This time on the Compression algorithm version 3.1.1, a vulnerability has been updated which is of the Integer Overflow type. This vulnerability can be exploited on the 1903 and 1909 versions of Windows 10 and acts as unauthenticated.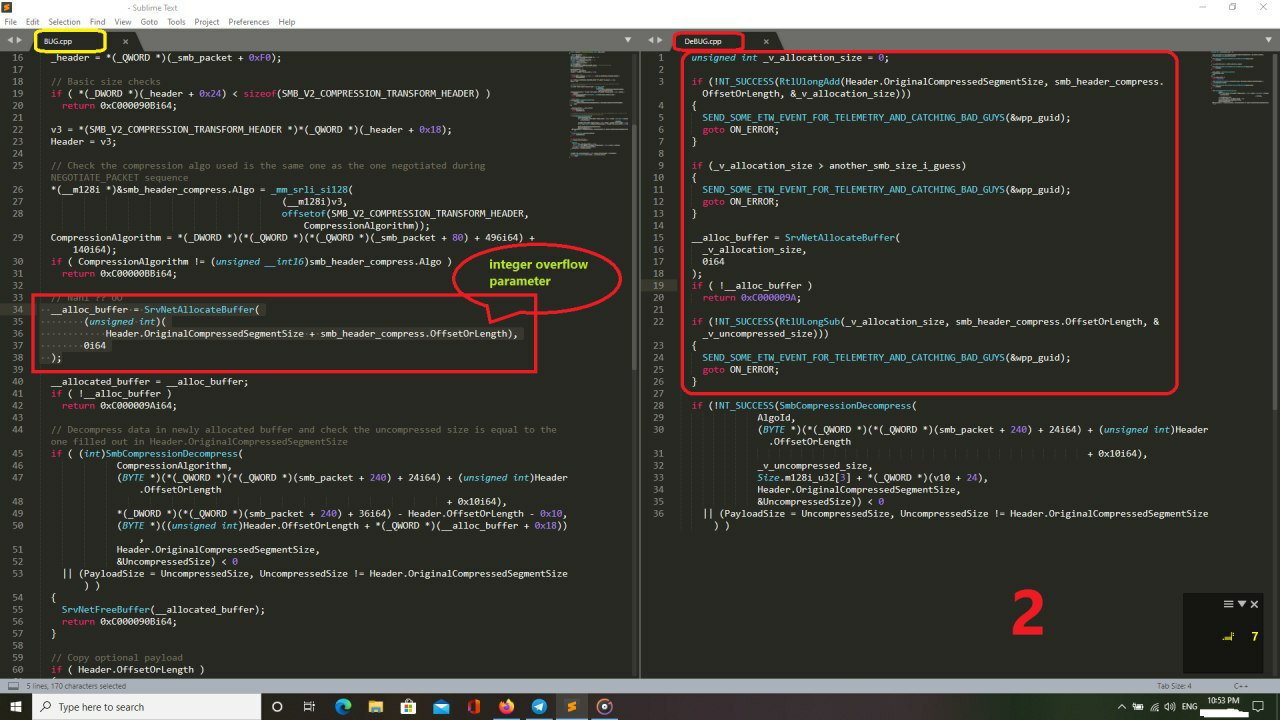


This time on the Compression algorithm version 3.1.1, a vulnerability has been updated which is of the Integer Overflow type. This vulnerability can be exploited on the 1903 and 1909 versions of Windows 10 and acts as unauthenticated.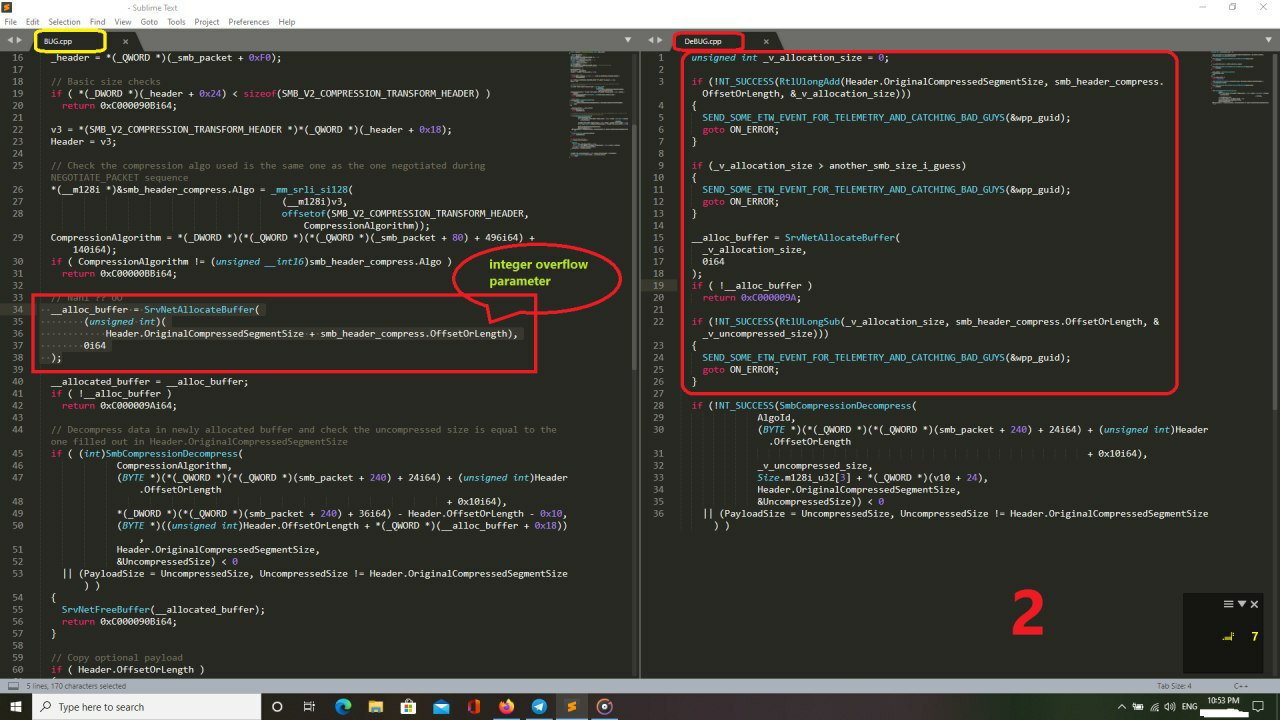
Subscribe now to keep reading and get access to the full archive.
