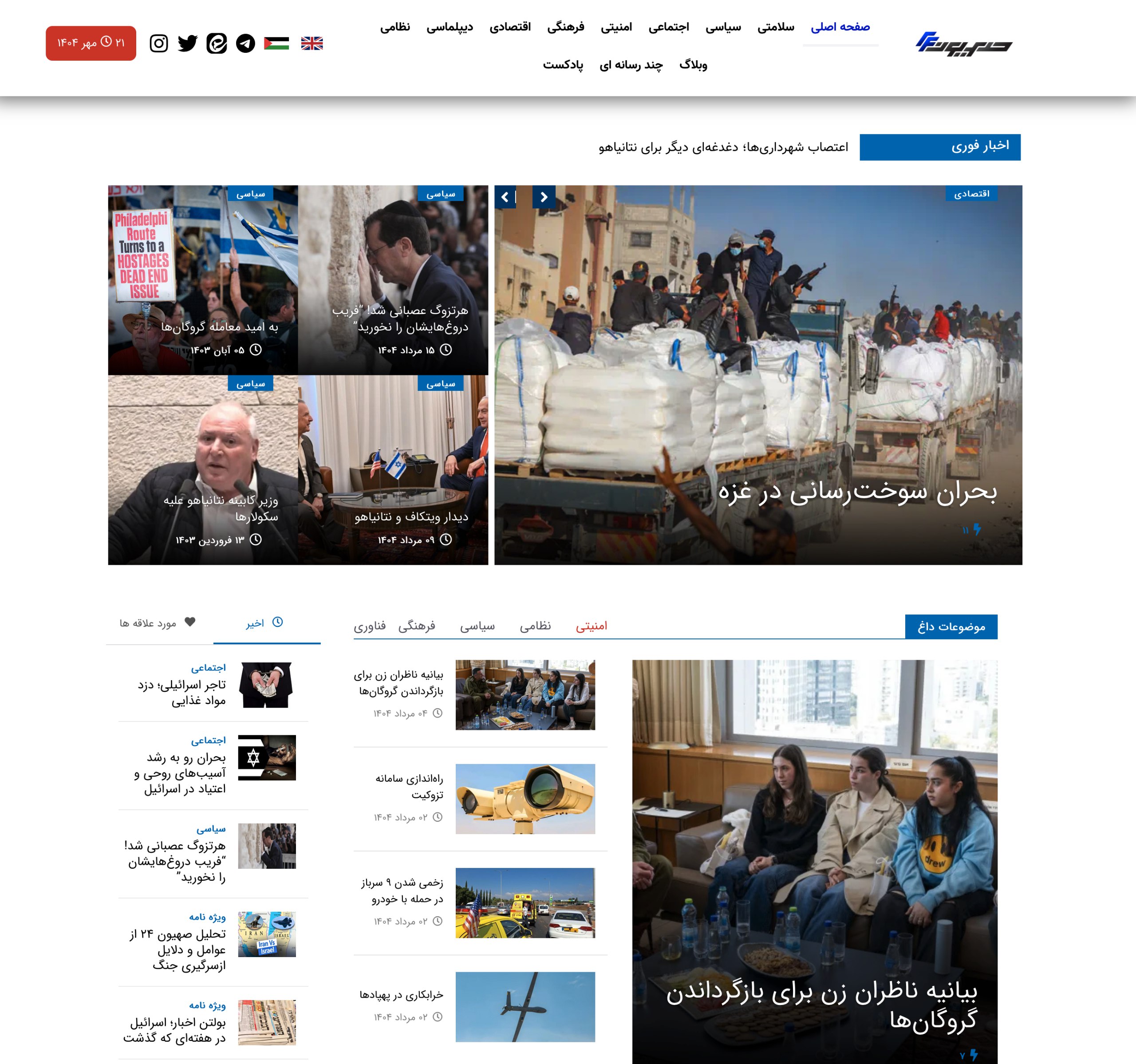
Evidence in the leaked pack points to an #IRGC-IO Unit 50 program that directs intrusions against Israeli targets and selected regional and Western entities. Documents, invoices, screenshots, and Persian memos tie operators to front firms, a custom Windows RAT named Thaqib (تاقب), and monthly operational reporting. Names, national IDs, and signatures create traceable anchors. Front companies appear to procure network access, IP services, and office cover while developers maintain a multi-module panel with stealer, keylogger, file exfiltration, and RAT update features. Targeting lists include foreign and domestic victims, including Iranian citizens. Evidence supports an APT35-adjacent cluster under a unified managerial layer.
Source Pack — What each artifact supports
| Artifact (thumbnail ref) | Language & issuer | Claimed content | What the artifact evidences | Confidence |
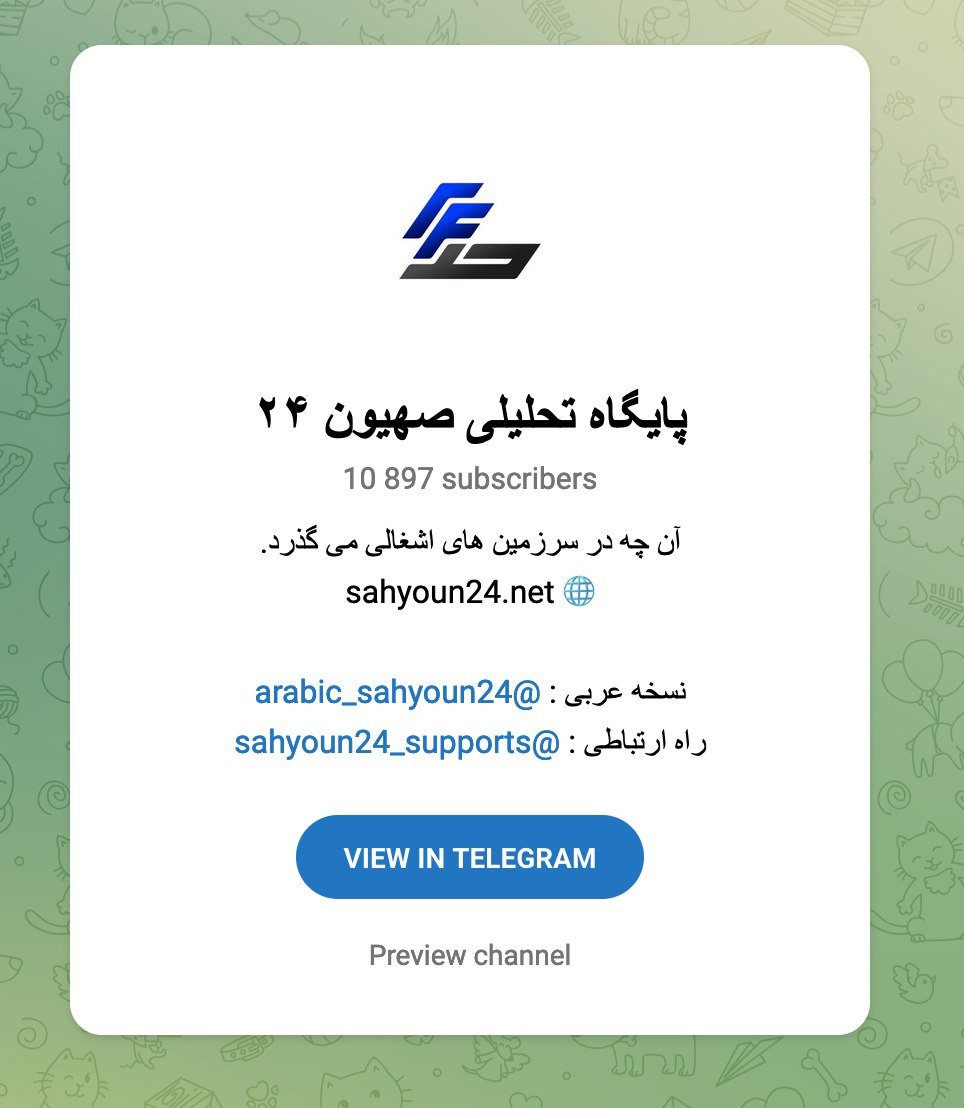
| Employment letter (اندیشان تفکر سفید) | Persian; “White Thought Depths” NGO | Confirms employment for Mohammad Erfan Hamidi Aref (ID 0023199709) | HR link between front firm and named operator; signature Manouchehr Vosoughi Niri | Medium |
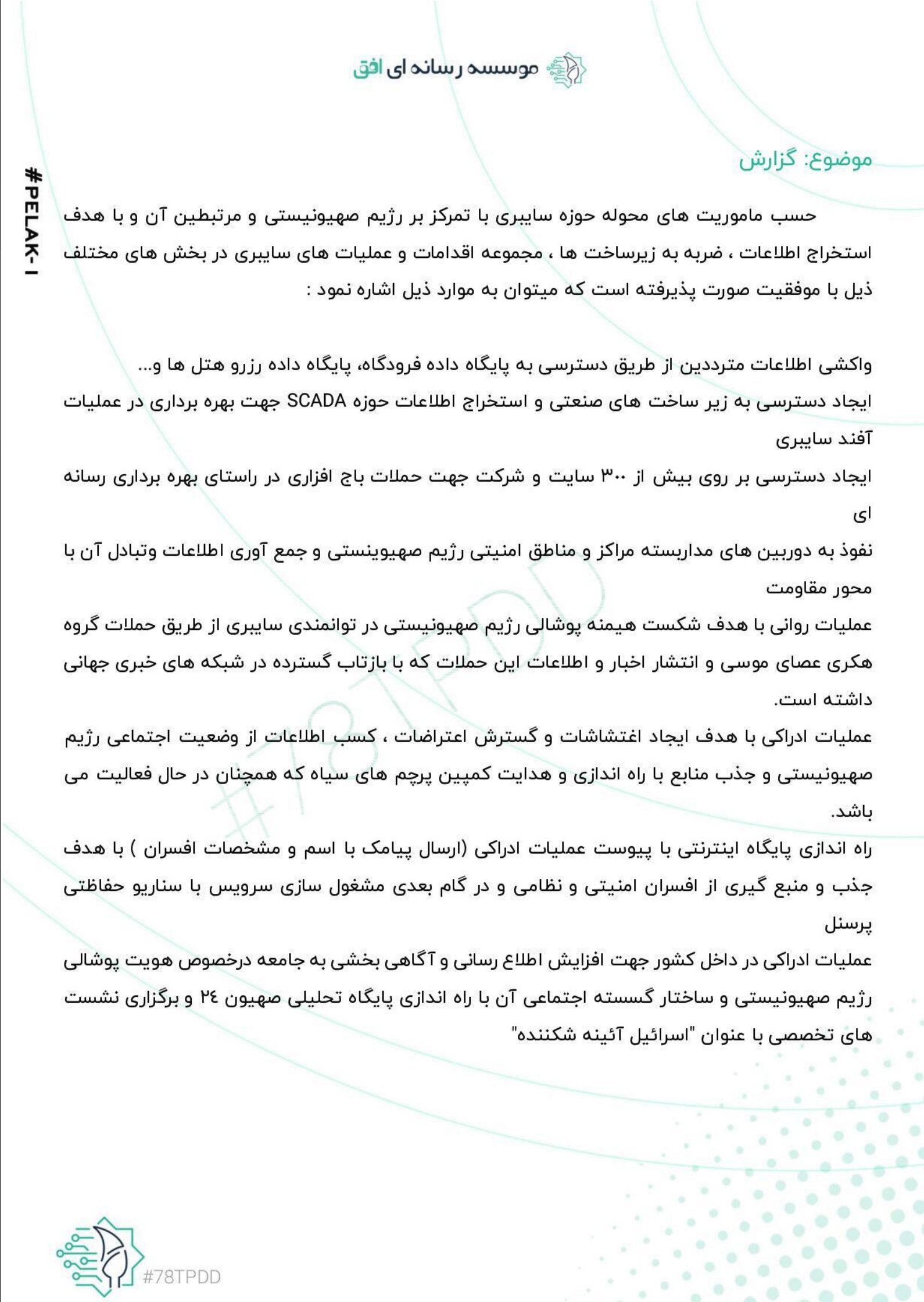
| “Ofogh Media Institute” tasking page | Persian | Task list- 300+ site access, SCADA info extraction, camera access, influence ops | Directives align with intrusion + IO playbook; wording reflects tasking, not publicity | Medium-High |
| Presenter frame “سهیل کثیری نژاد” | Persian lower-third | Researcher on “Israel” domain in Sakhyoun24 media | Link to propaganda ecosystem that launders narratives from ops | Medium |
| Zitel ISP pro-forma invoice | Persian; dated 1403/06/11 | 171 days of “IP usage” | Infrastructure procurement trail; buyer Mohsen Foroughi named elsewhere | Medium |
| Telegram channel “پایگاه تحلیلی صهیون۲۴” | Persian | Subscriber footprint and domains | Media node for perception ops and narrative packaging | Medium |
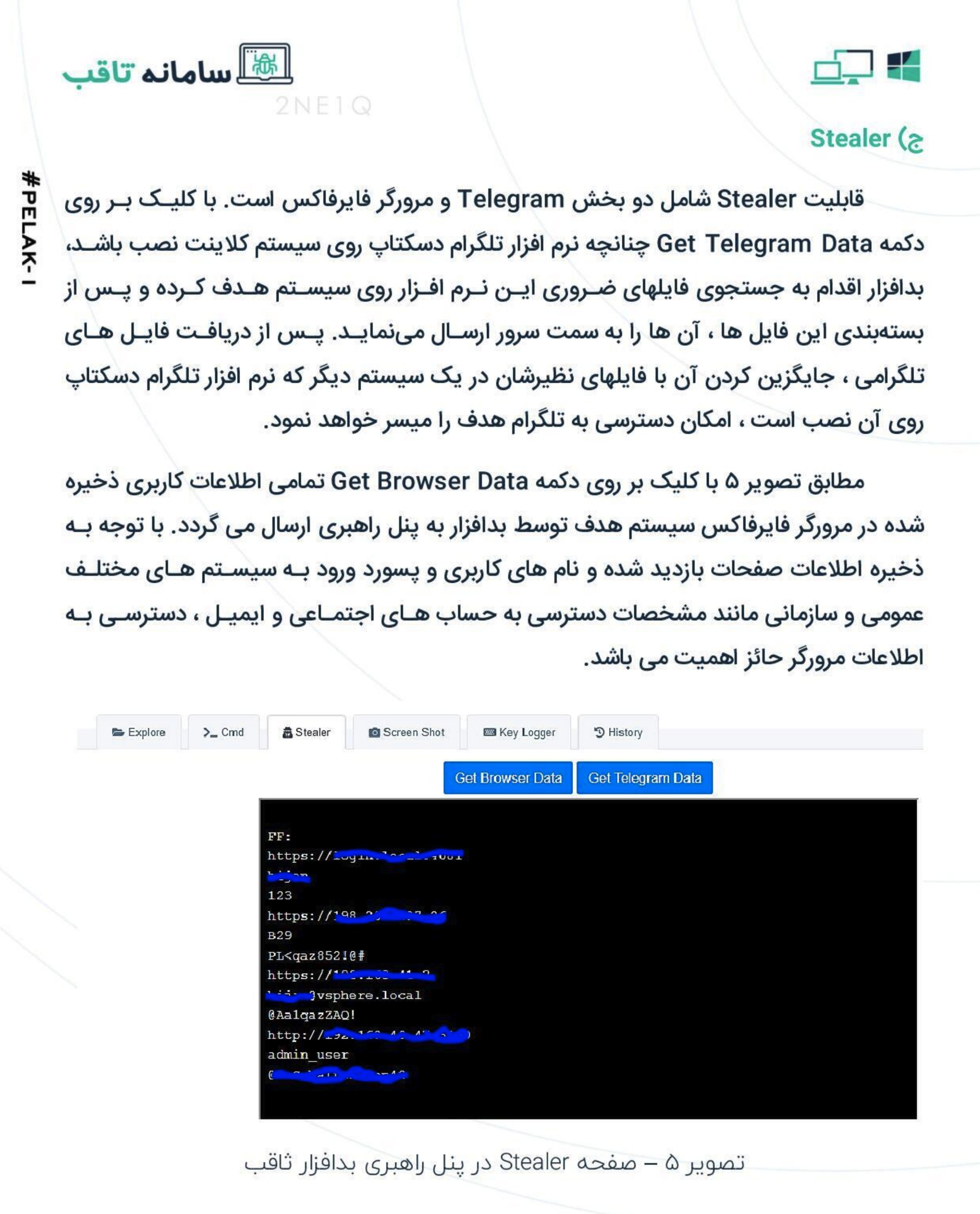
| Thaqib cover pages + panel screenshots | Persian UI | RAT management- Explore/Cmd/Stealer/Keylogger/History; “Get Browser Data / Get Telegram Data”; “Update RAT” | Custom Windows implant with modular C2; Telegram token theft; credential harvesting; versioning | High |
| News portal screenshot (Sakhyoun24 site) | Persian | Anti-Israel editorial front | IO outlet aligned with Unit 50 themes | Medium |
People, fronts, and roles (from the pack)
| Name | National ID | Role in pack | Linked entity |
| Abbas Rahrovi a.k.a. Abbas Hosseini | 4270844116 | Overall ops commander | IRGC-IO Unit 50 |
| Manouchehr Vosoughi Niri | — | Signatory on “White Thought Depths” letter | IRGC-IO official; front oversight |
| Mohammad Erfan Hamidi Aref | 0023199709 | Employee named in HR letter | White Thought Depths |
| Mohsen Foroughi | 1467932698 | Purchaser of technical services | Zitel IP services invoice |
| Sakhyoun24 / Ofogh Media Institute | — | Media + developer front | Thaqib RAT docs, channel ops |
TTP mapping (MITRE ATT&CK)
| Phase | TTPs observed in evidence | Examples in pack |
| Recon | T1593, T1591 | Directed collection on Israeli gov, energy, aviation, finance; embassy accounts |
| Initial access | T1566, T1190, T1059, CVE-2024-1709 exploitation | Phishing, supply-chain notes, panel cmd exec |
| Execution | T1059, T1204 | RAT “Execute” features; one-click stealer |
| Persistence | T1547, T1543 | Auto-run weekly toggle in panel |
| Priv-Esc | T1068 | Exploit references in dev notes |
| Defense evasion | T1027, AV bypass claim | “Bypass antivirus” feature note |
| Credential access | T1555, T1552 | Browser and Telegram data theft |
| Discovery | T1082, T1016 | “Ask Current Info” host survey |
| Collection | T1114, T1056 | Email stealing, keylogger |
| C2 | T1071, T1090 | Web panel; DNS/router manipulation note |
| Exfiltration | T1041 | File list and transfer counters |
| Impact/IO | T1491, T1585 | Media site tie-in; psychological ops lines |
Authenticity assessment
- Document style and stamps match Iranian HR and invoice templates; date formats use Solar Hijri; phrasing tracks administrative Persian.
- Panel UI follows common Delphi/.NET RAT dashboards seen in Iranian clusters; feature names align with Telegram stealer workflows on Windows.
- Front brand set (Ofogh, Sakhyoun24) reflects a media-security blend that often masks tech ops with “research” cover.
- Names plus national IDs create verifiable trails across Iran’s registries, tax codes, and telco accounts.
- Cross-cue between tasking memo and monthly reporting screenshot shows managerial oversight and time logging.
Assessment- High likelihood of genuine internal material; moderate chance of partial fabrication within narrative slides. Overall confidence- Medium-High.
Operational picture
- Program orders infiltration of 300+ sites, SCADA reconnaissance, and CCTV access near security nodes.
- Team tracks hours, produces monthly summaries, and routes reports to senior officials.
- Procurement flows through Zitel IP service blocks and likely other ISPs; 171-day allotment aligns with campaign windows.
- “Thaqib” provides RAT, stealer, keylogger, screenshot, and remote shell; operators update implants from the panel.
- Target set spans Israel and regional adversaries; internal task lists include Iranian dissidents and domestic infrastructure.
OPSEC mistakes that open doors
| Mistake | Exploit path |
| Real names with national IDs on HR and procurement | Civil registry pulls, tax file tracing, property and corporate record checks |
| Visible panel strings and buttons | YARA and Sigma rules from UI text; hunting across VT, sandboxes, EDR telemetry |
| Zitel invoice numbers and dates | ISP request for payer accounts, source IP allocations, MAC CPE records |
| Telegram channel handles | Platform requests for admin phone hashes, payment receipts, login IP history |
| Signature blocks and seals | Handwriting, stamp forensics, prior filings correlation |
Forensics to extract now
- Malware IOCs- panel paths, URL patterns, hardcoded routes, user-agent strings, update beacons, mutex names.
- Crypto traces- any wallet mentions in panel logs; procurement payments.
- Network- Zitel IP ranges tied to the invoice period; DNS rewrite infra mentioned in the memo.
- Document metadata- author fields, creation times, printer serials.
- Linguistics- recurring phrasing across memos and media posts; author clustering for Rahrovi/Hosseini.
Alternative hypotheses and tests
| Hypothesis | What would validate | What would falsify |
| Genuine Unit 50 leak | Registry hits for named IDs; ISP confirmation; matching C2 telemetry in victim nets | No registry match; forged stamp analysis; dead infrastructure |
| Mixed package (true tech + inflated tasking) | Live C2 plus partial doc forgery signals | Strong signs of tampered images; mis-typed bureaucratic norms |
| Deception by rival faction | Mismatch between names and payroll; media assets registered abroad | Direct payroll links to IRGC organ; internal comm chains recovered |
Action plan for defenders and investigators
- Build YARA from Persian UI strings- “Get Browser Data”, “Get Telegram Data”, “Ask Current Info”, “Update RAT”, and module tab names in Persian.
- Query EDR for Telegram Desktop path grabs and levelDB token theft sequences; flag browser Login Data access bursts.
- Sweep for DNS CPE rule edits on consumer routers; search for policy objects pushed during the invoice window.
- Task registries in Iran for corporate files on White Thought Depths, Ofogh Media Institute, and any Sakhyoun24 legal shell; pull officers, addresses, bank accounts.
- Engage Zitel for IP block allocation and payer identity tied to invoice numbers.
- Pivot on Telegram handles for admin phone hashes, recovery emails, and session IPs; request session teardown.
- Share IOCs with SCADA operators; hunt for reconnaissance traffic that queries Modbus, DNP3, or vendor web panels from Iranian IP space linked to Zitel records.
- Prepare preservation orders for email and hosting related to the panel domain(s); capture TLS cert histories.
Prosecutorial hooks
- National ID-anchored identities tied to procurement and HR letters.
- Invoice chain with dates, amounts, and bank fields.
- RAT panel screenshots with distinct UI and dataset samples.
- Channel branding that connects propaganda output to the technical team.
- Monthly reporting cadence that shows managerial control and systematic operations.
Evidence supports an IRGC-IO Unit 50 program that aligns with APT35/Charming Kitten tradecraft while extending into infrastructure and media operations under front branding. Names, IDs, and invoices give law enforcement a direct route to subpoenas and arrests. New releases from “Catbreakers” likely expose more nodes; rapid triage and preservation will lock in the trail before operators burn infrastructure.












You must be logged in to post a comment.