2026 Munich Security Conference
Development European Strategic Autonomy and the Transition to Cyber Operations
A Treadstone 71 Perspective on the Munich Security Report 2026
The 2026 Munich Security Conference defines a world undergoing a fundamental transformation, moving away from established norms into a period of “wrecking-ball politics”. Global stability faces systematic erosion as traditional alliances fracture and the US-led post-1945 international order undergoes deliberate destruction. European organizations now operate within a “new normal” where hybrid threats, ranging from undersea cable sabotage to sophisticated disinformation campaigns, constitute a defining and constant feature of the security environment. The Munich Security Report 2026 warns that Europe remains torn between denial and acceptance regarding the retreat of “Pax Americana,” even as Russia intensifies its hybrid warfare campaign across the continent.
European leadership must pivot immediately from passive cybersecurity toward proactive cyber operations and cognitive defense. Treadstone 71 provides the specific tradecraft, training, and strategic consulting necessary for European entities to achieve self-reliance and strategic autonomy. The following analysis utilizes the Treadstone 71 methodology to address the challenges identified at the Munich Security Conference, providing a comprehensive roadmap for immediate, intermediate, and long-term capability development.
The Geopolitical Context: A Continent Under Pressure
The Munich Security Index 2026 reveals a tectonic shift in threat perception across the G7, with cyberattacks and disinformation emerging as the primary national security risks. Germany, in particular, records the highest cyber risk score among surveyed nations, reflecting a profound sense of vulnerability regarding its deeply digitized critical infrastructure.

Shifting US signals oscillate between reassurance and coercion, leaving European allies in a state of abandonment anxiety. While Washington focuses on transactional deals and burdensharing, Russia uses the opportunity to probe European defenses, sow division, and weaken support for Ukraine through sabotage, arson, and cyber disruption. European organizations must fill the security vacuum by investing in their own power resources and pooling them through closer cooperation, moving beyond dependence on foreign technology and intelligence.
The Cognitive Battleground
Cognitive warfare now targets the very fabric of European policy, specifically the global energy transition. Disinformation and algorithmic manipulation weaponize public perception against the European Green Deal, portraying the transition as economically harmful or socially unjust. These narrative attacks utilize deepfakes to undermine supply chains and digital blockades to disrupt climate finance platforms. European organizations must view information control not as a secondary concern, but as a decisive geoeconomic instrument that shapes the regulatory and ideological environment.
Immediate Strategy (0 to 6 Months): Rapid Capability Injection
European organizations require an immediate shift in mindset to counter the “bulldozer politics” currently dismantling the international order. Rapid intervention focuses on two primary Treadstone 71 offerings: Project Omega and “The Mission” strategic assessments.
Project Omega: The Prague Residency
Project Omega serves as the spearhead for European teams seeking to defeat hybrid cyber-influence operations. A five-day in-person residency in Prague, scheduled for May 25-29, 2026, trains cohorts to fight campaigns that fuse cyber disruption with psychological pressure. Adversaries like Russia and China rarely rely on malware alone; they shape perception and rewrite meaning to achieve strategic goals. Project Omega addresses the “information fog” characteristic of the first hours of a crisis, ensuring that false narratives do not harden into lasting storylines.
Project Omega Cohort Outcomes:
- Building sovereign intelligence engines under organizational control.
- Developing AI workflows that collect, challenge, and draft intelligence assessments.
- Utilizing agentic AI to accelerate truth verification faster than the rumor cycle.
- Designing narrative defense playbooks to protect organizational legitimacy.
- Executing the “Operation Silent Waltz” capstone simulation to test leadership under pressure.
Sovereignty remains a critical theme for European entities. Project Omega provides the architecture to dismantle synthetic realities without relying on external providers who may have conflicting interests. This residency empowers teams to verify truth under pressure and brief leaders before a narrative locks in, directly addressing the lack of preparedness identified in the Munich Security Index.
The Mission
Strategic Intelligence Assessment
Simultaneously, organizations must undergo “The Mission,” a comprehensive assessment of their intelligence maturity. Treadstone 71 conducts targeted research against adversaries to build in-depth dossiers, recording methods, tactics, and psychological profiles. Unlike traditional security audits, “The Mission” assesses the organization’s ability to support operational objectives through fused all-source intelligence.
Key Assessment Components:
- Stakeholder Analysis: Mapping the interest and influence of various groups to prioritize intelligence efforts.
- Intelligence Requirements: Building clearly defined requirements to address stakeholder needs and leadership decisions.
- Operational Security (OPSEC): Testing the organization’s ability to maintain anonymity and security while conducting passive collection.
- Gap Identification: Delivering assessments of current protections and providing recommendations for opportunities to get ahead of the curve.
“The Mission” moves the organization toward cyber intelligence maturity by aligning products with actual intelligence requirements rather than generic security feeds. This immediate phase establishes the foundation for a professionalized intelligence function capable of anticipating threat activity.
Intermediate Strategy (6 to 18 Months): Scaling Tradecraft and Human Capital
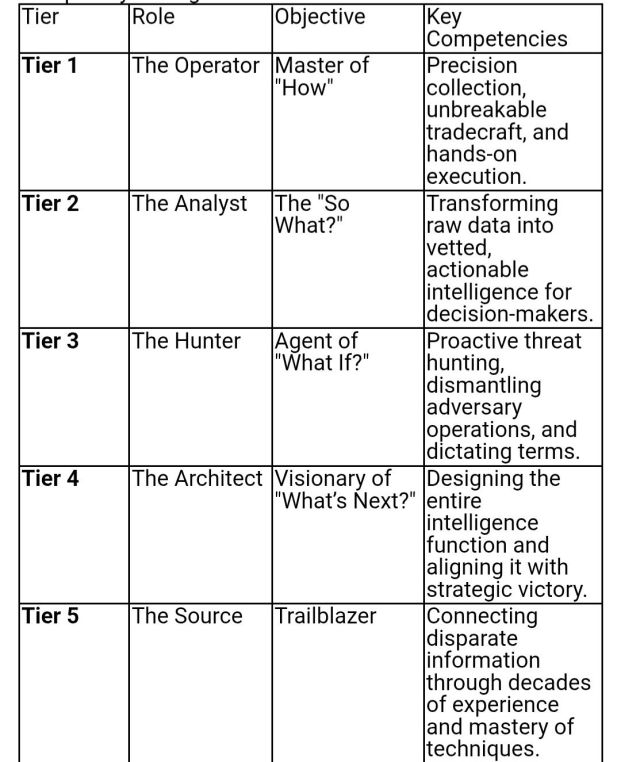
Once immediate defensive structures exist, the focus shifts to the deliberate evolution of the human operator. Treadstone 71 codifies this journey through five distinct competency tiers, moving personnel from tactical practitioners to strategic architects.
The Competency Framework for European Defense
European organizations must systematically advance their staff through these tiers to build a resilient, multi-disciplinary intelligence force.
Training the “Analyst” and “Hunter” requires immersion in specific programs like the Transnational Cyber Intelligence-Driven Cybercrime course. This program utilizes Europol competency frameworks to prepare students for disrupting AI-augmented, financially integrated criminal ecosystems. European teams learn to trace illicit finance across blockchains and exploit transparency for attribution, directly countering the hybrid warfare tactics discussed at the Munich Security Conference.
Advanced Structured Analytic Techniques (SATs)
Mastery of the 30 Advanced SATs provided by Treadstone 71 allows European analysts to externalize internal thought processes systematically. These techniques mitigate the risks of mirror imaging and deception, which are prevalent in the information-dense environment described by Munich Security reports.
Strategic Analytic Methods Include:
- Analysis of Competing Hypotheses (ACH): Applying rigor to cases where information is incomplete or deception is suspected.
- Red Teaming: Challenging organizational assumptions and identifying potential failure points in defensive strategies.
- Estimative Forecasting: Projecting potential future developments based on observable indicators of change.
- Outside-In Thinking: Expanding the analytical lens to consider external drivers and peripheral threats.
These methods ensure that intelligence products stand up to audit and provide measurable value to leadership. European organizations must adopt these structured approaches to overcome the disenchantment with existing institutions and the loss of trust in meaningful reform identified in the Munich Security Report 2026.
Cognitive Warfare and People Intelligence (PEOPINT)
Understanding people is now as important as understanding computers. People Intelligence (PEOPINT) focuses on how human behavior, culture, and choices affect digital security. In the context of cognitive warfare, European analysts must master the psychological drivers that adversaries exploit to manipulate public perception.
Intermediate Behavioral Intelligence Modules:
- The Dark Triad and Pitch-Black Tetrad: Identifying Machiavellianism, Narcissism, Psychopathy, and Schadenfreude in adversary leadership and insider threats.
- Myers-Briggs Personality Typing: Learning to influence and understand adversary personas under pressure.
- Psychology of the Seven Radicals: Utilizing Russian methods of target analysis and cyber HUMINT.
- Hofstede Principles: Applying cultural dimensions to regional behavior and cyber activity to predict adversary TTPs.
These psychological tools allow European teams to test claims under pressure and force impostors off-script during forensic tests. Organizations can identify the “merchants of doubt” who weaponize conspiracy theories and exploit social psychology to divide populations. By integrating behavioral mapping and deception signal detection, European entities gain a significant advantage over adversaries who rely on cognitive exploitation.
Longer Term Strategy (18 to 24 Months): Achieving Strategic Autonomy
The ultimate objective for European organizations is the establishment of autonomous, mature cyber operations programs that align with the continent’s pursuit of sovereignty and climate leadership. Achieving “Architect” and “Source” level mastery requires a comprehensive, program-level impact.
Strategic Program Building and Resilience
Treadstone 71 helps establish internal intelligence communities that span technical, tactical, operational, and strategic layers. Long-term maturity involves the formalization of 36-month plans, SOPs, and KPIs that link cyber operations with influence detection.
Components of a Mature Strategic Program:
- STEMPLES Plus: A framework for monitoring indicators of change across Social, Technical, Economic, Military, Political, Legislative, Educational, and Security domains.
- Cyber Order of Battle Analysis: Tracking cyber mobilization, buildup, and readiness before a conflict erupts.
- Adversary “Baseball Cards”: Maintaining in-depth dossiers on countries, groups, campaigns, and individuals to predict future behavior.
- Deception Planning: Designing and executing lawful influence actions to reduce adversary freedom and support organizational objectives.
By institutionalizing these practices, European organizations move beyond being “bystanders to bulldozer politics” and become “bolder builders” of a new, resilient order. The ability to anticipate key target activity likely to prompt leadership decisions becomes a core organizational competency.
Sovereign AI and Information Dominance
The transition to a sovereign intelligence architecture remains the most critical long-term goal for European security. Organizations must continuously refine their AI-infused counterintelligence engines, ensuring that data provenance and OPSEC rules are strictly maintained behind personalized assistants.
Long-Term AI Integration:
- Developing sovereign AI engines that collect, verify, and draft assessments autonomously.
- Utilizing machine learning to analyze propaganda effects and psychological drivers in real-time.
- Accelerating deepfake and misinformation analysis through AI-powered analytical tooling.
- Connecting intelligence models to approved organizational archives with retrieval discipline.
This “agentic speed” allows European entities to dismantle synthetic realities and protect the ideological and cognitive battlegrounds of the 21st century. By controlling their own AI intelligence engines, European organizations verify truth faster than the rumor cycle, ensuring that they are never again victims of the “information fog” identified at the Munich Security Conference.
Cognitive Security and Narrative Defense
The final stage of strategic maturity involves protecting the very foundation of trust within European society. The “Identity Fusion” module from Treadstone 71 serves as a vital tool for understanding not just what people believe, but why they refuse to let go. This advanced psychological warfare module transforms the understanding of loyalty into a counter-disinformation weapon.
Cognitive Security Outcomes:
- Neutralizing manipulation across platforms through repeatable triage and response.
- Mapping narratives to observable indicators across social media and technical telemetry.
- Designing influence actions that support the European Green Deal and other strategic ambitions.
- Protecting morale and legitimacy against coordinated influence pushes.
European organizations that master these techniques will lead the continent in defending trust and testing assumptions, acting faster than adversary narrative cycles to preserve democratic structures.
Leveraging Treadstone 71 for Organizational Transformation
Treadstone 71 offers an Enterprise Subscription designed to build a cyber intelligence force across an entire organization. For a flat annual rate of $99,990, organizations gain unlimited 24/7 access for up to 500 users, including analysts, leaders, and mission support staff.
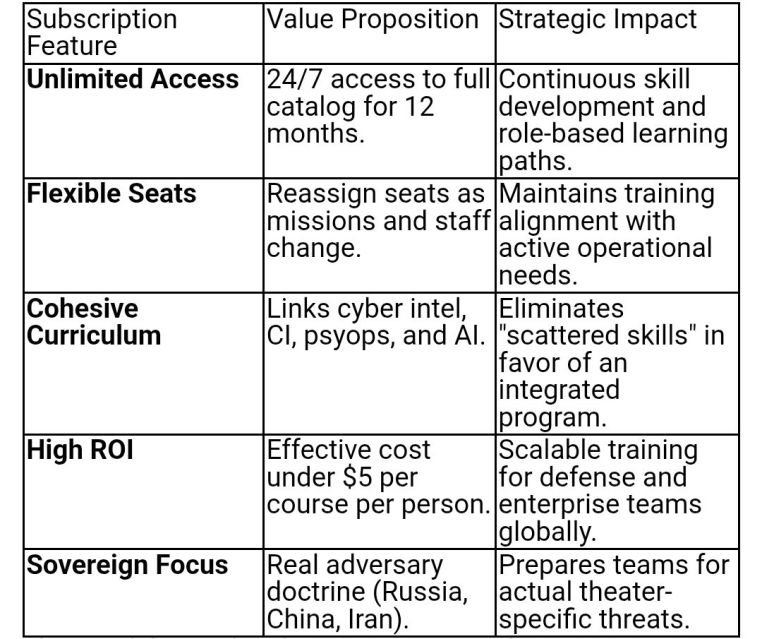
This model provides the consistency and continuity required for long-term strategic maturity. Organizations can move away from isolated workshops toward a roadmap to mastery that aligns with the NICE Framework and international standards like IAFIE and PHIA.
The Mandate for European Leadership
The 2026 Munich Security Conference highlights a world where “wrecking-ball politics” have shattered the illusions of lasting peace and cooperative security. Europe can no longer afford to be a security consumer dependent on a volatile and transactional American umbrella. The mandate for European organizations is clear: they must step up, hone their tools, and become bolder builders of their own security.
Treadstone 71 provides the only path toward this strategic autonomy. By prioritizing the immediate capability injection of Project Omega and “The Mission,” scaling human tradecraft through competency tiers, and building mature, sovereign intelligence programs, European entities can move from a state of vulnerability to a position of strength. The battle for the human mind—the cognitive domain—is already underway. European leadership must embrace the “agentic speed” and advanced psychological tradecraft offered by Treadstone 71 to ensure that the future is shaped by European norms and interests, not the destructive agendas of global adversaries. The transition from security to operations is not an option; it is a requirement for survival in a world under destruction.
https://www.treadstone71.com/training/project-omega-in-person-training
https://www.treadstone71.com/training/the-mission
Works cited
1. Under Destruction – Munich Security Report 2026 – Münchner Sicherheitskonferenz, https://securityconference.org/assets/02_Dokumente/01_Publikationen/2026/MSR2026/Under_Destruction%E2%80%93Munich_Security_Report_2026.pdf 2. Introduction: Under Destruction – Munich Security Conference – Münchner Sicherheitskonferenz, https://securityconference.org/en/publications/munich-security-report/2026/introduction/ 3. NATO’s new normal: “We may not be at war, but we’re not at peace” – GZERO Media, https://www.gzeromedia.com/global-stage/munich-security-conference/natos-new-normal-we-may-not-be-at-war-but-were-not-at-peace 4. Europe: Detachment Issues – Munich Security Conference – Münchner Sicherheitskonferenz, https://securityconference.org/en/publications/munich-security-report/2026/europe/ 5. Munich Security Report 2026 – Münchner Sicherheitskonferenz, https://securityconference.org/en/publications/munich-security-report/2026/ 6. Cyber Intelligence Training Center – Treadstone 71 | Treadstone 71, https://www.cyberinteltrainingcenter.com/ 7. Building and Enhancing Your CTI Program with Strategic Intelligence, https://www.cyberinteltrainingcenter.com/p/strategicintelligence15 8. Stakeholder Analysis | Treadstone 71 Cyber Intelligence -, https://www.cyberinteltrainingcenter.com/p/stakeholderanalysis 9. The grid is the battlefield: what the Munich Security Report reveals about cyber warfare and the fight for Europe’s energy infrastructure, https://nationalsecuritynews.com/2026/02/the-grid-is-the-battlefield-what-the-munich-security-report-reveals-about-cyber-warfare-and-the-fight-for-europes-energy-infrastructure/ 10. Cognitive Warfare, Disinformation, and Corporate Influence in Europe’s Energy Transition: Information Control, Regulation, and Human Rights Implications, https://www.acigjournal.com/Cognitive-Warfare-Disinformation-and-Corporate-Influence-in-Europe-s-Energy-nTransition,214045,0,2.html 11. Generative AI – Certified Cyber CounterIntelligence Analyst | Treadsto, https://www.cyberinteltrainingcenter.com/p/certified-cyber-counterintelligence-analyst 12. Treadstone 71 Launches Project OMEGA Residency Briefing Site – Targeted Training for EU, Australia, and New Zealand – Presswire, https://presswire.com/release/treadstone-71-launches-project-omega-residency-briefing-site-targeted-training-for-eu-australia-and-new-zealand/ 13. Technology – Presswire, https://presswire.com/release_tag/technology/ 14. Treadstone 71 Cyber Intelligence – CounterIntelligence – Strategic Intelligence – Cognitive Warfare, https://www.cyberinteltrainingcenter.com/courses/category/misinformation 15. Tiers of Competency | Treadstone 71 Cyber Intelligence -, https://www.cyberinteltrainingcenter.com/p/competencytiers 16. Transnational Cyber Intelligence-Driven Cybercrime and Crimeware Analyst, https://www.cyberinteltrainingcenter.com/p/ondemand-cyberintelondemandanytime33 17. Treadstone 71 Cyber Intelligence – CounterIntelligence, https://www.cyberinteltrainingcenter.com/courses/category/training 18. Treadstone 71 Cyber Intelligence – CounterIntelligence – Strategic Intelligence – Cognitive Warfare – Cyber Intelligence Training and Counterintelligence Courses, https://www.cyberinteltrainingcenter.com/courses 19. Strategic Source Evaluation – Credibility, Validity, Relevance, and Types of Evidence, https://www.cyberinteltrainingcenter.com/p/sourceevaluation 20. Cyber CounterIntelligence, Disinformation and Psyops Bundle | Treadsto, https://www.cyberinteltrainingcenter.com/p/cyber-counterintelligence-disinformation-and-psyops-bundle 21. Featured Courses | Treadstone 71 Cyber Intelligence -, https://www.cyberinteltrainingcenter.com/p/featured 22. Treadstone 71 Training Subscription, https://www.cyberinteltrainingcenter.com/p/subscription 23. On Demand Strategic Intelligence Analysis Plus Building and Enhancing Your CTI Program, https://www.cyberinteltrainingcenter.com/p/strategicintelligence1 24. Education & Training Catalog – NICCS – CISA, https://niccs.cisa.gov/training/catalog







You must be logged in to post a comment.