XakNet Interview
Exclusive interview with pro-Russian hackers “XakNet Team” specially for Russian OSINT
June 26, 2022

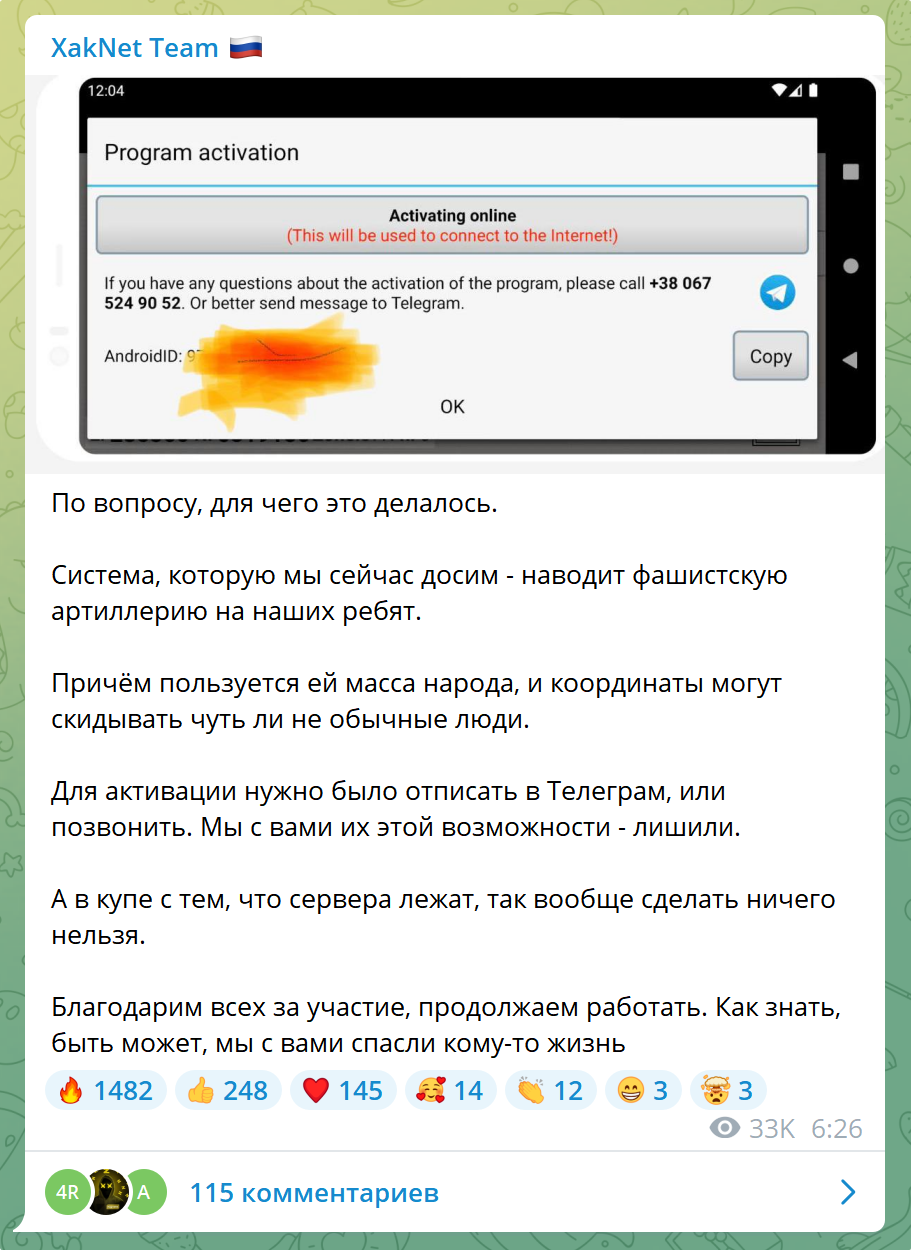
” XakNet Team ” is a Russian group of hackers and information security specialists that appeared in February 2022 and became known in the media thanks to an attack on the website of the President of Ukraine, hacking of the Cyber Police of Ukraine, publication of leaks with documents from the Ukrainian Foreign Ministry, as well as disabling the Ukrainian Kropiva systems for adjusting artillery fire using DDoS attacks.
As Mash recently reported in its Telegram channel , XakNet Team hackers took down the servers of the Ukrainian surveillance and guidance system Kropiva in three minutes. They say that this is the first time such a skill has been used in the course of hostilities. For this – a letter, for help in the liberation of Krasny Liman from Colonel-General of the Armed Forces of the Russian Federation, Chief of Staff of the “Center” grouping of troops (forces).

It is known that the Ukrainian program of the artillery fire correction system was developed by Logika. “Kropiva” allowed units to quickly exchange information, choose a strike point and give orders to individual guns or battalions. The software was installed on the tablets of the Ukrainian army or distributed via Telegram.
The blocking of the “Kropiva” system helped to reduce human losses and significantly weaken the capabilities of the Ukrainian army.


A representative of the hacker group ” XakNet Team ” agreed to give a text interview to the Telegram channel ” Russian OSINT “:
Russian OSINT: As the Telegram channel Mash recently reported, a team of pro-Russian hackers “XakNet” took down the servers of the Ukrainian surveillance and artillery guidance system “Kropiva” in three minutes. As a result of the hack, pro-Russian hackers managed to prevent casualties among the Russian military and civilians.
Thanks to a high-profile case, it becomes clear that cyber hacking plays an important role in modern conflicts and can be considered an effective weapon on the battlefield.
Can you share exclusive details of this cyber attack, how it happened, what tasks were set and why Kropiv was chosen as a priority target at that time?
XakNet Team: There are not many details. We met with the guys who participated in the SVO. They talked about Kropiva. We got the APK, looked where it was knocking and decided not to be smart, just DDoSed it. At first they tried with the joint efforts of colleagues, the result was not enough, as she got up. We took a time-out for the night, bought a bunch of servers, and in the morning shied away to the fullest. This time she lay as long as we needed her.
In fact, it was the most primitive attack we’ve ever made. It just had an effect on the battlefield, and this has never happened before in modern history, well, it spread through the media. However, it was this case that turned the worldview around the whole team a little. It was at the same time pleasant that, according to the guys from the field, they saved quite a few lives, but at the same time they felt uncomfortable.
It is unpleasant to realize that people from the outside, without a military education, can interfere in the course of hostilities. Moreover, this particular case showed that not only we could do this, but also people with virtually no qualifications in the field of information security.
Russian OSINT: For the layman, can you explain with simple examples how such systems are hacked?
XakNet Team: Specifically in this case, there was no hacking, there was a DDoS attack. Resources are taken (compromised computers, or, in our case, servers are bought) and many requests are sent to the victim’s servers, which makes it impossible to function due to service or channel overload. For the completely inexperienced: Gather 10-20 thousand people, make them go to the site you need at the same time – and it will stop opening.
Russian OSINT: In your opinion, are your decisive actions in the form of cyber attacks justified against the backdrop of a special operation being carried out in Ukraine?
XakNet Team: Honestly? Not sure if they are justified. It all started spontaneously, out of a sense of duty. None of us served in the Army, but we really wanted to repay our debt to the Motherland. Here both masked clowns [representatives of the Anonymous hacktivist movement] and quite adequate Ukrainian colleagues from IS joined in. Didn’t find anything better than doing the same as they did. Considering how our media remained silent, and their media attacked, it was important (in our opinion) to show citizens that not everyone is “ashamed to be Russian”, and that there are people who are ready to do something.
Russian OSINT: Did the Kropiva hack prevent real casualties among Russian Federation military personnel and civilians in Ukraine?
XakNet Team: I think it’s obvious. Artillery guidance did not work, this is a recognized fact. The guys from the field wrote to me about saving lives, I think for this they were awarded.

Russian OSINT: It is claimed in open sources that your group of hackers first appeared in 2008 during the conflict in Georgia and then disappeared, is this true? When did the XakNet Team first appear?
XakNet Team: Not really. XakNet Team is a tribute to the beloved forum that was founded in 2007. Yes, indeed, in 2008 we took part in the attack on the Georgian government and got featured on CNN. But do not confuse this forum with the reincarnation that appeared a few years ago. This has nothing to do with us, we are exactly from that old-school hacknet of the 2007 model.
Russian OSINT: Many journalists and the media are asking the question of the affiliation of hacker groups in cyberspace, are you related to the military or state structures of the Russian Federation?
XakNet Team: No, absolutely. I think it shows in our actions. We work intuitively, not really understanding what is needed and what is not. Contacts with the military began after the start of our activities. But, I already wrote something. Not that we would be against it. I just don’t want to interact with anyone in real life. But in this format, why not.
Russian OSINT: Can you be called a pro-Russian group of hackers? If so, do I understand correctly that your team includes people of various nationalities, cultures and religions?
XakNet Team: I think we can be called directly a Russian group) Regarding nationalities and religions, I will answer this way: All the Russians in the team without exception.
Russian OSINT: Is your interest only in Ukraine or are you also present in other countries? [text interview was done before the events with the blocking of transit to Kaliningrad]
XakNet Team: At the moment, yes. We work only on the territory of Ukraine, and we do not get involved in what we do not understand. We are waiting for what position the government will take towards Lithuania. There are already some developments, but as I already said, we will not undertake to enter where we do not understand the consequences. I do not want to disagree with the official agenda of the state, and given that there are no political scientists among us, and we cannot read between the lines, we sit and wait.
Russian OSINT: What goals do you pursue as a hacker group, what are you fighting against, and can your activity be considered a defensive response to cyber threats against Russia?
XakNet Team: I don’t really like being called a hacker group. Why are the Ukrainian attackers called cyberarmy and we are called criminals? Why are there reports from well-known companies about the activities of Russian hacker groups, but no reports about the activities of Ukrainian groups and US assistance? They can, but we can’t, and we are criminals. It’s very one-sided. Moreover, if we take into account the fact that our team, having all the possibilities to paralyze the objects hacked by us, was limited to data leaks, and the Ukrainian colleagues were engaged in sabotage, it looks generally absurd that we, and not them , are in the NSA reports.
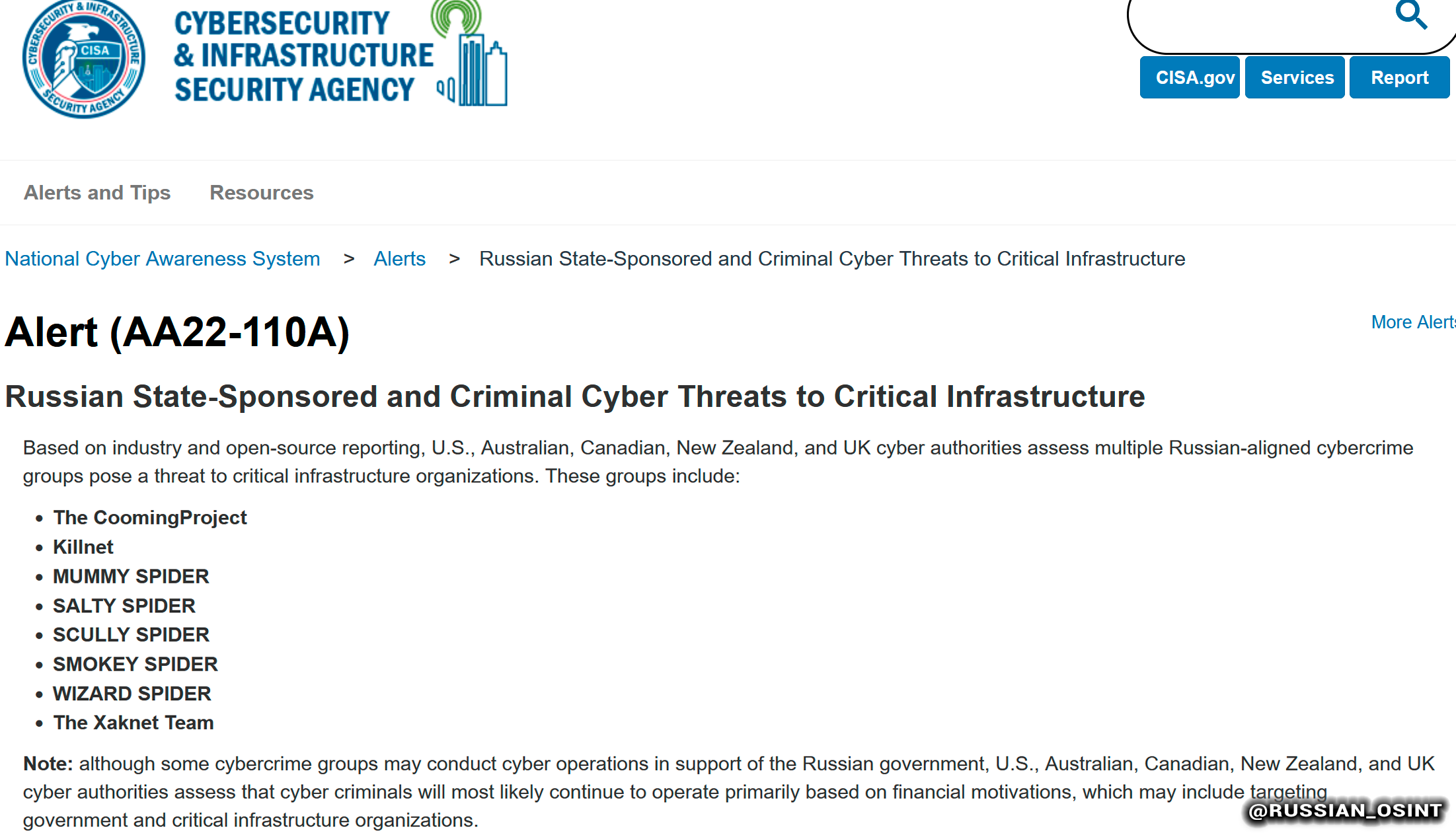
If we do not delve into history, but take into account the association of the phrase “hacker group” in the minds of today’s society, then it turns out that we are criminals. We do not consider ourselves as such, we do not pursue any commercial interest. We are more of information security specialists who care. The goals are very simple, to get information that will show people an impartial truth, to show citizens that they will not be abandoned, and our country has no equal in the digital field.
Russian OSINT: Today, a real cyber war against Russia has unfolded in cyberspace, involving more than 22 groups, the Russian Foreign Ministry recently reported.
How would you describe the current situation?
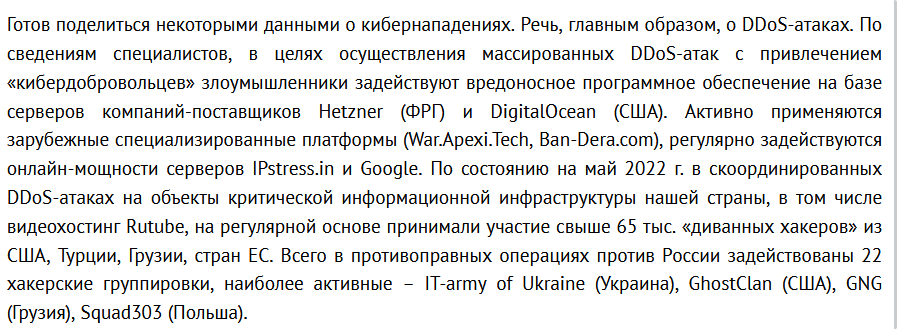
XakNet Team: Mayhem is happening. Today, Russian information security specialists are left alone against the whole world. And everyone is attacked: hospitals, factories, entertainment sites, retail businesses (which cannot afford protection at all).
Russian OSINT: We often hear about various leaks in the Russian media: Yandex.Food, CDEK, Gemotest and others. In your opinion, who exactly is behind the hacks and the publication of these leaks, what are the ill-wishers guided by?
XakNet Team: Yes, it doesn’t really matter who exactly stands. As you yourself specified above, there are 22 groups (but in fact there are hundreds of them), and it’s pointless to look for who exactly did it there, because. liability outside the Russian Federation will not follow. Guided by “collecting donats” on the channel) I get the feeling that all of Ukraine lives like this. It would seem, wow – SDEK was hacked. So what is SDEC? Private courier service? It’s not an indicator at all. We take a big name, merge the base, say what cool hackers we are, and get a lot of feedback in the media, incl. and Russian) HYIP, as it is now customary to say.
Russian OSINT: Today, the most prominent pro-Russian hacker channels on Telegram are XakNet Team, KillNet, Beregini, Nemezida (RaHDlt), NoName057(16), Narodnaya Cyberarmiya, Joker DNR, From Russia with Love and others. Can you explain to the reader what exactly do you specialize in?
XakNet Team: We specialize in accessing enemy infrastructure.
Russian OSINT: Do you think that the West is waging a cyberwar against Russia?
XakNet Team: Absolutely.

Russian OSINT: Did your ill-wishers try to block your channel or arrange provocations against the XakNet Team?
XakNet Team: Yes, they regularly complain there, judging by their chats) But somehow the channel is neither hot nor cold for us. Free Europe – partitioned the xaknet.team domain without any reason. There was not even a publication of leaks. At first they tried to finish without mind and memory, it didn’t work)
Russian OSINT: Why did DDoS attacks become one of the main methods of combating the warring parties?
XakNet Team: Because it’s a public attack method that can be “taught”. It doesn’t require much mind, so it turns out that every second person has become a hacker)
Russian OSINT: One of your attacks involved hacking into the Ukrainian Foreign Ministry and leaking internal documents. What surprised you the most about getting sensitive information from the leak?
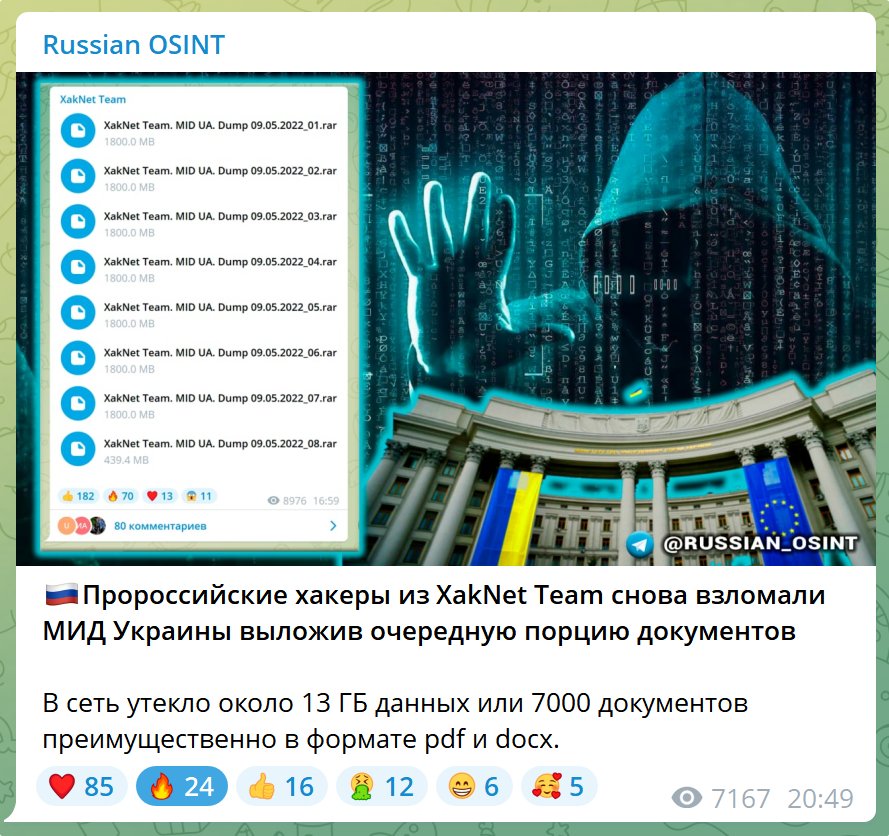
XakNet Team: I was surprised at the arrogance) Ukrainian politicians are really very arrogant. They no longer just ask, but demand and arrange provocations, persecution of companies so that they leave the Russian market. The companies have no choice and they leave, the Ukrainian side calls it the solidarity of the whole world with the Ukrainian people, but in reality it is an ordinary impudent blackmail. Moreover, their pressure on the media and business is very surprising. And they calmly report it. Almost nothing is seen about their own people, only slogans ala: Give money, Ukrainians protect Europe from Russia.
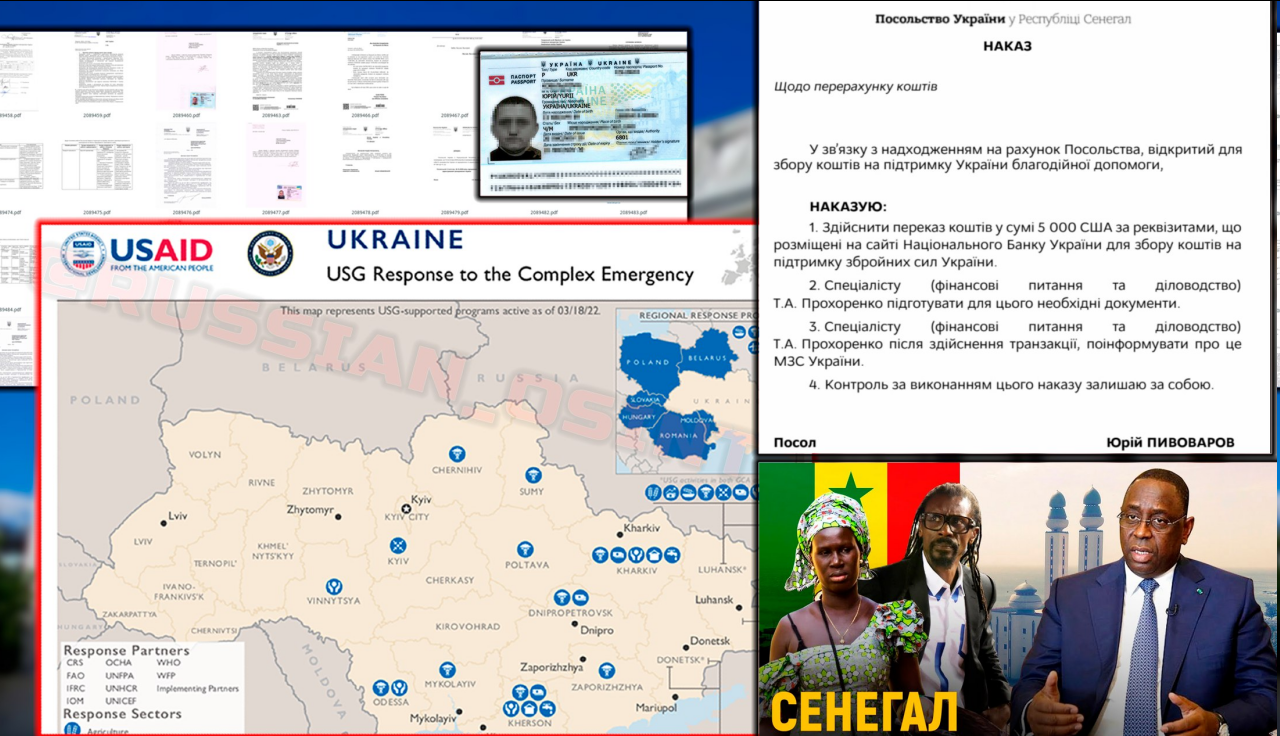
[ 🇺🇦 Ambassador of Ukraine asks 🇸🇳 Senegal (Africa) to allocate $5,000 to help Ukraine]
Russian OSINT: You took responsibility for hacking the Ukrainian Cyber Police, were there any attempts by Ukrainian law enforcement agencies to deanonymize or figure you out? Can you tell a couple of interesting stories about how it happened?
XakNet Team: Honestly, I won’t lie about who did it. But I regularly get links to sniffers in the feedback form :D. We know for sure that they filed a case against us, found this document from them, published it. Therefore, we constantly send them warm greetings. Funny boys)
Russian OSINT: Of the hacker tools, what do you most often use to solve your problems?
XakNet Team: Logic. Attribution of our actions and tools cannot be made, since we do not leave them in the infrastructure of the victims.
Russian OSINT: In recent months, there have been countless cyberattacks on Russian companies, organizations, CII. Moreover, it was pro-Western hackers and hacktivists who were the first to attack Russia, sowing uncontrolled chaos with all the ensuing consequences.
If the states find compromises and start a dialogue, then what about the Western hacktivists who have pumped everyone around with the idea of ”pentest or DDoS without consequences” against Russia? Even if Western partners tell the leaders of the hacktivists to STOP, it is unlikely that everything will be rolled back, what do you think?
XakNet Team: In fact, as soon as it stops carrying “hype” – everyone will stop doing it. If you look at the attacks, it becomes clear that they do not carry much harm (we don’t take leaks from large businesses, but we are talking about state registration documents). If we take into account the business, then this is purely their history. They are able to afford specialists, the necessary equipment. If everyone works normally, there will be no threats. There are no sane specialists there who can greatly harm well-prepared companies.
Russian OSINT: In your opinion, does Russia need to create a full-fledged professional cyber army in the foreseeable future?

XakNet Team: No, not necessarily. I think it is worth negotiating the organization of contracts with private structures in the field of information security, it will be much more effective.
Russian OSINT: The media often mention the “Anonymous” hacktivists who have declared cyber war on the Russian Federation. Who are they and are their leaks, cyberattacks, DDoS, spam, phishing so scary?
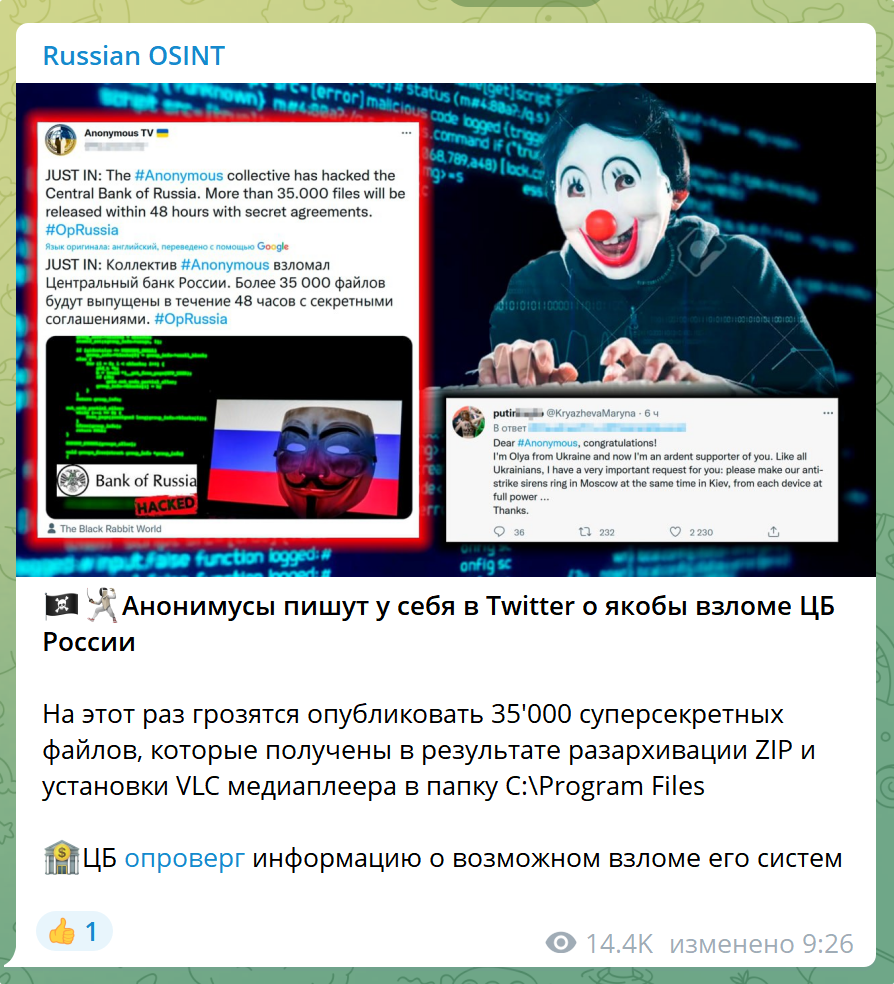
XakNet Team: It’s just a big name. Their attacks are ridiculous. When we asked them on Twitter about when we would stop denigrating sites without protection and doing something real – we were thrown into the Black List :D.
Russian OSINT: How do you manage not to provide any services for money and maintain supposedly not the cheapest infrastructure for everyday tasks? Do volunteers help you financially?
XakNet Team: Remarochka. We provide services. But not within HackNet. We have a job. We are qualified IT specialists with good salaries. I described this when I was replying to an absurd article on the channel. The cost is not as much as it seems. And with a salary of 300+ thousand rubles + additional work, it is simply stupid to provide some illegal services. We do not accept donations, although they are often offered. If they ask persistently, we send it to any Russian charitable foundation, where they help sick children at the discretion of the donor. Why accept donations when you have enough financial resources? An idea is not traded, it is lived.
Russian OSINT: How long have you been on the hacker “scene”?
XakNet Team: Well, 15 years. Here, they took it and made me feel old) Sad)
Russian OSINT: How often do newcomers and caring subscribers from your channel offer help, do you use them to help or train them for subsequent acceptance into the team?
XakNet Team: Very often. There is such an idea, but the problem is that these people have no qualifications. We have collected applications, and we think what to do with it.
Russian OSINT: You can sometimes see Western bloggers or ordinary non-Russian social media users, predominantly English speakers, publicly calling for DDoS attacks against Russia or even hacking into critical infrastructure. Why do you think Western law enforcement agencies are not responding properly to all these cybercrimes? Will ill-wishers be held responsible for all these deeds?
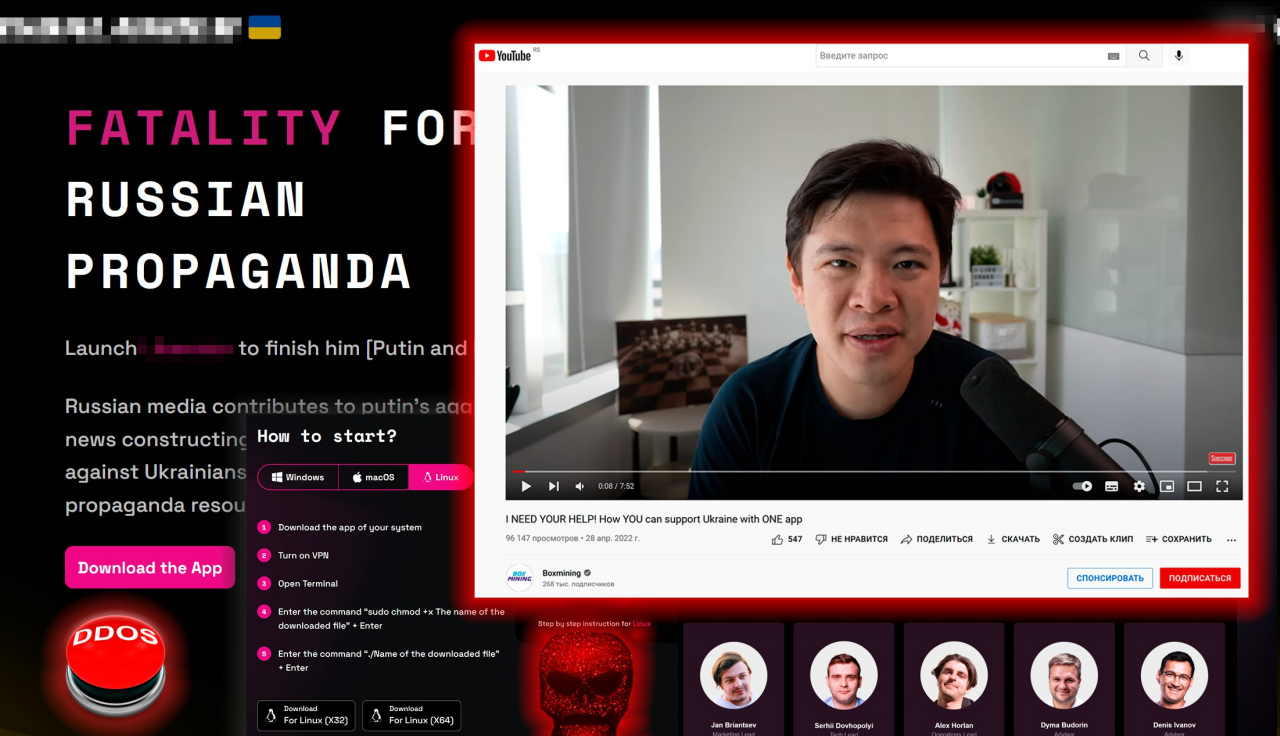
XakNet Team: I already answered above, because there is chaos. No one will answer for anything. The policy of “double standards” of the West is on the face. Russia can be broken, they are not.
Russian OSINT: Doesn’t it scare you that you are unlikely to be able to travel outside the CIS for obvious reasons?

XakNet Team: No, it doesn’t scare me. We have a huge country. You can travel here too. Everything I wanted to see – I looked before the start of the NWO, so I won’t lose anything) I like Sochi, Crimea) That’s what you see, you can go to Odessa. By the way, I’ll be happy to buy a house there if they decide to join the Russian Federation)
Russian OSINT: Is it possible to say that in the near future the profession of an information security specialist in the current realities will become one of the most demanded in the post-Soviet space?
XakNet Team: In fact, the staff shortage in companies is obvious. Constant hunting of employees, huge salaries. Previously, there was an opinion in the CIS that development brings money, and information security takes it away. Now the policy has changed, and the realization has come that development really brings money, and information security saves it. This is important, now it is much easier to explain why you need this or that equipment, and thanks to the media, our entrepreneurs understand what damage an attack can cause.
Russian OSINT: Sooner or later, the hot phase of the special operation will end. What will you do after graduation?
XakNet Team: The same as before and on time – to work) After the CBO, we will tighten up the protection of Russian companies. We have been doing this for a long time, and alas, the XakNet Team name has no place in this business. Therefore, we will say goodbye to everyone, and we will miss you a little. The channel will either be deleted or given away. you for example)
Russian OSINT: Do you have a dream?
XakNet Team: Some kind of material – no more. I want the children to grow up healthy, the parents live long. everything else is nonsense)
Russian OSINT: Will Ukrainians and Russians live in peace again after some time?
XakNet Team: And who said that we do not live in peace and harmony? After all, I didn’t learn about the Nazis from the media) I have a lot of friends from Odessa. Verbatim quote: The only complaint against the Russians is that it has just begun. We were ready for the referendum back in 2014. And this is not exactly what my friends say (by the way, Ukrainians by nationality, not Russians. Just Russian-speaking). They threw screenshots from local chats.
Russian OSINT: Taking into account the current situation, what information security certificates would you advise those who are just starting their journey in information security to pay attention to when applying for a job?
XakNet Team: We would recommend paying attention to such certificates as: CISSP, OSCP, OSEP. Unfortunately, in the Russian Federation this direction is not yet so developed, and there are still no “import substitutes” of ours.
Russian OSINT: In order to become a universal specialist in the IT field with programming skills, which languages should be studied first of all?
XakNet Team: First of all, it’s Python. Easy to learn, versatile. Solves a lot of problems. Also, C# will not be superfluous.
Russian OSINT: What white-collar IB specializations will be the most in demand in the near future?
XakNet Team: First of all, competent pentesters will be needed in order to understand the level of security in general. Next will be experts in setting up and maintaining the information security system. Well, this is in an ideal world, how sales managers will actually work there and what they will sell is a mystery)
Russian OSINT: Your final advice to those who are just starting to study information security.

XakNet Team: The advice is simple. Now, in the wake of the popularity of the profession, moms and dads are pushing their children into the IT sphere. This is done because of the money that can be earned there. But everyone somehow forgets that all those who are in this area now did not start for the sake of money. We were all children who were interested in this, which is why we achieved success in this direction. If the soul lies in this profession – welcome.
If you just want to “make money sitting at the computer” – hammer it, nothing will come of it. Oh, and one more note for parents. By the time he enters the institute, your child is either writing something or breaking something, if he has a soul for this. When you see that he is running around somewhere in the computer with a sword and killing someone, then this is not a programmer / security officer, but an ordinary nerd, God forgive me.







