24 февраля 2024 год
—–BEGIN PGP SIGNATURE—–
iQGTBAEBCgB9FiEED/QWqWKNTn7Q9cGmBa++qhk4O2AFAmXaWRlfFIAAAAAALgAo
aXNzdWVyLWZwckBub3RhdGlvbnMub3BlbnBncC5maWZ0aGhvcnNlbWFuLm5ldDBG
RjQxNkE5NjI4RDRFN0VEMEY1QzFBNjA1QUZCRUFBMTkzODNCNjAACgkQBa++qhk4
O2BC7AgAm0B+aYUToLZbN+dpXDC6cgYW1LhsbrTb4cYQfQYg1L9R3HCLNkMs0ppm
BJ0DwG1N0QHh8I4ZNDelBI9aQaSTATqqDzseIE1FDqjW03em+EWU3qi9XUQU3fFO
J9MOQsi1XLiS17lqqkJ7o10LaIfaSoymbyBL0S43gMonDQ+sYNwXn39YSIQkKDjb
nllLwjFvlcK27aOBFOPZ27wipgW8BhrorThKypSGKVZpXm5ffO8Hh9XJfSUqiaDy
645ubDdFEPyBjoDG+jLvhm9tUchBnoNlZoLWUgFHbr9gnOmmIrxc50ZVTtKuteO0
Tjw2L7GTaSK4rNJNCAbAWMdZpVhtmQ==
=XV1G
—–END PGP SIGNATURE—–
The message details a cybersecurity incident involving penetration testing of the author’s servers, leading to unauthorized access and data compromise. On February 19, 2024, the author encountered a “502 Bad Gateway” error on their website, followed by a “404 Not Found nginx” error.
Attempts to resolve these issues through server restarts were initially unsuccessful. Later, it was discovered that the server passwords had been changed, and all information on the disks had been erased.
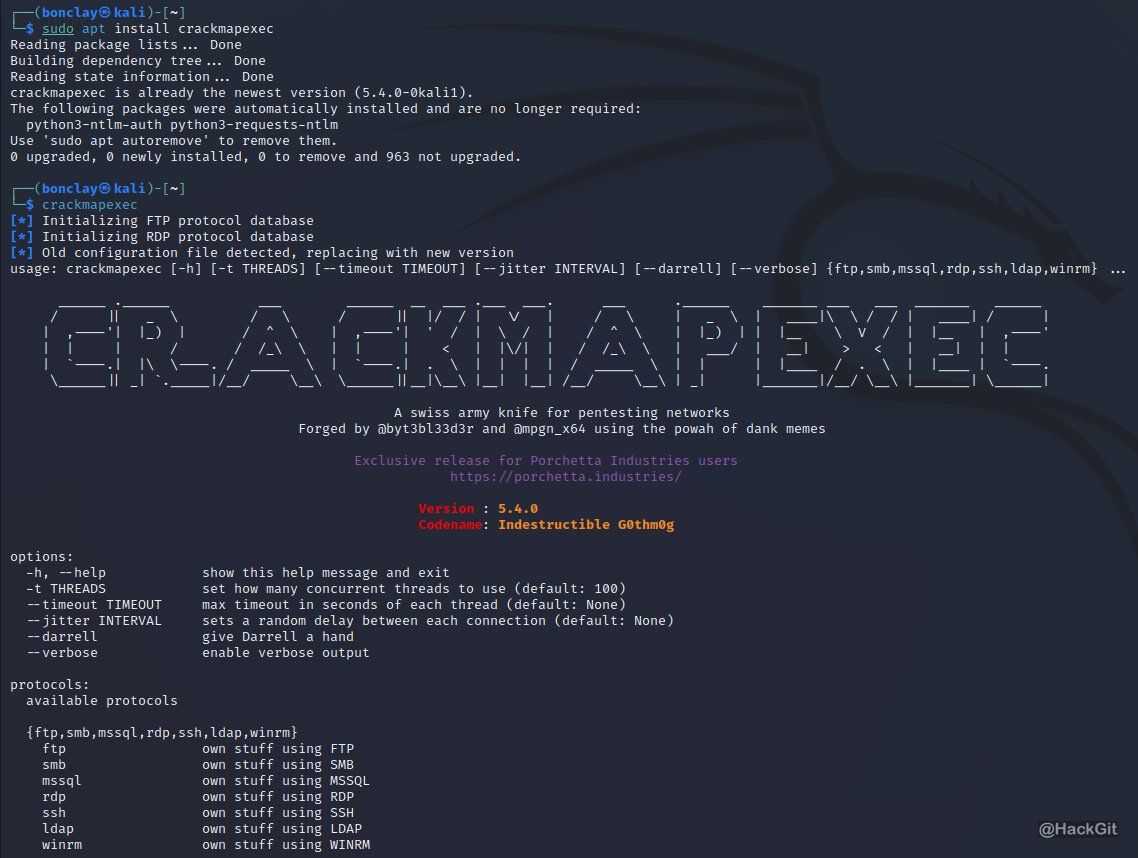
The breach was attributed to a failure to update PHP, with the servers running on PHP version 8.1.2, which had known vulnerabilities, possibly CVE-2023-3824. The author speculates that this vulnerability or another unknown (zero-day) exploit could have facilitated the unauthorized access, particularly to servers hosting admin panels, victim chats, and a blog server.
The author mentions the significance of this attack to themselves and others using vulnerable PHP versions, suggesting widespread potential for similar breaches. They express confidence that forums known to them were also compromised through PHP vulnerabilities based on information from informants and the nature of their breach.
A surprising turn in the narrative involves the FBI, which the author accuses of conducting the hack to prevent the leak of sensitive documents related to Fulton County (https://fultoncountyga.gov/) and Donald Trump’s legal cases, potentially influencing upcoming elections. The author expresses personal political views, including support for Trump, criticism of Biden, and the suggestion that the FBI acted out of political motives rather than cybersecurity concerns.
The message details the breach’s aftermath, including steps to secure the servers with the latest PHP version (8.3.3) and increased security measures to prevent future attacks. The author argues for the futility of simply updating PHP or changing servers and emphasizes the need for comprehensive security audits and infrastructure changes to avoid FBI surveillance and future breaches.
The author reflects on the broader implications of the incident, advocating for more aggressive cyberattacks against government (.gov) sectors to force the FBI to reveal vulnerabilities, thereby strengthening the author’s cybersecurity posture. The message concludes with a discussion of the FBI’s claims about decryptors obtained in the hack, the author’s financial gains from cybercriminal activities, and a defiant stance against FBI efforts to demoralize or stop their operations.
The narrative highlights the complex interplay between cybersecurity vulnerabilities, criminal activities, and potential political motives behind cyberattacks. It underscores the importance of regular software updates, comprehensive security practices, and the potential implications of cyberattacks on political and legal processes.
The text presents several vital points that merit focused attention for their implications on cybersecurity, influence operations, and the geopolitical landscape:
Vulnerability Exploitation
The breach was facilitated through an unpatched vulnerability in PHP, possibly CVE-2023-3824. Tunpatched vulnerability underscores the critical importance of timely software updates and vulnerability management as fundamental components of cybersecurity defense strategies. Exploiting known vulnerabilities remains a common attack vector, emphasizing the need for continuous monitoring and patching practices.
FBI Accusation and Political Implications
The author’s claim that the FBI orchestrated the hack to prevent the leak of sensitive documents related to Fulton County and potentially influential to U.S. elections introduces a complex narrative of cyber operations potentially used for political purposes. While these claims are unverified and could be seen as an attempt to deflect blame or create disinformation, they highlight the perceived role of state actors in cyber operations and the potential for cyber incidents to be intertwined with political narratives and influence operations.
Cybersecurity Posture and Response
The author’s admission of complacency due to financial success and subsequent lack of vigilance in updating critical infrastructure is a cautionary tale about the importance of maintaining a proactive and attentive cybersecurity posture, regardless of past successes or perceived security.
Decentralized Infrastructure and Recovery Efforts
The shift towards a decentralized infrastructure with multiple servers and the absence of PHP on backup servers as a means of rapid recovery and resilience against similar attacks in the future illustrates an adaptive approach to cybersecurity. This strategy could inform best practices for organizations looking to enhance their defensive measures against sophisticated cyber threats.
Operational Security and Cryptocurrency
The discussion around operational security measures, such as the use of cryptocurrency mixers for obfuscating financial transactions and the importance of comprehensive changes post-breach (including host, server, passwords, and user credentials), highlights the evolving practices within cybercriminal operations to maintain anonymity and financial security.
Cybercriminal Community and Tactics
The text provides insight into the mentality and tactics of cybercriminals, including the emphasis on attacking .gov sectors, the use of public vulnerabilities, and the importance placed on reputation within underground forums. This insight is valuable for understanding cybercriminal actors’ motivations, targets, and operational security considerations.
Law Enforcement and Cybercrime
Whether factual or speculative, the narrative around the FBI’s actions points to the ongoing cat-and-mouse game between cybercriminals and law enforcement agencies. It raises questions about the effectiveness of law enforcement strategies in penetrating cybercriminal networks and the potential for misattribution or collateral damage in cyber operations.
Focusing on these points can provide a more nuanced understanding of the current cybersecurity threat landscape, the challenges of attributing cyberattacks, the strategies employed by cybercriminals to evade detection and prosecution, and the potential use of cyber operations for political ends.
The original text, written in Russian, contains several phrases and colloquialisms that provide insight into the author’s style, potentially indicating regional dialects or specific subcultural affiliations within the Russian-speaking cybercriminal community. Here are some notable examples:
“купания в деньгах” (swimming in money)
This phrase suggests a lavish lifestyle, highlighting the author’s financial success. It is a colloquial way to describe someone with abundant money.
“сисястыми девочками” (girls with boobs)
This colloquial, somewhat vulgar expression reflects a casual and arguably disrespectful attitude towards women. It also hints at the author’s attempt to boast about their lifestyle.
“ФБР решились на взлом” (The FBI decided to hack)
This direct accusation against the FBI is not a colloquialism per se. However, the framing indicates conspiracy narratives often found in specific online communities, particularly anti-establishment or involved in illegal activities.
“не допустить утечки информации” (to prevent information leakage)
While not a colloquial phrase, this statement reflects a common concern in cybersecurity and intelligence narratives, emphasizing the strategic importance of information control.
“партнёр опубликовал пресс релиз” (the partner published a press release)
This phrase, while straightforward, is interesting in the context as it suggests a formal or semi-formal organizational structure within cybercriminal operations, where press releases or public statements are part of their operational protocols.
“качественно отмывать криптовалюту” (to launder cryptocurrency efficiently)
This phrase indicates the sophisticated financial operations involved in cybercrime, highlighting the use of cryptocurrencies and the importance of laundering to obscure the origins of illicit funds.
“атаковать .gov сектор” (attack the .gov sector)
Directly targeting government websites (.gov) is a specific and risky endeavor, suggesting technical capability and political or ideological motivation behind cyberattacks.
These phrases and the overall tone of the message suggest a mix of bravado, technical acumen, and a deep entrenchment in the cybercriminal ecosystem.
The language and colloquialisms are indicative of a person who is proficient in cyber operations and deeply embedded in a subculture that celebrates and normalizes these activities.