The SBU eliminated an enemy bot farm that created more than 500 accounts every day to spread Kremlin propaganda
Cyber specialists of the Security Service blocked a powerful bot farm that worked for the special services of the aggressor country. As a result of investigative and operational actions in Kyiv and Vinnytsia region, five of its organizers were exposed, who were conducting information sabotage against our state.
The specialized equipment of the enemy “cell” allowed daily registration of more than 500 anonymous accounts in various social networks, including those banned in Ukraine.
It was these fake accounts that were used to spread Kremlin propaganda in the Internet space.




First of all, the perpetrators massively spread disinformation about the situation at the front, and also justified the armed aggression of the Russian Federation.
Similar “dismissals” were submitted on behalf of “average” citizens who allegedly live in Ukraine, in particular in its temporarily occupied areas.
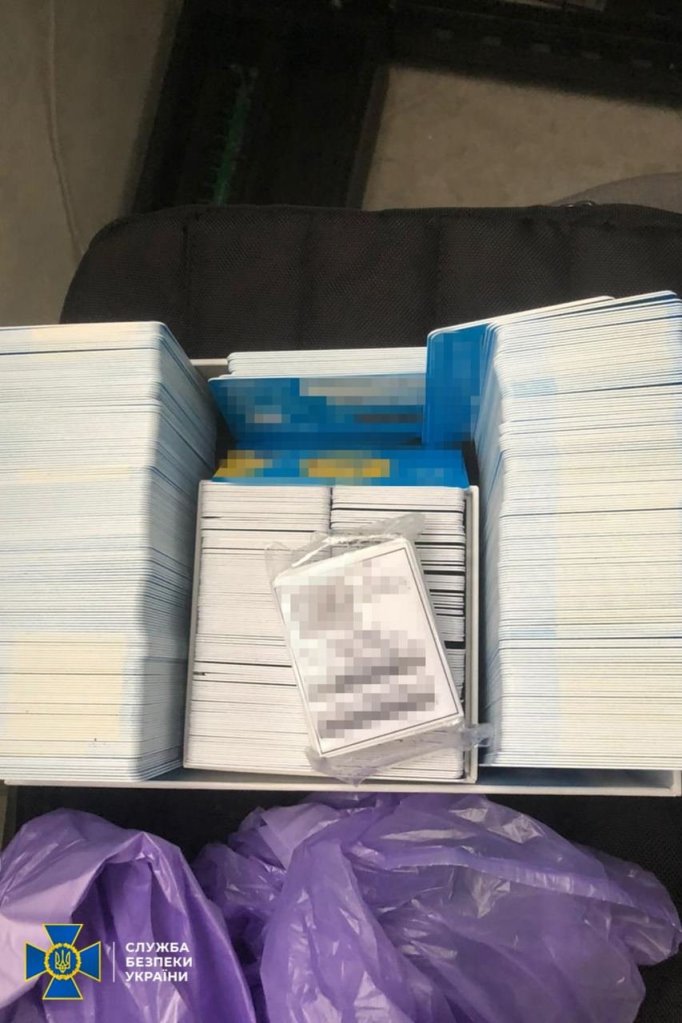
During searches of the administrator’s residence and the premises of the bot farm, law enforcement officers found:
- computer equipment with evidence of illegal activity;
- thousands of SIM cards of various mobile operators;
- special software.
The seized equipment was sent for examination.
According to the investigation, the enemy bot farm was organized by four residents of Vinnytsia region, and its technological support was carried out by a resident of Kyiv.
It was established that they offered “services” to “disperse” destructive content from the Russian Federation.
At the same time, the attackers’ main clients were representatives of the special services of the aggressor country, who used “bots” to impose racist ideology and Moscow’s lies about the war in Ukraine.
Through impersonators, the enemy bought anonymous accounts and used them to carry out information-subversive activities.
For each “bot”, the dealers were paid by electronic transfers that went through the payment systems of the Russian Federation.
Within the framework of criminal proceedings under part 5 of Art. 361 (unauthorized interference with the operation of electronic computing machines (computers), automated systems, computer networks or telecommunications networks) of the Criminal Code of Ukraine, the investigation is ongoing to find out all the circumstances of the offense and bring the guilty parties to justice.







You must be logged in to post a comment.