos and statements, often in Farsi. Used media coverage (Radio Farda, VOA) to amplify messages, which focused on economic grievances and anti-IRGC sentiment. Grassroots Opposition (possibly linked to exile activists). Tapandegan presented as an indigenous movement arising from the 2017–18 protests. Its content often aligned with narratives promoted by diaspora opposition (e.g., MEK and others railing against IRGC’s regional spending and corruption). In one instance, Iranian state media even claimed to arrest some airport hackers by October 2018, implying it was a local network. Some analysts suspect Tapandegan had support or coordination with the MEK’s “rebel cells,” given the overlap in messaging and the MEK’s known cyber activities (MEK outlets amplified Tapandegan’s leaks). Nonetheless, Tapandegan was publicly independent, portraying itself as patriotic Iranians inside and outside the country using cyber protest to support the people’s movement.
Predatory Sparrow (Gonjeshke Darande)
2021 – present (active)
Anti-Iranian regime hack-and-sabotage group. Ostensibly Iranian (name in Persian), claiming to target regime institutions that harm the people. Often justifies attacks as retaliation for Iran’s malign acts (terrorism, etc.). Implied goal: make the regime feel consequences on its own soil. Frequently references corruption and misdeeds of targets in statements.
July 2021
Cyberattack on Iran’s train system (overlap with Indra case – researchers later linked this attack to Predatory Sparrow as well). It caused nationwide rail service delays and displayed hack messages, much like Indra’s operation.
Oct 2021
Massive hack on Iran’s subsidized fuel distribution network, crippling pumps at ~4,000 gas stations for days. Displayed the message “cyberattack 64411” on pump screens (64411 is the hotline of Khamenei’s office), similar tactic to the train hack. Regime accused Israel; PS later took credit on social media.
June 2022
Hacked three Iranian steel companies, including one of Iran’s largest steel plants, causing production to halt. Released video of a furnace explosion, claiming it caused physical damage due to cyber manipulation. Stated these companies were tied to the IRGC and repression.
2022
Leaked internal data from Iran’s Ministry of Housing and other agencies (on its Telegram) to expose regime corruption.
June 2025
Amid Iran-Israel war, attacked Iran’s state-owned Bank Sepah, claiming to have destroyed all of the bank’s data and backups. Brought down the bank’s services; customers reported outages.
June 2025
(Next day) Breached Nobitex (Iran’s top crypto exchange), allegedly transferring ~$49 million out, accusing Nobitex of helping Iran evade sanctions. Advanced multi-stage attacks, often causing physical or irreversible damage. Likely uses custom malware and sophisticated recon: security experts note these operations exceed normal hacktivist skills, aligning more with nation-state APT capabilities. For instance, the steel mill attack required knowledge of industrial control systems and careful timing – something a well-resourced team could do. PS focuses on critical infrastructure (trains, fuel, steel, banking) and employs wipers/sabotage malware to permanently destroy data or equipment, rather than simple defacements. They do accompany attacks with propaganda releases (via Telegram, with Farsi messages explaining rationale). OPSEC is good; they remain untracked and don’t respond to media inquiries directly. Often attacks in context of Iran’s actions (e.g., striking back during protests or war). Widely assessed as an Israel-linked proxy. Though Predatory Sparrow claims to be Iranian patriots, multiple indications point to Israeli involvement: Israeli media openly calls it “Israel-linked”, and the timing of attacks often corresponds with Israeli strategic interests (e.g., hitting steel plants amid tensions over nukes, or responding to Iranian crackdowns). The sophistication and access needed (e.g., 2021 gas station hack likely involved supply-chain compromise of a system controlling all pumps) suggest nation-state backing. Israel has not formally admitted it, providing deniability, but experts and even ex-NSA officials consider PS essentially a front for Israeli cyber operations. It may also involve some Iranian dissident contributors, but largely it operates in concert with Israel’s objectives.





You must be logged in to post a comment.