Social media and AI bots explode

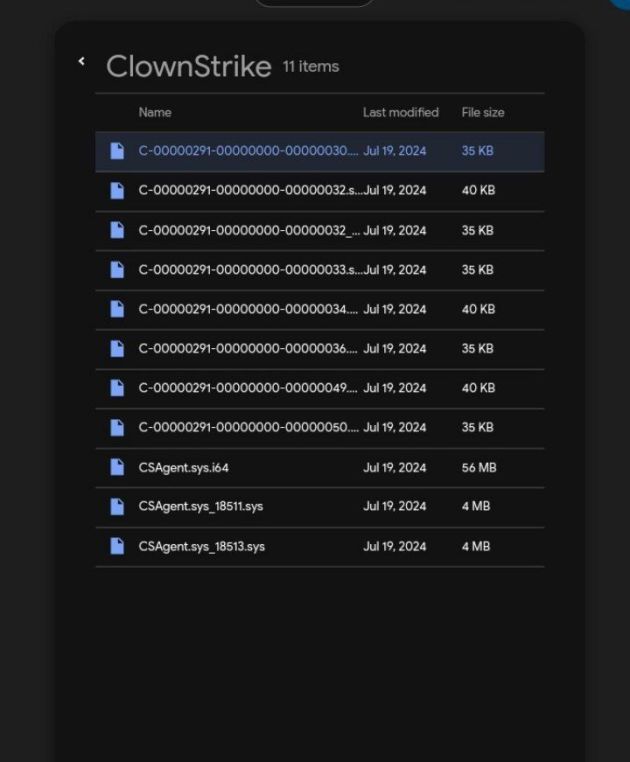
وارد safe mode بشوید. فایل معیوب را حذف کنید
del “C:\Windows\System32\drivers\CrowdStrike\C-00000291*.sys”
—————————————
کاربرانی که خطای CSAGENT.SYS با صفحه آبی رنگ دارند:
حالت safe mode
بروید
تغییر نام بدید CSAGENT.SYS to CSAGENT_OLD.SYS
توی مسیر
windows/system32/drivers/Crowdstrike/CSAGENT.SY


The Microsoft-CrowdStrike disaster underscores the catastrophic impact of a single point of failure within a cybersecurity framework, exacerbated by a lack of rigorous change and release management and inadequate testing before deployment.
Вы помните, что случилось с Solarwinds?
Теперь посмотрите Crowdstrike и убедитесь, что никогда не стоит доверять безопасности американских и израильских продуктов!
The decision to grant CrowdStrike’s “rootkit” excessive trusted access as a requirement for use has led to severe repercussions, with potential lawsuits and significant monetary losses on the horizon.
Global Scale of the Issue
Around — one billion computers are affected globally, with the majority being corporate machines. Businesses face massive operational disruptions due to the extensive reach of this issue.
Severity of the Problem —
The problem is far from a minor inconvenience. Each affected computer requires a complex recovery process, demanding more than a simple restart. The situation highlights the profound flaws in the deployment strategy and the dire consequences of insufficient testing.
Recovery Process —
Every affected computer must undergo a reboot in fail mode, followed by the manual removal of a specific driver. The labor-intensive process underscores the critical need for robust recovery mechanisms that handle such widespread issues without manual intervention.
Corporate Restrictions —
Corporate computers typically impose strict restrictions, preventing employees from performing technical tasks. The limitation places an overwhelming burden on IT departments, already stretched thin by the sheer number of computers needing immediate attention.
User Competency Concerns —
Even if users were permitted to perform the recovery tasks, many lack the necessary technical skills. The moderately complex procedure, which includes operations like file management, poses a significant challenge to the average user.
Scale and Impact —
The unprecedented scale of the problem, affecting a billion computers, threatens to disrupt business operations substantially. The resulting downtime and productivity losses could have severe financial implications, further highlighting the risks associated with inadequate change management and testing protocols.
Critical Analysis —
Granting CrowdStrike’s ‘rootkit’ excessive trusted access without thorough testing and change management has proven disastrous. The incident calls for an urgent reevaluation of security strategies, emphasizing the importance of resilient, multi-layered defense mechanisms. Businesses must prioritize rigorous testing and change management to prevent similar catastrophes and ensure a secure, stable environment. Potential lawsuits and monetary losses underscore the need for accountability and the adoption of best practices in cybersecurity.
The disaster highlights the critical importance of comprehensive change and release management, rigorous testing, and the adoption of resilient security strategies to prevent similar issues in the future.






You must be logged in to post a comment.