The Persian-language slides from Nariman Gharib cybersecurity company #امنبان (“Amanban”) highlight the organization’s strategic goals for the past year. Analyzing this within the framework of Iranian cyber capabilities and intelligence doctrine provides a critical perspective on its function, intent, and possible malign uses.
Key Content and Context Analysis
Content Summary
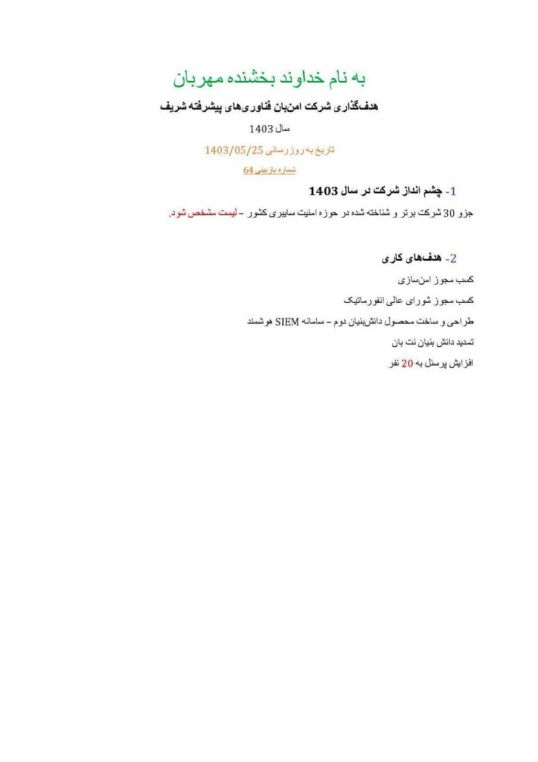
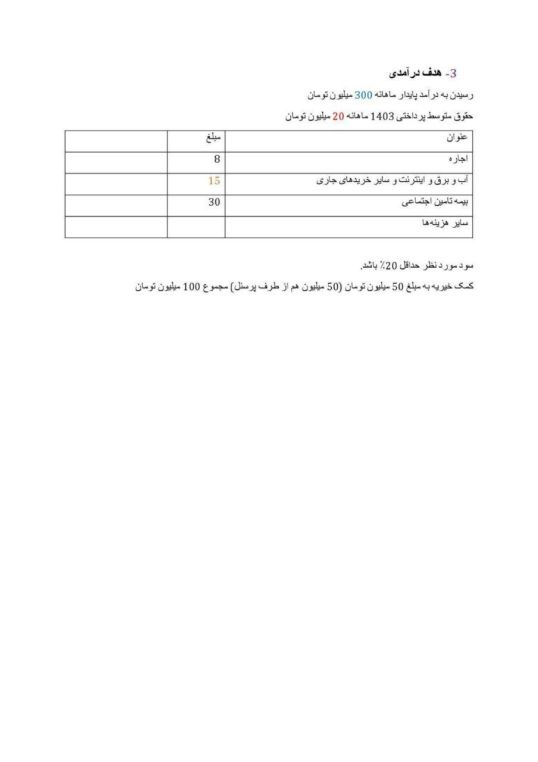
The slide lists strategic objectives of Amanban, such as “improving national cybersecurity”, “increasing threat detection capabilities”, “expanding cooperation with domestic entities”, and “developing indigenous technologies”.
The organization identifies as a national cyber defense actor but does not mention offensive capabilities directly.
Organizational Role
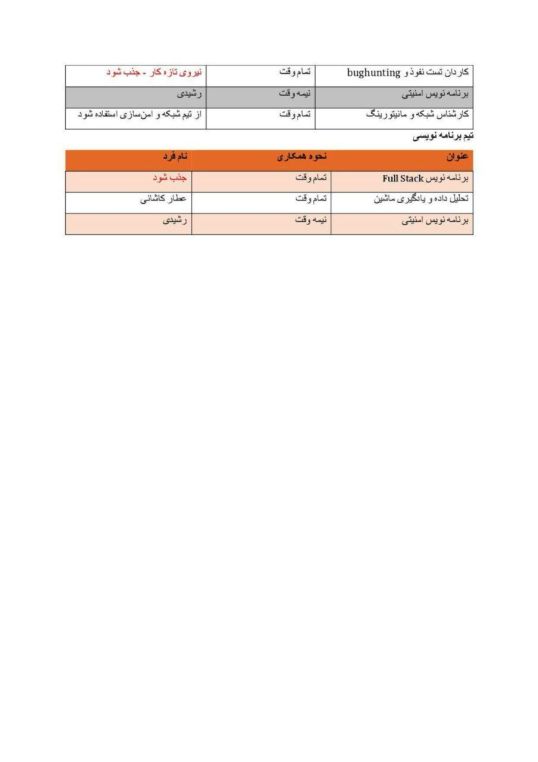
Despite its defensive posture, Amanban likely functions as a contractor or cover entity for more aggressive Iranian state-affiliated cyber units, particularly the IRGC’s Cyber Command (IRGC-CEC) or MOIS. Similar organizations like Eeleyanet Gostar, Dataware Arman, and Ravin Academy have been documented as fronts or intermediaries for Iran’s cyber apparatus.
Alignment with IRGC Objectives
The slide’s emphasis on national capability and “threat hunting” aligns closely with the IRGC’s doctrine of internal and external surveillance and offensive preparation. In line with Iran’s hybrid warfare and “forward defense” strategy, such cybersecurity entities contribute to both defensive resilience and preemptive cyber operations.
The intent, while stated as “protective”, often masks dual-use infrastructure (e.g., malware labs, threat intel platforms) which are used in campaigns like those run by APT34 (OilRig) and APT35 (Charming Kitten).



Malicious Potential
While the slide is sanitized for public or intra-agency distribution, its vague references to “operational expansion”, “strategic partnerships”, and “platform development” may signal capability growth to support IRGC or MOIS priorities, including regional espionage, counter-dissident activities, and cyber-enabled influence operations.
The lack of transparency, absence of international cooperation markers, and the association with other known IRGC-linked projects suggests a probable malign intent cloaked under a defensive narrative.
—–
While #امنبان presents itself as a national cybersecurity actor, the goals outlined in the slide strongly align with the IRGC’s broader cyber doctrine. Given the opaque nature of Iranian cyber institutions and historical precedents, it is highly likely this entity plays an auxiliary role in Iran’s offensive cyber infrastructure, supporting activities such as digital espionage, infrastructure mapping, or influence operations.







You must be logged in to post a comment.