One day Parchin, one day Natanz, one day Zargan, one day Shiraz, and tonight Garmadreh and the west of Tehran…
One day after the explosion at the new generation of centrifuge assembly plants at the Natanz nuclear site in Isfahan province and a week after the explosion of the Khojir military barracks in northeastern Tehran, the Telegram channel “Pasdaran Cyber Corps” published a photo of a map of Palestine and Israel by a guard. The terrorist targeted it and subtitled it with verses one to seven of Surah Isra, implicitly threatening to take revenge on Israel.
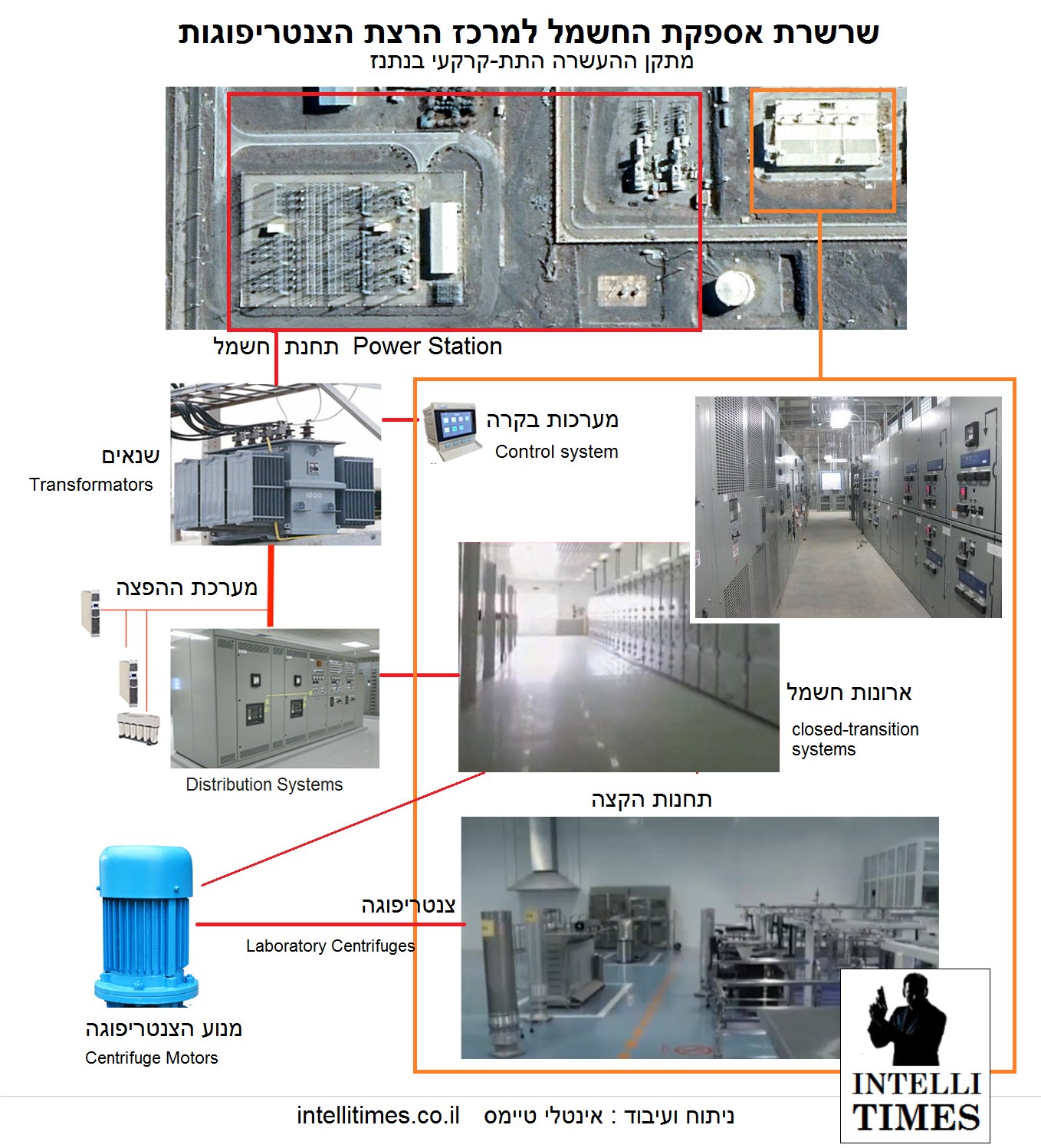
Mapping the energy infrastructure of the Natanz Centrifuge Development Center can support a cyber-trigger, even if a certain party managed to implant equipment with sabotage components. #natanz
Israel’s attack on Natanz destroyed 80 percent of the Islamic Republic’s UF6 gas reservoirs
This gas is used to enrich uranium.
Note: The hand is supposed to be Soleimani’s (symbolic) and, looks like Iran accepts this map as ALL Israel.
In both the facilities, there is the same Power Station that responsible for producing the power of the facilities. Regulating electricity is carried out through automation and industrial controllers That can be manipulated by cyber attack.
26th June – Gas Tanker Explosion at Khojar Missile Complex 30th June – Gas Explosion at medical center in Tehran 2nd July – Explosion at Natanz Nuclear Plant, Centrifuge Assembly Hall 4th July – Explosion at Zargan Plant 4th July – Chlorine leak in Karoun Petrochemical complex.
Three Iranian regime officials have told Reuters on condition of anonymity that the blast at the Natanz nuclear facility was a cyber attack.According to Reuters, one of the men said the attacks had taken place in the past.
Israel bombed and destroyed Iran’s largest uranium enrichment plant. Iran has called on Russian experts to deal with radioactive contamination.
The Israeli Times quoted Kuwait’s Al-Jarida as saying that the site of the Israeli nuclear attack was the site of the explosion, and that the missile site was blown up by missiles fired from Israeli F-35 radar escape fighters.
NASA maps of the Natanz site fire with satellite images of Natanz nuclear facilities contains two important points:First the accident happened in a place where the centrifuges are located. And that a large part of the site has been destroyed.Second, NASA fire maps show that the time of the accident was yesterday
Two of them also said that the attack was carried out by Israel.Following the explosion of Natanz nuclear site two days ago in the morning, despite the announcement of the Atomic Energy Organization of the Islamic Republic that no radioactive material has leaked, there is evidence that there is radioactive in the area.The technology of Natanz nuclear facilities is very old and it is not possible to detect radioactive materials, and because ECA_DT detection devices are made in China, their error rate in this system is very high. (Saturday, July 5) They leave for Natanz to take a closer look.
1) The image released from the Natanz nuclear facility is consistent with the data. What was not said was that there was a definite “explosion” before or after the fire.
2) The main damage is behind this building
3) The upper part of the entrance A using edited Photoshop (black spot)
4) Eliminates the intensity of the explosion of the entrance doors B.
5) The intensity of the explosion was such that the objects were thrown around
6) With a 180-degree wheel, satellite imagery is likely to determine the angle at which the camera is positioned.
7) A strip is drawn around the structure to reinforce it. Unusual machines or equipment are stored inside which entry is prohibited.
Renowned Israeli security and intelligence analyst Ronen Bergmann on page 4 of today’s issue of Israel’s Yedioth Ahronoth newspaper described the various aspects of the explosion at the nuclear facility on Thursday morning in a note entitled “Explosion in the heart of Iran’s nuclear facilities” Natanz has paid.
Bergman hinted at the coincidence of the anniversary of the Olympic Games (the Stuxnet virus ‘cyber-attack on Iran’s nuclear facilities in July 2010), citing Western intelligence sources’ report of a sabotage operation at the Natanz nuclear facility. Has unveiled.The final part of Bergman’s memo is devoted to explaining the issues raised in a statement by a group calling itself “Homeland Cheetahs.”
At 02:56 on Thursday, July 3, Tehran time, an e-mail was received by a group of journalists claiming to have carried out an “operation” on the Natanz nuclear site. Hours later, the Atomic Energy Organization of Iran announced an “accident” at the Natanz Enrichment Facility.
یوزپلنگان وطن
It seems that the emails were different and some of them even received a video attached to the e-mail. The first three images above are screenshots of that videoThe image used as the logo is the image of a leopard, not a cheetah, and is most likely purchased from video service sites and then flagged. Sample original logo here as an example
The satellite image, at least in this part of the message, was not taken from Google Maps, but from Google Earth Pro. The image belongs to 12.062020.
Another important point is that despite the fact that in the Persian language, the language of this nuclear center is known as “Natanz”, but in many foreign sources, this center is introduced as the center of “Kashan”. Example: books.google
Picture of new satellites from the explosion site of tanks in #Khojir #Iran https://t.co/FeN0WMN7QR
One of the sheds under construction in the open area of Natanz site was damaged this Thursday morning following an incident that is being investigated #natanz #nuclear #iran https://t.co/86G6qqYd2k
At around 02:06 on Thursday morning, an explosion or fire broke out at two points northwest of the #Natanz nuclear site, according to NASA satellite data.
Israeli nuclear facilities could become targeted in sabotage: Iranian analysis
A website close to Iran’s Supreme National Security Council says giving credit to an attempt to undermine the country’s nuclear capabilities could have wider international ramifications, including the possibility for an attack on nuclear facilities operated by the Israeli regime.
A Saturday article by Nour News said media reports crediting Israel for an alleged cyber attack targeting Iran’s Natanz nuclear facility mean that the regime itself would be posed to similar threats.
The former Israeli defense minister has implicitly said that the “Middle East intelligence source” whom the New York Times referred to twice in recent days as the perpetrator of the explosion at the Natanz nuclear site in Iran is Israel’s top intelligence official.
According to the Times of Israel, Avigdor Lieberman is apparently referring to Yossi Cohen, Mossad chief, the Israeli spy agency.
In an interview with his country’s army radio on Monday, July 16, without naming Youssef Cohen, Mr Lieberman said all Israeli intelligence officials were well aware of who the latest intelligence source was and that only Benjamin Netanyahu could “shut his mouth”.
The New York Times first wrote on July 4, a day after the incident at the Natanz nuclear site, quoting an “Middle East intelligence source” without naming him, that Israel was behind the scenes.
But hours after Israeli Defense Minister Benny Gantz told state radio on July 15 that all events on Iran’s nuclear sites were “not necessarily related to Israel,” the New York Times reported on Sunday evening. An “intelligence source in the Middle East” blamed Israel for the blast.
In a July 15 report, the New York Times quoted an intelligence source as a “senior” man who said the bomber struck shortly after noon.
The New York Times quoted an IRGC commander as saying, without naming him, that a powerful bomb blast had caused severe damage to Natanz’s facilities, and that Iran had ruled out a cyber-explosion.
According to the newspaper, the powerful bomb exploded at the new generation centrifuge production center on the Natanz nuclear site, with the aim of delaying the process of accelerating Iran’s uranium enrichment program.
…
The hypothesis of a missile attack on Natanz
The first relatively good satellite images of the remains of a centrifuge assembly building in Natanz have been released. Evidence suggests the most likely option is an “air strike.”
The level of destruction of class B (destruction and cracking of 50% to 70% of brick walls to non-repairable level) in the new image has a radius of about 20 meters (yellow circle). This level of destruction, according to Gilbert’s criteria, requires more than 200 to about 300 kilograms of TNT explosives.
In addition, other evidence, such as the scattering of building debris in the east-west direction to distances of more than 50 meters (pale yellow lines), strongly reinforces the assumption of an explosion caused by a foreign projectile hitting the same public side of the east.
The assumption of two collisions (one outside and one inside) is more consistent with the pattern of destruction and debris.
What that projectile was (probably a kind of cruise missile) should be clear to the Iranian authorities at this time.
Many believe that Israel and the United States are targeting the attack. Bringing Iran into the war is primarily aimed at extending the arms embargo, which is set to release Iran’s access to international weapons soon.
#Karaj, #Shahriyar and Garmadreh and #Shahr-e-Quds.
The blockage of the Tehran-Karaj highway, power outages, internet disruptions


































You must be logged in to post a comment.