Shifts in doctrinal language hide deeper truth. Labels changed from “Peace, Crisis, and War” to “Competition, Challenge, and Confrontation,” yet the underlying reality stayed constant: partners in public may act as rivals in practice. A handshake in daylight does not erase a shadow network already moving behind closed doors.
Silent gaps in diplomacy create false comfort. A pause in hostile messaging only means an operator shaped the environment away from view. Adversaries thrive in quiet phases because quiet phases limit attention. Operations run across cyber networks, influence channels, and covert liaison lines without sending loud signals. A competitor that speaks softly often advances the fastest.
Weak signals become the early warnings. A slight shift in messaging tone, sudden changes in trade patterns, sharper intelligence taskings, and small troop rotations create the early pattern. Analysts who train for weak-signal detection read those fragments as forward indicators. A strong program studies outliers, anomalies, and emerging inconsistencies before they align into clear threats.
A table shows the structure at play
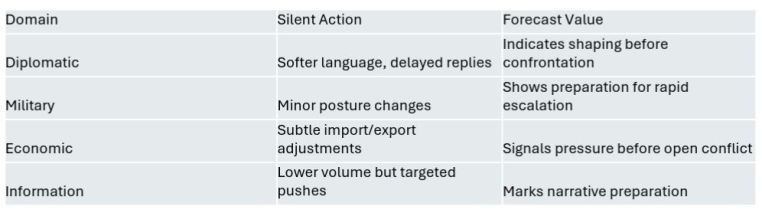
Predictive operators read these thin traces early. Preemptive action grows from disciplined pattern tracking, not from sudden reactions. Strategic competition grows in narrow spaces long before confrontation rises to the surface. Strong situational awareness comes from constant monitoring of faint movements that hint at larger plans.
A deeper layer opens next–how cognitive warfare doctrines treat silence as a weapon and how analysts map those silent intervals into structured threat forecasts.








You must be logged in to post a comment.