Operational and Strategic Analysis of the January 18 IRIB Cyber Offensive
The Collapse of the Monolith
On the evening of January 18, 2026, the ideological fortress of the Islamic Republic of Iran suffered a structural failure that no amount of concrete or kinetic force could mitigate. At approximately 21:30 local time, millions of Iranian households tuned into the state broadcaster, Islamic Republic of Iran Broadcasting (IRIB), were witnesses to an unprecedented intrusion. The programming schedule, which that evening included the highly anticipated coverage of the Spanish Super Cup final between Barcelona and Real Madrid on IRIB TV3, and standard evening news broadcasts on other channels, was violently interrupted.
The static did not lead to technical difficulties or a test pattern. Instead, it dissolved into the unthinkable: the crossed-out face of Supreme Leader Ayatollah Ali Khamenei, chants of “Death to the Dictator,” and a direct, televised appeal from the exiled Crown Prince Reza Pahlavi urging the nation to revolt. For ten minutes, the monopoly on truth that the Islamic Republic has jealously guarded for nearly five decades was shattered. This event was not merely a cyberattack; it was a psychological decapitation of the state’s primary instrument of control during a period of existential domestic crisis.
This report offers an exhaustive analysis of the January 18 incident, situated within the broader context of the “Bloody January” uprising that began in late 2025. By synthesizing technical forensic data, social media intelligence (SOCMINT), and geopolitical indicators, we reconstruct the anatomy of the attack, the ferocity of the state’s kinetic response, and the irreversible fracture of Iran’s digital sovereignty.
A Winter of Discontent
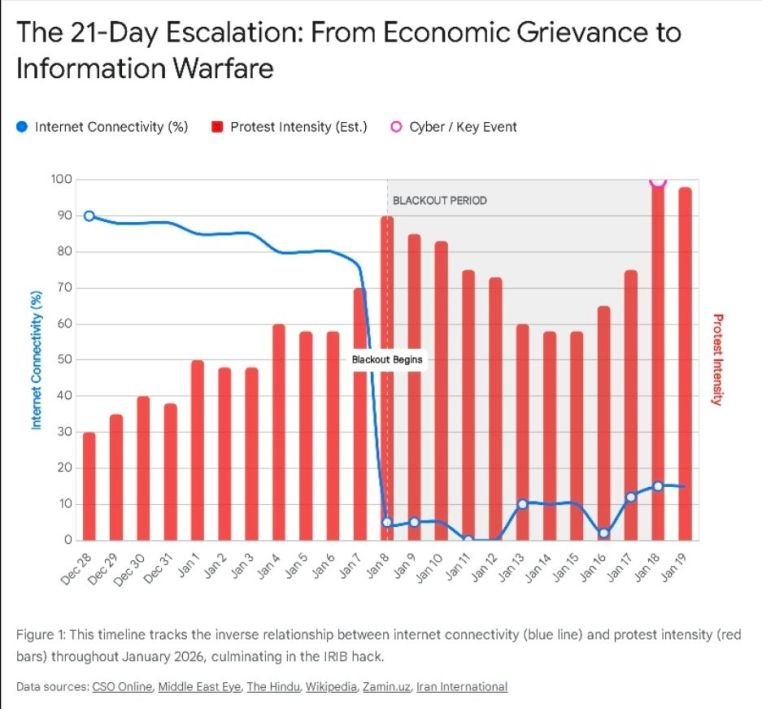
To understand the strategic significance of the IRIB hack, one must first map the terrain of unrest that preceded it. The cyber offensive was not an isolated bolt from the blue but the culmination of a twenty-one-day escalation cycle that brought the regime to the brink of collapse.
From Economic Malaise to Insurrection
The unrest began on December 28, 2025, triggered initially by the collapse of the Rial and the removal of subsidies on basic goods. However, as is characteristic of Iranian protest cycles, economic grievances rapidly metastasized into political demands. By the first week of January 2026, the slogans had shifted from “Bread, Jobs, Freedom” to “Clerics Get Lost” and “We Don’t Want an Islamic Republic.”
The scope of the uprising was unprecedented. Unlike the urban-centric protests of 2009 or the working-class unrest of 2019, the 2026 movement bridged all social strata. From the bazaars of Tabriz to the universities of Tehran, and crucially, to the impoverished provinces of Khuzestan and Sistan and Baluchestan, the rejection of the system was total.
The Kinetic Response: “Bloody January”
The state’s response was immediate and lethal. By January 8, recognizing that tear gas and batons were insufficient to stem the tide, the Supreme National Security Council (SNSC) authorized the use of military-grade force. The resulting crackdown has been described by human rights organizations as the deadliest in the history of the Islamic Republic.
Reports emerging from the country paint a harrowing picture of state violence. In Tehran, security forces deployed snipers to rooftops in residential neighborhoods like Ariashahr. One documented case is that of Reza Eskandarpour, a 37-year-old cabinet maker. On January 8, while protesting with friends, Eskandarpour was pinned down by sniper fire. After attempting to aid a wounded companion, he was targeted and struck by six live rounds, dying instantly. His story—an ordinary citizen preparing for marriage, gunned down in his own neighborhood—became a rallying cry on the few encrypted channels that remained operational.
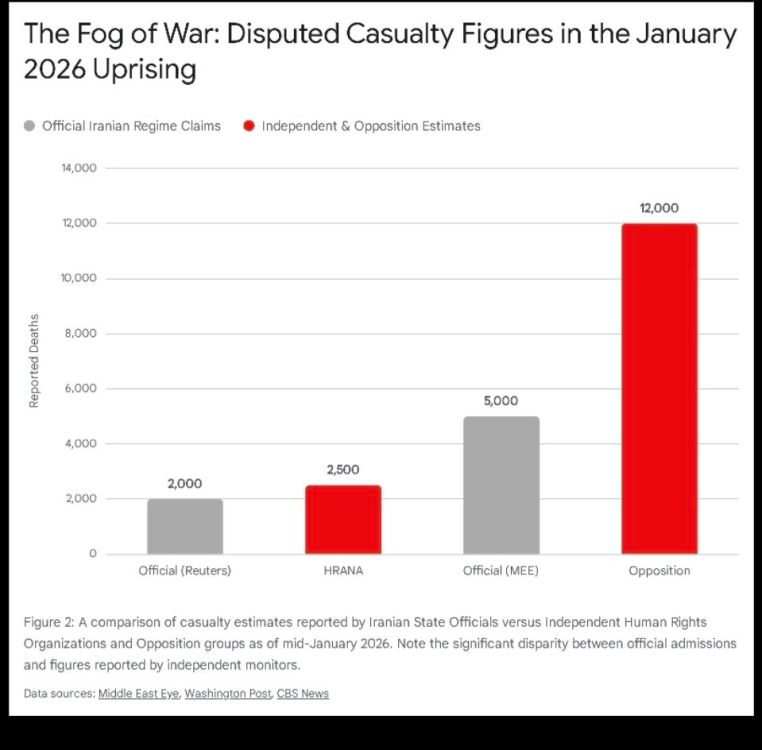
The casualty figures remain a subject of intense contention and form a key battleground in the information war:
- The Official Line: Government spokespersons, speaking anonymously to Reuters and domestic agencies, admitted to approximately 2,000 deaths. They framed these casualties as “terrorists” and “rioters” funded by foreign intelligence services, specifically blaming the US and Israel for “sedition.”
- The Opposition Count: Sources affiliated with the Mujahedin-e Khalq (MEK) and other diaspora opposition groups place the toll much higher, estimating between 5,000 and 12,000 fatalities.
- Forensic Verification: The most chilling evidence came from leaked video footage of a morgue in a Tehran suburb, verified by CBS News. The video showed at least 366 bodies piled in a single facility. Forensic analysis of the footage revealed a pattern of “birdshot” wounds fired at close range and high-velocity rifle rounds consistent with AK-47s, confirming the use of lethal force against unarmed crowds.
Anatomy of the Blackout
Parallel to the physical crackdown, the regime initiated a “Digital Iron Curtain.” On January 8, internet connectivity across Iran plummeted. This was not a degradation of service but a deliberate “kill switch” event. The Ministry of Information and Communications Technology (ICT) effectively severed the international gateways, isolating the Iranian intranet (The National Information Network or “NIN”) from the World Wide Web.
3.1 The “Barracks Internet” Strategy
The blackout of January 2026 marked the debut of a new long-term strategy known as the “Barracks Internet.” Unlike previous shutdowns which were temporary tactical measures, this operation signaled a permanent shift in infrastructure. The regime began a systematic purge of the telecommunications sector; the CEO of Irancell, a major mobile network operator, was reportedly dismissed and accused of treason for delaying the blackout orders, replaced by an appointee directly loyal to the IRGC.
The objective was total information sanitization. Access to global platforms like Instagram, WhatsApp, and Telegram—lifelines for the opposition—was completely blocked. In their place, the state promoted domestic alternatives like “Rubika,” a super-app monitored extensively by intelligence services. To enforce this migration, physical checkpoints were established in major cities where security forces confiscated smartphones to check for “illegal” VPNs and protest footage.
The War on Starlink
Recognizing the threat posed by satellite internet, the state launched a massive jamming operation. Leveraging ground-based electronic warfare stations, the IRGC broadcast high-power noise on the Ku and Ka bands used by Starlink terminals. Reports from the ground indicated packet loss rates of 30% to 80% in urban centers, rendering the service intermittent at best. Despite these countermeasures, smuggling networks managed to bring hundreds of terminals into the country, providing the thin digital thread through which the morgue videos and sniper footage eventually reached the outside world.
January 18, 21:30 IRST
It was against this backdrop of total suppression—a silenced internet and bloodied streets—that the IRIB hack occurred.
IRIB and the Badr Satellite
The Islamic Republic of Iran Broadcasting corporation is constitutionally mandated to be the sole broadcaster in Iran. Its head is appointed directly by the Supreme Leader, and its remit is the propagation of state ideology. For the regime, IRIB is not media; it is command and control.
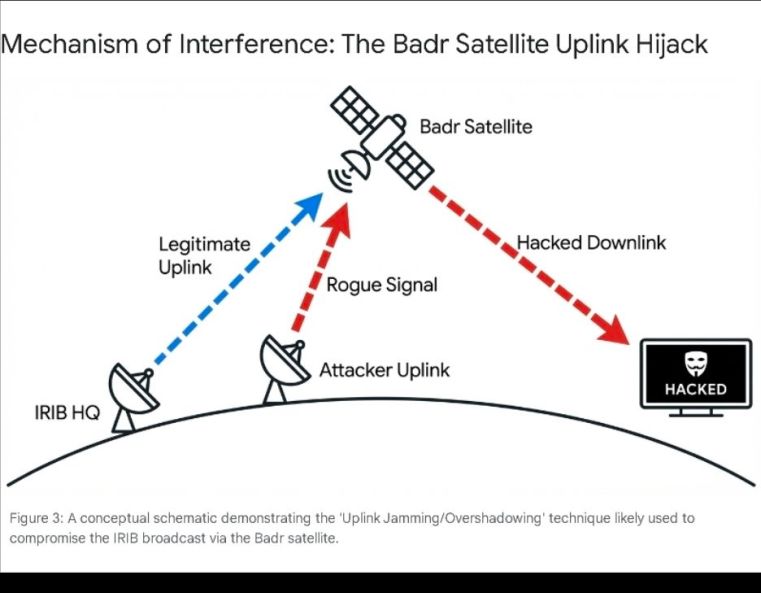
The specific channels targeted—IRIB TV1, TV3, and the provincial channel “Farsat”—are distributed via the Badr satellite constellation (specifically Badr-4/5/6/7 at 26° East). This satellite fleet, operated by the Arab Satellite Communications Organization (Arabsat), covers the entire Middle East, North Africa, and parts of Europe. It is the primary downlink source for millions of Iranian households who rely on satellite dishes to bypass local censorship, ironically making them vulnerable to this specific vector of attack.
The Mechanics of the Hijack
Technical analysis of the disruption suggests a “Signal Override” or “Uplink Jamming” attack rather than a compromise of the studio playout servers.
In a standard DVB-S (Digital Video Broadcasting – Satellite) architecture, the broadcaster sends a signal from a ground station (uplink) to the satellite. The satellite’s transponder amplifies this frequency and beams it back to Earth (downlink). The vulnerability lies in the fact that most commercial satellites act as “bent pipes”—they do not authenticate the source of the uplink. If an attacker can transmit a signal on the same frequency with significantly higher power than the legitimate ground station, the satellite’s automatic gain control (AGC) will lock onto the stronger rogue signal, effectively overwriting the legitimate broadcast.
The fact that analog and cable networks inside Iran were largely unaffected supports this theory. The attack occurred in the “last mile” of space transmission, invisible to the internal fiber networks but blindingly obvious to anyone with a satellite dish. However, IRIB’s subsequent statement admitting to a “complex” hacking operation suggests a hybrid component. It is possible that the attackers also compromised the telemetry and control (T&C) systems to prevent the IRIB engineers from switching transponders or mitigating the jam, or that they inserted the content directly into the uplink stream at a compromised ground station outside of Iran.
A carefully Curated Psychological Blow
The choice of content injected into the stream revealed a sophisticated understanding of Iranian psychology and political semiotics.
- The Taboo Breaker: The broadcast opened with the image of Supreme Leader Ali Khamenei, his face violently crossed out with red graphical strokes. In a country where defacing the Leader’s image is a crime punishable by death, seeing this on state television shattered the aura of untouchability that surrounds the Velayat-e Faqih.
- The Alternative Sovereign: The feed then cut to Reza Pahlavi. The exiled Crown Prince, son of the deposed Shah, has long been a figure of nostalgia, but in this broadcast, he assumed the role of a commander-in-chief. His message was operational, not just aspirational. He explicitly called on the armed forces—the Artesh and the disgruntled elements of the IRGC—to “choose the side of the nation” and facilitate the transition.
- The Reality Injection: Perhaps most damaging was the footage of the protests themselves. For three weeks, IRIB had shown only calm streets and pro-regime rallies. Suddenly, millions of Iranians saw the burning tires of Isfahan, the street battles in Sanandaj, and the international solidarity marches in Berlin and Los Angeles. The “Spiral of Silence”—the belief that one is alone in their dissent—was broken instantly.
Attribution and the Geopolitical Shadow War
The sophistication of the attack has led to immediate speculation regarding the perpetrators. While no group has provided definitive cryptographic proof of responsibility, the geopolitical fingerprints point to two primary suspects, likely working in concert.
The “Israel” Hypothesis
Iranian state media and officials immediately pointed the finger at Tel Aviv. This is not merely reflexive blaming; it aligns with the strategic doctrine of the Israeli intelligence community. Following the “Octopus Doctrine” articulated by Prime Minister Naftali Bennett in the early 2020s, Israel shifted from fighting Iran’s proxies (the tentacles) to striking the head of the regime in Tehran.
Israel possesses the requisite SIGINT capabilities to execute a satellite hijack. The Unit 8200 and the technological division of the Mossad have a long history of cyber-sabotage in Iran (e.g., Stuxnet, the Natanz explosion, the port of Shahid Rajaee hack). Hijacking IRIB to foment internal unrest serves a clear strategic goal: destabilizing the regime from within, forcing it to divert resources from its nuclear program and regional proxies (Hezbollah, Hamas) to domestic survival.
The “Edalat-e Ali” and “Handala” Nexus
While state actors likely provided the technical means, the operation bore the branding of Iranian hacktivist groups.
- Edalat-e Ali (Justice of Ali): This group gained fame for hacking the CCTV cameras of Evin Prison, exposing the abuse of prisoners. Their involvement (or the use of their moniker) lends the attack domestic legitimacy, framing it as an act of internal resistance rather than foreign aggression.
- Handala: Conversely, the cyber-conflict is bidirectional. As noted in research snippets, pro-Iranian groups like “Handala” and “Cyber Fattah” have been active in targeting Israeli infrastructure and even Saudi sporting events (like the Saudi Games data leak). This indicates a crowded theater of cyber-warfare where state-sponsored APTs (Advanced Persistent Threats) mask themselves as hacktivists to maintain plausible deniability.
Strategic Implications: The Post-Truth Era in Tehran
The January 18 attack has profound implications for the survival of the Islamic Republic.
The Loss of Deterrence
The IRIB hack proved that the regime’s vaunted cyber-army—which has successfully attacked US elections and Albanian government servers—cannot defend its own home front. This vulnerability invites further attacks. If the state broadcaster can be hijacked, then the banking system, the air traffic control networks, and the nuclear command and control infrastructure are theoretically within reach. The “complex” nature of the attack admitted by IRIB officials is a tacit acknowledgment of this fragility.
The Fragmentation of the Security Forces
Reza Pahlavi’s direct appeal to the military, delivered via the regime’s own airwaves, inserts a “poison pill” into the chain of command. Every commander must now wonder if their subordinates watched the broadcast and if the seed of doubt has been planted. In a conscript-heavy army, the realization that the “rioters” are supported by a viable alternative leadership can lead to mass desertions or, more dangerously for the regime, mutiny.
The Failure of the “National Information Network”
The regime’s massive investment in the NIN—intended to create a halal, sealed internet—has failed its primary stress test. The “Barracks Internet” may stop a teenager in Tehran from accessing Instagram, but it could not stop a signal entering from space. The regime is fighting 21st-century information warfare with 20th-century censorship tools. The technological asymmetry favors the offense; as Starlink terminals proliferate and satellite jamming techniques are circumvented, the “Digital Iron Curtain” will become increasingly porous.
The events of the evening of January 18, 2026, represent a watershed moment in the history of the Iranian opposition. For ten minutes, the Islamic Republic ceased to exist on its own airwaves, replaced by the vision of a secular, democratic alternative. While the streets may be cleared by sniper fire and the prisons filled with dissidents, the psychological barrier of the regime’s invincibility has been breached.
The IRIB hack demonstrated that in the modern era, sovereignty is not just about controlling borders but about controlling the narrative. By losing control of the screens, the Islamic Republic has lost the most critical battle of the revolution. The static has cleared, but the signal sent on January 18 will resonate long after the broadcast ended. The war for Iran is no longer just being fought in the alleyways of Tehran, but in the orbital mechanics of the Badr satellites and the server farms of the digital underground.





You must be logged in to post a comment.