
APT34 tools full LEAK
pass:vJrqJeJo2n005FF*
https://mega.nz/file/eQ8w0CKB#WwZh_NB_IKn9ApCfrmlcvHDZN_4SJTVmuMRA7IIMVhc
https://x-junior.github.io/malware%20analysis/2022/06/24/Apt34.html
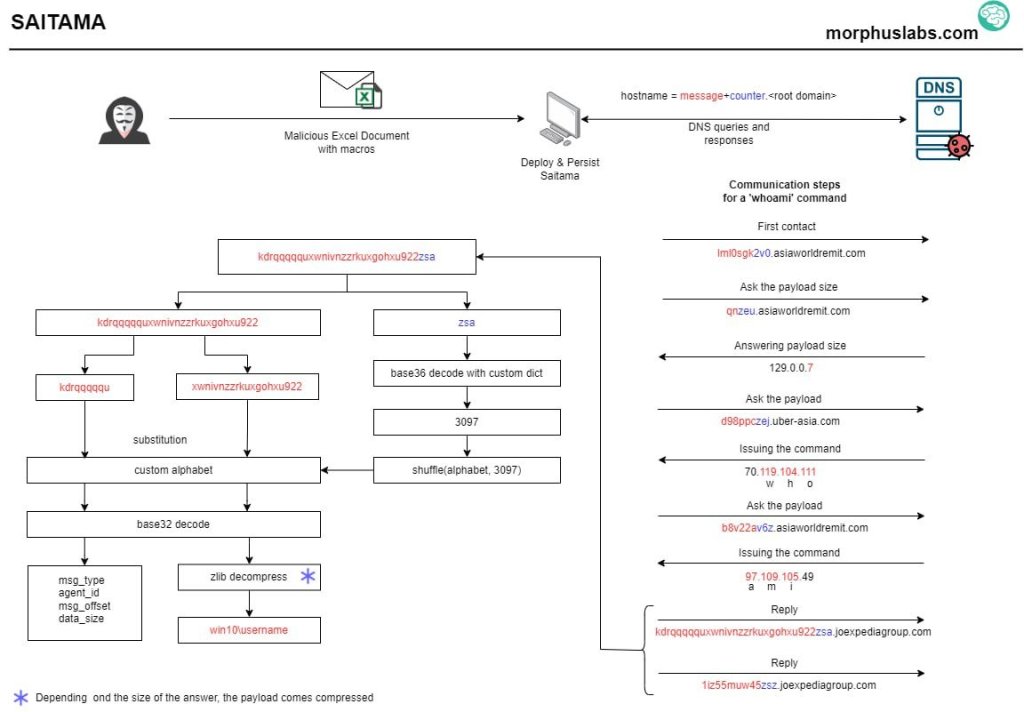
When the victim opens the XLS file and activates the Enable Content option, a malicious macro will be activated and will drop a malicious file named
update.exe
.
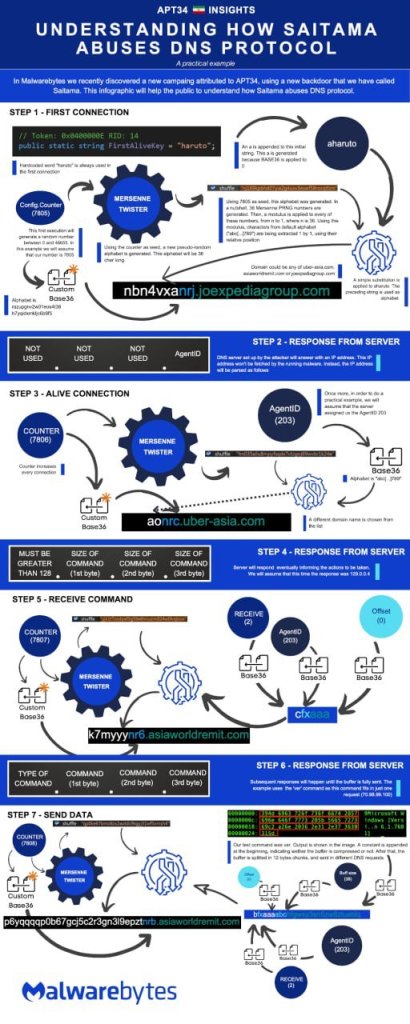
But the interesting thing about this macro is the use of a technique called Saitama , which is apparently the invention of the APT34 team itself, and is a tactic for creating DNS Tunneling and sending a DNS-based command that encodes in the FQDN part and on the subdomain.
oxn009lc7n5887k96c4zfckes6uif.rootdomain.com
When the backdoor is activated, it sends a DNS request to the FQDN and receives the IP value, this IPv4 Octet-based meaning for C2, for example the following address
70.119.104.111 - 97.109.105.49
Octet code numbers are translated into ASCII characters, for example
w=119
,
h=104
,
o=111
and
i=105
, which finally sends the word whoami from the command line (C2) to Backdoor.
# 👇
https://github.com/kbandla/APTnotes
#abdalrhman_Ali
APT-41📥📄
https://www.mediafire.com/file/cab3o77n6pobca6/APT_41.pdf/file
APT-34
https://www.mediafire.com/file/nfhk8f863l834xe/APT34.pdf/file
APT-27
https://www.mediafire.com/file/dh88tg40t21jo1c/APT_27.pdf/file
APT Notes
This is a repository for various publicly-available documents and notes related to APT, sorted by year. For malware sample hashes, see the individual reports 👇
https://github.com/kbandla/APTnotes
abdalrhman_Ali
https://github.com/RedDrip7/APT_Digital_Weapon/tree/master/APT34










You must be logged in to post a comment.