The statement uses mockery to frame Saudi Arabia’s public narrative of cybersecurity leadership as hollow, asserting ongoing adversary access to systems without detection or remediation. The claim works as an influence operation to discredit technical competence, erode institutional credibility, and signal superiority over Saudi cyber defenses.

Moderate confidence in the psychological intent of the statement — the ridicule framing aligns with established adversary influence tactics targeting perceived hypocrisy. Low confidence in the factual claim of persistent, undetected system control without corroborating technical evidence. The message’s primary measurable impact will be reputational rather than tactical unless paired with verifiable breach disclosures.
Narrative structure — what the message says and how it is built
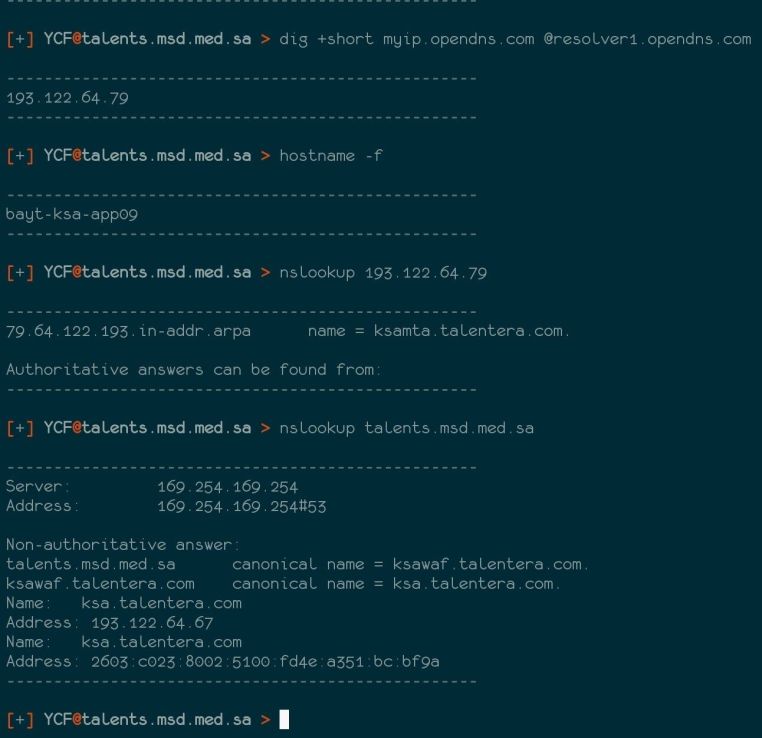
The core assertion is that Saudi Arabia promotes itself as “number one in cybersecurity,” yet remains compromised, with adversaries maintaining control of systems. The speaker emphasizes that no detection or patching has occurred, using the adjective “ridiculous” to underscore incompetence. The statement positions the adversary as dominant and the defender as inept, while implying that the intrusion is persistent and strategic.
Cognitive warfare dimensions — intended psychological effects
The message aims to produce humiliation within Saudi cybersecurity circles by publicly contrasting self-praise with an alleged operational reality of failure. It erodes domestic trust in the Kingdom’s technical capability by suggesting that official proclamations are propaganda rather than fact. For foreign observers and potential allies, it encourages skepticism toward Saudi cyber assurances, potentially undermining investment and cooperation. For adversary-aligned communities, it boosts morale by portraying penetration and control as effortless and prolonged.
The ridicule component functions as a narrative amplifier. It encourages sharing within opposition or hacktivist networks because it invites a “gotcha” framing — an “emperor has no clothes” moment that is easily memed. This ridicule is a cognitive weapon, using shame to pressure decision-makers and potentially provoke rushed or ill-considered defensive actions.
Influence manipulation — embedded strategic objectives
By claiming continued control without detection, the speaker seeds doubt about the efficacy of Saudi cyber monitoring tools, incident response workflows, and threat intelligence capabilities. The claim undermines not only technical defenses but also institutional legitimacy, painting any official silence as either ignorance or deliberate cover-up. This pressures defenders into reactive communication, which can reveal investigative progress or limitations, giving the adversary insight.
If amplified internationally, the statement can impact reputation-based assets — such as Saudi Arabia’s push to lead regional cybersecurity initiatives — by painting such leadership claims as performative. Domestically, it can fuel dissent in professional cyber and IT communities, fostering blame narratives against government agencies or private contractors.
Disinformation risk indicators — assessment of credibility
No direct proof is offered in the statement. There is no technical evidence of ongoing access, no list of vulnerable systems, and no timeline beyond “so far.” The claim leverages plausibility through alignment with known regional cyber threats and recent publicized intrusions but remains unverifiable without independent forensics. The ridicule serves to distract from this lack of substantiation, shifting focus to emotional resonance rather than evidentiary support.
Impact forecast — short- to mid-term narrative effects
Short term (0–3 months): Amplification in hostile or opposition-aligned social media channels, with memes, hashtags, and recycled jokes about “number one in cybersecurity” narratives. Possible domestic media pushback or attempts to reassert capability.
Mid term (3–12 months): If not countered with credible incident reporting, the claim risks becoming a persistent talking point for critics. The statement could surface in diplomatic or industry discussions as an example of Saudi vulnerability, especially in cybersecurity conferences or rival state media.
Strategic foresight — scenario outlook
Scenario 1: Immediate amplification and ridicule loop
Indicators: Increased reposting of the statement in Arabic and English cyber forums; emergence of visual memes pairing the claim with Saudi promotional material; mocking commentary in Telegram hacktivist groups.
Implications: Rapid erosion of narrative control; difficulty reestablishing credibility without verifiable public proof of remediation.
Scenario 2: Defensive counter-messaging
Indicators: Official Saudi statements emphasizing active defense measures; release of statistics or case studies showing threat neutralization; media coverage framing the claim as false.
Implications: Potential restoration of confidence among domestic stakeholders, but risks confirming that the claim touched a sensitive nerve.
Scenario 3: Narrative entrenchment
Indicators: Claim is repeated months later in unrelated cyber discussions; foreign policy critics use it as shorthand for Saudi cybersecurity weakness.
Implications: Persistent reputational drag; possible hesitancy from partners in joint cyber exercises or intelligence sharing.
Measures of effectiveness — tracking counteraction success
Reduction in mention volume of the claim in monitored channels; shift in framing from ridicule to neutral reporting; emergence of alternative narratives positioning Saudi Arabia as responsive and adaptive in cyber defense.
They talk a lot about Saudi Arabia being number one in cybersecurity, but we still control the systems so far, and they have not been able to detect or fix the vulnerabilities, and this is ridiculous.






You must be logged in to post a comment.