The reliance on mobile technology has become an undeniable aspect of modern life, extending its reach into the domains of military operations. This increasing integration, while offering advantages in terms of connectivity and information access, also presents a growing attack surface for cyber espionage targeting military personnel. The recent discovery of the Android.Spy.1292.origin malware, embedded within a counterfeit version of the popular Alpine Quest application, serves as a stark illustration of this evolving threat landscape, particularly within the context of the ongoing conflict involving Russia and the broader spectrum of cyber hostilities. This report aims to provide a comprehensive analysis of this malware incident, dissecting its technical capabilities, exposing the vulnerabilities within Russian military cybersecurity practices that allowed its proliferation, assessing its potential operational impact, and ultimately determining its implications for the security of personnel engaged in active conflict.

The Alpine Quest application, known for its utility as an offline topographic map tool, has gained considerable traction among Russian military personnel operating in active theaters. This popularity makes it a prime target for adversaries seeking to infiltrate the devices of military personnel and extract sensitive information, a tactic observed in previous instances of state-sponsored attacks targeting military personnel through compromised applications.
The initial detection of this malicious software was credited to Doctor Web, a Russian cybersecurity firm with a recognized expertise in identifying and analyzing Android-based threats.
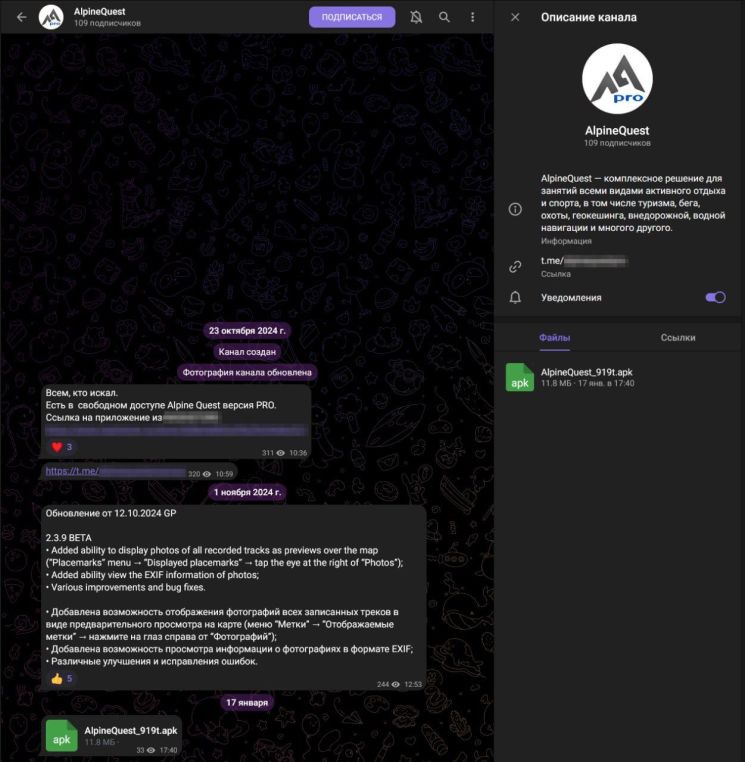
The immediate reaction to the discovery of Android.Spy.1292.origin within Russian online communities, particularly on platforms like VK, OK, and Telegram, revealed a significant level of alarm and a rapid dissemination of warnings.
The provided Russian text underscores the urgency of the situation, with explicit calls to action such as “⚠️ IMPORTANT! Pass it on to the military in the SVO zone!” This immediate and widespread concern among users, including those identifying as part of the “Digital Army of Russia,” highlights a degree of digital awareness within the targeted demographic, even if their subsequent security practices prove inadequate. Key warnings being circulated emphasized the critical need for military personnel using Alpine Quest in the Special Military Operation zone to verify the application’s source, strongly advising downloads exclusively from the official Google Play store and cautioning against obtaining it from third-party sources. The urgency of these warnings is further amplified by the instruction to share this information with those on the front lines, with the stark assertion that doing so “could save lives.” This reflects an understanding of the potentially life-threatening consequences of the malware’s capabilities. While the Rutube video itself was not accessible for direct analysis, its inclusion as part of the user’s query suggests that initial reporting and reactions likely also surfaced within Russian media channels. The emphasis within the Russian warnings on the specific dangers posed to military personnel is notable, citing the potential for “coordinate leak = security threat” and the possibility of “interception of military information.” This indicates a clear comprehension of the operational risks associated with the compromise of location data and communications in a military context. The warnings also acknowledge the “Internet Search channel” as the source of the information, underscoring the role that potentially unofficial news aggregators and social media platforms play in the dissemination of security-sensitive information within the Russian online sphere. This reliance on non-official channels for such critical alerts points to a potential gap in the formal communication structures within the Russian military for disseminating cybersecurity warnings effectively.
The malware in question, designated Android.Spy.1292.origin, was identified by cybersecurity specialists at Doctor Web. The method of its spread involved the distribution of counterfeit versions of the Alpine Quest application through unofficial third-party Android app stores and a deceptive Telegram channel. This reliance on unofficial sources by Russian military personnel to obtain applications represents a significant lapse in security, a vulnerability commonly exploited by malicious actors to distribute malware. The core functionalities of Android.Spy.1292.origin, as detailed by Doctor Web and outlined in their GitHub repository , include the surreptitious collection and transmission of sensitive user data. The malware is capable of stealing geolocation data in real time , a particularly critical capability in a military context where the precise location of personnel can have life-or-death implications. Furthermore, it is designed to exfiltrate phone numbers, correspondence, and various files stored on the infected device, with a specific focus on data from popular messaging applications like Telegram and WhatsApp. Adding to its dangerous nature, the Trojan possesses the ability to download and install additional modules, effectively allowing attackers to expand its spying capabilities and potentially introduce further malicious functionalities onto compromised devices. The Russian text provides further insight into the permissions sought by this malware, revealing its attempts to gain access to a wide array of sensitive information and device features. These include not only precise and coarse geolocation but also access to the device’s calendar, contact list, call logs, phone state information, external storage, user accounts, SMS messages (both reading and sending), and the ability to send SMS, which could potentially lead to financial losses for the user. The comprehensive nature of these requested permissions should have served as a red flag to users, indicating a level of access far exceeding the legitimate needs of a mapping application, had they been adequately trained in mobile security awareness.
The operational routine of Android.Spy.1292.origin, as detailed in Doctor Web’s GitHub repository , begins with requests for critical permissions upon initial launch, including access to external storage and a request to disable battery optimization for the application, a common tactic used by malware to ensure uninterrupted operation and persistence. Once these permissions are granted, the malware proceeds to log user contact data and information about all files stored on the device’s external storage, saving this collected information into specific vocabularies within its working directory, named resp_dir. For command and control communication, Android.Spy.1292.origin utilizes the Parse SDK to interact with its C2 server, located at hxxps[:]//detect-infohelp[.]com/parse/. The malware establishes a separate thread through its Serv class to initialize this connection, using hardcoded parameters for the C2 server address, application ID, and client key. Following this, it updates general user information and registers the infected device with the C2 server by calling the connectToBase method, transmitting data such as the current date, the user’s mobile phone number and associated accounts, and the application version. Subsequently, the malware employs the sendDataToSrv method to exfiltrate files to the C2 server. It systematically crawls the resp_dir directory and transmits the collected data logs, including the log of files and the log of phonebook contacts. A particularly concerning aspect of its operation is the requestTask method, which checks the C2 server for the availability of additional malicious modules. If the server confirms the presence of such modules, the Trojan proceeds to download them and dynamically execute them using the DexClassLoader, allowing for the runtime expansion of its malicious capabilities. Analysis by Doctor Web uncovered modules specifically designed for stealing user-specified files, particularly confidential documents.
In addition to the primary C2 communication, the malware also employs the pingTele method to redundantly transmit user information to a Telegram bot accessible via hxxps[:]//api[.]telegram[.]org/bot95:hij-_Z5HijN4y*/. The data sent to this Telegram bot includes the current date, user mobile phone number and accounts, and the application version. Furthermore, Android.Spy.1292.origin actively monitors the geolocation of the infected device through both GPS and mobile networks, sending updates to both the C2 server and the Telegram bot whenever the device’s location changes. This location logging occurs both upon application launch and through the onLocationChanged method. The malware also implements the noteLocation method, which records all location data to a separate file. To manage storage, this file is deleted and replaced with a new one once its size exceeds 100 megabytes. The SHA-1 hash for this specific malware sample is ce71efb93cf4d79bf431d8edfbae7b8b7b55fe44. Key network indicators of compromise include the C2 server domain, hxxps[:]//detect-infohelp[.]com/parse/, and the Telegram bot API endpoint, hxxps[:]//api[.]telegram[.]org/bot95:hij-_Z5HijN4y*/. The IP address 77[.]73.69[.]118 has also been identified as associated with this malicious activity. Unfortunately, access to the VirusTotal analysis for this specific sample was unavailable, which would have provided further insights into its detection rate across different antivirus solutions and potentially revealed additional behavioral characteristics.
The compromise of Russian military personnel through the Android.Spy.1292.origin malware highlights several critical weaknesses in their operational security procedures concerning the acquisition and use of mobile applications.
A primary failure lies in the apparent reliance on unofficial sources, such as third-party app stores and Telegram channels, for obtaining software. This practice fundamentally undermines security by bypassing any vetting processes that official app stores, such as Google Play, might employ, thereby exposing users to a significantly elevated risk of downloading malware. The allure of obtaining a “free Pro version” of a paid application like Alpine Quest appears to be a potent social engineering tactic that successfully enticed military personnel to download the compromised software. This suggests either a lack of adequate financial resources allocated for official software procurement within the Russian military or a prevailing culture of circumventing established protocols to obtain desired applications without incurring personal cost.
Furthermore, the incident underscores the apparent absence of secure software distribution channels specifically designed for military personnel. Without an official and secure mechanism for distributing approved applications, the Russian military lacks the ability to ensure the integrity and safety of the software utilized by its personnel, whether for operational purposes or personal use on devices that might also handle sensitive information. This absence indicates a significant gap in their cybersecurity infrastructure and policy framework concerning mobile device usage in potentially sensitive environments. The fact that personnel seemingly resort to public and unverified platforms like Telegram for obtaining applications highlights a failure to establish and enforce secure alternatives. The likely widespread infection also points to a deficiency in the implementation of basic digital hygiene practices among Russian military personnel. The failure to verify the legitimacy of application sources and to carefully scrutinize the permissions requested by applications before granting them indicates a lack of sufficient cybersecurity awareness and training within their ranks. Had personnel been adequately educated on mobile security best practices, the broad range of intrusive permissions sought by Android.Spy.1292.origin should have raised immediate suspicion. Several factors might contribute to the Russian military’s reliance on unofficial app stores and the challenges they face in secure software procurement. Russia has been actively pursuing the development of domestic alternatives to Western app stores like Google Play and Apple’s App Store, with initiatives such as RuStore. However, these domestic alternatives might not yet offer the same breadth of application availability, the same level of user convenience, or the same perceived access to advanced features as their Western counterparts, potentially driving users to seek software from less secure sources. Moreover, the imposition of international sanctions and restrictions on Russia’s access to Western technology could also limit the official avenues through which the Russian military can procure and update software, potentially forcing personnel to rely on unofficial and potentially compromised channels to obtain necessary applications.
Additionally, while the Russian government places a strong emphasis on controlling the flow of information within its national cyberspace , this focus might not have been effectively translated into robust security measures for the mobile devices used by individual military members, particularly concerning the acquisition and use of third-party applications. The priority might be on preventing external influence at a national level, rather than on securing the diverse array of personal devices used by military personnel at the tactical edge.
The intent behind the deployment of the Android.Spy.1292.origin malware against Russian military personnel strongly suggests a cyber espionage operation orchestrated by a state-sponsored actor. The primary objective is likely the clandestine gathering of intelligence on Russian military operations, personnel details, and equipment deployments, providing valuable insights to potential adversaries. The specific targeting of military personnel, achieved through the compromise of a mapping application known to be popular within their ranks, points directly to an intelligence-gathering motive focused on obtaining information pertinent to the ongoing conflict. The real-time exfiltration of geolocation data, coupled with the theft of communications and files, indicates an aim to gain immediate tactical insights into troop movements and operational activities. Furthermore, the compromise of personal information could be leveraged for future social engineering attacks targeting other military personnel or even their families. The sophistication of the malware, characterized by its modular design, use of a third-party SDK for command and control, and the employment of a Telegram bot as a redundant exfiltration channel, strongly suggests the involvement of a well-resourced and highly capable threat actor, most likely a state-sponsored entity with advanced cyber capabilities.
Non-state actors typically lack the extensive resources and strategic focus required for such a targeted and technically advanced campaign against military targets operating within an active conflict zone. The maliciousness of Android.Spy.1292.origin is evident in the broad scope of data it is designed to exfiltrate, encompassing not only location information but also personal contacts, a wide range of files, and the content of communications from popular messaging applications. This comprehensive data theft indicates a significant breach of privacy and security for the affected individuals. Moreover, the malware’s capability to download and install additional modules elevates its maliciousness, allowing attackers to dynamically expand its functionalities after the initial infection. This adaptability enables them to tailor the malware’s behavior to specific targets or evolving intelligence requirements, potentially leading to even more intrusive surveillance or the deployment of disruptive capabilities in the future. The lethality of this malware in the context of military operations cannot be understated. The compromise of sensitive location data poses a direct threat to the physical safety of military personnel. If this information falls into the hands of enemy forces, it could be used to precisely target Russian units with artillery fire, drone strikes, or ground ambushes, potentially resulting in casualties. The interception of military communications could expose critical operational plans, troop movements, logistical details, and other sensitive information, severely jeopardizing ongoing missions and the overall security of Russian forces in the field. This intelligence advantage could allow adversaries to anticipate Russian actions, develop effective countermeasures, and ultimately inflict greater losses. The potential for the malware to install further spying modules only exacerbates this lethality, as it could lead to the compromise of even more sensitive data or the introduction of capabilities designed to disrupt military operations directly.
Assessing the precise impact of the Android.Spy.1292.origin malware on Russian military personnel to date is challenging due to the unavailability of definitive infection statistics. However, considering the reported widespread use of the Alpine Quest application among their ranks , it is highly plausible that a significant number of individuals have inadvertently downloaded and installed the counterfeit Pro version from unofficial sources. This widespread adoption of the compromised application suggests a potentially large-scale intelligence breach for the Russian military, with a substantial portion of their personnel operating in active conflict zones potentially having their sensitive data exposed. The consequences of this exfiltrated data falling into the hands of adversaries are considerable. Detailed geolocation data could provide Ukrainian forces and their allies with invaluable targeting information, enabling them to conduct more precise and effective kinetic strikes against Russian military positions and assets. Compromised communications could offer deep insights into Russian operational plans, tactical deployments, logistical vulnerabilities, and even the morale and psychological state of their forces, providing a significant advantage in planning and executing counter-operations.
Furthermore, the personal information harvested from infected devices could be exploited for social engineering attacks, potentially targeting other Russian military personnel or their families to gain further access to sensitive information or to sow discord and undermine morale. While a definitive assessment of the damage remains elusive without access to classified Russian military intelligence, the potential for significant operational impact and security risks stemming from this malware incident is undeniable.
The incident involving the Android.Spy.1292.origin malware serves as a stark reminder of the persistent and evolving cyber threats targeting military personnel in modern warfare. The technical capabilities of this spyware, coupled with its deceptive distribution through unofficial channels, underscore the significant risks associated with the lax operational security practices within the Russian military concerning mobile application usage. The compromise of sensitive geolocation data and communications has the potential for severe operational impact, directly endangering personnel and undermining mission security. The weaknesses exposed, particularly the reliance on unverified software sources and the lack of adequate digital hygiene awareness, highlight systemic failures in their mobile security posture. This incident underscores the urgent need for the Russian military to implement more robust software procurement processes, establish secure channels for application distribution, and significantly enhance cybersecurity awareness training among its personnel, specifically addressing the risks associated with downloading and using third-party applications on devices that could be used in or near operational theaters. Ultimately, the Alpine Quest compromise illustrates the critical challenges that military organizations face in securing their personnel in an increasingly hostile digital environment, where even seemingly innocuous applications can be weaponized to devastating effect.
Table 1: Permissions Requested by Android.Spy.1292.origin and Potential Exploitation
Permission Name
Potential Malicious Use
ACCESS_FINE_LOCATION
Precise tracking of military personnel movements, revealing operational deployments and potential targets.
ACCESS_COARSE_LOCATION
Approximate tracking of military personnel locations, aiding in broader intelligence gathering.
READ_CALENDAR
Gathering information about schedules and potentially revealing operational timelines or meetings.
READ_CONTACTS
Identifying command structures, social networks, and gathering information for potential social engineering attacks.
READ_CALL_LOG
Understanding communication patterns and identifying key individuals within military units.
READ_PHONE_STATE
Obtaining device identifiers and phone numbers, potentially linking devices to specific personnel.
WRITE_EXTERNAL_STORAGE
Storing collected data and potentially installing additional malicious files or modules.
GET_ACCOUNTS
Identifying user accounts on the device, potentially revealing linked services and email addresses.
READ_SMS
Intercepting SMS messages, including potentially sensitive information or two-factor authentication codes.
SEND_SMS
Sending malicious SMS messages to other contacts, potentially spreading the malware or conducting phishing attacks.
Table 2: Indicators of Compromise (IOCs) for Android.Spy.1292.origin
IOC Type
Value
SHA-1 Hash
ce71efb93cf4d79bf431d8edfbae7b8b7b55fe44
C2 Server Domain
hxxps[:]//detect-infohelp[.]com/parse/
Telegram Bot API Endpoint
hxxps[:]//api[.]telegram[.]org/bot95:hij-_Z5HijN4y*/
IP Address
77[.]73.69[.]118





You must be logged in to post a comment.