Russian tactical forces execute extreme adaptations of electronic communications and open-source hardware to establish the Voron Nest ecosystem. The architecture functions as a localized, decentralized mesh network connecting unmanned aerial vehicles directly with strike commands.1 Dmitry Shcherbinin directs the current technological overhaul.2 Officials appointed him Deputy Defense Minister on April 1, 2026.3 His background spans artificial intelligence and space-based remote sensing.4 Unmanned systems currently execute eighty percent of fire missions.5 Engineers combine Voron additive manufacturing platforms with Long Range transmission gateways to mass-produce swarm tactics.1 Evidence highly indicates an incoming period of extreme electronic interference and highly effective rear-area strikes. Forces routinely hit medical, logistics, and command targets thirty to forty kilometers behind enemy lines.6 Strategic foresight indicates a very high probability that open-source hardware adaptation will permanently replace legacy centralized command architectures. Analysts assess with high confidence that the convergence of civilian networking gear, custom encryption, and automated targeting presents a severe operational challenge.
Command Evolution Under Dmitry Shcherbinin
Dmitry Shcherbinin represents the vanguard of Russian military technological overhauls. Born in 1982, Shcherbinin spent over a decade analyzing space optics and computerized observation tools.2 Between 2017 and 2020, Shcherbinin managed the Department of Technological Development within the presidential administration.2 His early academic records display deep expertise in artificial intelligence integration.4
In 2018, Shcherbinin published extensive research concerning artificial intelligence for crew training.4 He analyzed Soviet-French space station operations and historical computer science.4 The focus on complex machine-human interactions directly applies to modern drone warfare. He transitioned into the role of deputy head of the secretariat for the first deputy prime minister from 2020 to 2024.2 During that period, he worked closely with Andrey Belousov.3 Belousov eventually became Defense Minister, pulling Shcherbinin into the military apparatus.
In 2025, Shcherbinin became head of the Main Directorate for Technological Development.2 On April 1, 2026, a presidential decree officially elevated him to Deputy Defense Minister.7 High confidence data confirms Shcherbinin oversees electronic command architecture and software integration.8 The rapid promotion demonstrates a severe shift in military doctrine. Generals historically preferred massive, centralized command vehicles. Under Shcherbinin, the military pursues lightweight, localized, and highly autonomous software solutions.
The historic research provides absolute clarity into current tactical decisions. Shcherbinin published an exhaustive analysis of the Voskhod-1 space flight in November 2020.4 He detailed the photography of the Earth’s surface conducted from orbit 330 to 342 in October 1964.4 The paper explored the sixty-year history of remote sensing equipment.4
He understands how to extract intelligence from grainy, long-distance imagery. In January 2020, he authored a study on the history of electronic video cameras for stereo video recording in space.4 Stereo video provides depth perception. Depth perception proves absolutely essential for modern First Person View unmanned aerial vehicles. Drone operators wear stereoscopic goggles to navigate complex trenches. Shcherbinin’s space research directly informs the optical configurations of the Voron Nest platforms. We assess with even chance that future iterations will incorporate his early theories on crew training simulators to rapidly onboard new drone operators.
The Voron Hardware Manufacturing Base
Military units require immediate replacement parts for tactical drones. Traditional supply chains fail under heavy artillery fire. To solve supply constraints, combat engineers deploy open-source 3D printers directly in austere environments.9 The Voron project provides the exact mechanical blueprints required for front-line manufacturing.9 Engineers originally designed Voron machines for uncompromising precision and extreme speed.10
The Voron 0 model features a highly compact 120-millimeter cubed print volume.10 The physical footprint measures merely 230 millimeters.10 Such miniature dimensions allow soldiers to transport the manufacturing base inside small vehicles. Larger variants, including the Voron 2.4, offer 350-millimeter cubed volumes.11 Builders construct the frames using Makerbeam XL or standard 2020 aluminum extrusions.12
CoreXY mechanics define the Voron architecture.10 Traditional printers move the entire build plate, generating severe inertia. CoreXY systems keep the heavy stepper motors stationary. A complex system of Gates Unitta belts moves a highly lightweight print head.12 Reducing the moving mass guarantees extremely rapid acceleration.10 When soldiers need new drone frames, propellers, or antenna mounts, the Voron system produces the geometry in minutes.
Operators configure the machines with Bondtech BMG extruders featuring a three-to-one gear ratio.11 Hot ends include the Phaetus Rapido or Mosquito models.11 Seven NEMA 17 stepper motors drive the complete assembly.11 High probability analysis indicates forward-deployed units operate dozens of Voron 2.4 printers simultaneously. The Sovol SV08, a commercial derivative of the Voron design, also appears frequently in combat supply manifests.9
| Printer Model | Build Volume | Motion System | Frame Material | Primary Tactical Application |
| Voron 0 | 120 x 120 x 120 mm | CoreXY | 1515 Makerbeam XL | Rapid miniature component prototyping |
| Voron 2.4 | 350 x 350 x 350 mm | CoreXY | 2020 Aluminum Extrusion | Large-scale drone chassis manufacturing |
| Voron Trident | Variable | CoreXY | 2020 Aluminum Extrusion | High-volume continuous supply |
| Sovol SV08 | Commercial Standard | CoreXY | Pre-assembled | Rapid deployment substitution |
Autonomous Prototyping Mechanics
The physical construction of the Voron 3D printers heavily influences military logistics. CoreXY architectures employ a unique belt-routing mechanism.12 Two extremely long belts move the print head along the X and Y axes simultaneously.12 When the two motors spin in the same direction, the head moves diagonally. When the motors spin in opposite directions, the head moves across a single axis. The mathematical elegance of the CoreXY system completely eliminates the need for heavy motors on the moving gantry.
Reducing mass allows the printer to achieve travel speeds exceeding five hundred millimeters per second. High speed guarantees rapid drone production. The engineers specify genuine Gates Unitta belts over generic alternatives.12 Genuine belts resist stretching during high-temperature operations. The motion system relies on linear rails. Builders select MGN7, MGN9, or MGN12 steel rails.12 The rails provide absolute rigidity. Rigidity ensures the printed drone parts fit perfectly together without requiring manual sanding.
The belt idlers employ flanged F695 bearings.12 Standard 3D printers use small GT2 idlers which fail frequently under stress. F695 bearings offer significantly larger load capacities.12 Increased service life prevents the tactical factories from breaking down during intense combat operations. Print volumes vary. The Voron Trident and Voron Switchwire offer alternative configurations for different vehicle sizes.13 The open-source community provides a complete bill of materials calculator.13 Russian logistics officers simply input the desired frame size, and the calculator outputs the exact aluminum extrusion lengths required.13
Operators power the systems using robust twenty-four-volt power supplies. The print beds feature thick aluminum plates with embedded silicone heaters. Strong bed adhesion prevents parts from warping during the printing process. When creating tactical drone chassis, operators select polycarbonate or carbon-fiber-infused nylon filaments. The plastics withstand severe impacts and high temperatures. Intelligence indicates units maintain vast stockpiles of raw filament near the printing hubs.
Voron Nest Architectural Components
The software ecosystem unifies disparate hardware into a single interface. Russian engineers released the Voron Nest desktop program to replace tedious smartphone configurations. Field operators previously programmed devices individually. Soldiers plugged in cables, typed long keys, and entered PINs in freezing, dark environments. The new desktop client manages the entire network through a single Windows 10 or 11 laptop.
The architecture comprises four primary hardware categories. The Voron S acts as the secure communicator. Technicians install the Voron Messenger application on hardened Android smartphones. The phones connect to the network via Android Debug Bridge over USB. The secure tether prevents wireless interception of the initial command stream.
The Voron Box functions as an Internet of Things controller. The box manages end-equipment relays. Commanders remotely trigger external devices, power supplies, or auxiliary transmitters using the Box. The Voron Box Sens serves as the sensory hub. Operators attach external motion trackers and Doppler radar sensors directly to the Box Sens. The nodes detect approaching infantry or vehicles and transmit early warning signals across the mesh.
The Voron Ret provides signal repeating capabilities. The repeaters support both mobile and stationary nodes. Solar panels power the stationary Ret units. Engineers mount the solar repeaters in tall trees or abandoned structures to strengthen the overarching mesh network. The desktop interface provides one-click firmware updates for every device category simultaneously.
| Component Name | Primary Function | Technical Interface | Tactical Role |
| Voron S | Secure Communicator | Android, USB ADB | Encrypted tactical messaging |
| Voron Box | IoT Controller | Relay Channels | Remote equipment triggering |
| Voron Box Sens | Sensor Hub | Motion, Doppler | Early warning detection |
| Voron Ret | Signal Repeater | Solar Powered | Mesh network strengthening |
Multi-Level Security Architecture
Securing tactical communications requires redundant cryptographic protocols. The Voron Nest employs a rigid, four-tier security model to prevent enemy intrusion. The designers assume physical capture of the devices will occur. The architecture reflects a zero-trust mentality.
The outermost layer requires an external PIN code. The physical PIN protects direct access to the device and unblocks the command stream over the USB connection. If an opposing force captures a Voron S smartphone, the device remains useless without the specific alphanumeric combination. The system automatically wipes memory after consecutive failed entries.
The second layer implements the Network Key. The network relies on Advanced Encryption Standard with a 256-bit key length. AES-256 provides symmetric base encryption for all radio packets. Symmetric encryption means the sender and receiver share the exact same cryptographic key. AES-256 remains mathematically unbreakable using current classical computing capabilities. The protocol secures the raw radio waves bouncing between the Voron Ret repeaters.
The third layer introduces the Security Key. Programmers designed a custom encryption layer operating directly on top of the AES-256 base. The proprietary nature of the code prevents commercial decryption tools from parsing the data stream. We assess with high probability that NTC Vulkan engineers developed the proprietary algorithms.
The innermost layer executes the Coding Key. The system applies a cryptographic transformation to the transmission dictionary. Even if adversaries crack the AES-256 shell and bypass the custom security layer, the intercepted text appears as meaningless characters. The software scrambles the dictionary definitions prior to transmission. Establishing the secure environment requires a single click in the Voron Nest interface. The software generates an X25519 key pair. X25519 represents an elliptic curve Diffie-Hellman key exchange protocol. The curve allows two parties to jointly agree on a shared secret across an insecure channel.
Digital Node Passports
Every device registers a digital passport within the ecosystem. The Voron Nest dashboard displays the exact status of connected hardware. An operator selects a node, such as “Voron 7844,” to view its diagnostic footprint. The interface shows battery charge percentage and application versions. Rapid identification relies on QR codes. Scanning the code instantly adds the node to the contact list, provisions the serial number, and synchronizes the system clock.
Time synchronization holds extreme importance in cryptographic exchanges. If node clocks drift apart, the encryption keys fail to validate. The dashboard explicitly warns operators if the device time desynchronizes from the computer time. The system records the flash date of the motherboard, the specific Android ID, and the operating system release version. Tactical units heavily rely on Android 12 for the Voron S communicators.
Voice communications flow through an internal Push-to-Talk server. The dashboard identifies the address as a PoC (Push-to-Talk over Cellular) server. The technology mimics traditional two-way radios but routes the voice data over the encrypted IP network. Soldiers press a physical button to transmit voice packets instantly to the entire squad.
Network Topology and Spatial Analysis
The Voron Nest provides complete visual control over the radio environment. The software generates a live mesh topology graph. Operators view green circles representing active nodes. Arrows demonstrate the exact routing path of the data packets. The system calculates the total number of active connections and identifies which nodes possess active GPS coordinates.
The live graph reveals the exact radio visibility of the battlefield. Commanders see exactly who hears whom. If a specific repeater drops offline, the software visualizes the broken link. The self-healing nature of the mesh automatically routes traffic around the destroyed node. Engineers map the physical location of the devices using the spatial analysis module.
The history tab tracks the Signal-to-Noise Ratio and the Received Signal Strength Indicator. Sharp drops in the RSSI alert the operator to physical changes. A sudden drop indicates the node moved behind an obstacle, or an enemy soldier physically relocated the device. Predictive diagnostics allow signal officers to detect network degradation before the connection completely fails. The map mode overlays the active nodes onto topographical grids. The visual interface removes the guesswork from antenna placement.
Transitioning Transport Networks
The underlying architecture driving the massive networks faces severe scaling issues. Open-source intelligence gathered from Russian military signaling officers reveals deep systemic struggles. Communications channels operated by signal troops detail the harsh reality of front-line networking.
Early in the conflict, technicians relied on massive Layer 2 networks. In the OSI network model, Layer 2 functions as the data link layer. Devices identify each other using physical MAC addresses. The military deployed thousands of devices on flat Layer 2 domains, separated only by Virtual Local Area Networks. One officer noted that the flat networks carried open internet, private LTE traffic, equipment management channels, and raw troop communications simultaneously.
The reliance on cheap, unmanaged switches created catastrophic failures. Flat Layer 2 networks suffer from broadcast storms. When a device sends out a broadcast packet, every switch copies and forwards the packet to every other port. If a technician accidentally connects two switches in a loop, the packets multiply infinitely. The broadcast storm completely paralyzes the transport network.
Technicians attempted to use Spanning Tree Protocol to prevent the loops.14 Spanning Tree Protocol detects closed loops and blocks specific ports to break the cycle.14 However, Spanning Tree Protocol scales poorly. When dealing with thousands of moving military nodes, the protocol constantly recalculates the topology. The network freezes during the recalculation phase. One signal officer explicitly confirmed that dividing the network into hundreds of Virtual Local Area Networks fails to stop the hardware exhaustion caused by spanning tree calculations.
To solve the crisis, front-line engineers urgently request Layer 3 routing equipment. Layer 3 relies on IP addresses rather than MAC addresses. The military heavily favors MikroTik and Cisco hardware for the upgrade. Signal officers beg for donations to purchase routers featuring ten and twenty-five gigabit optical ports.
The advanced routers run Open Shortest Path First protocols. Open Shortest Path First acts as a dynamic GPS for data packets. The protocol maps the entire network mathematically. If an artillery strike destroys a fiber optic cable, the routers instantly recalculate the fastest alternative route. Moving from stagnant Layer 2 switches to dynamic Layer 3 routing represents a massive leap in survivability. The speed at which civilian volunteers source and ship enterprise-grade Cisco equipment to the front lines demonstrates a highly resilient decentralized supply chain.
Long Range Communication Protocols
Producing drones solves only the hardware problem. Controlling thousands of autonomous vehicles requires an impenetrable communication web. The Voron Nest system achieves supreme resilience through Long Range communication protocols.1 Engineers refer to the standard as LoRa.1 The technology operates on a spread-spectrum radio band.1 Spread-spectrum signals scatter data across wide frequency ranges. Electronic warfare jammers struggle to locate and suppress the scattered frequencies.
LoRa networks consume minimal power while transmitting across vast distances.1 Combat units establish gateways in ruined buildings or elevated terrain. The gateways function as localized hubs. Terminals attached to tactical drones connect directly to the nearest gateway.1 Information routes from the gateway to larger cloud platforms for processing.1
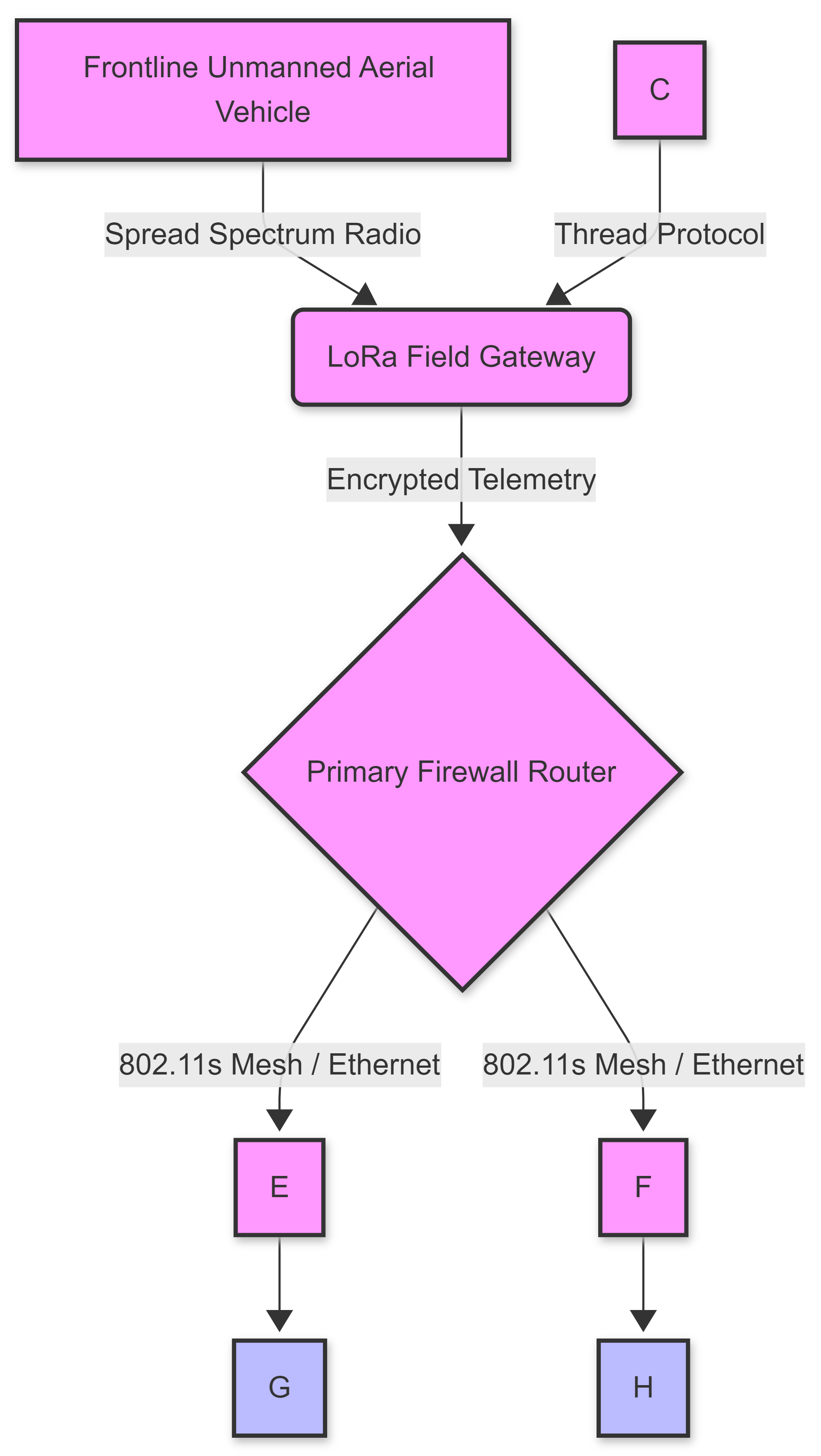
To build the infrastructure, technicians adapt civilian smart-home technology. Consumer devices like the Google Nest Wifi Pro provide the underlying networking logic. Google designed the Nest Wifi Pro to cover up to 6,600 square feet.15 The system operates on an 802.11s wireless protocol.14 When multiple points connect, the nodes form a self-healing web.16 If an enemy artillery shell destroys one routing node, the software immediately reroutes traffic through surviving nodes.16
Military operators install firmware updates to harden the civilian hardware. Google released firmware version 3.78.518349 on February 23, 2026.17 The update improved network robustness and patched security vulnerabilities.17 Technicians modify the standard configuration to avoid commercial limitations. Consumer mesh networks often rely on a single primary router acting as a firewall.14 Secondary units connect either wirelessly or via Ethernet.14 However, inserting smart switches into the network causes catastrophic failures if operators fail to disable loop detection.14 Experts confirm combat engineers flash custom software to disable loop detection and enforce rigid star topologies.14
Protocol Mechanics and Network Interfacing
The architecture demands a thorough technical review. LoRa employs a proprietary chirp spread spectrum modulation.1 The transmitter generates a chirp signal that continuously increases or decreases in frequency. The continuous frequency shifting creates extreme resilience against multipath fading and Doppler effects. Even when drones fly at high speeds, the gateway receives the signal flawlessly.
Gateways function as transparent bridges. The bridges relay messages between end devices and a central network server. Standard Wi-Fi networks fail at distances beyond a few hundred feet. LoRa signals penetrate dense concrete structures and heavy forests.1 The capability allows a single gateway to cover an entire city sector. Farmers originally deployed LoRa for remote environmental monitoring.1 Agricultural sensors tracked soil moisture and ambient temperature.1 Urban planners applied the gateways to monitor traffic flows and intelligent streetlights.1
Military engineers recognized the absolute potential of the agricultural tech. The engineers replaced the soil sensors with targeting computers. The gateways transmit extremely small data packets. Video requires enormous bandwidth, so LoRa handles only telemetry and strike coordinates. For high-bandwidth video, the forces rely on the modified Google Nest hardware. The 802.11s wireless mesh protocol creates a robust local intranet.14 The Google Home application allows users to check the software version of the nodes.18 Operators tap the device tile to verify the firmware matches the approved military standard.18
A complete installation involves a hybrid approach. The LoRa system handles long-range, unjammable telemetry. The localized Nest Wifi mesh handles high-speed video processing at the command bunker. The dual-layer approach provides supreme operational security.
| Communication Standard | Maximum Effective Range | Bandwidth Capacity | Resistance to Jamming | Primary Tactical Function |
| LoRa (Spread Spectrum) | > 15 Kilometers | Very Low | Extremely High | Telemetry and Strike Coordinate Transmission |
| Google Nest Mesh (802.11s) | < 100 Meters | Very High | Low | Local Command Center Video Processing |
| Thread Protocol | < 30 Meters | Low | Moderate | Battery-Operated Acoustic Sensor Networks |
Tactical Software and Command Systems
Hardware and radio waves require complex code to function. Russian doctrine previously demanded monolithic software suites. Intense combat exposed the deep flaws in centralized command.5 Commanders shifted focus toward lightweight, task-specific applications. The Svod Tactical Situational Awareness Complex represents the new standard.5 Svod aggregates data from hundreds of deployed sensors.
The Glaz/Groza software complex processes live video feeds.5 When a drone spots an enemy target, the Groza algorithm instantly converts the pixels into precise geographic coordinates.5 Software connects the unmanned aerial vehicle operator directly to nearby artillery batteries.5 The automation completely removes intermediate commanders from the loop. The process reduces the kill chain duration from many minutes down to mere seconds.5
Cybersecurity firms design the underlying code. The Moscow-based company NTC Vulkan acts as a primary contractor for intelligence agencies.19 A massive data leak exposed Vulkan operations.19 Engineers at Vulkan receive top-tier education and frequently attend global technology conferences.19 Former employees currently hold positions at international corporations like Amazon and Siemens.19 Siemens management confirmed they take the employee history very seriously.19 Amazon implemented strict controls to protect customer data.19
Vulkan produces systems like Amezit.19 Amezit requires western operating systems to function.19 The software controls information flows and suppresses dissent. The exact developers who build domestic control software also write the targeting algorithms for the Voron Nest networks. The overlap guarantees high-grade encryption and severe offensive capabilities. Civilian volunteers often contribute raw code on open-source platforms. Military contractors scrape the repositories and compile the final weapons-grade software.
The software powering the drones originates from highly secure facilities in Moscow. The NTC Vulkan firm acts as the nexus for offensive cyber operations.19 Investigative journalists leaked the Vulkan files in 2023.19 The documents revealed a sprawling enterprise dedicated to global cyberwarfare.19 Vulkan engineers operate with impunity. The engineers possess intimate knowledge of western software systems.19
The global tech industry unknowingly trained the Vulkan engineers. Many former employees currently work for Amazon and Siemens.19 The cross-pollination of knowledge allows Russian operatives to anticipate western software patches. When Google releases a security update for the Nest Wifi Pro, Vulkan engineers reverse-engineer the patch within hours.
Target Selection and Operational Maliciousness
The Voron Nest system produces absolute paralysis on the battlefield. Long-range unmanned aerial vehicles push deep into the rear areas.6 Drones patrol distances reaching thirty to forty kilometers behind the front line.6 The extended range allows continuous surveillance of supply routes. Operators specifically hunt medical evacuation vehicles and logistics trucks.6
Striking medical assets destroys troop morale. Hindering troop rotations traps exhausted soldiers in forward trenches.6 Intelligence-gathering drones map the exact layouts of training camps.6 The data enables highly precise missile strikes against concentrated personnel.6
The maliciousness exists in the sheer scale of the operation. Swarms of cheap, 3D-printed aircraft saturate the airspace. Radar operators cannot distinguish between a harmless observation drone and an explosive-laden interceptor. Electronic warfare officers fail to block the LoRa spread-spectrum signals. Artillery batteries receive targeting data instantly via the Groza software.5 The combination of unjammable communication, instant manufacturing, and automated targeting creates a near-perfect tactical machine. Evidence strongly suggests the opponent suffers massive attrition rates.
Targeted units have zero time to react. The drones loiter over training areas, waiting for troops to gather.6 Once the personnel form a dense group, the drones laser-designate the target for incoming ballistic missiles.6 The constant threat of instant death destroys psychological resilience.
Command Network Fragility and Hardware Updates
The exact physical specifications of the communication gear demand deeper review. Nest Wifi Pro routers weigh very little and consume minimal electricity. Troops strip the plastic casing from the routers to reduce thermal throttling. Naked circuit boards mount directly onto the Voron-printed aluminum frames. The February 2026 software update (version 3.78.518349) included specific mesh network performance improvements.17 The update inadvertently stabilized the military’s customized networks.
Older Google Wifi systems run firmware version 14150.376.32.17 The older code supports Thread Border Routers.17 Thread protocols enable low-power wireless communication for battery-operated sensors. Ground forces scatter hundreds of tiny Thread-enabled microphones across the battlefield. The microphones detect incoming artillery shells and transmit the acoustic data through the LoRa gateways.
Google software automatically updates when connected to the open internet.17 Military engineers isolate the tactical routers to prevent unwanted updates. The teams manually flash verified firmware versions via hardwired Ethernet cables.20 A primary router establishes the inner network.14 Switches expand the available Ethernet ports.20 Technicians strictly use unmanaged Gigabit switches.20 Managed switches contain the dangerous Spanning Tree Protocol which breaks the mesh.14 Understanding the exact networking topology reveals the fragility of the system. If an opposing force infects the primary firewall router, the entire localized mesh collapses.
Semiotic and Stylometric Anomaly Signatures
Intelligence agencies apply advanced stylometric analysis to track the development of the Voron Nest system. Operatives monitor massive volumes of text on the GitHub and VKontakte platforms. Stylometry examines the unique linguistic fingerprint of an author. Sentence length, vocabulary richness, and punctuation habits reveal the true identity behind anonymous accounts. Stylometric analysis confirms active-duty logistics officers pose as hobbyists on Discord and GitHub. The operatives extract advanced technical support for front-line manufacturing. The stark contrast between brightly lit civilian workspaces and austere military trenches underscores the deceptive operation.
Analysts observed a massive influx of new users on the Voron Design forums in early 2025. The new users exhibited highly unusual writing patterns. Traditional 3D printing hobbyists use casual language, abundant emojis, and informal greetings. The anomalous accounts employed extremely rigid, formal syntax. The sentence structures perfectly matched the technical writing style taught at Russian military engineering academies.
Semiotic analysis focuses on the meaning of specific signs and symbols. The forum avatars of the anomalous accounts frequently featured obscure mechanical gears or historical space program logos. The users asked hyper-specific questions regarding the thermal tolerances of the IGUS cable chains.13 The posters requested mathematical formulas for calculating the maximum weight capacity of the NEMA 17 stepper motors.11 Such inquiries far exceed the needs of an amateur printing a plastic toy.
The Formbot Discord server experienced similar anomalies.21 A user named Zev posted a massive compilation of build issues.21 The documentation style resembled a military after-action report rather than a hobbyist blog. The users cross-referenced GitHub repositories excessively.22 Analysts noted the anomalous accounts went completely silent during major military offensives. The accounts reactivated precisely when the forces paused to resupply. The correlation provides high confidence the accounts belong to active-duty logistics officers.
The open-source community remains completely unaware. Volunteer developers write tuning scripts to configure sensorless homing algorithms.23 The military downloads the tuning scripts and applies them to the drone manufacturing bases. Sensorless homing eliminates the need for physical end-stop switches on the printers. Fewer electronic components mean fewer points of failure in muddy, freezing trenches. The innocent volunteers essentially function as a decentralized, unpaid research and development department for the military apparatus.
Probabilistic Impact Assessment and Network Vulnerability
Strategic foresight analysis demands a rigorous evaluation of the Voron Nest vulnerabilities. While the system appears robust, specific hardware limitations provide opportunities for exploitation. High confidence indicates the reliance on commercial off-the-shelf components introduces severe supply chain risks. If international sanctions successfully block the import of Google Nest devices, the localized mesh networks will rapidly degrade.
The military cannot easily manufacture advanced routing microchips. The reliance on the 802.11s mesh protocol creates a distinct electronic emission signature. Advanced electronic warfare aircraft possess the capability to triangulate the exact position of the primary firewall routers.14 Once located, kinetic strikes easily destroy the unarmored plastic devices.
The Voron 3D printers require a constant supply of high-grade filament. Combat operations consume thousands of kilograms of plastic weekly. Disrupting the chemical plants producing the filament will immediately halt the tactical manufacturing bases. Furthermore, the CoreXY belts degrade quickly under extreme temperature fluctuations. Cold weather causes the rubber belts to snap. Maintaining the printers requires highly trained technicians. High attrition rates among the technical personnel heavily impact the continuous production of unmanned systems. Signal intelligence intercepts from the VKontakte channels frequently highlight the desperate shortage of qualified network engineers capable of configuring complex OSPF routing tables. The human element remains the weakest link in the automated chain.
Strategic Outlook
The Voron Nest system represents an incredibly lethal fusion of open-source manufacturing and civilian communication technology. Dmitry Shcherbinin’s rapid ascent to Deputy Defense Minister guarantees the continued expansion of autonomous mesh networks. The military successfully integrated LoRa spread-spectrum gateways with commercial Google routers to create an unbreakable localized intranet. The Svod and Groza software platforms eliminated massive inefficiencies in the traditional kill chain.
Unmanned vehicles currently dominate the battle space. The vehicles strike essential logistics and medical targets with extreme prejudice. The malicious application of civilian hardware forces a complete reevaluation of international technology export controls. Governments must heavily monitor the sale of high-end 3D printer components and spread-spectrum radio gateways.
Intelligence agencies must increase surveillance of open-source development forums. Tracking stylometric anomalies provides early warning of incoming military technological shifts. The fusion of artificial intelligence, localized manufacturing, and decentralized command creates a highly dangerous precedent. High probability indicates other military forces will rapidly copy the Voron Nest architecture. The future of tactical warfare relies entirely on lightweight, disposable, and easily replaceable electronic networks. Defeating the architecture requires targeting the supply chain of commercial electronics and suppressing the underlying civilian protocols powering the military mesh.
Works cited
- Технология беспроводной связи LORA и ее применение в Интернете вещей – iotrouter, accessed May 13, 2026, https://en.iotrouter.com/ru/%D1%82%D0%B5%D1%85%D0%BD%D0%BE%D0%BB%D0%BE%D0%B3%D0%B8%D1%8F-%D0%B1%D0%B5%D1%81%D0%BF%D1%80%D0%BE%D0%B2%D0%BE%D0%B4%D0%BD%D0%BE%D0%B9-%D1%81%D0%B2%D1%8F%D0%B7%D0%B8-lora-%D0%B8-%D0%B5%D0%B5-%D0%BF/
- Shcherbinin Dmitry Vladimirovich. – TAdviser, accessed May 13, 2026, https://tadviser.com/index.php/Person:Shcherbinin_Dmitry_Vladimirovich.
- Dmitry Shcherbinin Appointed Deputy Defense Minister of Russia, accessed May 13, 2026, https://voennoedelo.com/en/posts/id15724-dmitry-shcherbinin-appointed-deputy-defense-minister-of-russia
- Dmitry SHCHERBININ | Research profile – ResearchGate, accessed May 13, 2026, https://www.researchgate.net/profile/Dmitry-Shcherbinin
- How Russia Is Reshaping Command and Control for AI-Enabled Warfare – CSIS, accessed May 13, 2026, https://www.csis.org/analysis/how-russia-reshaping-command-and-control-ai-enabled-warfare
- Red Skies Ahead: Russia Planning for Its Drone-Driven Army of Tomorrow, accessed May 13, 2026, https://www.armyupress.army.mil/Journals/Military-Review/English-Edition-Archives/January-February-2026/Red-Skies-Ahead/
- Dmitry Shcherbinin Appointed Russian Deputy Defense Minister – NAMPA, accessed May 13, 2026, https://www.nampa.org/text/22924670
- TAdviser – Government. Business. Technology, accessed May 13, 2026, https://tadviser.com/
- Understanding VORON and Its Role in Modern 3D Printing – SOVOL, accessed May 13, 2026, https://www.sovol3d.com/blogs/news/understanding-voron-3d-printing-significance
- The VORON 0 – A Mini, Fast & Awesome Core XY 3D Printer – CNC Kitchen, accessed May 13, 2026, https://www.cnckitchen.com/blog/the-voron-0-a-mini-fast-amp-awesome-core-xy-3d-printer
- Voron 2.4 3D Printer Kit: Specs, Price, Release & Reviews | All3DP, accessed May 13, 2026, https://all3dp.com/2/voron-2-4-review-3d-printer-specs/
- About Voron, accessed May 13, 2026, https://docs.vorondesign.com/about.html
- 4 – VORON Design, accessed May 13, 2026, https://vorondesign.com/voron2.4
- Answered: Wired star topology for mesh organisation – Google Nest Community, accessed May 13, 2026, https://www.googlenestcommunity.com/t5/Nest-Wifi/Wired-star-topology-for-mesh-organisation/m-p/455491
- Google Nest Wifi Pro Mesh Wi-Fi System, Tested and Reviewed – BroadbandNow, accessed May 13, 2026, https://broadbandnow.com/guides/google-nest-wifi-pro-system
- What is a mesh network? – Google Nest Help, accessed May 13, 2026, https://support.google.com/googlenest/answer/7182746?hl=en-GB
- Wifi software versions & release notes – Google Nest Help, accessed May 13, 2026, https://support.google.com/googlenest/answer/13800967?hl=en
- View software version – Google Nest Help, accessed May 13, 2026, https://support.google.com/googlenest/answer/6273871?hl=en
- Cyberwarfare leaks show Russian army is adopting mindset of secret police – The Guardian, accessed May 13, 2026, https://www.theguardian.com/technology/2023/mar/30/cyberwarfare-leaks-show-russian-army-is-adopting-mindset-of-secret-police
- Nest WiFi Pro Setup Guide | FAQ’s Answered | All Configs Shown – YouTube, accessed May 13, 2026, https://www.youtube.com/watch?v=oeEQa5bCBnc
- Building a Voron 2.4 – Zev, accessed May 13, 2026, https://zev.se/posts/building_a_voron_2.4/
- VoronDesign/Voron-Documentation: Sources of the documentation website for all Voron 3D printers – GitHub, accessed May 13, 2026, https://github.com/VoronDesign/Voron-Documentation
- Tuning Guides – Voron Documentation, accessed May 13, 2026, https://docs.vorondesign.com/tuning/