Snake Keylogger is a malware developed using .NET. It’s focused on stealing sensitive information from a victim’s device, including saved credentials, the victim’s keystrokes, screenshots of the victim’s screen, and clipboard data.
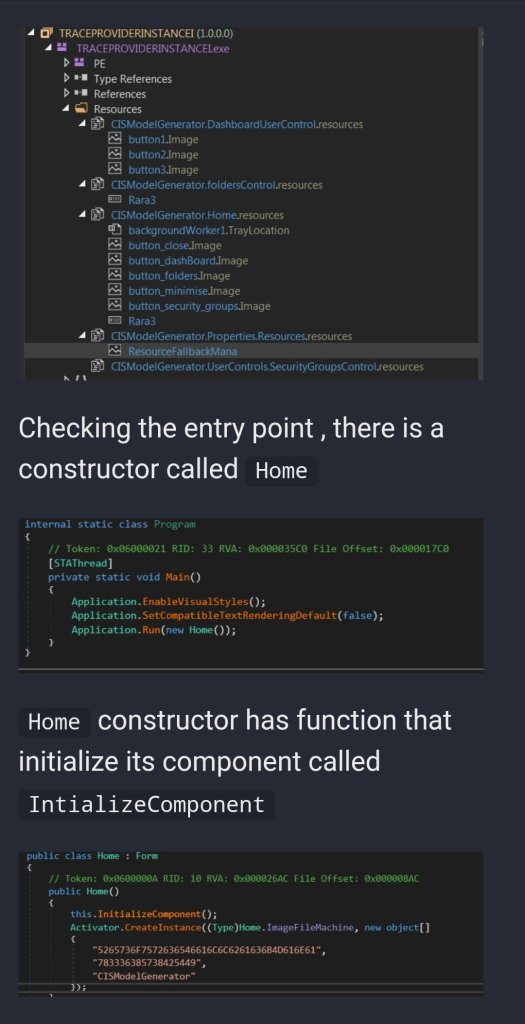
The malware usually is delivered by malicious doc and the malware comes packed , so let’s start unpacking.
https://x-junior.github.io/malware%20analysis/2022/06/24/Snakekeylogger.html
Researchers have stumbled upon a cybercriminal campaign that uses PDF attachments to install the Snake keylogger on a victim’s system. As noted by experts, PDF attachments are rarely used compared to DOCX or XLS. Most likely, the chosen format is due to the fact that people are gradually getting used to the idea of the real danger of mindlessly opening Microsoft Office files. Because of this, attackers can expect the PDF to inspire more trust. In a report from HP Wolf Security, researchers give an example of using PDF to transfer documents with malicious macros. The purpose of such documents is to install a malicious program on the user’s device that steals important data. HP Wolf Security noted that the mentioned PDFs are delivered by a letter with the subject “Remittance Invoice”, and in the body it says that the recipient is entitled to some kind of payment. When opening a PDF, Adobe Reader prompts the user to run a DOCX file that is embedded inside the original document. Already at this stage, an experienced recipient should suspect something is wrong – this is atypical behavior for PDF documents. However, the criminals tried to anticipate this and named the built-in file “has been verified”, so the user was shown the message “File has been verified”. This approach is designed for the following: the potential victim will consider that Adobe has confirmed the authenticity and harmlessness of the embedded file. Of course, the embedded DOCX file contains malicious macros that will download another file to the user’s computer – in RTF format. As experts have found out, attackers use an old vulnerability in Microsoft Equation Editor to run arbitrary code ( CVE-2017-11882 ). This gap was fixed as early as November 2017. At the final stage of the attack, the Snake modular keylogger is loaded into the victim’s system, which collects and sends the victim’s confidential data to operators.
Источник: https://www.anti-malware.ru/news/2022-05-23-111332/38730
https://link.medium.com/0tEsE6oDFzb





You must be logged in to post a comment.