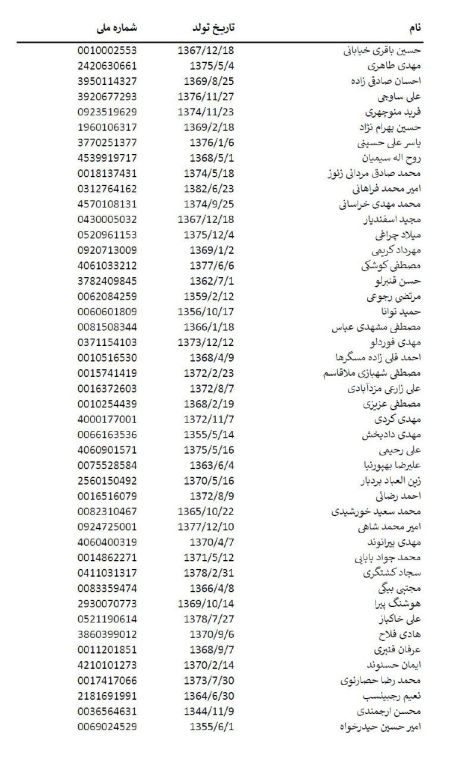
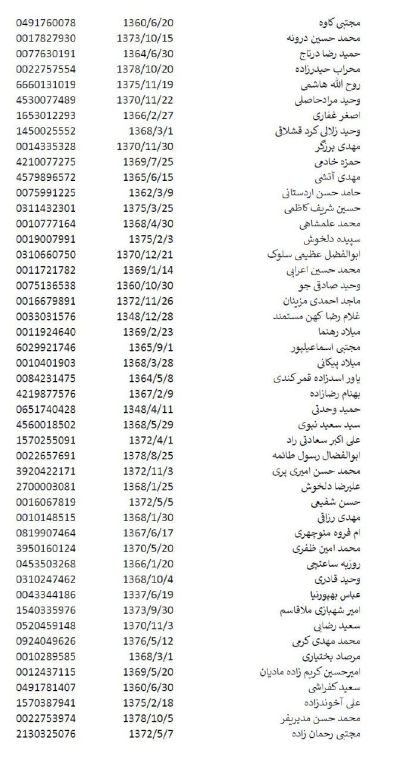
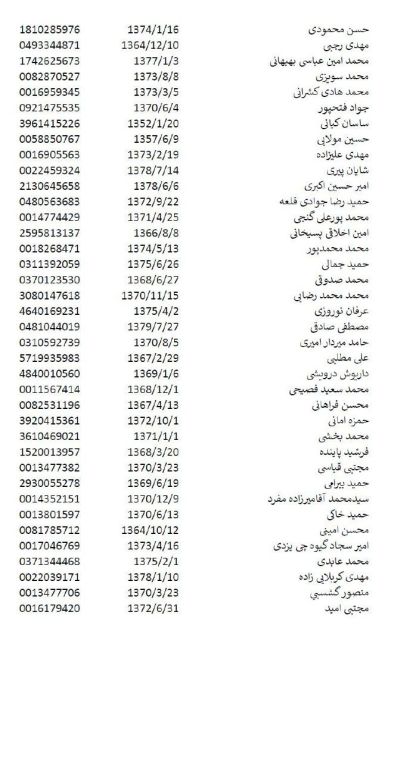
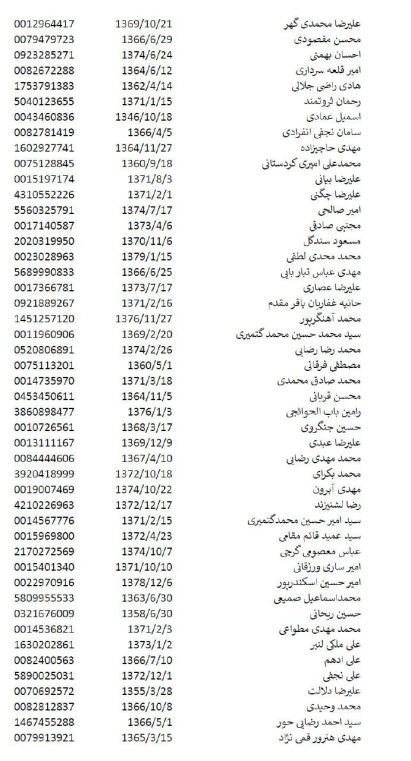
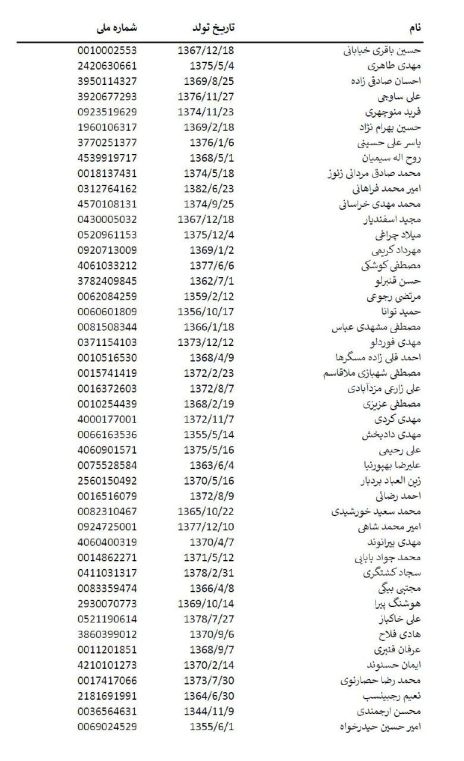
We have only a small amount of information about the regime’s cyber mercenaries, thanks to ByteSec1401_1. We invite security agencies that want to identify groups and individuals and neutralize cyber operations in countries targeted by the regime to cooperate. Thanks to our friends in these systems, we have information on 90% of cyber groups and are ready to negotiate.
#BlackWolves #Opiran #FreeIran #MahsaAmini





https://www.france24.com/en/tv-shows/tech-24/20241213-my-identity-was-stolen-by-iranian-hackers-france-24-journalist-says
Iran’s cyber capabilities are ever growing but their proxies still have patterns of behavior. Take APT42 AKA CharmingCypress or CharmingKitten for example and their latest attempt to spear phish France 24’s audience and associates by pretending to be their technology editor, Peter O Brien.
For months, the group has tried to conduct fraudulent interviews with potential clients about Iran. The reason why, could be them trying to find out what their opposition knows about them, their attempt to influence an audience, or trying to find spies within their borders.
Most likely however, they were going to use this as a chance to spread malware, a malware that according to Veloxity, has the ability to track locations, record phone conversations, access videos and images and even extract entire SMS inboxes.
France 24, with all of their subscribers and connections was right to make this PSA warning about #Iran and the #IRGC





You must be logged in to post a comment.