BI.ZONE conducted a study and found that 40 organizations in Russia became victims of the Leak Wolf group. Hacktivists hack companies and post stolen data on their Telegram channel. Interestingly, they do not use malware and disguise themselves as real employees, which makes them difficult for cybersecurity services to track down.
According to the company, unlike other attackers, Leak Wolf does not pursue financial or espionage purposes. Their actions are motivated rather by “moral” motives.
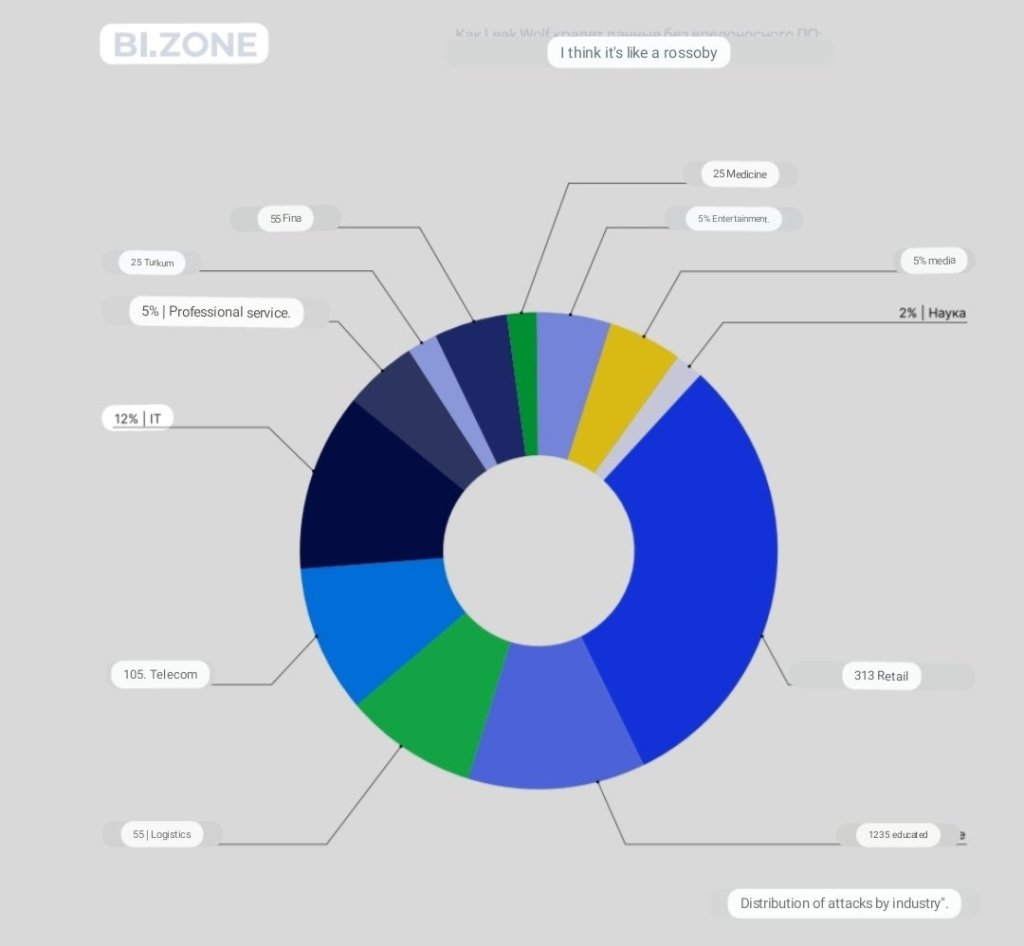
Leak Wolf became active in April 2022 and since then they have carried out successful attacks on over 40 Russian companies. Organizations in the areas of retail, education and information technology were particularly affected.
An interesting fact is that Leak Wolf did not try to use popular vulnerabilities or malware for their attacks. According to representatives of the Bi-Zone company, the attackers used the accounts of company employees or the access of IT contractors. So the attackers managed to go unnoticed for a long time. In order not to attract attention, the criminals also rented servers in Russia or used a VPN for remote access.
After infiltrating the company’s infrastructure, the attackers scanned the network, collected business-critical information (for example, the customer base), uploaded it to cloud storage, and published the link in their Telegram channel.
BI.ZONE noted that almost 60% of the incidents they encountered in 2022 were related to data breaches. The number of such attacks has quadrupled compared to the previous year. Leak Wolf’s actions reaffirm that attackers do not need to use malware to achieve their goals. Detection of such incidents is almost impossible without effective monitoring, and a proactive search for threats is also required.




You must be logged in to post a comment.