The content contains a detailed roster in Arabic titled:
“لائحة وطنية بأسماء الأشخاص والكيانات المعنيين بتورطهم في الإرهاب أو تمويل الإرهاب”
(English: National list of individuals and entities involved in terrorism or its financing)
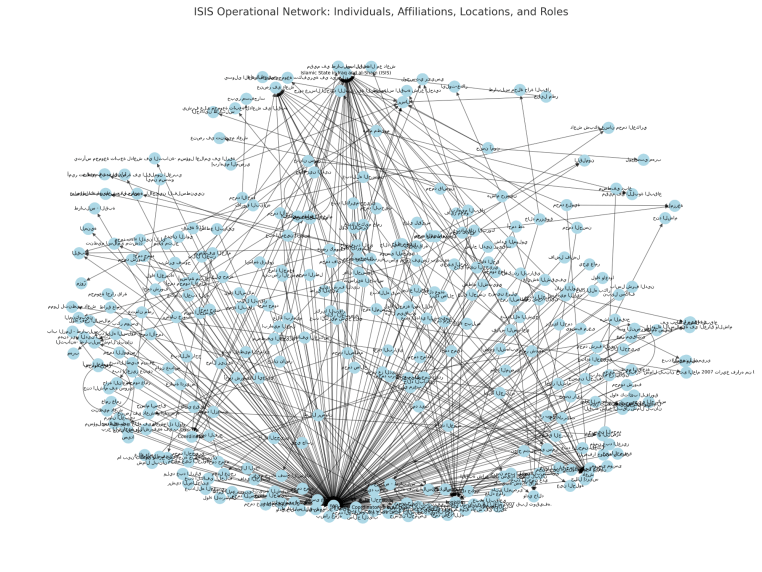
The data identifies individuals tied to ISIS (داعش), particularly its operations in Syria and Lebanon. Each entry includes biographical data, roles, affiliations, arrest information, and legal actions by Lebanese authorities.
Structured Elements from the Dataset—>
Names and Titles
Occupation or Function (e.g., Main Coordinator)
Parental Information (Father and Mother’s Names)
Birth Dates and Places
Nationality
Passport and ID details
Residence Locations (precise to neighborhoods or camps)
Date of Arrest and Circumstances
Categorization: “Natural Person”
Affiliation: Islamic State of Iraq and al-Sham (ISIS)
Date of Inclusion on List
UN Security Council Reference: 1373 (2001)
Legal Follow-up: Prosecutor’s Office and Military Tribunal
Additional Notes and Observations
Initial Observations
The dataset carries significant intelligence relevance. Lebanese internal security and counterterrorism authorities likely compiled it during a high-threat operational period from 2014 to 2016, the height of ISIS regional activity. Every entry ties back to either ISIS combat coordination, logistics, or facilitation within Lebanon, especially from the North (Tripoli region) and Beirut (Burj al-Barajneh and Ashrafieh), with strong Syrian connections (Raqqa being the origin for many).
Assessment Using Intelligence Analysis Methods
1. Source Reliability and Content Credibility (MIRAC)
The structured nature, legal references, inclusion of identity documents, and precise arrest records suggest access to primary Lebanese state security documentation. Reference to UNSC Resolution 1373 (which mandates counter-terrorism financing enforcement) supports credibility. Source reliability rates high, content very likely accurate.
2. Intent and Functionality of the List
The objective appears to support operational targeting, judicial processing, and internal security coordination. Each record reflects persons tracked or detained based on intelligence collection, direct arrest, or militant affiliations. The document holds probable links to intelligence fusion efforts involving internal Lebanese services and potentially UN counterterrorism branches.
3. Geographic Analysis
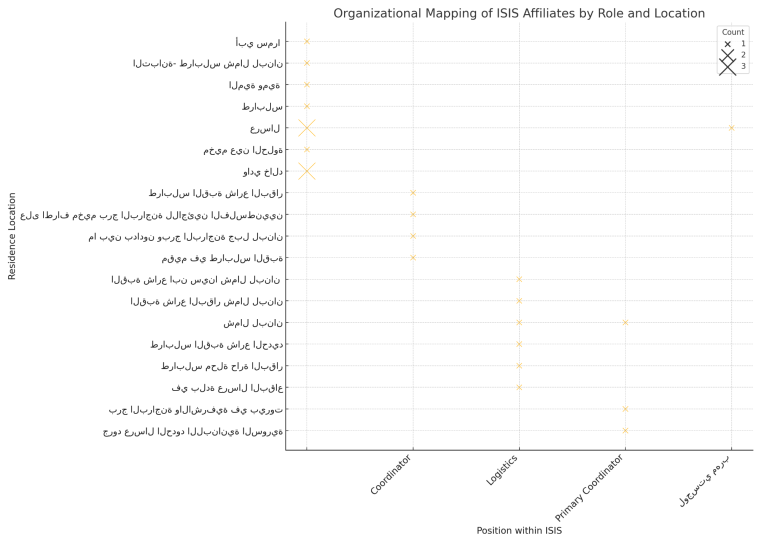
Entries anchor activity hubs in:
Tripoli and Akkar
Recruitment grounds for ISIS cells; predominantly Sunni and marginalized economically.
Raqqa, Syria
Original hometowns for multiple entries, indicating either direct travel for combat or familial displacement.
Beirut (Burj al-Barajneh, Ashrafieh)
Zones with refugee density and security gaps exploited for logistics.
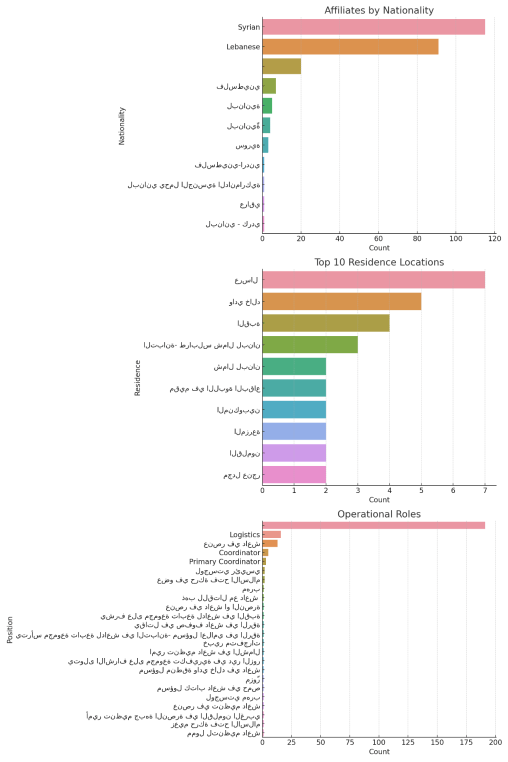
This confirms that Lebanese and Syrian border zones, as well as Palestinian camps, remained fertile ground for ISIS operatives or logistical nodes. Syrian nationals with established networks in Lebanon were instrumental in cell coordination.
4. Patterns in Arrests and Surveillance Timing
Most arrests occurred between November 11–14, 2015, pointing to a synchronized operation, possibly triggered by real-time intelligence (e.g., SIGINT intercepts, HUMINT sources). Arrest locations show systematic sweeps across different socio-political sectors—north, central Beirut, and refugee camps.
5. Affiliations and Roles
Each entry references a known organizational affiliation: “الدولة الإسلامية في العراق والشام (داعش)” (ISIS). Roles such as “منسق رئيسي” (main coordinator) and “عامل” (worker/laborer, often a cover for logistical roles) appear repeatedly. The designation “شخص طبيعي” (natural person) suggests compliance with anti-terror legal phrasing, separating individuals from organizations.
6. Legal and Institutional Processes
The data structure aligns with Lebanon’s legal submission to UN standards post-9/11 (especially Res. 1373). Lebanese Military Tribunal’s involvement indicates that these cases transcend civilian courts due to national security implications.
7. Implications
The leak reflects an institutional breach, possibly due to either insider exfiltration, state actor compromise, or cyber penetration into Lebanese internal security servers. Iran, Israel, or Syria (each with operational interests in Lebanon’s internal stability) could benefit from such exposure, depending on timing and intended audience. Exposure of suspects with identifiable residential data also risks counterproductive retaliation or community destabilization.
Strategic Insights
The Lebanese internal security framework had significant awareness of ISIS-linked logistics and personnel movement inside its borders. The document shows granular counterterrorism documentation consistent with international standards. However, the leak—whether intentional or the result of external compromise—jeopardizes operational security and opens pathways for ISIS sympathizers to alter behavior, relocate, or destroy links.
The structured association between names, locations, and logistical support functions presents an actionable template for intelligence fusion across allied services. It invites an updated regional network map of ISIS remnants or sleeper nodes in refugee camps, Tripoli, and greater Beirut.
Next Steps for Intelligence Exploitation
1. Cross-reference all names with existing INTERPOL Red Notices and UN Sanctions databases.
2. Verify current legal status, including whether detainees remain imprisoned or released.
3. Map network linkages using social media activity, known associates, and community affiliations.
4. Confirm whether any names or aliases correspond to recent attacks or reactivated ISIS cells post-2022.
5. Identify the source of the leak. Examine metadata and exfiltration indicators for origin tracing.
The strategic foresight analysis of individuals tied to ISIS in Lebanon and Syria reflects a pattern of evolving threat vectors deeply rooted in geography, demography, and operational history. Behavior patterns point to a high probability of continued recruitment within refugee camps and along border corridors. Palestinian camps such as Burj al-Barajneh and towns like Arsal served as launch pads for logistical and operational coordination. Evidence within the dataset indicates a return to vulnerability in these areas due to decreased surveillance and diminished counterterrorism momentum. That environment will enable a new generation of actors, many of whom remain undocumented or operate under family aliases.
Operational roles have undergone transformation. Earlier direct-action profiles are giving way to embedded actors tasked with financing, indoctrination, and influence projection. Arrest records reveal early signs of this shift, particularly among those flagged as coordinators or logistics support. Rather than surface in traditional militant form, many of these actors now occupy grey zones—working in non-governmental sectors, informal economies, and encrypted communications. Their residence patterns and affiliations suggest a reversion underground, often hidden beneath layers of familial, tribal, or humanitarian fronts.
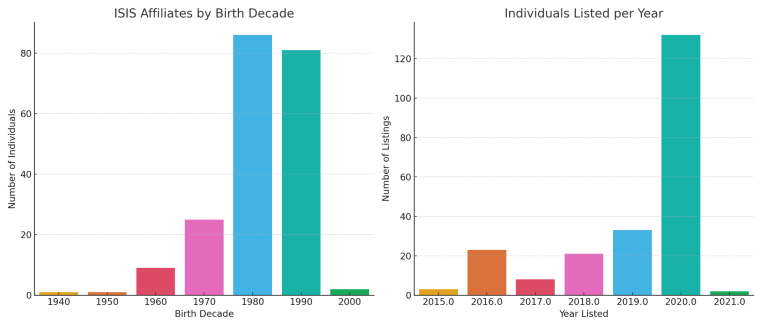
The data shows a concentration of individuals born in the 1980s and 1990s. Those now enter a maturity window where tactical experience and ideological persistence intersect. These individuals possess battlefield knowledge, incarceration narratives, and deep community embedment. Their operational flexibility exceeds that of earlier militant profiles. Law enforcement efforts centered on youthful radicalization now risk ignoring a network of maturing actors who maintain both ideological commitment and operational discretion.
Affiliations to ISIS in their original form will fragment. Groups formerly pledging allegiance will now engage under alternate identities or embedded fronts. Hybrid actors emerge who fuse religious narratives with organized criminal logistics. They embed in conflict-adjacent zones and manipulate existing sectarian divisions for tactical gain. Towns where Hezbollah and Sunni networks collide such as Ain al-Hilweh and Sidon offer geographic friction ripe for exploitation. Those areas become strategic pivots where proxy activity will gain momentum through tribal or ideological loyalty rather than top-down command.
Behavioral indicators remain consistent. Individuals under thirty-five with no stable employment, embedded in border towns, and connected to Raqqa or Deir ez-Zor by kinship or travel history represent elevated concern. Arrest patterns between 2014 and 2016 show repeated entries by those returning from Syria under the pretext of labor or refugee relocation. That method continues under new guises with current migrant flows. Names listed as coordinators or logistic facilitators will now engage in influence work or resource smuggling using pseudonyms or newly forged documents.
Strategic foresight identifies the next phase of ISIS reconstitution inside Lebanon not through mass mobilization but through cell-based reactivation. That structure avoids detection, relies on trusted networks, and operates through known choke points. Arsal, Tripoli’s inner quarters, and refugee housing units in Beirut remain open nodes. Intelligence focus must follow biometric continuity, familial association, and digital activity to maintain operational awareness of these actors. Geographic redundancy and generational recruitment cycles ensure that the network will not dissolve but morph into a more decentralized model.
Future collection should center on financial movements masked as humanitarian aid, inter-governorate travel by unregistered males between the ages of twenty-five and forty-five, and identity correlations between detainees from the 2015–2016 period and recently active social media personas







You must be logged in to post a comment.