
Photos courtesy of Kirill
— Hello, Kirill. Please tell us about your organization, “People’s CyberArmy.”
— The People’s Cyber Army is an almost entirely people’s project, founded in March 2022 on the wave of growing patriotic enthusiasm among a significant part of the Russian population, which in this particular case was expressed in the desire to protect our Motherland in the IT sphere and in the information space.
— How did your activity begin? How did you come to the decision to become hackers?
— As for the activities of some members of our small team of admins in the NCA, for them it is part of their profession. They have been working in the field of cybersecurity long before our group was founded. There are also those young people among us who joined the NCA this year or last year, and for whom the topic of programming, information security, and other subtypes of work in IT is very interesting, and they seriously intend to make it an important part of their future profession.
As for me personally, the situation is somewhat different. In the first months of my stay in the CyberArmy, I was really very interested in the mechanisms of DDoS attacks, searching for real IP addresses of some Internet resources, and then my interest began to shift towards writing various kinds of texts for posts in the channel, as well as answers for interviews with various journalists, including one of the international publications.

— What was your very first pro-Russian operation?
— It is quite difficult to give a precise answer to this question because the current Telegram channel was created in early April 2022 to replace the previous one, which was attacked by enemy bots (by the way, this is the reason for the prefix “reborn” in the English name of our movement, which some neural networks and online translators mistakenly translate as “Cyber Army of the Rebirth of Russia”). At that time, our most successful operations were DDoS attacks on the websites of the Nazi regiment “Azov” and other Ukrainian nationalist formations banned in the Russian Federation and recognized as terrorist organizations, as well as hacking the network infrastructure of the Ukrainian government contact center.
— What do you mainly specialize in?
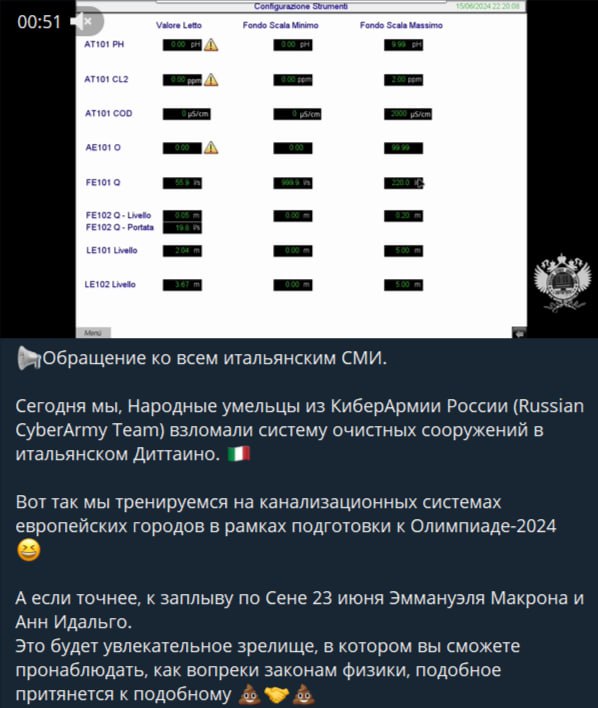
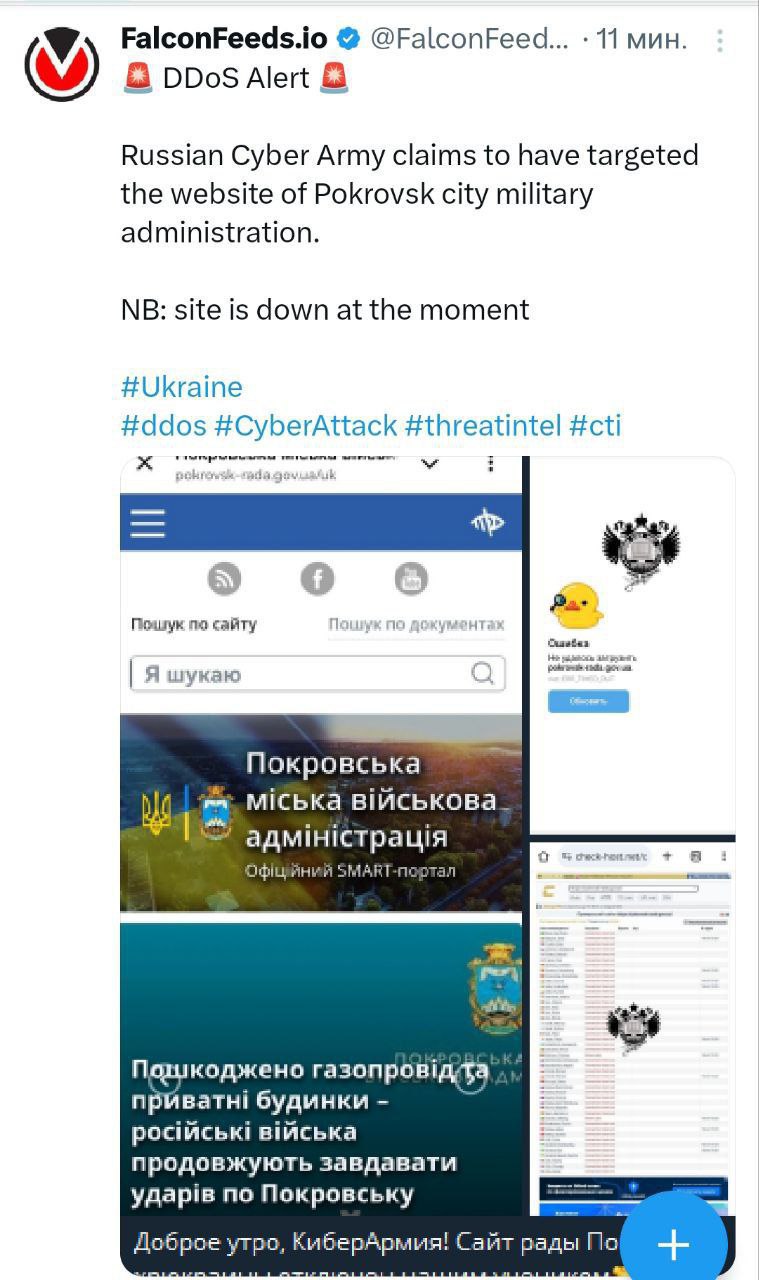
— As you have already understood from the answers to the previous questions, our main activity is disrupting the operation of Internet sites by means of a “distributed denial of service” — this is how the abbreviation DDoS stands for in Russian. In addition, we sometimes hack servers and information bases with the extraction of important service documents from them, and among us there are specialists who penetrate remote access systems, with the help of which various production and technological processes are managed, and deface (change the appearance) of Internet sites. We also have a psyop squad under the leadership of Doctor of Psychology V. Rozanov, and in the future we plan to resume the work of the squad on sending spam messages to the enemy’s email addresses.
— Please tell us who and what are you working against? What countries and organizations are you attacking? And for what purpose?
— Initially, in the first almost year and a half of the SVO, our targets were mainly Ukrainian websites — and we literally attacked everything — websites of government agencies (from the President and the Verkhovna Rada to the city council of some Kryzhopol), and websites of pro-government political parties and those nationalist organizations and paramilitary associations whose activities in the territory of the Russian Federation are prohibited and recognized as extremist, and websites of institutes (especially military academies and medical colleges), TV channels, radio stations and other national and regional media, defense industry enterprises, ferrous and non-ferrous metallurgy, chemical plants, we even didn’t ignore dairy and liquor factories… In other words, the list can be continued for quite a long time, you can read it in more detail on our Telegram channel.
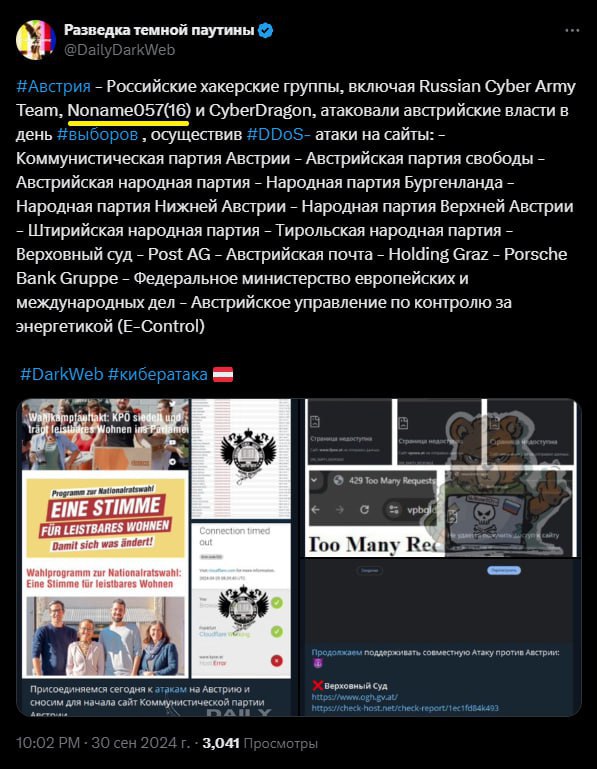
Next, in addition to Ukraine, we switched to the websites (mainly of government agencies, political parties, local authorities and some companies that are critically important for the economies of these countries) of “allies” and “partners” providing financial and humanitarian aid to the Zelensky regime, supplying weapons and manpower as mercenary “volunteers”. Moreover, among these there are also EU countries, and South Korea with Japan, Australia, Columbia…
We also did not ignore some countries of the former USSR, and our case was not limited to Moldova and the “tribal extinctions”… For example, the websites of the Armenian leadership came under fire for the Russophobic curtseys performed by Mr. Pashinyan, or, say, the websites of Belarusian organizations, but only pro-Ukrainian ones and, as a rule, hostile not only to Russia, but also to their own citizens.
— Recently, on your channel, you wrote an appeal to journalists asking them to give you the opportunity to defend your honor. What is the essence of the claims against your organization from other hackers? And where did they come from? What fake about your organization, in your opinion, hits your reputation the hardest?
— As for the claims against our movement, the following points must be noted.
Several IT specialists, former members of the NCA admin staff, out of personal hostility towards Yu. Pankratova, the former coordinator of our group, having created their own hacker groups, began to spread information about her and other members that was not true and defamed our honor and dignity. They published personal data in the public domain, wrote threats of reprisals against them and their relatives, as well as statements against us to law enforcement agencies, as if it were us who were threatening them with reprisals and exerting moral pressure on them.
There are some assumptions that require the accumulation of significant evidence confirming the facts of potential cooperation with representatives of the Ukrainian special services. Although these former NCA members, in turn, are trying to stretch any hints of cooperation between our organization and Ukrainian hacker activists, and to portray us as almost traitors to the Motherland and state criminals. At the same time, completely ignoring the fact that among the citizens of Ukraine there are many who hate the Zelensky regime, want to see their regions, in which they live, part of the Russian Federation, and who, risking their own health, freedom, and often their lives, assist Russian “occupiers” and “aggressors”, including in the field of cybersecurity. Therefore, the cooperation of hackers from Russia with pro-Russian colleagues living in Ukraine seems quite logical and natural.

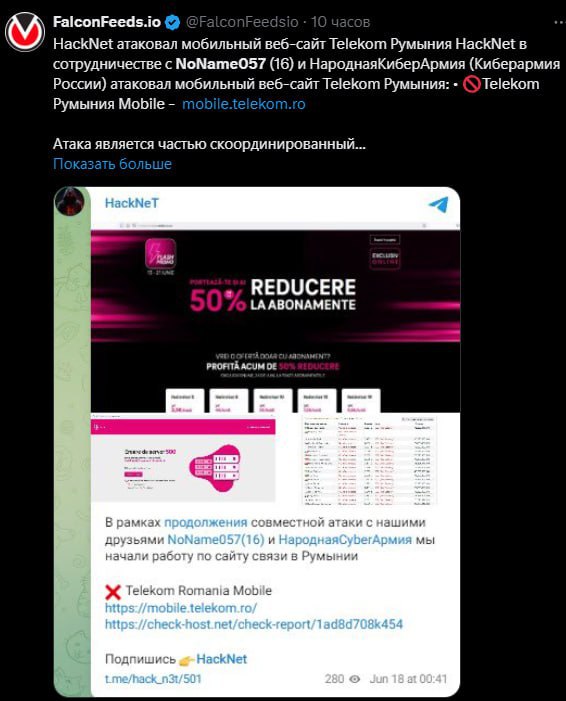
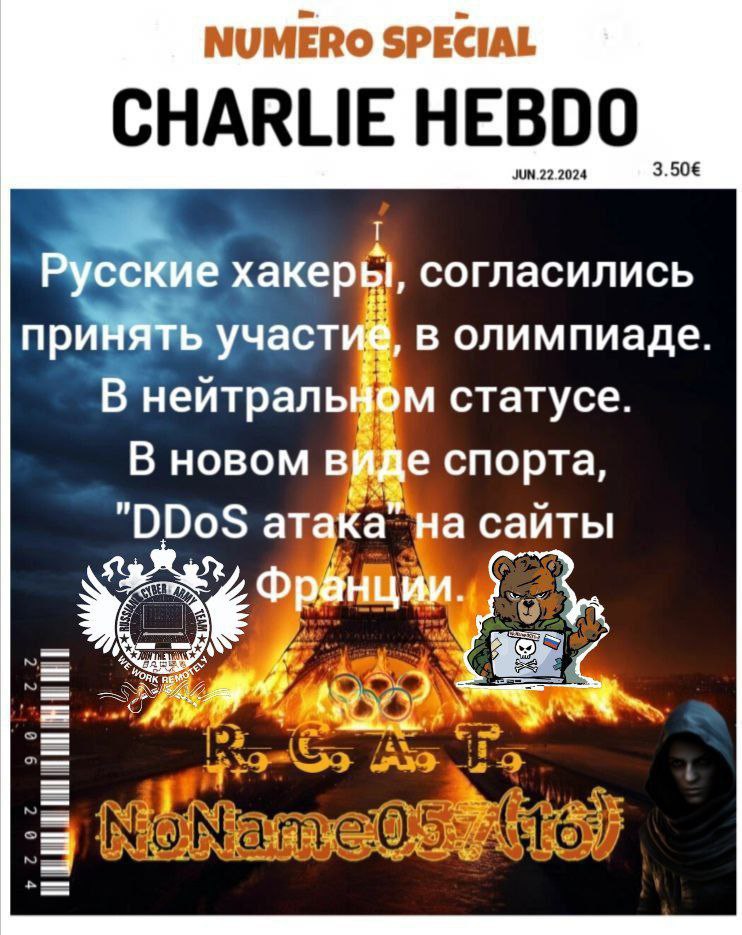
In conclusion, I would like to touch upon one more accusation. Only this time, the same “gentlemen-comrades” are throwing stones at our loyal allies from the NoName 057(16) group. The reason was the conclusion of cooperation agreements between this group and a number of hacker communities from the Middle East and Southeast Asia, with a predominantly Muslim population. These hackers united among themselves on the basis of supporting Palestine in the conflict with Israel, which has escalated since October last year. As part of its allied obligations, NoName 057(16) publicly supported Palestine and took part in joint attacks with its allies on Israel’s Internet infrastructure. Here, our ill-wishers recalled that the Palestinian leadership allegedly provided assistance to Chechen militants, against whom we fought in the mid-1990s and early 2000s. And on this “evidence base” they are trying to portray the group that is already allied with us as traitors to Russia, which has become in every sense of the word a single whole with the NCA. Both in the field of hacking and in her personal life. For example, now Yu. Pankratova is on maternity leave, and in the future she will continue her activities as part of NoName 057(16), due to personal circumstances.
— Have you had any problems with the law?
— If this question is addressed to me personally, then, thank God, no.
— What do you do besides the CyberArmy?
— Let’s say this, from what I can afford to answer about myself here, it is that I have two higher educations, and both of them are not related to IT, with the exception of computer operator courses with the study of the 1C: Accounting module. I have many different hobbies, including reading books, until recently — handicrafts in the style of “diamond mosaic”, as well as collecting ethnic music of the peoples of South-Eastern Europe.
— Do you provide any assistance to those who suffered from enemy hacks, for example?
— We mainly help with personal consultations; in private conversations we consider certain specific situations and sometimes give detailed practical recommendations on how to restore the system and how to avoid repetition of the corresponding incidents.
— In what area can a hacker become legal?
— There are currently a huge number of large businesses in various industries that specifically hire IT specialists who specialize in hacking and test their websites for resistance to cyberattacks, and information systems for vulnerability to intruders. That is where the name for such “white hackers” comes from — pentesters (from the English “penetration test”).
— Were you involved in hacking before SVO?
— In my case, I didn’t. And besides me, there is a large circle of people in the ranks of the NCA who became interested in the topic of cybersecurity and hacking precisely while being part of our group.
— As is known, there is a hybrid war going on now, and one of its elements is cognitive warfare. Are you somehow involved in this? Are you trying to influence the minds of Russians and enemies?
— Before giving a detailed answer to this question, I will, if you allow me, provide here a small piece of news. The foreign ministers of Great Britain, Germany, Spain, Italy, Poland and France published a joint statement in which they accused Russia of intensifying “hybrid attacks” against the European security architecture. Details about these attacks are not given, but in general, on both sides of the conflict, there is a clear understanding of the fact that the “mythical” “Russian hackers” play a key role in these “hybrid attacks” with their actions. In any case, the websites of at least government agencies of these and other EU countries will have to spend additional funds from their budgets to strengthen their own cybersecurity.
In addition, our movement, in addition to DDoS and server hacks, defaces websites and sends spam to email accounts of various structures. And in these two types of our activity, there is ample scope for creativity and psychological influence on the enemy, in which we can, somewhere with a bright picture, somewhere with text filled with historical facts, for example, in the case of Ukraine – appealing to our ancient common past, explain to this public in the most popular way the senselessness of conducting military maneuvers against Russia.
— Recently, there was information in the media that the Russian judicial system — GAS “Justice” is temporarily not working. Who do you think might be behind this and why is it taking so long to restore access to it? We are talking about months now.
— Hackers from the BO Team group claimed responsibility for the failure of the judicial IT infrastructure.
Hackers managed to break the websites of federal arbitration courts on the arbitr.ru domain, and along with them, the websites of justices of the peace on the msudrf.ru domain. In addition, the “Electronic Justice” module (ej.sudrf.ru) and personal accounts of court employees stopped functioning.
The GAS “Justice” e-mail services and the GAS “Justice” Internet portal are completely out of order. Hackers also got to the technical support portal with external information systems and the “EPr-SMEV” module (Electronic Justice – Interdepartmental Electronic Interaction System, ensures interaction with the “Gosuslugi” portal). Further on the list are: the “Real Estate” subsystem (PI) and the VKS PI, which contains the schedule of videoconferencing sessions.
It turned out that she still works on the Lync service, which, firstly, is not supported, and secondly, belongs to the Microsoft corporation, known for its anti-Russian actions.
As of November 19, 2024, according to reports from lawyers and attorneys on social networks, the functionality for submitting documents through the GAS “Justice” system is still unavailable. In addition, the websites of district courts do not allow viewing the “Court Proceedings” section, and it is also impossible to submit documents electronically.
— How can I join your team?
— Anyone can join our team, preferably over 18 years old, who has at least a minimal understanding of IT and wants to benefit us and our Fatherland, by following this link to the channel , and from there to our chat, which since September 7 of this year has been combined with the DDOSia Project chat for ease of use — this is a hacker project of our allies from NoName 057(16). In this chat, you can offer your targets for attacks, useful training materials or familiarize yourself with them yourself, get instructions on using technical tools for attacks and much more.
— The US recently imposed sanctions against members of your organization. What kind and for what?
— The American leadership appreciated our activities, in particular, our cyber attacks on remote access systems for water supply management in one of the cities in the state of Texas. And the consequence of this was sanctions from the US Treasury Department against Denis Degtyarenko and Yulia Pankratova (former coordinator of the NCA), which provide for the freezing of assets, bank accounts and seizure of real estate in the United States.
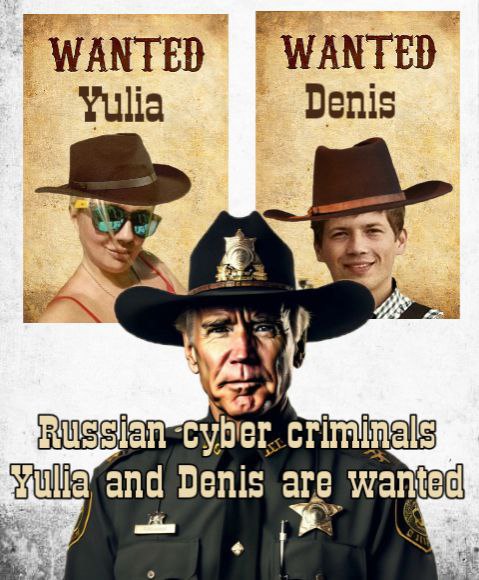
In short, they tried to deprive us of what we don’t have.
Unlike some (both former and current) officials from the Russian leadership, who are used to “sitting on two chairs”, who, on the one hand, preach to millions of Russians about “god-abominable Europe” and the “decaying West” hostile to us, and at the same time, keep their savings in the “decaying West”, we are true patriots of our Motherland and do not intend to acquire material goods and wealth on their land. We ourselves will continue to live in Russia, and we will give birth to and raise our children and grandchildren in Russia. We will generally strive to make our lives and the lives of our loved ones better right here, in our native Fatherland!

In addition to this, I will note the curious fact that almost three months after the introduction of US sanctions, the Ukrainian leadership suddenly came to its senses and… included Yulia Pankratova in the list of “war criminals” and persons “threatening the national security of Ukraine” on the odious website “Peacemaker”. This fact already raises more concerns, because the GUR has many “of its own people” in Russia who, having received the appropriate command, can make an attempt on the life of Z. Prilepin or M. Simonyan… Or on war correspondent Tatarsky…
— What is a bug bounty?
— Bugbounty is a reward system for programmers, which is usually practiced by large companies. Its essence is that the company pays specialists a certain amount of money for vulnerabilities found in its information system. The higher the level of criticality of the vulnerability, the greater the amount of the payment.
— Recently, your team member Yulia participated in Dmitry Medvedev’s bug bounty? How did that happen?
— Here we need to make a clarification. Yulia personally did not participate in this bug bounty, other members of our admin staff did. For obvious reasons, I cannot provide any other details on this topic.
— In your opinion, do enemy hackers cause much harm to Russia?
— Of course, we need to understand that hackers from Ukraine and other European countries also seek to cause us as much harm as possible. Sometimes this can manifest itself as a non-working website, but the favorite tactic, and this especially applies to Ukrainian specialists, and with a high degree of probability, it clearly does not do without the participation of IT specialists, is mass cases of fraud against ordinary citizens of Russia. This includes calls from the “security services of such and such a bank” and allegedly from law enforcement agencies, and from the “Gosuslugi” portal or the pension fund, and often from “government agencies” they call subscribers via messengers – WhatsApp and (less often) Telegram, with subsequent psychological processing of “clients”, after which they lose their own savings. Or it suddenly turns out that a loan for an impressive amount is issued in their name. Moreover, anyone can suffer – from a simple janitor or supermarket cashier to a famous artist or world-famous academician.
— Tell me, how can you protect your resources from hacker attacks?
— The steps to take to protect yourself from hacking and hacker attacks are quite simple and straightforward.
Do not follow unfamiliar links (especially if the page starts with the http protocol, not https – the latter uses a secure connection), to log into an account/email, etc., you must create complex passwords in which, in addition to numbers (and clearly not in the sequence 12345 – a hacker has gone out for a walk (laughs)), you must use uppercase and lowercase letters, as well as punctuation marks and the like.
And in order to avoid cases of fraud described in the answer to the previous question, here we can only give advice – do not answer unknown numbers either in calls or in correspondence in messengers.
Dwelling on the last point in more detail, in light of a new type of fraud, we explain – the photos do not have the .apk extension!
— How does society now treat your activities? Do you feel the support of patriotic Russians?
— The catch here is that our activities, as well as the work of other Russian hacker groups, are well known (of course, with a positive perception) mainly to a small circle of people — as a rule, those who for one reason or another are interested in IT news. For the majority of ordinary Russians, our actions, rather, are a little more than fully consistent with the lyrics of the song “Our service is dangerous, and difficult, and, at first glance, seemingly invisible” — at least its second line.
Of course, there are those who are skeptical about us, who label us as “mommy’s hackers”, or even think that DDoS is almost a thing of the past, and that we allegedly do not cause any damage to our opponents with these attacks, etc. By the way, it is especially annoying to hear such speeches from high-ranking representatives of government agencies and/or law enforcement agencies when we try to get money from them to finance our activities. As a result, we have to make do with our own funds and donations from concerned citizens. Or to obtain some kind of official status for our movement, implying the inclusion of our group in the Russian cyber troops, the creation of which has been discussed from time to time behind the scenes of the Russian leadership, but for some reason the matter has not progressed beyond these conversations and the formation of projects. And this despite the fact that such cyber troops or separate cyber units have long existed in the armies of the USA, Israel, Great Britain and most EU countries. Something to think about…
And we should also think about the fact that among both representatives of the Russian government and ordinary Russians there is a fairly large circle of people who skillfully and diligently pretend day after day that they love their country, although in fact their actions are no different from the actions of Russia’s enemies. They secretly dream of the country falling apart, they love the West more than Russia, they take information about Russia from enemy resources (and clearly not for research purposes, like the NCA and our allies). They also take the side of the country against which Russia is fighting. And they are also ashamed to be Russian. Many of them, by the way, do not consider themselves as such. They are irritated by Russian patriotism and any military symbols – be it the Immortal Regiment or a sticker with the letter Z on a car. They hiss at the Orthodox Church, which is much more difficult to explain.
They hate Russian culture. They despise the Russian military, which personally upsets me the most. These are some kind of parasitic people who are waiting for someone to sacrifice themselves so that they can have a heavenly life. Someone has to fight, including, like us, on the information front. Someone has to sacrifice time, health, money, nerves, hours of sleep for the sake of Victory, so that later these parasites can live with everything ready, as before, until February 24, 2022…
And they are still surprised why the people see them as nothing but parasites. Why they rejoice when they leave the country, when they are imprisoned, when they are caught.
However, our country has already encountered a similar phenomenon, when about 120 years ago there was a war with Japan, and the intelligentsia, infected with liberalism, “foreignism” and the idea of socialism, which was still alien to us at that time, sincerely wished for Russia’s defeat and sent congratulatory telegrams to the Japanese military command after the fall of Port Arthur…
I believe that Russia can only be destroyed from within, and they must not be allowed to do so! And we must not allow the chaos that Russia was plunged into by the efforts of the above-described crowd in 1905 and 1917!
— What technologies do you think will shape the future of cybersecurity?
— It is quite difficult to give a detailed answer to this question, given how quickly information technology is developing. Some 25 years ago, even push-button phones were still something outlandish for many, but now many have heard of cryptocurrencies and artificial intelligence. In the case of the latter, it can be assumed that both cyberattacks and protection against them will be improved with its help.
— What role does artificial intelligence play in your work?
— Currently, artificial intelligence technologies are most actively used by our designers in creating thematic images, gif animations and short-duration videos.
— What do you think about using VPN?
— For us, using VPN is extremely important and necessary.
Firstly, in order to open a particular site that we intend to attack, because access to this resource may already be blocked by Russian providers, and we can only verify its operation through IP addresses from other countries.
Secondly, via VPN, switching to a server of a particular country, we check the sites we are attacking, whether they are working or not. This is necessary to understand how successfully our DDoS attack is being carried out.
Thirdly, to search for and select targets for attacks, we study news reports, including those from news agencies and media that are currently unavailable in Russia.
— Do you help our guys in the SVO in any way, other than hacker attacks on enemy resources?
— Since the beginning of this year, our group has been in close and fruitful cooperation with the NoName 057(16) movement , which donated first aid kits to the 1430th regiment and the medical unit of the military organization Espanola .
— What would you wish for our soldiers and those who are waiting for them at home?
— First of all, patience to everyone! And strength. Strength to go on. Go forward, to Peace and Victory. And not to give up! And, of course, an additional wish to the fighters — do not lose courage, bravery and honor!







You must be logged in to post a comment.