Convert simple output to hash for IDOR search
Sometimes, it is necessary to convert the input directly in the console to md5 / base64 / 32 etc. This can be especially useful when you’re looking for an IDOR and the endpoint has a hash value, like this:
https://targetdomain.com/user/3bf1114a986ba87ed28fc1b5884fc2f8
To solve this problem you can use a simple bash script with ffuf .
Suppose you have an endpoint that accepts an id parameter in md5 format. We can test it for IDOR using the following command, which generates a list of numbers from 1 to 1000:
seq 1 1000 | hashit md5 | ffuf -w – -u https://targetdomain.com/user/FUZZ
Insecure Direct Object Reference (IDOR) is a vulnerability that arises when attackers can access or modify objects by manipulating identifiers used in a web application’s URLs or parameters. It occurs due to missing access control checks, which fail to verify whether a user should be allowed to access specific data.

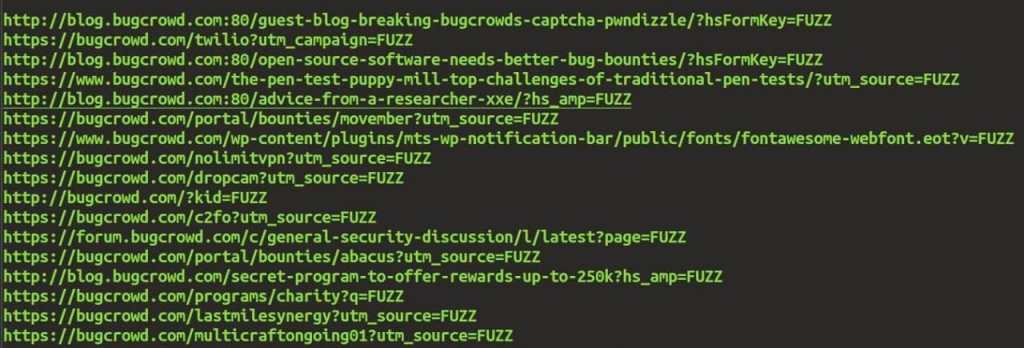
Automate the search for hidden parameters
This can really help you find new vulnerabilities, as some hackers and developers forget to check for them.
As for console tools to find hidden parameters, I like to use arjun and x8.
For automation, we save the list of URLs in the
web.list
file:
https://example.com
https://example.com/download
[…]
Arjun:
cat web.list | xargs -I% bash -c "arjun -u % -oT arjun.urls && cat arjun.urls >> arjun.list"
X8:
cat web.list | xargs -I% bash -c "x8 -u % -o x8.urls -O url && cat x8.urls >> x8.list"
As a result, we get a list of URLs with hidden parameters:
https://example.com?p=1&id=2
https://example.com/download?u=123
[…]
Don’t forget that you can use your lists with parameters for better results. They can be specified using the
-w
flag. Here are some of them:
• samlists
• arjun
• Param Miner






You must be logged in to post a comment.