ISIS was able to secure a highly sought after document detailing how to identify drones. The document (below), circulating on #Daesh social media channels and groups clearly puts the drones at risk of destruction. The perpetrators translated the artifact to Arabic, proudly distributing the stolen material.
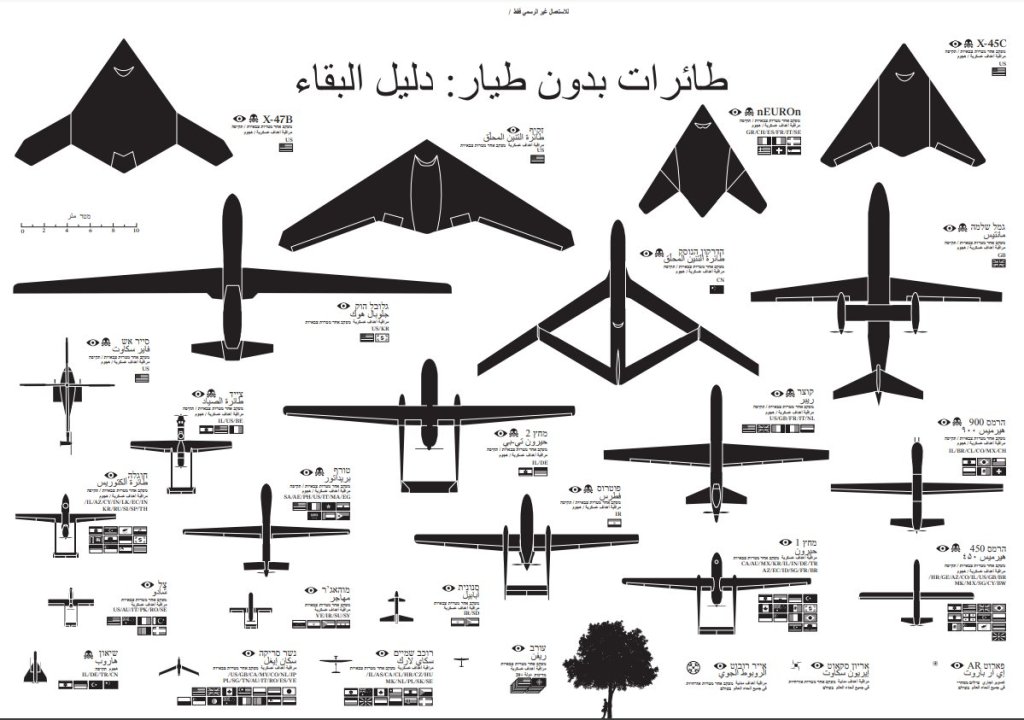
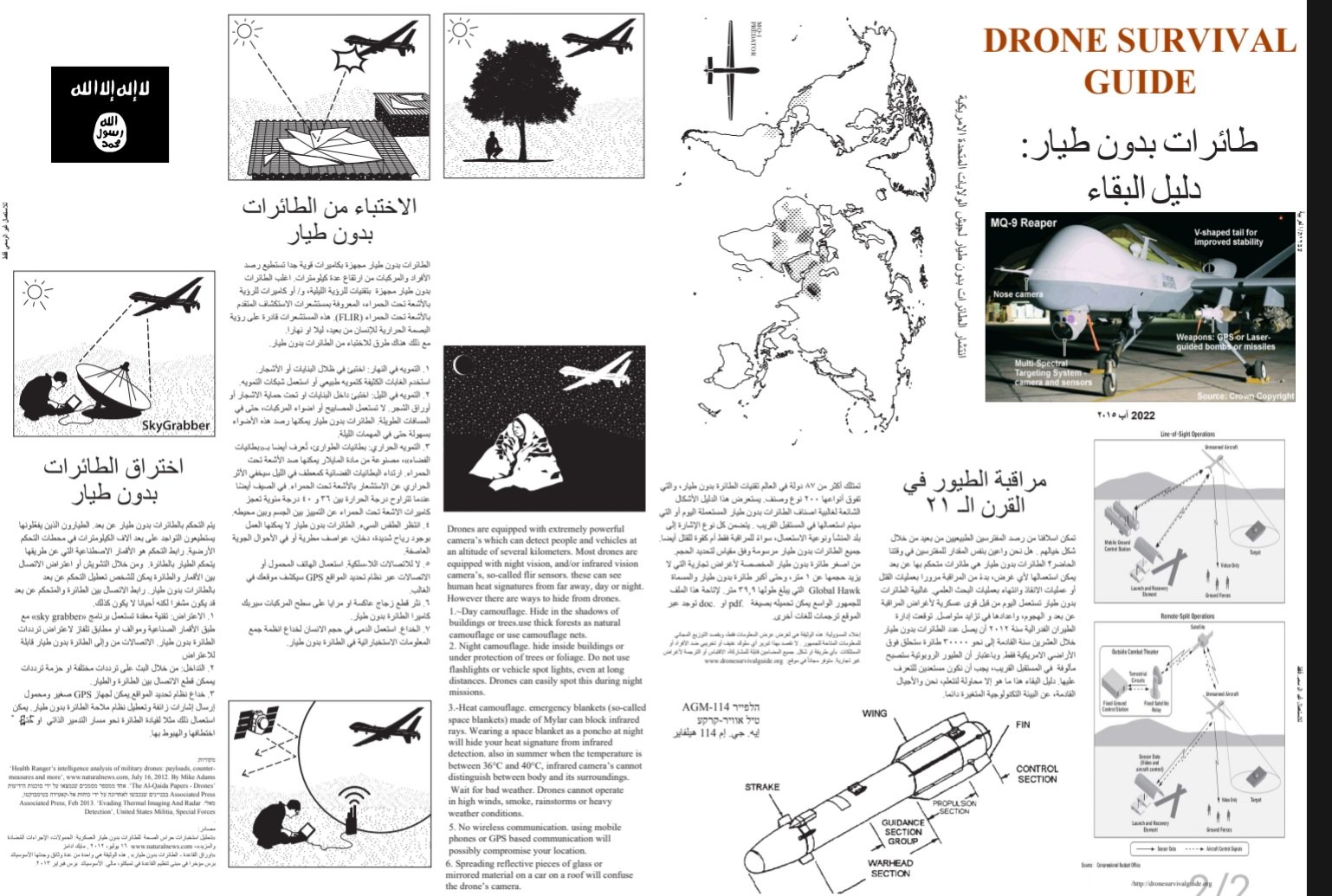
ISIS cyber capabilities have grown to the point where such documents are no longer safe. Stored behind extensive security, this document should be a wake up call for information security professionals charged with protecting sensitive data.






You must be logged in to post a comment.