The Islamic Republic of Iran faced a coalition consisting of the United States and Israel from late 2025 through spring 2026. Military forces exchanged massive kinetic strikes. State-sponsored hackers executed parallel intrusions into civilian and government networks. Conventional defense strategies failed. Hackers bypassed core databases. Attackers easily compromised public-facing websites and socioeconomic messaging applications. The conflict almost certainly redefines modern operational security. State secrecy faces overwhelming challenges from crowdsourced intelligence. Future engagements will highly likely see an expansion of attacks on unprotected peripheral systems.
Introduction
Bombs fell, and servers crashed. The period between late 2025 and spring 2026 exposed a new paradigm in conflict. Forces from the Islamic Republic of Iran fought an intense battle against an alliance led by the United States and Israel. Physical combat heavily degraded Iranian military capabilities. Israeli strikes killed Supreme Leader Ayatollah Ali Khamenei. Opposing militaries launched ballistic missiles across the region. A parallel silent war exposed profound flaws in information security. Traditional databases failed to protect state secrets. Operatives successfully extracted highly granular intelligence from public domains. United States (US) Central Intelligence Agency operatives publicly recruited informants. Iranian hackers targeted Western corporate networks. Hackers exploited everyday socioeconomic grievances to breach secure systems. The following sections analyze intelligence leaks, infrastructure breaches, and psychological operations.

Exploiting Peripheral Infrastructure
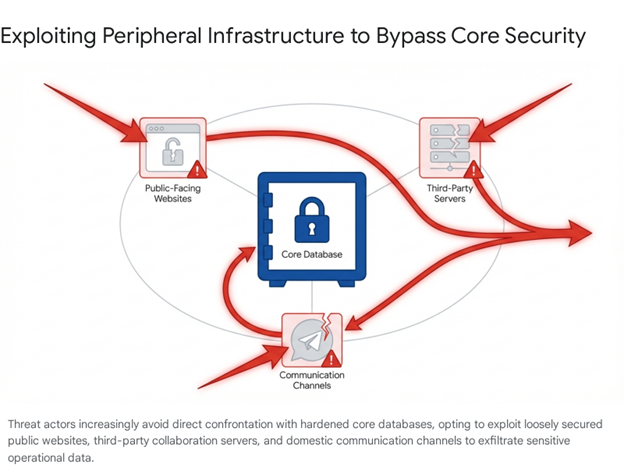
Security planners have historically assumed that core databases remain safe. Professionals believe encryption and physical isolation protect sensitive information. The 2025 to 2026 conflict proved the assumption false. Cryptographic strength matters little when hackers compromise public-facing portals. Attackers target the human element. Connected administrative networks and unclassified logistical channels present enormous attack surfaces.
Avoiding the Core
Adversaries almost certainly avoid direct assaults on hardened central repositories. Such attempts require massive resources. Defenders easily detect brute-force attacks. Hackers prefer secondary systems. Unclassified platforms offer hidden pathways to sensitive data. Operations during the 2020 US elections demonstrate the tactic. Iranian hackers infiltrated municipal systems. The actors altered unclassified election result pages. Core voting databases remained untouched. Falsifying public numbers inflicts severe psychological damage. The tactic effectively undermines confidence without breaking secure firewalls.
European Space Agency networks suffered a highly publicized breach in late 2025. Attackers targeted external servers tied to collaborative scientific projects. The intruders bypassed the heavily fortified primary corporate network. Attackers successfully extracted project files and technical schemas. Hostile actors do not need to penetrate military headquarters. Hacking unclassified logistical contractors yields excellent intelligence.
Crowdsourcing Intelligence
State secrets suffer from terrible operational security. Mapping military locations does not require sophisticated hacking. Independent researchers and civilian resistance movements rely on public websites. Analysts observe commercial high-resolution satellite imagery. Intelligence agencies monitor localized social media chatter. Analysts dynamically reconstruct troop deployments from unclassified logistical records.
Unprecedented volumes of information about Iranian military logistics were posted on public platforms in March 2026. The data did not come from a single database breach. The intelligence emerged from aggregated public data points. Military forces generate massive electronic exhaust. State actors occupy physical spaces and procure local supplies. Public mapping tools systematically capture the exhaust. The environment surrounding the enemy remains transparent.
Public Dashboards
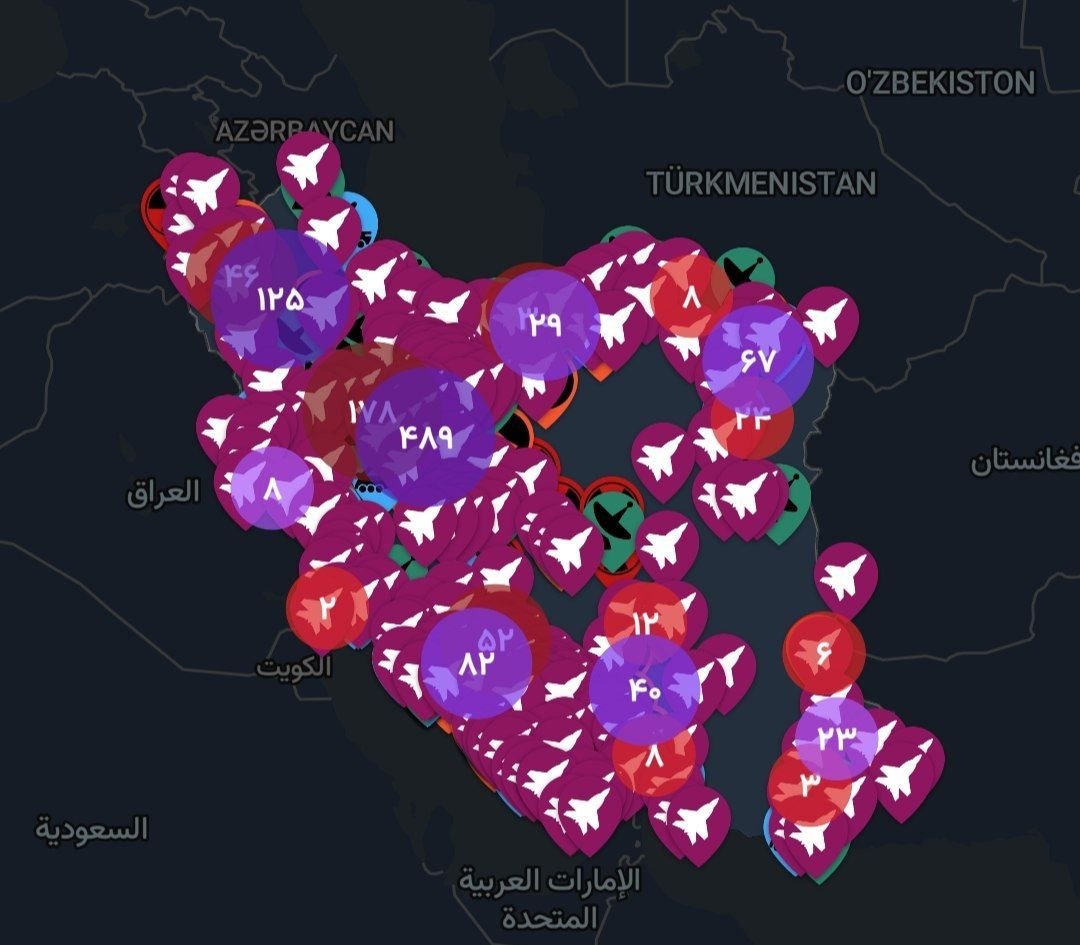
Highly classified military data surfaced on public-facing dashboards. Visual evidence retrieved from compromised networks indicates the presence of sophisticated tracking platforms. Developers mapped the entirety of Iran’s military and internal security infrastructure. Platforms transformed guarded state secrets into public knowledge.
Leaked interfaces reveal a comprehensive catalog. The dashboard tracked Confirmed Attacks and Evacuation Warnings. Crowdsourced models relied on Public Reports sections. The platforms featured sections dedicated to fallen citizens. The most severe breach involved the mapping of High-Risk Areas. The section cataloged exact geolocation markers. Users found coordinates for nuclear programs, missile facilities, air defense networks, radar installations, and drone bases.
The dashboard also monitored the domestic control infrastructure. The platform listed Locations of Oppression. Coordinates included government sites, paramilitary headquarters, intelligence bureaus, and prisons. The map featured dense clusters of nuclear and missile sites. The staggering concentration of deployed assets became highly visible. Decentralized mapping technologies completely obliterate geographical secrecy.
| Category (English) | Sub-Categories | Strategic Impact |
| High-Risk Areas | Nuclear Program, Missile Program, Air Defense, Radar. | Nullifies strategic surprise. |
| Locations of Oppression | Paramilitary HQ, Intelligence Centers, Prisons. | Empowers domestic resistance. |
| Active Conflict Monitoring | Confirmed Attacks, Evacuation Warnings. | Provides real-time battle damage assessment. |
Central Intelligence Agency Recruitment
Foreign intelligence services proactively used public websites to gather data. The US Central Intelligence Agency launched a highly visible recruitment campaign. The agency specifically targeted the Iranian populace.
The agency broadcast Farsi-language videos. The videos quickly accumulated millions of views. Officials explicitly solicited information. The broadcasts provided step-by-step instructions for secure communication. The US Central Intelligence Agency directed informants to bypass internet restrictions. The instructions advised using virtual private networks and disposable devices. Operatives guided users to public agency websites and darknet portals.
The public solicitation transformed millions of disaffected citizens into a decentralized surveillance network. The Iranian government instituted internet shutdowns between March 2 and March 14, 2026. Citizens systematically funneled eyewitness accounts and geolocated visual evidence through encrypted channels. The public website served as a secure drop-off point.Weaponizing Civilian Sites
Intelligence leaks exposed the covert deployment of military assets within civilian infrastructure. Security forces moved personnel and advanced weapons into at least 70 distinct civilian sites. The revelation fundamentally altered the tactical execution of the war.
The leaked intelligence documented a deeply entrenched pattern. The identified locations spanned 17 provinces and 28 cities. Thirty-four of the sites were active schools. Other locations included hospitals, public stadiums, and mosques. Journalists successfully geolocated visual evidence from seven educational facilities.
The deployment strategy operated as a premeditated military doctrine. Leaked internal directives confirmed the practice. The military embedded mobile ballistic missile launchers and anti-aircraft batteries within civilian infrastructure. Leaders shifted the risk of combat onto the civilian population. Planners assumed Western rules of engagement would protect schools and medical facilities.
International humanitarian law grants protected status to hospitals and schools. Protected status is not absolute. Legal frameworks stipulate that military occupation strips locations of their protected status. The presence of missile commands legally permits coalition forces to target the structures. The decentralized intelligence network nullified the human shield strategy. The public dissemination provided precise coordinates. The leaks proved to the domestic populace that the government intentionally endangered children.
The Minimum Wage Earner Vulnerability
Sociopolitical and macroeconomic conditions provided optimal conditions for massive cyber exploitation. Foreign actors compromised localized electronic communication networks. Intelligence communities conceptualize the exploitation through the Begir Negaran vulnerability.
The term translates to “anxious minimum-wage earner.” The Iranian populace suffered a series of economic shocks prior to 2025. Hyperinflation and devastating international sanctions decimated purchasing power. Retirees and minimum-wage workers faced acute desperation.
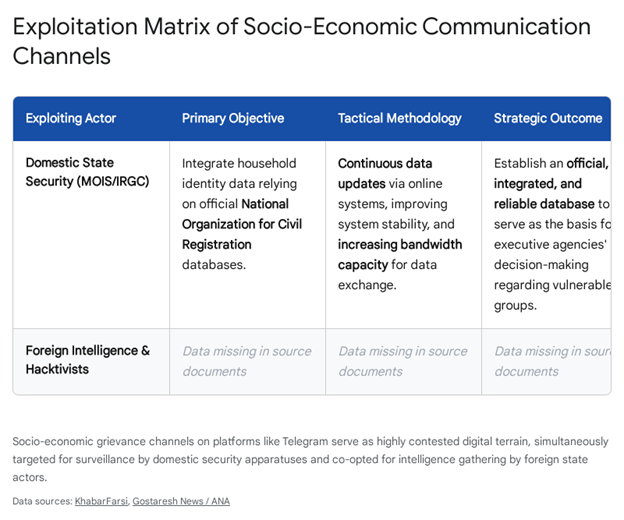
Millions of worried minimum-wage earners turned to encrypted messaging apps. Users relied on Telegram to organize horizontally. Workers discussed unpaid wages and coordinated localized labor protests. The sprawling Telegram channels evolved into massive repositories of granular sociopolitical data. The data mapped the exact geographic fault lines of civilian discontent.
Channel Compromise
State surveillance and foreign intelligence targeted the highly active user bases. Several high-profile grievance channels fell to compromise. The breach leaked internal communications, user databases, and geographic data.
Domestic state security infiltrated the channels to identify dissident leaders. Foreign intelligence services recognized the concentrated pools of potential informants. Operatives identified technologically adept individuals hostile to the state. Citizens likely provided essential human intelligence in exchange for financial support or access to a virtual private network.
Administrators list control of the channels. Attackers published private messages and the identities of tens of thousands of users. The massive leak exposed vulnerable citizens to state retaliation. The event demonstrated the profound depth of internal instability. Modern adversaries merely require access to online environments where an oppressed population discusses daily struggles.
State-Sponsored Retaliation
The Islamic Republic of Iran aggressively escalated offensive cyber operations. Coalition forces systematically destroyed air defense systems and eliminated senior command leadership. Cyber warfare became the primary mechanism for asymmetric retaliation.
The state apparatus relies on two primary entities. The Islamic Revolutionary Guard Corps oversees highly destructive operations against state-level adversaries. The corps penetrated the US Navy Marine Corps Intranet in 2013. The Ministry of Intelligence and Security focuses exclusively on psychological warfare and transnational repression.
The Handala Hack Team emerged as a highly disruptive actor. International intelligence assessments rapidly attributed the group directly to the Ministry of Intelligence and Security. Handala operates explicitly to create loud, chaotic, and maximally humiliating events. The group targets entities with ties to Israel or Western geopolitical interests.
Handala rarely attempts to crack hardened firewalls. The group exploits known vulnerabilities on public-facing websites. Attackers execute rapid operations to exfiltrate highly sensitive databases. The final step involves the immediate publication of stolen data on Telegram channels.
Handala’s operations targeted domestic US infrastructure. The group claimed responsibility for a destructive malware attack against Stryker, a multinational medical technologies firm. Operations targeted industrial manufacturing facilities in Israel and airport infrastructure in Kuwait. Hackers actively attempted to hijack municipal camera networks to improve ballistic missile targeting telemetry. The ministry additionally targeted international journalists to terrorize the expatriate dissident community.
Active Defense Operations
The highly visible nature of Handala’s operations necessitated aggressive countermeasures. The US Department of Justice seized four core domains operated by the Ministry of Intelligence and Security.
The seizure successfully dismantled the primary online pillars of the Iranian network. Attorney General Pamela Bondi and Federal Bureau of Investigation Director Kash Patel publicly condemned the operations. The retaliatory action aligns seamlessly with the evolving US Cyber Command doctrine.
Cyber warriors actively operate on foreign networks. Operatives gather intelligence and preemptively disrupt infrastructure. The dismantling of Handala’s domains demonstrated a forward-leaning defense posture. The United States actively degrades adversary infrastructure in the public sphere.
Wrap Up
The unprecedented convergence of cyber and kinetic warfare establishes a highly volatile paradigm. Cyber warfare is intrinsically linked to the physical survival of state apparatuses. The conflict eroded the distinction between combatant and civilian infrastructure. Iranian forces weaponized civilian spaces. Iranian hackers executed destructive attacks against civilian medical technology firms. The legal protections afforded to civilian sites inherently degrade under dual-use conditions.
The public online sphere is almost certainly the primary battleground for intelligence operations. Securing a nation requires far more than air-gapping central military databases. Adversaries relentlessly target poorly coded public websites and vulnerable external servers. Decentralized open-source intelligence aggregation offers a highly effective alternative to conventional military force.
Traditional theories of deterrence possess profound limitations in the cyber domain. The threat of overwhelming kinetic retaliation failed to stop Iranian offensive cyber operations. Hackers rapidly reconstituted offensive capabilities using deniable proxies. Heavily degraded states are highly likely to rely on asymmetric cyber warfare to project power and exact revenge. The modern battlefield depends entirely on the ability to monitor and manipulate the interconnected networked continuum.







You must be logged in to post a comment.