Power prefers reflex arcs over reflection. An instruction to react faster than reason strengthens that trend. A common message repeats across feeds that “thinking freely is no longer a skill; it is a threat.” The message spreads through repetition, social proof, and engineered outrage. That message primes audiences to trade inquiry for identity. Once that swap settles in, decision advantage shifts to actors who script the next impulse.
Information abundance hides meaning behind noise. Platforms optimize for engagement, not accuracy. Algorithms rank velocity, novelty, and emotion over provenance, coherence, and source integrity. Incentive structures push users toward speed, certainty, and tribal signaling. Emotional obedience replaces disciplined reasoning. Thought emerges from impulse rather than reflection. Reaction comes first, comprehension trails behind, and revision almost never arrives. That pattern forms the backbone of cognitive war.
Strategists have treated cognition as terrain for decades. Russian reflexive control theory lays out methods for shaping an adversary’s perception-action loop so that choices feel self-directed while actually steered. Chinese political warfare doctrine integrates psychological, media, and legal pressure to set conditions before conflict. Iranian security organs blend clerical authority, paramilitary networks, and online brigades to police narratives and punish dissent. Practitioners seed storylines across VK, OK.ru, Aparat, Telegram, TikTok, and fringe forums, then route amplification through proxies and influencers. Content laundering moves a claim from an obscure source to a respectable outlet through staged citations and selective translation. Fabricated documents, synthetic personas, and clipped audio create plausibility while staying deniable.
Operational tradecraft follows a predictable arc. Targeting begins with audience segmentation based on identity, grievance, and aspiration. Framing attaches meaning to events in ways that reward in-group loyalty and punish doubt. Repetition across channels imprints salience. Microtiming syncs posting bursts with real-world stressors such as elections, trials, and crises. Exposure spawns perceived consensus, which triggers conformity pressure. Fact checks often arrive too late to neutralize first impressions. Actors who master velocity and volume tilt cognition before counter-messaging finds footing.
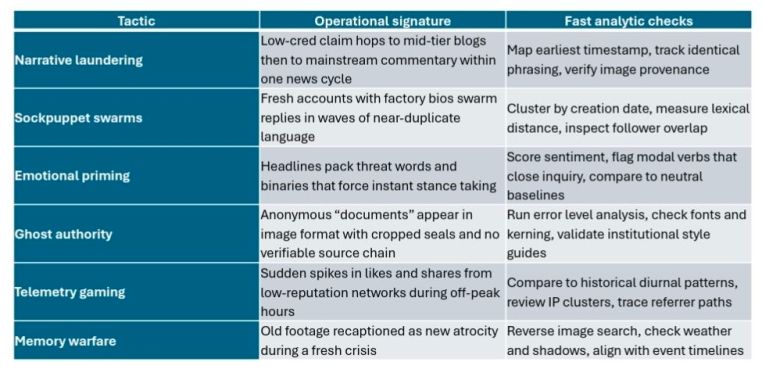
Defenders need reliable ways to spot manipulation in motion. The following reference matrix supports rapid triage across teams and time zones.
Adversaries pursue effects on thinking, not only on opinions. The goal seeks to occupy attention, overload working memory, and short-circuit deliberation. Once cognition shifts from inquiry to performance, an outside script sets the frame. People feel free while following a path engineered for them. No more effective control exists than control that feels like freedom.
An effective defense starts with tradecraft, not slogans. Build collections that emphasize earliest known appearance, cross-lingual tracing, and structured source evaluation. Maintain adversary playbooks that translate doctrine into observable signatures across platforms in Russian, Persian, Arabic, and Chinese. Establish narrative tripwires for recurring themes such as existential threat, moral panic, purity versus contamination, and betrayal within. Prebunk likely falsehoods before they surge. Train analysts to separate claims from frames and to write in plain language that resists emotional bait. Pair humans with models that enrich rather than replace judgment. Measure outcomes against decision quality, not raw reach.
Treadstone 71 provides a full spectrum response aligned to those needs. Analysis as a Service delivers finished intelligence on influence networks, narrative flows, and operational signatures across priority theaters. Adversary Dossiers and Reports map decision makers, financiers, intermediaries, and technical infrastructure with evidence trails. Targeted Influence Operations design and run counter-narratives that degrade hostile storylines while staying inside legal and ethical bounds. Cognitive Warfare training and PEOPINT modules build skill in detecting unwitting participation, reflexive control triggers, and narrative scaffolding. STEMPLES Plus frames socio-technical factors for country and sector assessments, while STEMPLES Plus for cybercrime extends that frame to illicit markets. Advanced Analytic Dominance programs teach thirty new structured methods that raise rigor and repeatability. OPSEC Assessment and Intelligence Preparation of the Cyber Battlefield harden collection and production nodes against adversary discovery. Intelligence Requirements drafting and Priority Intelligence Requirements workshops align collection to mission. Insider Threat Capability Maturity Model and Protective Intelligence strengthen internal detection of influence risks. Elicitation Interview Protocol sharpens human collection and counter-elicitation. Strategic Cyber Intelligence Integration Bootcamp connects method to mission so that leadership receives clear options grounded in evidence. Counter and Contain Influence Operations bring disruption plans that neutralize enablers and close off ramps for escalation. Program Build services and Maturity Assessments convert practice into sustained capacity.
Execution follows a tight loop. Define the decision that analysis must inform. Translate that decision into testable questions and PIRs. Map the adversary narrative order of battle with doctrines, themes, channels, and amplifiers. Stand up a cross-lingual collection plan that reaches VK, OK.ru, Aparat, Telegram, and regional outlets. Ingest, timestamp, and normalize content flows. Run detection matrices for laundering, bot coordination, and ghost authority. Score hypotheses against observed signatures. Publish findings that distinguish fact patterns from frame manipulation. Deploy counter-messaging only after pre-testing for second-order effects and adversary adaptation. Feed outcomes back into the playbook and refine.
Decision advantage depends on the recovery of disciplined thinking under pressure. Reflection beats impulse when leaders demand process, evidence, and clarity. Influence actors pursue the occupation of consciousness because conquered minds police themselves. No more effective control exists than when the controlled believe they act in freedom.




You must be logged in to post a comment.