Analysis of the attack on the fuel station system

So far, there have been many requests to talk about the attack on the fuel station system. As you know, the cyber attack on the country’s fuel system has caused the entire system to fail. Well, we have nothing to do with the political issues here. We do not want to talk about the technical aspects of this issue, the first issue is that industrial control systems are one of the most important systems in a country so that if a person or persons have access to these systems, impossible things can happen. Compensate, for example, consider a dam that is controlled by an industrial control system. A hacker can do anything if he can access this system. One of the least he can do is open a dam in front of the water. And it causes a lot of financial and human losses and thousands of other problems. I said that you should know that the security of industrial control systems is not a joke and should be taken seriously.
Well, let’s skip these issues and get to the point, the internet connection has made it easier for us to manage many devices and systems, for example, we sit at home and we can easily remotely control our devices and face Let’s see the information live. The problem is that many industrial control devices are not ready to connect to the Internet and connect to the Internet without proper authentication or other mechanisms, which is just the beginning of a great catastrophe.
In the following, we will first get acquainted with the structure of a fuel station. Pay attention to the image below
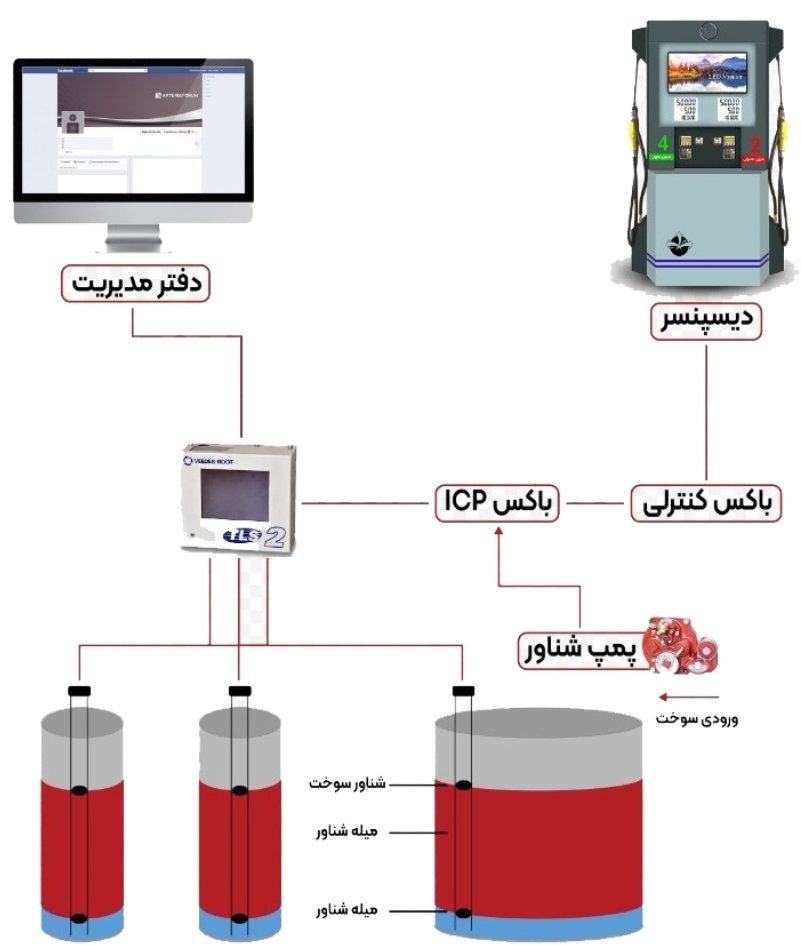
The picture above clearly shows everything, the management of fuel tanks in gas stations is a very important issue, there are many companies that produce these systems, one of the companies that is very popular is Veeder Root, which is used in Iran. There are many, unfortunately, Veeder Root devices are very weak in terms of security and it is not difficult for a hacker to penetrate them, there are many protocols in industrial control systems such as modbus, s7comm which are vulnerable and a hacker can Easily scan and infiltrate these devices with tools like PlcScan, I told you above that these devices are not suitable for connecting to the Internet, and unfortunately they connect the devices to the Internet and a hacker can rasily identify its targets using Shodan and infiltrate with the items I introduced, take a closer look at industrial control systems. These devices are not used without proper security mechanisms, and if someone has worked in the discussion of penetration testing of industrial control systems, he will realize this catastrophe.







You must be logged in to post a comment.