What is Predator-os v3.1 – 06-26-2024
Polymorphic Security Platform
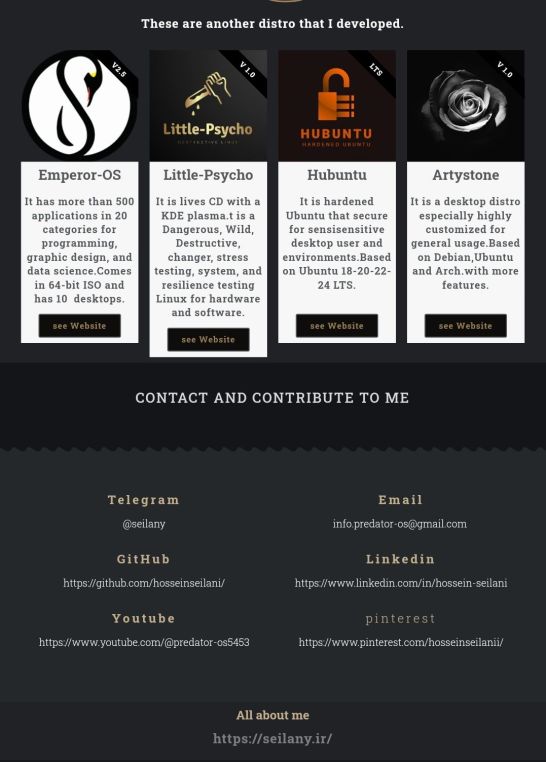
It was developed in 2021 by Hossein Seilani, who is also the developer of https://emperor-os.ir/ Linux. Predator-OS is a free and open-source community project, emphasizing freedom.


The distribution is designed for Penetration testing, Ethical hacking, privacy, hardening, and secure, anonymized Linux.
Predator Linux is based on Debian Stable, with kernel 6.6.15. Fully customized Plasma desktop with a specialized menu of tools.
Predator Linux comes with approximately 1200 pre-installed tools in 40 different categories and 9 modes.
These tools have been sourced from both Debian repositories, and GitHub pages.
Most kernel and user configurations are customized by default to prevent hacking attempts and non-privileged access and reduce the attack surface.
Additionally, numerous built-in firewalls and defensive tools enable end-users to have control over the Predator-OS. Predator also supports various privacy, anonymization, and security tools, and can be run as a live CD or from a USB Drive, as well as in installation mode.
Included in more than 2 TB (Online + Offline) password lists.
Included in more than 500 lists of Red and Blue team tools.
Included in more than 200 lists of AWS cloud tools.
Included in Web3 security tools.
Included in more than 10 sets of roadmaps in cybersecurity.
Included in more than 100 search engines for security and penetration testing.
Included in more than 300 educational scripts for security and penetration testing.
Included in more than 100 security training websites and penetration testing resources for kids.
Included in more than 10 tools for running a cybersecurity lab and conducting penetration testing.
Included in more than 40 websites for running a cybersecurity lab.
Included in the source of 800 malware files, divided into 80 different groups (400 MB file).
Included in 1000 websites for OSINT (Open
source intelligence).
Included in more than 70 online and self
reading websites in cybersecurity.
Included in more than 11 offline and self
study training categories in cybersecurity.
Included in 600 forensic and reverse engineering tools.
Included in more than 6000 Google dorks and exploits as offline resources.
More Features:
1) Includes many boot grub parameters both in live and after installation.
2) Disables many unnecessary services and loggers during the boot-up.
3) Allows the kernel to automatically proceed without prompting the user for any input.
4) Improves and includes security features that protect against certain types of attacks.
5) Improves and includes performance tuning features for low latency behavior of the system.
6) Automatically detects other operating systems installed on the system and adds them to the GRUB boot menu.
7) Changes to the calamares installer instead of the default ubiquity installer.
8) Provides easy installation and better user-friendly tools and environment.
9) Suitable for newbie users and useful for general work compared to Parrot and Kali distribution.
10) Includes the best privacy, hardening, anonymous configuration, and tools.
11) Offers a lighter and smaller download file size, despite having more tools than BlackArch, Tsurugi Linux, and dracOS Linux distributions.
12) Has the ability to boot both in live mode and for installation, unlike deft, Discreete Linux, despite having all the tools of that distribution.
13) Includes the feature of booting in safe-mode, text-mode, Noacpi, Iommu, forensic-mode, and having CLI tools like the dracOS distribution that lacks graphical tools.
14) Includes all Bugtraq Linux tools.
15) Includes more web penetration testing tools than Samurai Linux.
16) Includes more tools than BackBox Linux.
17) Includes all Pentoo Linux tools.
18) Includes specialized PC crime detection tools and also the ability to run Windows tools in Linux, such as deft and CAINE Linux.
19) Includes Kodachi Linux features in the field of privacy and anonymity.
20) Includes secure and privacy features of Discreete Linux.
21) Includes all Santoku Linux tools in the field of Mobile pentesting.
22) Includes the Whonix distribution features for more security and anonymity.
23) Includes all Attifyos Linux tools in the field of IoT penetration testing and even more with a user-friendly interface.
24) Includes all stressLinux tools in the field of stress testing and more.
25) Includes the features of anonymity on the web, such as IprediaOS distribution.
26) Includes many tools from the following site: insecure.org
SEE GALLERY
Plasma Desktop
– V 3.1 06-26-2024
– kernel 6.6.15
– AMD 64 bit
– 4G 770 MB
Gallery
Guide Book
Source Code
GitHub
MD5-SHA256
Post-installation Notes
Download ISO
default username:user
default password:user
default username:root
default password:user
Predator-os Updater
The predator-os has a default PPA repository and it has the predator-os-updater tool. you can run it from the application menu to get the last configs and updates of predator-os without installing it again or from scratch.
if you want to add the predator-os source list to old version,try this:
1) curl -fsSL https://www.seilany.ir/predator-os/KEY.gpg | sudo gpg –dearmor -o /etc/apt/trusted.gpg.d/predator-os.gpg
2) echo “deb [arch=$(dpkg –print-architecture)] https://www.seilany.ir/predator-os/predator-updater-ppa ./” | sudo tee /etc/apt/sources.list.d/predator-os.list




You must be logged in to post a comment.