Features:
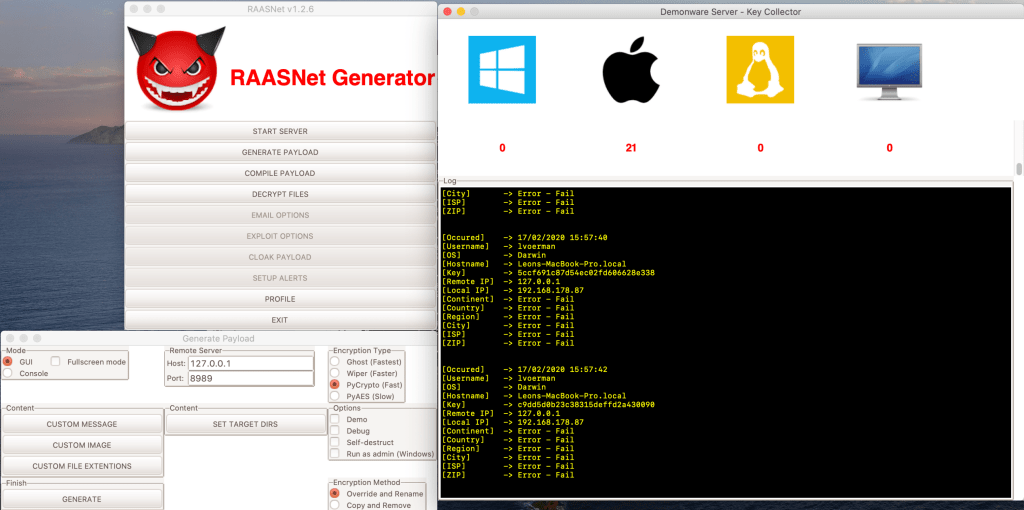


- Generate a ransomware payload
- With or without GUI payload
- FUD (Fully Undetectable by Anti-Virus)
- Works on Windows, MacOS and Linux
- Super fast encryption with PyCrypto
- Compile to EXE, APP or Unix/Linux executable
- Custom icon for your EXE payload
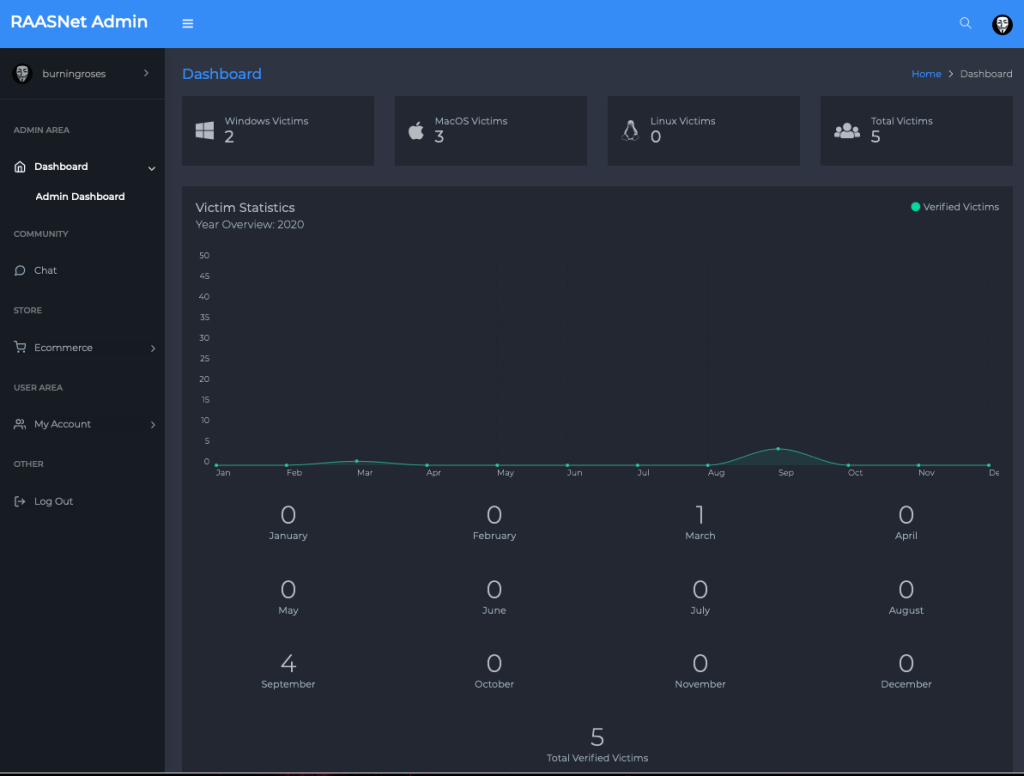
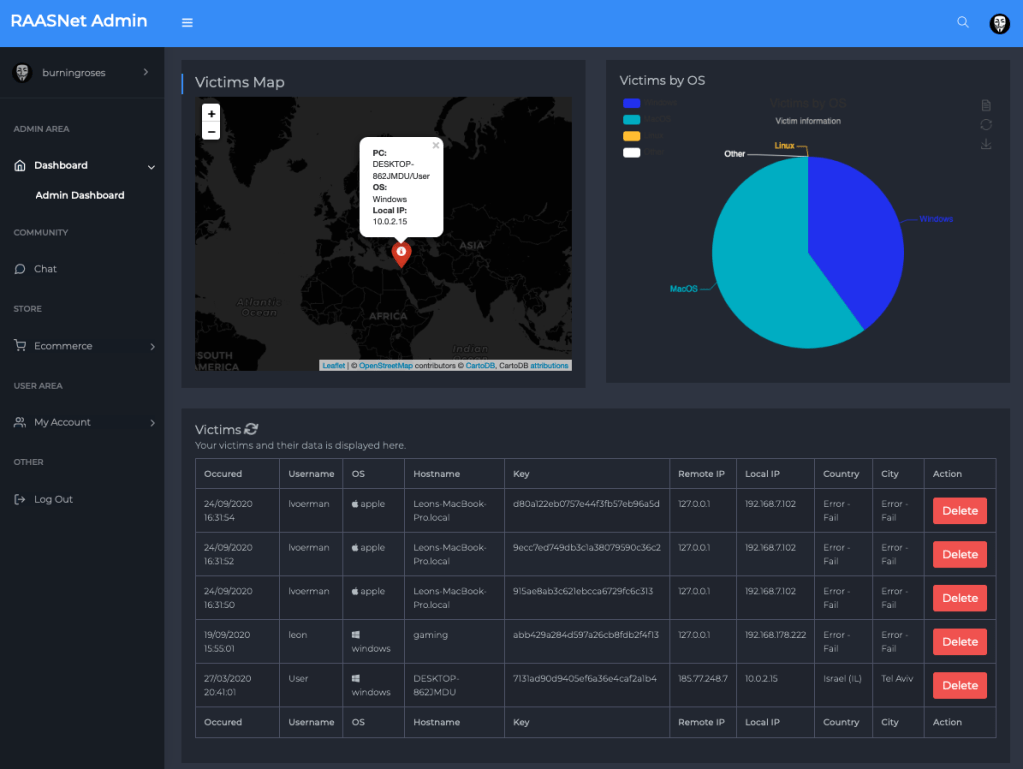
- Receive keys of victims
- Decrypt files
- Demo mode (payload won’t encrypt anything)
- Fullscreen mode (Warning takes over the screen)
- Custom warning message for your victim
- Custom image in your payload
- Ghost mode (Rename by adding .DEMON extention instead of encrypting the files)
- Multiple encryption methods
- Select file extentions to target
- Decide if payload should self-destruct (Console mode feature only)
- Decide wich drive to target for encryption (working directory)
- Verified server access through port forwarding VPN
- Encode payload as Morse code








You must be logged in to post a comment.