Strategic Investigative Report- Privatization of Federal Targeting Operations
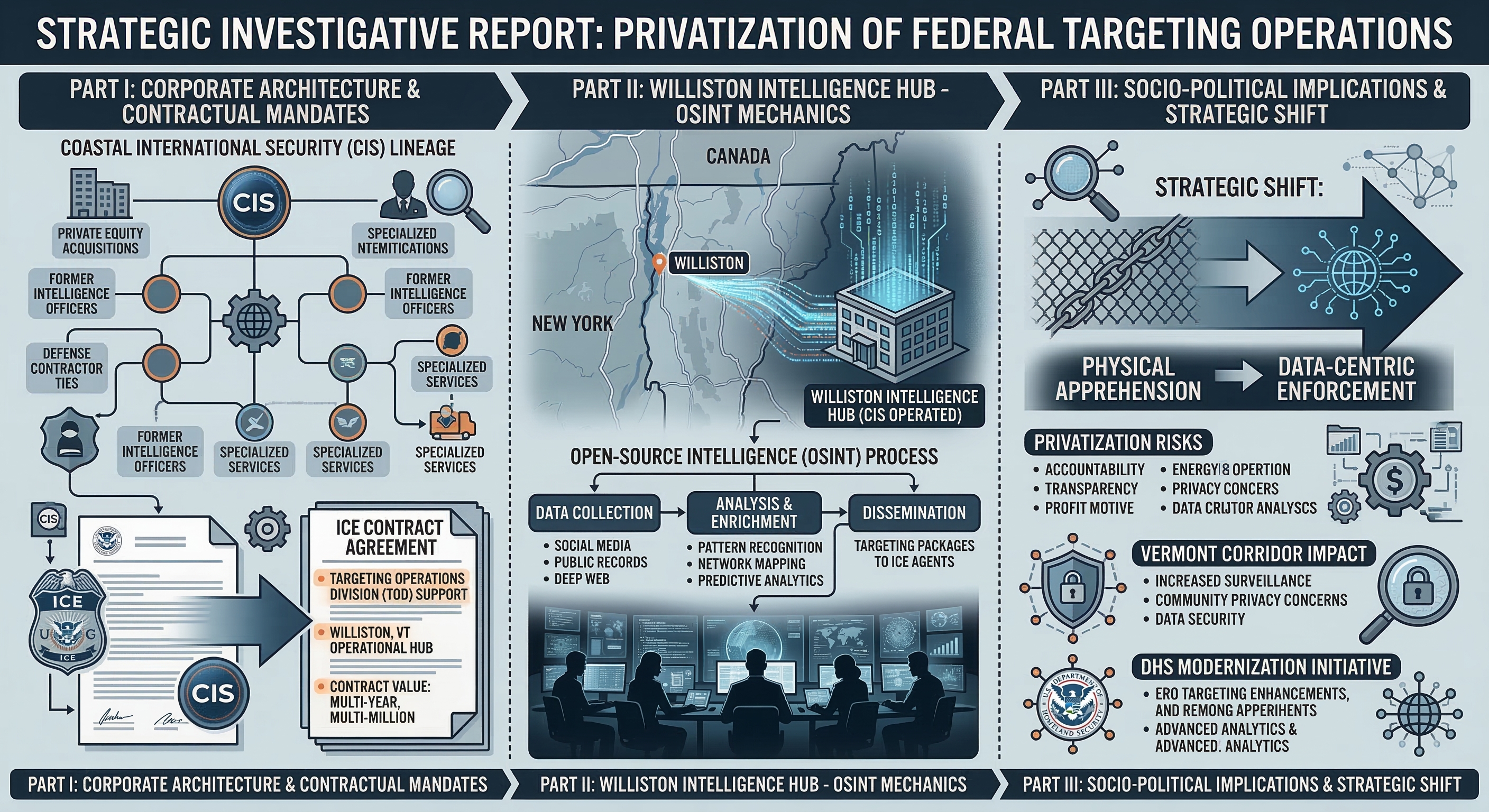
The landscape of American federal immigration enforcement has undergone a significant transformation, shifting from traditional physical apprehension models to a data-centric, intelligence-driven framework. At the heart of this evolution is the increasing reliance on specialized private contractors to perform functions previously reserved for government personnel. Coastal International Security (CIS), a firm with a storied and complex corporate lineage, has emerged as a critical partner in this domain, particularly through its operational support to U.S. Immigration and Customs Enforcement (ICE) in Williston, Vermont. The recent surge in high-level recruitment for Open-Source Intelligence (OSINT) analysts at this location is not merely a localized hiring event; it is a manifestation of a broader strategic initiative by the Department of Homeland Security (DHS) to modernize the Targeting Operations Division (TOD) within Enforcement and Removal Operations (ERO). The report examines the corporate architecture of Coastal International Security, the specific nature of its contractual mandates with ICE, the technical mechanics of the OSINT operations in Williston, and the socio-political implications of privatized digital surveillance in the Vermont corridor.
Corporate Architecture and the Evolution of Coastal International Security
Coastal International Security (CIS) represents a significant case study in the consolidation and specialization of the private security industry. Originally founded in South Carolina, the firm established an early reputation for providing high-stakes protective services to federal agencies, eventually expanding its operations to include maritime security and program management across 21 states and 23 nations. Its history is inextricably linked to Akal Security, a massive federal contracting entity founded in 1980 by members of the Sikh community in New Mexico. For decades, CIS operated as a wholly owned subsidiary of Akal, benefiting from its parent company’s “American success story” trajectory—a path that took Akal from a $1,200 small business loan to a billion-dollar empire with 15,000 personnel.
The modern corporate identity of Coastal International Security is defined by its integration into the Akima, LLC portfolio. Akima is a subsidiary of NANA, an Alaska Native Corporation (ANC) owned by more than 15,000 Iñupiat shareholders. The ownership structure is a pivotal factor in the company’s ability to secure and maintain complex federal contracts. As an ANC-owned entity, Akima and its subsidiaries, including CIS, navigate a unique regulatory environment that provides substantial advantages in the federal procurement process, particularly through the Small Business Administration’s 8(a) program.
| Entity Level | Organization Name | Primary Function |
| Parent Corporation | NANA (Alaska Native Corporation) | Holding company for Iñupiat shareholder assets |
| Intermediate Holding | Akima, LLC | Portfolio management of 40+ specialized subsidiaries |
| Operating Subsidiary | Coastal International Security, Inc. | Protective services, investigative analysis, and mission support |
| Affiliated Network | Akima Infrastructure Services (AIS) | Staff augmentation and specialized skill set delivery |
The transition of CIS from the Akal umbrella to the Akima portfolio reflects a broader trend of large-scale federal contractors reorganizing under ANC structures to use procurement preferences. While CIS continues to maintain operational hubs in Upper Marlboro, Maryland, and Lorton, Virginia, its corporate headquarters in Anchorage, Alaska, anchors it within the NANA ecosystem. The organizational depth allows CIS to offer “Fortune 500-level back-office support” while operating with the agility of a specialized mission-support firm.
The Alaska Native Corporation (ANC) Procurement Advantage
The strategic value of Coastal International Security to federal agencies such as ICE is significantly enhanced by its position within the Akima portfolio. Under the Federal Acquisition Regulation (FAR) and 13 CFR 124.506(b), the Small Business Administration (SBA) is authorized to award direct, sole-source contracts to 8(a) participants controlled by an ANC. The mechanism bypasses the traditional competitive bidding process, which can often be protracted and susceptible to legal protests. For an agency like ICE, which frequently operates under urgent national security priorities, the ability to award a contract—sometimes up to $100 million for Department of Defense (DoD) clients or $25 million for civilian agencies—without a formal “Justification and Approval” (J&A) is an invaluable tool for operational continuity.
Furthermore, the “Small Disadvantaged Business” and “Native American” credits associated with ANC-owned firms help federal agencies meet their mandated diversity and small-business utilization goals, ensuring that firms like CIS are not just service providers but strategic partners in the federal government’s compliance and socioeconomic engineering efforts. The integration of Iñupiat values—such as honesty, integrity, and treating everyone with dignity—is a central pillar of Akima’s corporate narrative, intended to provide a moral and ethical framework for its high-stakes security work.
The National Criminal Analysis and Targeting Center (NCATC) in Williston
The focus of current investigative interest regarding Coastal International Security is centered on Williston, Vermont. The location is not a standard field office but the site of the National Criminal Analysis and Targeting Center (NCATC), an intelligence hub operated by ICE’s Enforcement and Removal Operations (ERO). The NCATC is situated within the White Cap Business Park, a facility that houses a diverse array of tenants, including the Vermont Department for Children and Families and various local businesses.
The NCATC serves as the East Coast counterpart to the Pacific Enforcement Response Center (PERC) in Santa Ana, California. Together, these centers form the operational backbone of the Targeting Operations Division (TOD), a specialized unit created to “identify and locate aliens that pose a threat to public safety or national security”. The decision to place a primary intelligence node in Williston is likely a function of several factors, including the proximity to the Canadian border, the existing presence of the Federal Protective Service (FPS) Region 11 office, and the availability of a workforce capable of meeting the stringent background investigation requirements of the DHS.
Operational Mandates of the Targeting Operations Division (TOD)
The TOD mission is fundamentally defined by the need to overcome “countermeasures” employed by individuals seeking to evade immigration enforcement. These countermeasures often include the use of fraudulent identities, frequent residential moves, and the avoidance of traditional financial and government systems. As a result, standard law enforcement techniques have historically had “limited success” in locating high-priority targets.
The NCATC addresses this gap by providing a centralized environment where federal personnel and private contractors work side by side to perform “real-time and mission-critical analysis”. The facility’s primary output consists of person-specific information, including current addresses, vehicle registrations, identified associates, and behavioral patterns. The data is then synthesized into “lead packages” that are transmitted directly to field officers for enforcement actions, such as arrests and removals.
| Facility Role | Regional Responsibility | Staffing Profile |
| NCATC (Williston, VT) | East Coast Intelligence | Analysts, Site Leads, Program Managers |
| PERC (Santa Ana, CA) | West Coast Intelligence | 24/7 Operational Coverage |
The scope of work at the NCATC has expanded significantly in recent years, reflecting a shift toward “digital lead development”. Personnel are required to be proficient not only in standard law enforcement databases but also in the exploitation of “publicly accessible, open-source and social media platforms”. The move toward “proactive and modern enforcement tools” is viewed by ICE leadership as an “essential approach” to achieving national public safety priorities.
The OSINT Analyst Role- Technical Mechanics and Intelligence Methodologies
The recruitment efforts by Coastal International Security and its peers, such as Bluehawk, LLC, for OSINT analysts in Williston, reveal the highly technical and invasive nature of the work performed at the NCATC. These analysts are tasked with “conducting comprehensive research and analysis of various data sources to identify, develop, and initiate investigative leads”. The role requires a unique combination of investigative intuition, linguistic skill, and technical proficiency with a variety of digital tools.
Data Sources and Exploitation Tools
Analysts at the NCATC use a tiered approach to data collection, moving from public-facing information to restricted commercial and government databases. The primary categories of information sources include-
- Commercial Investigative Databases- Tools such as LexisNexis CLEAR and Thomson Reuters Accurint are used to verify historical addresses, utility records, professional licenses, and property ownership.
- Social Media Intelligence (SOCMINT)- Analysts exploit platforms like Facebook, Instagram, X (Twitter), and TikTok to identify current photographs, real-time location tags, and networks of associates.
- Law Enforcement Query Systems – Access to internal federal databases enables analysts to cross-reference investigative findings with prior criminal history, immigration records, and border-crossing data.
- Geospatial and Pattern-of-Life Tools – Analysts build “person/entity dossiers” that confirm identifiers and map the subject’s daily routines, enabling field agents to plan arrests at times and locations where the individual is most likely to be present.
The technical requirements for these positions often include a “working knowledge of immigration law, border security, and/or criminal justice policy”. Furthermore, proficiency in Spanish is “strongly desired,” as it enables analysts to monitor non-English social media accounts and community forums that may contain critical investigative information.
Intelligence Synthesis and Reporting
The work of an OSINT analyst is not merely about finding information but about ensuring its “accuracy, relevance, and timeliness”. Analysts are subject to strict “Quality Control” (QC) standards and are held to high expectations for “first-pass acceptance” of their lead packages by federal personnel. The process involves-
- Confirming Identifiers- Ensuring that the digital profiles being analyzed belong to the correct individual through the correlation of birthdates, family names, and physical descriptions.
- Documenting Corroboration- Providing “auditable citations” and screenshots of findings to ensure that the information can withstand legal scrutiny during removal proceedings.
- Prioritizing Leads – Managing cases across multiple urgency levels with “tight turnaround windows” for high-priority enforcement actions.
- Continuous Monitoring- Maintaining a “persistent” digital presence to detect changes in a target’s location or associations that may signal an attempt to flee.
The analytical pipeline is designed to “balance the government’s needs for timely products, accurate information, and quality products” in a “dynamic and fast-paced law enforcement environment”. The use of private contractors, such as CIS, allows the TOD to scale its operations rapidly in response to changing migration patterns or national security threats without the long-term commitment of hiring additional permanent federal agents.
Contractual Landscape- Recompetition and the Transition from Deloitte
The specific contract governing activities at the NCATC and PERC is currently in flux. Historically, these services have been provided by Deloitte Consulting, LLP, under contract number GS00Q14OADU113/70CDCR21FR0000022. However, the DHS has recently issued an acquisition forecast for the recompetition of this requirement, titled “Targeting Operations Division – Lead Development and Open-Source Intelligence Analysis”.
The Shift Toward Small Business Set-Asides
A critical development in this procurement is ICE’s decision to designate the recompetition as a “Full Small Business Set-Aside” under NAICS code 541990 (All Other Professional, Scientific, and Technical Services). The shift is significant for several reasons-
- Procurement Strategy- By moving away from a large global firm like Deloitte and toward a small-business set-aside, the agency is likely seeking to increase competition among specialized security firms and to meet federal mandates for small-business participation.
- Cost Management- Small business set-asides often result in more competitive pricing than large-scale consulting contracts, although the “Estimated Dollar Range” for this effort remains high, at $20,000,000 to $50,000,000.
- Operational Agility- Firms like Coastal International Security, which qualify under the size standards for these NAICS codes despite their affiliation with large parent organizations like Akima, are ideally positioned to capture this market.
| Procurement Detail | Current/Upcoming Contract Cycle |
| Contract Vehicle | PO (FAR Subpart 13.5) |
| Contract Type | Firm Fixed Price |
| Anticipated Solicitation Release | March 12, 2026 |
| Estimated Completion | July 8, 2031 |
| Primary Requirement | OSINT/SOCMINT Lead Development for TOD |
The Request for Information (RFI) issued in October 2025 specifically sought feedback from vendors on their capabilities in “social media/open-source research,” “technological modernization,” and “staffing retention strategies,” suggesting that ICE is not just looking for more analysts but for a partner that can help it integrate artificial intelligence (AI) and automated tools into its targeting workflow.
Ethical and Socio-Political Implications in the Vermont Corridor
The expansion of ICE’s digital surveillance capabilities in Williston has ignited a significant controversy within the local community and the broader human rights advocacy network. The White Cap Business Park, once a mundane commercial center, has become a “site of resistance” for activists who view the NCATC’s work as a violation of fundamental rights.
Activist Pushback and the “ICE Violates Rights Here” Movement
In early 2026, activists conducted a series of “noise demonstrations” and banner drops aimed at the facility. These groups allege that the NCATC is used to “spy on innocent people” and “identify targets for kidnapping and deportation”. The core of their concern is the invasive nature of social media surveillance, which they argue allows the government to map entire communities based on the digital interactions of a few individuals.
The anonymous activists involved in these protests have specifically targeted the facility’s landlord and local officials, calling for the cancellation of the long-term contract that allows ICE to operate in Williston. The local resistance is mirrored by national-level criticism from organizations that highlight the role of private corporations in what they term the “deportation profiteering” industry.
The Ethics of Privatized Surveillance
The use of private contractors to perform sensitive intelligence functions raises profound ethical questions. Critics point to the history of Coastal International Security and its parent organizations as evidence of the potential for abuse when profit motives are introduced into law enforcement and national security.
Of particular concern is the historical affiliation between CIS/Akal Security and various spiritual or yoga-based groups, which some argue creates a jarring dissonance with the firm’s involvement in the detention and deportation of immigrants. Furthermore, the company’s past legal troubles—including the $1.65 million fraud settlement with the State Department—have led to skepticism regarding its ability to self-regulate in the high-stakes environment of federal intelligence gathering.
The controversy is further compounded by the role of other private partners, such as Palantir Technologies, which provides software infrastructure that enables agencies like ICE to streamline identification and deportation. The combination of Coastal International Security’s analytical labor and Palantir’s algorithmic power has created what activists describe as a “digital dragnet” that is increasingly difficult for migrants to escape.
Historical Litigation and Regulatory Compliance
The reputation of Coastal International Security is shaded by significant historical litigation that continues to inform its relationship with federal overseers. In 2016, the company was the subject of a coordinated investigation by the Department of Justice (DOJ), the State Department’s Office of Inspector General (OIG), and the FBI.
The 2016 Fraud Settlement
The investigation centered on allegations that CIS defrauded the Department of State during the performance of a security contract. According to the DOJ, the company improperly obtained and used competitors’ private pricing information to underbid for contracts over multiple years. Additionally, the company was accused of submitting fraudulent bills and subsequently concealing the fraud from government contracting officials.
The president of CIS at the time, Curtis Wrenn, pled guilty to making false statements to the federal government, admitting that he “intentionally deceived” the State Department to prevent the company from getting a “black eye”. The company ultimately paid $1.65 million to resolve both criminal and civil allegations, including violations of the False Claims Act and the Procurement Integrity Act.
Modern Compliance and Security Standards
Despite this history, CIS has maintained its eligibility for federal contracts through extensive reorganization and the implementation of rigorous compliance programs, often supported by the Akima “shared services” model. Current job descriptions for OSINT analysts emphasize “strict adherence to all security, privacy, and data handling standards”.
The requirements for “Public Trust” or “Top Secret” clearances are a primary mechanism for ensuring that individual analysts are vetted and suitable for handling “Sensitive But Unclassified” (SBU) and “Sensitive Security Information” (SSI). The background investigation process for these roles is intensive, requiring candidates to have resided in the U.S. for at least 3 of the past 5 years and to undergo periodic reinvestigations every 5 years. The focus on personal integrity and professional conduct is intended to mitigate the risks associated with the privatization of sensitive law enforcement data.
Geographic and Logistics Analysis- Why Williston?
The NCATC’s location in Williston, Vermont, is a strategic choice that integrates several layers of DHS infrastructure. Williston is not only a hub for ICE analytical services but also houses the Burlington District Office for the Vermont Department for Children and Families and has historically served as a base for the Federal Protective Service (FPS).
| Location Feature | Relevance to ICE/DHS Operations |
| White Cap Business Park | Low-profile commercial setting for NCATC intelligence gathering |
| Harvest Lane Facility | Associated with U.S. Citizenship and Immigration Services (USCIS) |
| Proximity to I-89 | Logistics corridor connecting New England to the Canadian border. |
| FPS Region 11 | Regional oversight for federal facility protection |
The presence of the NCATC in Williston has also been linked to “ICE Air” operations, with contractors such as Akal and CSI Aviation Services providing logistical support for the actual removal of individuals identified by analysts in Vermont. The end-to-end integration—from the digital identification of a target in a Vermont business park to their physical removal via a private charter flight—illustrates the scale and efficiency of the modern privatized immigration enforcement machine.
Strategic Outlook- The Future of Privatized Intelligence in ERO
The trajectories of Coastal International Security and the NCATC point toward an increasingly automated, data-rich future for immigration enforcement. The DHS acquisition forecast for 2026 and beyond indicates a clear intent to “refine processes and modernize information technologies”.
The Integration of Artificial Intelligence
As part of the upcoming recompetition, ICE is researching the feasibility of incorporating “AI utilization” and “automated lead generation tools” into the Targeting Operations Division’s workflow, thereby reducing the manual labor currently performed by OSINT analysts and allowing them to focus on high-level synthesis and quality control. At the same time, algorithms handle the initial screening of social media and public records.
Expansion of Digital Surveillance Scope
The scope of information sought by the TOD is also likely to expand. Current plans already include gathering information about a targeted person’s “associates,” including “family members and coworkers,” to “determining someone’s whereabouts”. As digital footprints grow larger and more interconnected, the ability of private contractors to map entire social networks will become a central pillar of enforcement strategy.
The Resilience of the Private Contractor Model
The reliance on firms like Coastal International Security is unlikely to diminish, regardless of the political climate in Washington. The “Mission Focused” narrative of firms like Akima positions them as neutral executors of federal policy, capable of providing “mission support services to more than 100,000 military personnel, retirees, family members, and contractors”. The diversification ensures that even if specific immigration policies change, the underlying infrastructure of privatized federal security will remain a core component of the American government.
Strategic Conclusions and Investigative Summary
Coastal International Security is an illustrative example of the modern federal contractor- a firm with deep historical roots, a complex ownership structure through the Alaska Native Corporation framework, and a highly specialized mission in the realm of digital intelligence and targeting. Its presence in Williston, Vermont, is not a coincidence but a strategic deployment of analytical resources at the National Criminal Analysis and Targeting Center (NCATC) to support ICE’s Enforcement and Removal Operations.
The purpose of the OSINT analyst role at this location is to bridge the gap between digital data and physical arrest, providing the “real-time and mission-critical” information necessary to locate individuals who have successfully evaded traditional law enforcement efforts. The mandate is executed through the exploitation of social media, commercial databases, and internal federal records, all managed under a high-value government contract that is currently undergoing recompetition.
While the technical efficiency of this model is high, its implementation in the Vermont corridor has sparked a significant ethical and socio-political debate, highlighting the tensions between national security priorities and individual privacy rights. The historical legal challenges faced by CIS and its parent organizations serve as a reminder of the complexities involved in outsourcing the state’s power of surveillance and apprehension to private, for-profit entities. As the NCATC continues to evolve through the integration of AI and more expansive data collection methodologies, Coastal International Security will likely remain a central, albeit controversial, figure in the architecture of American federal enforcement.