DOWNLOAD the TOOL
The artifact identified as VK Paranoid Tools.msi functions primarily as a specialized analytics engine for the Russian social platform VKontakte. Developers designed the software to conduct Open Source Intelligence (OSINT) operations against VK user profiles. The application extracts hidden friend lists, analyzes interaction patterns, and scrapes metadata not readily available through the standard user interface. While the operational intent appears legitimate—marketing analytics and user curiosity—the technical execution mirrors malware behavior.
The developers employ ConfuserEx to obfuscate the code, protecting their intellectual property. The obfuscation triggers heuristic engines within antivirus solutions, resulting in frequent false positives.
Analysts must treat the software as “grayware.” The capabilities allow for extensive data harvesting which adversaries could weaponize for surveillance. The risk profile elevates significantly if the provenance remains unverified, as threat actors often repackage such tools with genuine malware.

Provenance Verification Workflow
Verifying the authenticity of the MSI file requires a rigid, linear process to rule out trojanized versions. The analyst initiates the workflow by calculating the cryptographic hash of the file. Comparing the SHA-256 hash against known good values from the official distribution point or trusted repositories like VirusTotal establishes the initial baseline.
The next step involves digital signature validation. Legitimate software often carries a valid certificate. A missing or invalid signature warrants immediate isolation. The analyst then extracts the MSI contents using administrative tools to inspect the internal structure. Comparing the internal binaries against the expected file list exposes any injected payloads. Finally, executing the file within a controlled sandbox environment allows the analyst to observe network callbacks. Traffic destined for known developer domains validates the file, while connections to unrelated IPs indicate a compromise.
Risk Scoring Matrix
The risk assessment for this specific MSI relies on weighing the functional utility against the deceptive behaviors. A narrative breakdown of the scoring follows.
Low Risk Factors
The explicit purpose of the tool aligns with user analytics. The targeted platform, VK, operates within a specific regional context, limiting the global threat scope. Public documentation and a known developer community support the legitimacy claim.
Medium Risk Factors
The distribution method presents a moderate threat. Users often download the file from third-party repositories or forums rather than a centralized, secure app store. The lack of enterprise-grade signing certificates complicates trust establishment.
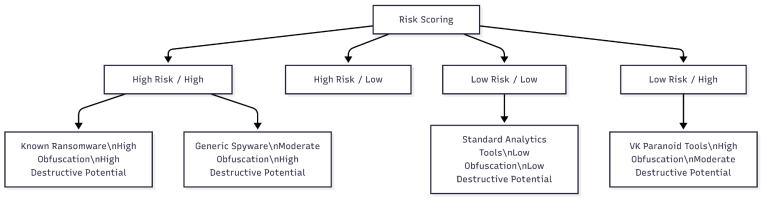
High Risk Factors
The software exhibits behaviors indistinguishable from malware. The use of ConfuserEx obfuscation actively hinders reverse engineering. The application modifies the Windows Registry to maintain persistence or store configuration data. The process enumeration capability allows the tool to scan running tasks, a technique often used by spyware to detect security software. The combination of obfuscation, registry manipulation, and process scanning generates a high-risk score, necessitating strict containment.
Chain of Custody Checklist
Maintaining forensic integrity demands a precise chain of custody from the moment of discovery. The analyst begins by documenting the exact time and location of the file discovery. The system name, file path, and user account associated with the file provide essential context.
The second phase involves cryptographic preservation. The analyst generates MD5, SHA-1, and SHA-256 hashes immediately. Documenting these hashes creates a permanent fingerprint of the evidence. The analyst then copies the file to a write-blocked storage medium to prevent accidental modification.
The third phase tracks all interactions. Every individual handling the evidence must log their name, the reason for access, and the duration of possession. The final transfer to long-term storage or legal counsel requires a countersigned transfer form. Any break in this documentation renders the evidence inadmissible and analytically suspect.
Behavioral Comparison Against Known Malware
Understanding the threat landscape requires contrasting VK Paranoid Tools against established malware families. The comparison focuses on execution flow, persistence, and network activity.
Execution Flow
VK Paranoid Tools executes with user privileges to interact with the VK API. Malware families like RedLine Stealer also execute with user privileges but immediately attempt to escalate privileges or inject code into other processes. The analytics tool stays within its own process boundary, whereas the malware moves laterally.
Persistence Mechanisms
The analytics tool modifies the registry to save user preferences or session tokens. Emotet or similar trojans modify the registry to ensure the malware restarts upon system reboot. The distinction lies in the registry keys targeted. The tool targets software configuration keys; malware targets the “Run” or “RunOnce” keys.
Network Activity
VK Paranoid Tools generates high-volume traffic to api.vk.com and developer domains. The traffic patterns appear consistent with API querying. Cobalt Strike Beacons or C2 agents generate low-volume, jittered traffic to obscure command and control servers. The analytics tool screams on the network; the malware whispers.





You must be logged in to post a comment.