CrowdStrike Kernel Mode Binary #Vulnerabilities
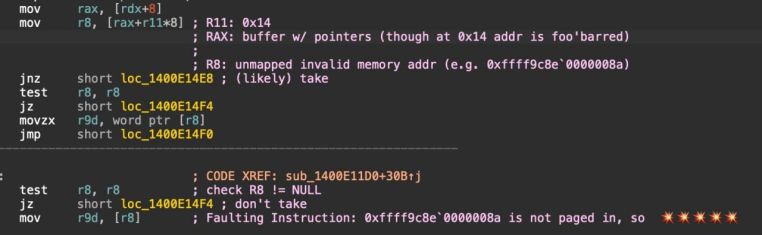
Vulnerability of NULL Pointer Deference in the Falcon sensor driver
#CrowdStrike Kernel Mode Binary #Vulnerabilities
Vulnerability of NULL Pointer Deference in the Falcon sensor driver, which will detect malicious behavior in the operating system and implement the incident response process in the implementation of artificial intelligence models, is vulnerable and operates under the name of CSAgent.sys has done
But the details of the vulnerability:
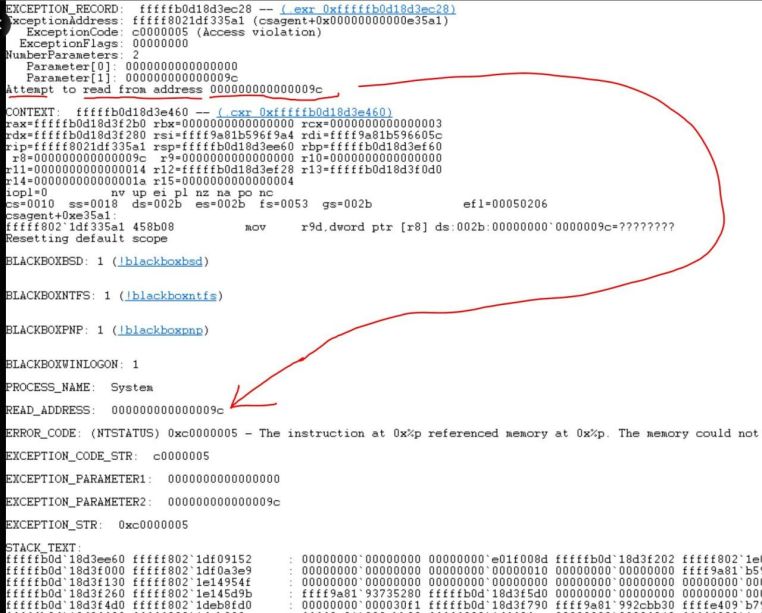
First, a kernel-level driver of the operating system is installed and launched during the boot of the operating system.
Second, the driver has the possibility of direct communication with the hardware and can also have operating system resources and access to protected memory.
Third, a kernel-level driver can affect the basic behavior of the operating system.
These drivers receive Microsoft’s digital signature in the Windows Hardware Lab Kit to operate in the operating system, which includes the Falcon software driver.
The process of reviewing and granting permission to drivers by Microsoft is a time-consuming process, so CS has created an approach called RRC to quickly perform its quick response content in the form of a content configuration update and load the driver dynamically.






You must be logged in to post a comment.