Technical Breakdown
#silenttrigger
#Firmware Logic Bomb Payloads (WW0001022061 & WW0001001220)
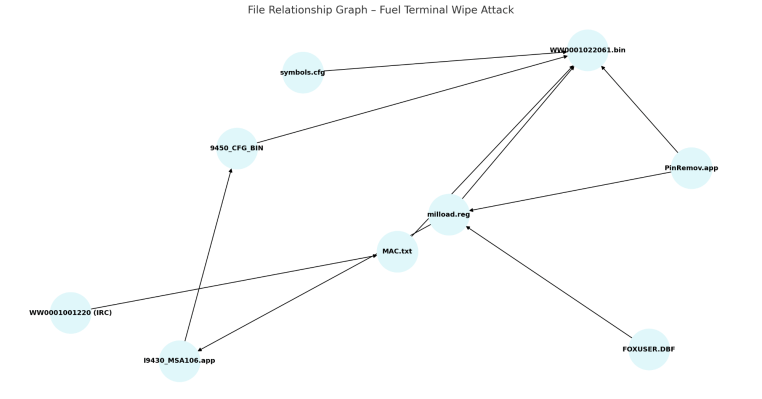
Disassembly and Payload Roles: The core malicious firmware components in this attack are binary files (e.g. WW0001022061.bin and WW0001001220). These act as logic bombs planted in the device firmware. Upon activation, they corrupt device memory and halt the CPU, effectively “bricking” the terminal. Both binaries contain distinctive opcode sequences corresponding to destructive actions: notably 0xEA (far jump), 0xC3 (return), 0x00 (null byte), and 0xF4 (halt). These opcodes are intentionally used to divert execution flow, wipe memory, and stop the processor. Table 1 summarizes their behavior:Opcode (Hex)InstructionPurpose in PayloadF4HLT (Halt CPU)Forces the processor to stop execution (used at final stage to freeze the system).C3RET (Return)Returns from a call – repurposed here to create a return-loop that stalls normal execution (an infinite loop effect).EAJMP FAR (Far Jump)Jumps to a far memory address – used to leap into the logic bomb routine hidden in firmware memory.00NULL byte (NOP/Fill)Filler used to overwrite memory with zeros – effectively wiping data/instructions in the targeted region.
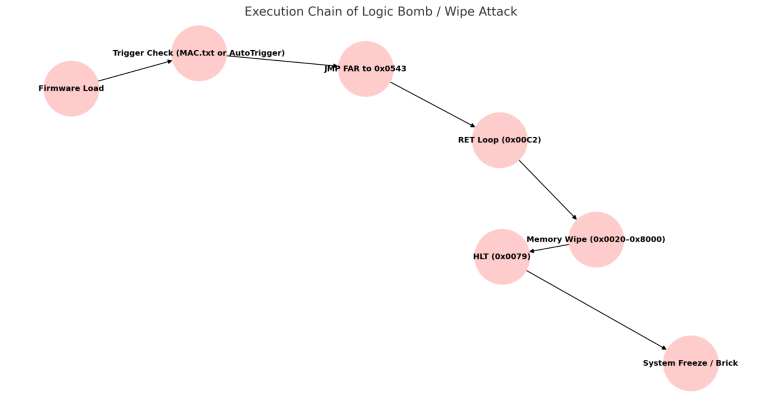
Execution Chain and Memory Wipe Mechanics: Once the malicious firmware is loaded into a device, it follows a deterministic execution chain to carry out the sabotage. The steps below describe this sequence for the WW0001022061.bin payload (the behavior of WW0001001220 is very similar):
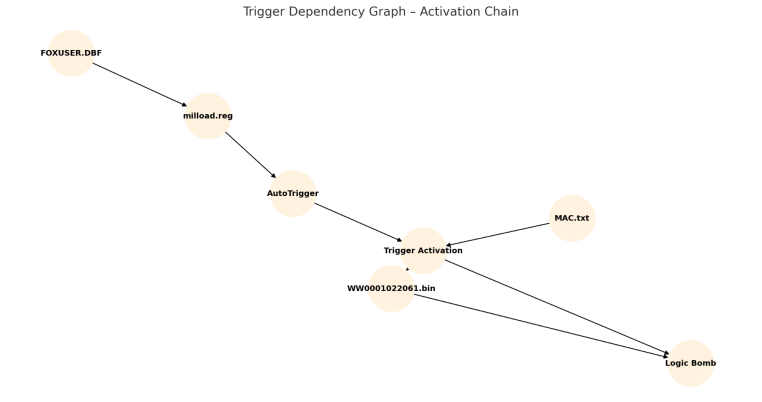
- Load Malicious Firmware: The compromised firmware (
WW0001022061.bin) is introduced into the device (e.g. via an update process). A small companion stub (e.g.WW0001022060, 411 bytes) likely triggers loading of the main 90 KB payload into memory (the stub contains an ASCII reference to the large file and version). - Trigger Check: On execution, the malware checks a trigger condition. It reads either a MAC address filter or an AutoTrigger flag to decide whether to activate the logic bomb. Specifically, it consults a list of target MAC addresses in a config file (MAC.txt) or a registry key flag (
AutoTrigger=1) that forces activation. If the device’s MAC address matches an entry in MAC.txt (or if AutoTrigger is set), the malicious routine proceeds; otherwise, it stays dormant (allowing normal operation). This conditional design makes the attack selective and stealthy. - Far Jump to Logic Bomb: When triggered, the firmware executes a far jump (opcode
EA) to a designated address in memory that holds the destructive routine. For instance, in WW0001022061 the jump goes to offset0x0543where the “logic bomb” code resides. This separates the trigger check from the payload, making analysis harder. - RET Loop and Memory Corruption: Entering the logic bomb section, the code uses a series of
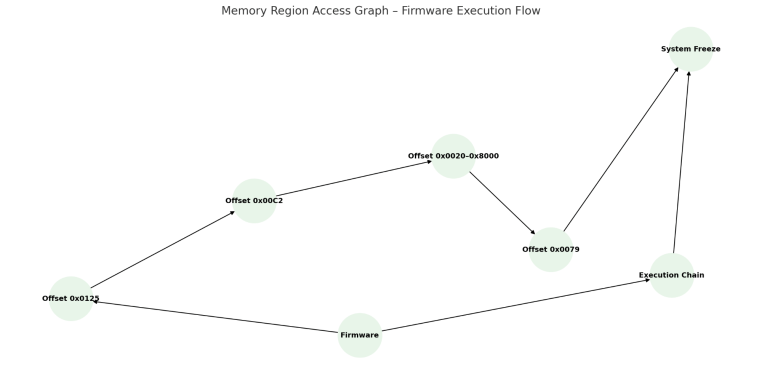
RETinstructions (0xC3) to create a return-oriented loop. This effectively traps the execution flow in a tight loop or recursive returns, preventing any normal firmware function. Immediately after, the payload begins wiping memory: it writes null bytes (0x00) across a broad memory range (observed from around0x0020through0x8000in memory). This overwriting of memory with0x00bytes erases code and data in that region. In some variants, the wipe routine may also use0xFFbytes in addition to0x00, likely to ensure all binary data is overwritten (0xFF is a common flash erase pattern). The Memory Region Access Graph provided in the materials visualizes this behavior – it shows the firmware systematically writing to the memory addresses in the 0x0020–0x8000 range (and possibly beyond), effectively corrupting the device’s program storage. - CPU Halt (Device Bricking): Finally, the malware executes a CPU halt. In WW0001022061, a
HLTinstruction at address0x0079is invoked to stop the processor dead in its tracks. This halts the entire terminal, requiring a hard reset or hardware repair. In the case of WW0001001220 (also referred to as IRC007001030.bin), the ending is functionally similar: a HLT at0x00C3is observed. In addition, analysis indicates this variant also performs a jump to address0x0000after the wipe, creating an infinite execution loop at a null location. In both cases, the outcome is the same – the device’s memory is wiped and the CPU is either halted or trapped in a useless loop, rendering the terminal permanently non-functional (bricked). As the report notes, the device “enters permanent freeze (bricked)” once this sequence completes.
The above sequence is corroborated by the “Execution Chain of the Logic Bomb” diagram from the source material, which depicts the exact flow: loading of the firmware, the MAC/AutoTrigger check, the jump to the wipe routine, the progressive memory null-fill, and finally the halt that freezes the system. This careful ordering ensures the payload does maximum damage before the device can shut down. Notably, the malware’s use of conditional triggers means the destructive routine can remain latent until the specified condition is met, avoiding immediate detection. The presence of multiple jump and loop instructions (EA, RET) further suggests the code might attempt to evade simple linear analysis or interfere with any fail-safes by not returning control to normal firmware execution once triggered.
Trigger Configuration Files (MAC.txt & AutoTrigger)
Two external configuration inputs control the logic bomb’s activation: a plaintext MAC address list and a Windows registry flag.
- MAC.txt (MAC Address Filter): This is a simple text file containing a list of device MAC addresses (each 12 hex digits, no colons). It serves as a “kill list” for the malware. During execution, the firmware reads the terminal’s unique MAC and compares it against entries in MAC.txt. If a match is found, the malicious jump to the wipe routine is authorized. If the MAC is not on the list, the logic bomb will not activate, and the device continues normal operation. In other words, MAC.txt provides surgical targeting of specific terminals. The list observed in the attack contained multiple MAC entries (likely corresponding to critical fuel distribution terminals in Iran). Security analysis notes that this hardcoded list, being plaintext, is easily modifiable and not authenticated. The risk is twofold: an attacker can insert target MACs of choice (or an insider could remove entries to protect certain devices), and the static list itself is evidence of intended targets. The use of an external file for conditional logic is unusual in firmware but underscores the attackers’ need to limit the blast radius of the attack to specific systems. (The provided “MAC Trigger” portion of the visuals presumably shows this logic flow, with a conditional branch leading to the wipe if the MAC is in the list.)
- Registry AutoTrigger Flag (milload.reg): In addition to the MAC filter, the malware can be force-triggered via a Windows registry key on the host system. The registry file milload.reg (a REGEDIT4-format registry export) contains a relevant key:
HKEY_CURRENT_USER\Software\Telesincro\milload\Settings\AutoTrigger. When thisAutoTriggervalue is set to1, the malware will initiate its destructive routine regardless of the MAC check. Essentially, this is a manual override to instantly fire the logic bomb on any device. The firmware or its loader logic explicitly checks this key’s presence/value and if true, bypasses the MAC.txt filtering entirely. In practice, an attacker with access to the host PC (where the device management software runs) could set this flag in the registry to ensure any connected terminal gets wiped out on the next update cycle or trigger event. The existence of such a switch implies the attackers anticipated scenarios where they’d want a universal kill (perhaps for testing or if they obtained access to a system where selective targeting was unnecessary). The registry file also contains other configuration entries (such as file paths likeDirAplicand an encoded “Password” field), indicating it is part of the milload utility’s settings. The presence of a plaintext password (which decodes to “MegaMicrosis” as noted in the analysis) and hardcoded paths highlights poor security, but the critical point is that the malware could leverage this host-side config. By settingAutoTrigger=1, the firmware’s trigger check will immediately jump to the wipe routine without needing any specific MAC. This registry key acts as a booby-trap: if an operator or automated process loads the malicious firmware while that flag is set, the device will self-destruct immediately.
Memory Wipe and HALT Logic: Both payload variants devote significant portions of code/data space to zero bytes (0x00), which are used to overwrite memory regions. In WW0001022061, the binary from offset 0x0020 onward is largely 0x00, indicating a wipe zone that gets written into device memory. The disassembly mapping shows a “NULLs Wipe memory zone” spanning 0x0020–0x8000. Similarly, WW0001001220 shows repetitive 0x00 patterns starting at offset 0x0068 and continuing through its memory space. The wipe is followed by execution of the HLT instruction (or an infinite jump loop). The combination of erasing memory then halting means even if the device is power-cycled, its firmware is in an invalid state (important code has been nullified) and it cannot boot or operate. The Memory Region Access Graph in the report likely illustrates how the malicious code writes across different memory addresses (possibly showing a spike or line for each address range accessed). This correlates with our understanding: the logic bomb indiscriminately corrupts both code and data regions of memory, rather than a targeted payload (suggesting the goal is outright destruction rather than subtle manipulation). The inclusion of RET (C3) in a loop further ensures the normal program flow never recovers. The analysis even highlights an “infinite loop and memory wipe” sequence in the IRC007001030 sample: a series of RET/CALL instructions, memory being filled with 0xFF/0x00, and a jump to address 0x0000 to cycle forever. This is essentially another way to halt operation (by trapping the CPU in a loop) in case the HLT didn’t terminate the process. In summary, the payload’s mechanics are geared towards maximum irrecoverable damage – they wipe critical sections of firmware and then stop the processor, leaving the terminal completely non-functional.
Role of DBF and Application Files (Privilege Escalation & Spoofing)
Beyond the firmware logic bomb, the attackers leveraged supporting files to escalate privileges and spoof terminal identities within the fuel distribution system. Key among these are a FoxPro database file (which stores user/terminal roles) and several “.app” descriptor files that define device identity and permissions.
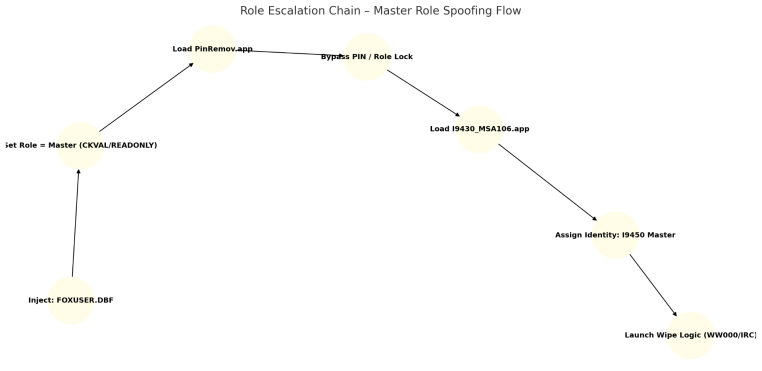
- FOXUSER.DBF (Role/Identity Database): This file is a small (≈4 KB) legacy database in FoxPro (.DBF) format. The analysis of its structure reveals it contains fields for device/user type, ID, name, flags, role level, and other data at fixed offsets. For example, offset 0x0020–0x002F is labeled “TYPE” (likely a code indicating if the entry is a terminal, operator, etc.), 0x0040–0x004F is “ID” (terminal or operator ID), 0x0060 is a name, 0x0080 a read-only flag, and importantly 0x00A0–0x00AF is a role level/check value. This suggests FOXUSER.DBF holds credentials or permissions profiles for terminals on the network. An attacker who can manipulate this file can alter a device’s identity and privileges. For instance, by editing the “TYPE” or “Role level” fields of a given record, a normal station could be falsely elevated to an admin or master role. The context implies that the fueling system used FOXUSER.DBF to verify if a terminal is a master controller or has authority. The malware operators likely replaced or modified this DBF on targeted systems to grant themselves higher privileges. For example, they could change a local terminal’s type/ID to mimic a master terminal expected by others, or set a flag that marks it as a maintenance/admin user. This is what we refer to as terminal role spoofing – the database tricked the system into treating the compromised terminal as a trusted high-privilege device. This step is critical in the kill chain because without the appropriate role, a rogue device might not be allowed to issue commands or distribute firmware updates to other terminals. By spoofing the role via FOXUSER.DBF, the attackers ensure their device or software commands are accepted as if they came from legitimate control units. (The “Role Escalation Chain” visualization likely maps this process: starting from an ordinary terminal/user entry in the DBF, then an arrow showing modification of fields, leading to an elevated role that grants broader system access.) There is no evidence of encryption or integrity checking on this DBF; being a legacy format, it’s simply loaded by the application. Thus, the attackers could directly patch it (or include a malicious version in their deployment) to seize higher privileges within the system.
- Terminal Descriptor Files (I9430_MSA106.app & I9450__222_107.app): These “.app” files are actually plaintext INI-style configuration files that describe terminal models and roles. The file
I9430_MSA106.appcontains sections like[MODEL]and[COMMUNICATION]with fields: for example,CODE=I9430 RS232 1M/4M:andDESC=NIOC Fuel Project. This defines a device model “I9430” using an RS232 interface (serial) with certain memory specs, and tags it as part of the “NIOC Fuel Project”. In contrast,I9450__222_107.app(mentioned in metadata) or the similarly structured PinRemov.app (which we detail next) defines an I9450 model, which appears to be a more advanced “Master Device” using Ethernet (ETH) and designated as the fuel project’s master controller. In hierarchical terms, it’s likely that I9450 is the master terminal model and I9430 the subordinate terminal model in the Iranian fuel system. By deploying these .app files, the attackers could spoof a terminal’s identity. For example, an I9430 device (ordinary pump/controller) could be loaded with a forged I9450 descriptor so that it announces itself as a master device to the network. The analysis explicitly notes that these files “may define terminal identity or change its role” and *“can be spoofed to impersonate other units.”*. In practice, the attackers might plug a malicious device or compromise an existing one, then apply the I9450 configuration so that it’s recognized as a Master by others. This would grant it command authority. The .app files being plain text and not integrity-protected means the adversary could easily craft and introduce them via USB or over-the-air updates. Indeed, the report calls out that these files “can be injected via USB or OTA” with no validation. Summarizing, the .app descriptors are used to masquerade as trusted equipment within the target network, an essential step for the attackers to propagate their malicious firmware or send destructive commands without being blocked. - PinRemov.app (Master Device PIN Removal Patch): The
PinRemov.appfile is another INI-format configuration patch, specifically listingCODE=I9450 ETH 2M/4M:with a description “Master Device” under the fuel project. The name “PinRemov” suggests it is designed to remove a PIN – likely some security PIN or authentication requirement on the master terminal. The interpretation given in the analysis is that this file’s purpose is to “unlock [the] device or escalate access,” effectively bypassing protections on a Master I9450 terminal. It implies that in normal operation, certain critical actions on master controllers (like firmware updates or safety interlocks) might require entering a PIN code or having a physical key present. By applying the PinRemov.app patch, the attackers disable that requirement, granting themselves unfettered access to the master device’s functions. This file is clearly intended for the Master terminal (I9450) context, and would be used once the attackers either compromised an existing master or had successfully spoofed a subordinate as a master. In the latter case, removing the PIN checks would finalize the spoofed device’s elevation to full master privileges. Like the other config files, PinRemov.app is plaintext and lacks any cryptographic safeguards. The security assessment flags this as a significant risk: an attacker can easily create forged versions of such patches to manipulate device behavior. During the attack, the adversary likely introduced PinRemov.app to ensure that their master device (real or impersonated) would not prompt for credentials or fail any authentication that might otherwise prevent unauthorized firmware loading or settings changes. Essentially, PinRemov.app knocks down any last authentication barrier on the top-tier controller.
To summarize the interplay: FOXUSER.DBF provides the means to escalate a terminal’s role at the software/database level (making the system think an attacker is an admin or a master terminal operator), while the .app files (I9430_MSA106, I9450 descriptors, PinRemov) allow the physical device to impersonate the identity of a privileged terminal on the network and disable security checks. Together, these supportive files set the stage for the core firmware logic bomb to be deployed across the infrastructure. The “Role Escalation Chain” graph likely illustrates this multi-step elevation: the attacker goes from having a foothold on a regular device, to modifying FoxUser (gaining admin credentials), to applying I9450 master config (assuming master identity), to removing PIN protections (achieving full control), and finally to pushing the destructive firmware to target devices. Each stage corresponds to one of these files, forming a chain of trust abuse that culminates in the logic bomb execution described earlier.
Summary of Components and Their Roles
For clarity, Table 2 below maps the key files and firmware components to their functions in the attack:ComponentTypeRole in AttackWW0001022061.binFirmware binary (logic bomb)Primary malicious payload that wipes memory and halts the CPU when triggered, bricking the device. Contains HLT, RET, JMP opcodes to execute the logic bomb sequence.WW0001001220
(IRC007001030.bin)Firmware binary (logic bomb)Variant payload with similar destructive routine. Possibly an earlier or device-specific version; uses memory fill (0x00/0xFF) and an infinite loop or HLT to incapacitate the controller.WW0001022060 (and other ...0 files)Firmware loader stubSmall companion files (≈411 bytes) that likely contain metadata and initiate loading of the above larger .bin files. Attackers modified these as needed to introduce malicious code (e.g., some stubs contain the HLT opcode as well).MAC.txtPlaintext config (MAC list)Lists specific MAC addresses of target terminals. The logic bomb checks this list to decide whether to trigger, enabling targeted sabotage of chosen devices. Allows surgical filtering of victims.milload.reg (AutoTrigger)Windows Registry settingsContains AutoTrigger flag under Telesincro\milload settings. If set to 1, it forces the logic bomb to activate on any device, bypassing MAC checks. Essentially a master kill-switch used by the attacker. Also holds config info (paths, plaintext password) for the loader utility.FOXUSER.DBFFoxPro database (roles)Stores terminal/user profile data including type, ID, and role level. Manipulated by attacker to spoof device identity and escalate privileges (e.g., change a normal terminal’s role to “Master” or grant admin rights) within the system. Facilitates privilege escalation and trust manipulation.I9430_MSA106.appDevice descriptor (INI file)Configuration defining an I9430 terminal (serial-connected unit). Used by attacker to understand and possibly alter subordinate terminal identity (I9430 is presumably a field unit). May be involved in re-configuring a device’s reported model or linking it to the NIOC project context.I9450__222_107.app
(Master descriptor)Device descriptor (INI file)Configuration for an I9450 master terminal. By deploying a matching descriptor on a compromised device, the attacker’s device can impersonate the master controller. This grants the ability to issue commands or updates to other terminals (since it now appears as the legitimate master).PinRemov.appDevice patch (INI file)“PIN Removal” patch for I9450 Master devices. Disables PIN-based protections, allowing unauthorized configuration changes. Used to unlock master-level functions or remove safety interlocks during the attack. Ensures the attacker-controlled master device or account faces no authentication prompts.symbols.cfgLog/flag fileA simple log file that appears to be dropped after a wipe event, containing a timestamp. Likely used by the malware to note that a terminal was “cleaned” (wiped) successfully. Not directly part of the attack chain, but serves as a marker of destruction (for attacker’s confirmation or taunting forensics).
Table 2: Key malicious components and their functions in the SILENT Trigger attack. (Sources: Analysis of provided SILENT_Trigger data)
This technical breakdown demonstrates a coordinated set of actions within the device firmware and configuration: condition-based triggering, memory sabotage, CPU halting, and role/identity subversion. In the next section, we examine how an attacker would operationalize these components step by step in a real-world attack on the fuel distribution network.
Operational Breakdown
Attack Workflow: From Compromise to Execution
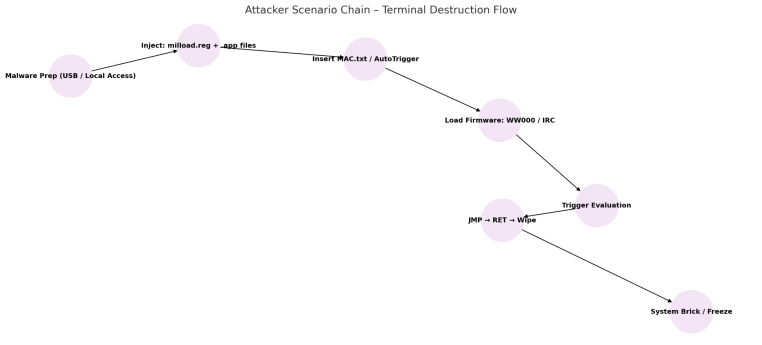
Initial Compromise and Malware Deployment: The SILENT Trigger operation likely began with the attackers gaining access to the maintenance or update infrastructure of the Iranian fuel distribution system. This could have been via an infected USB drive or local network intrusion into the PC that manages fueling terminals. The maintenance software (by Telesincro, as indicated by the registry path) probably uses the milload tool to update terminal firmware and configurations. The attacker’s first goal would be to introduce the malicious files into this environment. They could either replace legitimate firmware files with the tampered versions (e.g. swapping a genuine WW0001022061.bin with their logic-bomb-laden version) or place new files in the update directories. Given the file listing, multiple firmware and config files were present (for different device models), and the attackers prepared malicious counterparts for those. Once inside the system, the workflow might unfold as follows:
- Privilege Escalation on Maintenance PC: Using the FOXUSER.DBF and possibly stolen credentials, the attacker elevates their privileges in the software. For instance, they modify FOXUSER.DBF to add an account or terminal entry with high privileges (administrator or developer level). This could allow them to run unauthorized firmware update procedures or execute registry changes. If the maintenance PC was not initially compromised at an admin level, this step ensures they can now perform critical actions (like editing the registry and writing to system directories) without restriction. It’s also possible the FOXUSER.DBF trick was used to fool the system into treating the attacker’s field device as a trusted one when connected.
- Introduce Malicious Configurations: The attacker loads the .app descriptor files onto the system or directly onto a connected device. For example, they might plug in a rogue terminal or connect to an existing one over a serial/USB link and then apply the
I9430_MSA106.appandI9450...appconfigurations. This step is about device identity spoofing – the attacker ensures that when their device comes online, it will identify itself as a legitimate master controller (I9450) belonging to the NIOC fuel network. If the target network has an update broadcast mechanism, the attacker might impersonate a master to push updates; if it’s more manual, they might sequentially update each station but using master credentials. In either case, establishing a trusted identity is crucial. The.appfiles are simply copied into the appropriate directories (e.g.,...\APP\paths) so that the system will read them. Because there are no integrity checks or authentication on these config files, the system accepts them as if they were legitimate. - Disabling Security (PIN Removal): With the PinRemov.app patch, the attacker now disables any local security prompts on the master controller. If the fuel system normally requires a PIN or physical key to authorize changes (such as loading new firmware onto pumps), this patch ensures those checks are bypassed. The attacker sets the
PinRemov.appin place for the Master device (whether they have created a fake master or compromised the real one) to guarantee that the subsequent malicious actions won’t be stopped by something as simple as an operator PIN code. Essentially, this is preparation for unfettered access – the master device will now obey commands without asking “Are you authorized?”. - Deployment of Malicious Firmware: Now the stage is set to deliver the logic bomb firmware to the target terminals. There are a couple of scenarios for this: If the attacker controls a Master terminal in the field (real or impersonated), they can use it to propagate the update. For example, the master might have the capability to update subordinate controllers (I9430 units) over the network or via a connected bus (the presence of RS232 in descriptors suggests a serial network topology). In that case, the attacker, acting as the master, sends the
WW0001001220orWW0001022061firmware as an “update” or routine maintenance package to each target terminal. Alternatively, if each station is individually updated via the maintenance PC, the attacker (now an admin on that PC) could simply initiate the update process for each station’s firmware with the corrupted binaries. In both approaches, because the attacker’s files are in the expected format and the system lacks cryptographic signing, the malicious firmware is accepted as valid. Notably, the analysis highlights that the firmware files (even delivered as Intel HEX records or binaries) have “no checksum or signature”—the device will load whatever it’s given. This lack of verification means the attacker’s code slides right in. The malicious firmware might be deployed widely, but crucially, it won’t detonate immediately unless conditions are met. The MAC filtering ensures that even after deployment, the payload stays inert on non-targeted units. This is an important operational safety feature for the attacker: they could install the malware on many stations in preparation, without causing any effect until the chosen moment. - Triggering the Logic Bomb: The final step is to trigger the destructive payload on command. If the attackers synchronized the attack for maximum impact, they likely used the AutoTrigger mechanism or coordinated MAC triggers. For instance, they could remotely set the
AutoTrigger=1flag via the maintenance software or an update patch just before activation. This would cause every infected unit to execute the logic bomb immediately (ignoring MAC checks). Alternatively, they may have timed the attack using the MAC list: for example, including only certain MACs (perhaps those of critical or high-value stations) in the list from the start. In that scenario, as soon as the malicious firmware was installed on those specific stations, it would detect the MAC match and self-destruct the next time the station booted or the malware performed its check cycle. There is also the possibility mentioned in the threat report that the attackers manually triggered the event via some command. Given the sophistication, a likely scenario is that the attackers set a particular time or condition (maybe a specific date, or an external command from the master controller) to flip all the switches. Once triggered, each targeted terminal’s firmware goes through the execution chain described in the technical section: jumping to the wipe routine, blanking memory, and halting the system. Field devices (fuel dispensers or controllers) would suddenly fail, unable to dispense fuel or communicate. - Post-attack Stage: Following execution, the attackers have essentially accomplished their goal – the fuel terminals are non-functional. The
symbols.cfglog files noted in the analysis suggest that the malware may create a flag after wiping a device (e.g., dropping a file with the date/time of wipe). This could be for the attackers’ own confirmation that the wipe occurred on each device, or simply a by-product of the system logging an error/reset. In any case, at this point the attackers might simply disconnect and leave, especially if this was done remotely. The damage is done: technicians on the ground would find that the pumps/terminals are “dead” or frozen, and their firmware memory is trashed. Recovery would require reflashing firmware or swapping hardware modules, a process taking considerable time per device.
Throughout this workflow, the attacker’s privilege acquisition and escalation were key. By leveraging FOXUSER.DBF and PinRemov, they became essentially an insider with admin rights and master-device authority. This allowed them to abuse the normal firmware distribution channels to deliver a malicious update as if it were authorized. Notably, at no point in this chain would the system necessarily flag an anomaly: the files looked legitimate (no signatures to break), the commands came from a device identified as a master, and the payload remained dormant until the exact trigger condition was met.
Attacker Privilege Escalation & Terminal Hijacking
In the above scenario, two parallel tracks were critical: obtaining administrative privileges and obtaining device trust. The FOXUSER.DBF manipulation is an example of software-level privilege escalation – effectively hacking the user/role database to gain administrator capabilities on the system controlling the terminals. The .app file injection is a form of device-level privilege escalation – masquerading as the top-tier device in the hardware hierarchy (i.e., the Master terminal). By combining these, the attacker achieved a full terminal hijack.
Concretely, the attacker’s device (or the one they compromised) became a rogue master in the eyes of the network. The genuine master controllers (if any) could have been bypassed or overridden. For instance, if two masters were detected, perhaps the system allowed it or the attacker could have taken the real master offline first. The use of an Ethernet-enabled descriptor (I9450 ETH) suggests the master communicates over a network (possibly to a central system or between stations), whereas the I9430 RS232 suggests local serial links (maybe between a pump and a local controller). The attacker choosing to impersonate an I9450 means they intended to be at the top of the command chain, able to talk to either the central server or issue commands downstream to RS232-linked devices. In essence, they put themselves in the driver’s seat of the entire fuel terminal network.
The step of terminal identity spoofing has wider implications: by adopting the identity “I9450 – NIOC Fuel Project Master Device”, the attacker’s equipment could potentially issue any command that a master is trusted to send. This would include authorizing transactions, locking/unlocking terminals, or – most relevant – distributing configuration and firmware updates. Given the malicious firmware was named in a fashion similar to legitimate files (e.g., following the WW0001xxxxxx naming convention), the other devices likely accepted it as an update from their master. The operation also spoofed terminal role in a social sense: field operators would see nothing amiss because no alarms would be raised; the malicious changes were introduced under the guise of normal configuration updates or maintenance.
Finally, command authority seizure refers to how the adversary took control of the network’s decision-making. By removing PIN protections and any safety, the attacker’s commands executed without challenge. If the Iranian fuel infrastructure had any centralized monitoring, it might have logged that a firmware update occurred, but since it appeared to come from a legitimate master and user, it would not have been preventively blocked. Only after the fact – when stations started failing – would the victim realize something was wrong.
In summary, the operational phase of SILENT Trigger was a textbook example of “living off the land” in an industrial environment: the attackers used the system’s own update and authentication mechanisms (albeit flawed ones) against it. They blended in as administrators and master controllers to ensure the payload delivery went smoothly. The end result was a coordinated hijacking of multiple fuel terminals, all executing a destructive logic more or less simultaneously, leading to a nationwide disruption of gasoline distribution (as was observed in Iran).
Strategic Context
Targeting and Objectives
The SILENT Trigger attack was a surgically targeted operation aimed at Iran’s fuel distribution infrastructure – specifically the electronic control systems at fuel stations (and possibly depots). The inclusion of a MAC address filter in the malware is a strong indicator of deliberate targeting. Rather than indiscriminately infecting any system it could, the malware was programmed to activate only on devices with specific hardware network addresses. Those addresses presumably correspond to critical fuel station controllers or payment terminals across Iran. This approach ensured two things: (1) the attack focused on exactly the intended network (e.g., stations under the National Iranian Oil Company’s purview, as hinted by the “NIOC Fuel Project” descriptors), and (2) it minimized collateral damage or accidental trigger on non-target systems. In other words, the attackers were able to precisely distinguish friend from foe at the device level – a hallmark of an advanced, well-planned cyber operation.
Notably, the attackers even signaled this precision in their communications. The hacking group widely believed to be behind such operations (identified as Gonjeshke Darande or “Predatory Sparrow”) claimed responsibility for similar attacks and explicitly stated they left some stations untouched intentionally. For example, in a 2023 incident on Iranian gas pumps, the group said: *“We… ensured a portion of the gas stations across the country were left unharmed… despite our access and capability to completely disrupt their operation.”*. This mirrors the MAC-based selective approach seen in SILENT Trigger. It suggests a strategic intent not just to cause disruption, but to send a controlled message – demonstrating the ability to cripple infrastructure at will while showing restraint (arguably as a form of psychological warfare or to avoid humanitarian crises).
The hardware ID references (model codes I9430, I9450, etc.) further show the attackers knew exactly which equipment models they were dealing with. These model numbers are not generic; they are specific to the fuel automation systems used in Iran. This implies the adversary conducted reconnaissance or had insider knowledge to obtain the technical details of Iran’s fueling system architecture. The presence of strings like “NIOC Fuel Project” inside config files ties the attack firmly to Iranian state infrastructure. Such tailoring of malware to a nation’s specific systems strongly indicates a state-sponsored attacker with a clear target in mind.
The adversary’s objectives in this operation appear to be threefold: disruption, degradation of trust, and strategic signaling. The immediate goal was disruption – to knock offline a large portion of Iran’s gasoline distribution network. By bricking the station controllers, the attack effectively stopped fuel sales, causing long queues and public turmoil (indeed, reports from October 2021 confirm thousands of stations were paralyzed and motorists stranded). This creates economic and psychological pressure. A second objective was likely data denial or sabotage: wiping the devices not only interrupts service but also destroys any stored data (like transaction logs or configuration data) on them. Restoring service would require not just power-cycling but reprogramming each device, and any forensic evidence on the devices could be erased by the memory wipe. The third objective is equipment incapacitation – some of these controllers might actually be physically damaged or require factory repair due to corrupted firmware. In cyber warfare terms, this attack was more akin to using a cyber bomb than espionage; it was meant to cause lasting damage to tangible assets.
Adversary Sophistication and Tradecraft
The sophistication of SILENT Trigger is evident in its multi-layered approach and the technical prowess required to develop it. The attackers demonstrated firmware engineering capabilities that are relatively rare. Crafting malicious firmware for proprietary industrial devices (likely using obscure or custom instruction sets) shows expertise on par with nation-state intelligence agencies or defense units. They identified opcodes (HLT, RET, etc.) that would have specific low-level effects on the device CPU, indicating familiarity with the target CPU architecture and its assembly language. The use of far jumps and careful memory manipulation without tripping validation also suggests they tested this payload extensively – possibly even on genuine hardware – to ensure it achieves the intended result reliably.
Moreover, the adversary leveraged hardware abstraction knowledge: they understood how firmware is delivered (Intel HEX format, dual-file updates with stubs), how the device bootstraps code, and how configuration files integrate with the system. This is not script-kiddie territory; it implies access to documentation or reverse-engineering of the fuel system’s software. The fact that no security features (like code signing or encryption) hindered them might be due to the system’s inherent weaknesses, but knowing and exploiting that also required skill.
One especially sophisticated aspect is the conditional trigger design. Rather than a simple virus that activates anywhere, the logic bomb’s conditional checks (MAC list, AutoTrigger flag) show a nuanced understanding of operational security. The attackers built in a mechanism to avoid premature or unwanted execution – this way, if the malware leaked or was installed in a test environment, it might never activate, thus concealing its presence. Only under the exact conditions (which they can control) does it go off. This level of discipline in malware design (reminiscent of Stuxnet’s approach of checking for specific PLC signatures) is a strong sign of a well-funded, patient adversary.
In terms of signaling and psychology, the attack did carry a message. During the 2021 gas station attack (believed to be the same campaign), digital signs were hacked to display the message *“Khamenei, where is our gasoline?”* – a direct taunt to Iran’s leadership. This indicates the attackers weren’t solely interested in covert action; they wanted the impact to be public and embarrassing. By causing chaos on the anniversary of Iran’s 2019 fuel protests and making it obvious that a cyberattack was the cause, the adversary likely intended to undermine public trust in the government’s ability to protect critical services. The psychological deterrent here is aimed at the Iranian regime: it signals that “we can penetrate and disable your critical infrastructure at will,” potentially to dissuade certain behaviors (as the Predatory Sparrow group insinuated, it was in response to Iranian regional aggression).
Attribution and Comparison to Past Attacks
All evidence from this attack points to a highly capable adversary, most likely associated with Israeli cyber operations. Iran itself publicly blamed foreign countries and often implicates Israel or the US for such incidents. The group Predatory Sparrow, which claimed related attacks, is widely believed to be either an Israeli unit or closely aligned with Israeli interests. Their operations (attacks on Iranian railways, steel plants, and petrol stations in 2021-2022) exhibit a similar style: using cyber means to cause physical-world disruptions and send political messages. In comparison to earlier known attacks on Iranian infrastructure, SILENT Trigger has some novel aspects:
- Use of Firmware Logic Bombs: Stuxnet (2010), the famous US/Israeli attack on Iran’s nuclear centrifuges, did manipulate PLC logic and had a trigger, but it did not outright wipe the PLCs; it subtly sabotaged the process over time. SILENT Trigger, on the other hand, is a blunt instrument – it wipes out the controllers entirely. This is more akin to a wiper malware (like the Shamoon virus used against Saudi Aramco in 2012) but applied at the firmware level of industrial controllers, which is unprecedented in publicly known cases. It shows a willingness to cause irreversible damage rather than just temporary disruption.
- Surgical Targeting in ICS domain: Previous Iranian infrastructure attacks, such as the July 2021 train system hack or the 2021 gas stations hack, did involve some targeting (e.g., posting the Supreme Leader’s phone as a prank in train schedules). However, the MAC-filter technique in SILENT Trigger is a more fine-grained targeting method at the device level, not seen in earlier attacks. This indicates the attackers had detailed knowledge of the network down to individual device IDs. It’s a step beyond what was observed in broader network attacks and demonstrates a surgical strike capability within an operational technology (OT) environment.
- Multi-Stage Supply Chain Compromise: The attack leveraged the software supply chain (configuration files, update tools) of the fuel system. While supply chain attacks are not new (e.g., the SolarWinds hack on IT systems), in the Iranian context earlier attacks like Shamoon or even the gas pump hack were thought to be more straightforward malware deployments. SILENT Trigger’s method of infiltrating the maintenance tool (“milload”) and using it to deliver payloads shows a deep understanding of how the victim manages their infrastructure – suggesting long-term reconnaissance or insider collusion. This approach is more complex than, say, deploying a single wiper executable on Windows PCs. It required manipulating FoxPro databases, registry settings, and custom firmware – a significantly higher bar of difficulty.
- Focus on Industrial Controllers in Civil Sector: Past attacks by Israeli-linked actors on Iran often targeted high-value strategic assets (nuclear facilities in Stuxnet, military or economic targets). Hitting gas station controllers, while definitely impactful on the public, is a novel target choice. It represents a broad targeting of civil infrastructure and daily-life services. This could be seen as an escalation or expansion of the cyber battlefield. It’s also a test of Iran’s incident response in the civil domain. By bricking many controllers at once, the attackers forced Iran into a highly visible scramble to manual operations (reports noted technicians had to activate manual fuel pumps as a fallback). This approach contrasts with, for example, the Triton attack (attributed to likely Iranian or Russian actors) on a Saudi petrochemical plant in 2017, which aimed to sabotage industrial safety systems but did not broadcast its effects. SILENT Trigger was loud in its outcome, if silent in its infiltration – a conscious choice to make a statement.
In conclusion, the SILENT Trigger operation exhibits hallmarks of an Israeli state-sponsored cyber campaign: it is precise, technically advanced, and aligned with strategic objectives to undermine Iranian capabilities and morale. Its novelty lies in marrying an ICS firmware attack with IT-side identity spoofing and in the scale of disruption achieved against a civilian target. The attack’s success also underscores the fragility of systems that lack basic protections (like signed firmware or encrypted configs). From a strategic lens, SILENT Trigger not only accomplished immediate disruption but also likely serves as a deterrent message. It tells the Iranian leadership that key public services can be struck and taken down remotely, at will, by adversaries with the sophistication of Israel’s cyber units. This adds pressure on Iran in the ongoing covert cyber conflict between the nations, pushing that conflict squarely into the daily lives of ordinary citizens (queues at gas stations) and thereby into the public consciousness. Such psychological impact – achieved through technical means – is a defining feature of this attack and marks an evolution in the cyber hostilities in the region.
Sources: The analysis above is based on the forensic details provided in SILENT_Trigger.pdf (including disassembly of malicious firmware and config files) and open-source reporting on related infrastructure cyberattacks. The combination of technical evidence and geopolitical context paints a comprehensive picture of SILENT Trigger as a deliberate, state-of-the-art sabotage campaign.









You must be logged in to post a comment.