#go
Go-exploit is an exploit development framework in the Go language. The framework helps exploit developers create small, portable exploits. The framework was designed to simplify mass scanning, exploitation, and integration with other tools.
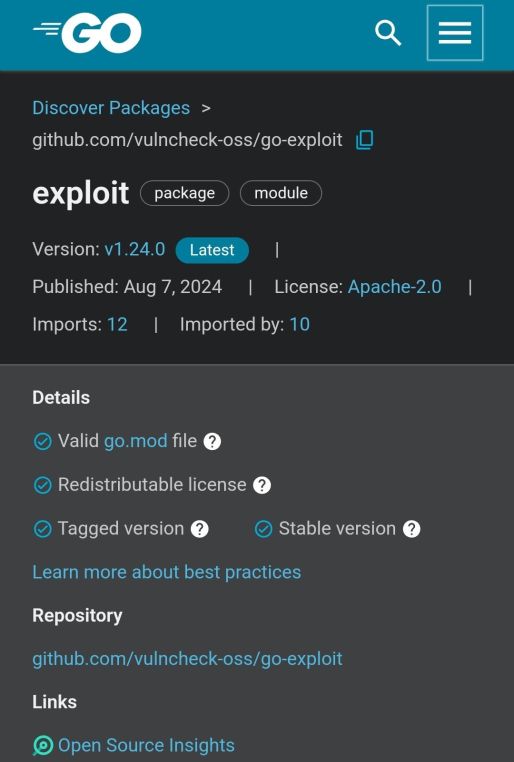
API documentation can be found HERE .
The Go Exploit framework includes the following steps, which can be linked together or executed independently:
Step 1 – Check the target
Step 2 – Scan the version
Step 3 – Operation
Step 4 – Management and Control
Features of Go Exploit
The Go Exploit framework includes the following additional features:
➡️ Automatic SSL/TLS detection on remote target.
➡️ Full support for working through proxy .
➡️ Output in key-value or JSON format for easy integration into other automated systems.
➡️ Built-in Java gadgets , classes and LDAP infrastructure.
➡️ Lots of payloads for reverse shells , droppers and bind shells .
➡️ Features that integrate exploitation with other tools or frameworks, such as Metasploit and Sliver.
➡️ Built-in C2 for intercepting encrypted/unencrypted shells or placing implants.
➡️ Support for various target formats including lists, files, VulnCheck IP-Intel and others.
My opinion about this tool : it’s still raw and not enough, BUT I see potential in this tool and maybe someday it will take off or get a bunch of “bindings” that will make this tool a fully combat one.



You must be logged in to post a comment.